UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
Washington, D.C. 20549
FORM 10-K
(Mark One)
☒ ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934
For the fiscal year ended December 25, 2021
OR
☐ TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 FOR THE TRANSITION
PERIOD FROM TO
Commission File Number 001-40714
EUROPEAN WAX CENTER, INC.
(Exact name of Registrant as specified in its Charter)
Delaware 86-3150064
(State or other jurisdiction of
incorporation or organization)
(I.R.S. Employer
Identification No.)
5830 Granite Parkway, 3 Floor
Plano, Texas
75024
(Address of principal executive offices) (Zip Code)
Registrant’s telephone number, including area code: (469) 264-8123
Securities registered pursuant to Section 12(b) of the Act:
Title of each class
Trading
Symbol(s) Name of each exchange on which registered
Class A common stock, par value $0.00001 per share EWCZ The Nasdaq Stock Market LLC
Securities registered pursuant to Section 12(g) of the Act: None
Indicate by check mark if the Registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. YES ☐ NO ☒
Indicate by check mark if the Registrant is not required to file reports pursuant to Section 13 or 15(d) of the Act. YES ☐ NO ☒
Indicate by check mark whether the Registrant: (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities Exchange Act of 1934 during the preceding 12 months (or for
such shorter period that the Registrant was required to file such reports), and (2) has been subject to such filing requirements for the past 90 days. YES ☒ NO ☐
Indicate by check mark whether the Registrant has submitted electronically every Interactive Data File required to be submitted pursuant to Rule 405 of Regulation S-T (§232.405 of this chapter)
during the preceding 12 months (or for such shorter period that the Registrant was required to submit such files). Yes ☒ No ☐
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, smaller reporting company, or an emerging growth company. See the
definitions of “large accelerated filer,” “accelerated filer,” “smaller reporting company,” and “emerging growth company” in Rule 12b-2 of the Exchange Act.
Large accelerated filer
☐
Accelerated filer
☐
Non-accelerated filer
☒
Smaller reporting company
☐
Emerging growth company ☒
If an emerging growth company, indicate by check mark if the registrant has elected not to use the extended transition period for complying with any new or revised financial accounting
standards provided pursuant to Section 13(a) of the Exchange Act. ☐
Indicate by check mark whether the registrant has filed a report on and attestation to its management’s assessment of the effectiveness of its internal control over financial reporting under Section
404(b) of the Sarbanes-Oxley Act (15 U.S.C. 7262(b)) by the registered public accounting firm that prepared or issued its audit report. ☐
Indicate by check mark whether the Registrant is a shell company (as defined in Rule 12b-2 of the Exchange Act). YES ☐ NO ☒
The aggregate market value of the Registrant's Class A common stock held by non-affiliates, based on the closing price of the shares of Class A common stock as reported on The Nasdaq Stock
Market LLC on December 23, 2021, was $613.9 million. The Registrant elected to use December 23, 2021 as the calculation date because on June 26, 2021 (the last business day of the
Registrant’s second fiscal quarter), the Registrant was a privately held company and it was the closest trading day prior to the Registrant's fiscal year-end.
As of March 10, 2022, the registrant had 37,032,423 and 26,433,636 shares of Class A and Class B common stock, respectively, $0.00001 par value per share, outstanding.
DOCUMENTS INCORPORATED BY REFERENCE
Portions of the registrant’s definitive proxy statement for its annual meeting of stockholders to be held on June 8, 2022 are incorporated by reference into Part II and Part III of this Form 10-K.
rd
Table of Contents
Page
PART I
Item 1. Business 1
Item 1A. Risk Factors 9
Item 1B. Unresolved Staff Comments 40
Item 2. Properties 40
Item 3. Legal Proceedings 40
Item 4. Mine Safety Disclosures 41
PART II
Item 5. Market for Registrant’s Common Equity, Related Stockholder Matters and Issuer Purchases of Equity Securities 42
Item 6. Reserved. 43
Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations 43
Item 7A. Quantitative and Qualitative Disclosures About Market Risk 59
Item 8. Financial Statements and Supplementary Data 60
Item 9. Changes in and Disagreements With Accountants on Accounting and Financial Disclosure 90
Item 9A. Controls and Procedures 90
Item 9B. Other Information 90
Item 9C. Disclosure Regarding Foreign Jurisdictions that Prevent Inspections 90
PART III
Item 10. Directors, Executive Officers and Corporate Governance 91
Item 11. Executive Compensation 91
Item 12. Security Ownership of Certain Beneficial Owners and Management and Related Stockholder Matters 91
Item 13. Certain Relationships and Related Transactions, and Director Independence 91
Item 14. Principal Accounting Fees and Services 91
PART IV
Item 15. Exhibits, Financial Statement Schedules 92
Item 16. Form 10-K Summary 93
i
PART I
Item 1. Business.
Overview
We are the largest and fastest-growing franchisor and operator of out-of-home ("OOH") waxing services in the United States by number of centers and
system-wide sales. We delivered over 21 million waxing services in 2019, over 13 million waxing services in 2020 and over 20 million waxing services in
2021 generating $687 million, $469 million and $797 million of system-wide sales, respectively, across our highly-franchised network. We have a leading
portfolio of centers operating in 853 locations across 44 states as of December 25, 2021. Of these locations, 848 are franchised centers operated by
franchisees and five are corporate-owned centers.
The European Wax Center brand is trusted, efficacious and accessible. Our culture is obsessed with our guest experience and we deliver a superior guest
experience relative to smaller chains and independent salons. We offer guests high-quality, hygienic waxing services administered by our licensed, EWC-
trained estheticians (our “wax specialists”), at our accessible and welcoming locations (our “centers”). Our technology-enabled guest interface simplifies
and streamlines the guest experience with automated appointment scheduling and remote check-in capabilities, ensuring guest visits are convenient, hassle-
free, and consistent across our network of centers. Our well-known, pre-paid Wax Pass program makes payment easy and convenient, fostering loyalty and
return visits. Guests view us as a non-discretionary part of their personal-care and beauty regimens, providing us with a highly predictable and growing
recurring revenue model.
Our asset-light franchise platform delivers capital-efficient growth, significant cash flow generation, and resilience through economic cycles. Our centers
are 99% owned and operated by our franchisees who benefit from superior unit-level economics, with mature centers generating annual cash-on-cash
returns in excess of 60%.
In partnership with our franchisees, we fiercely protect our points of differentiation that attract new guests, build meaningful relationships and promote
lasting retention. We are so confident in our ability to delight that we have always offered all of our guests their first wax free.
Our Recent Financial Performance
Financial Performance in 2019
During 2019, we administered more than 21 million services and grew our center count to 750. We generated $687 million of system-wide sales and $154
million of net revenue. Net loss was $24 million and Adjusted EBITDA was $34 million in 2019.
Performance in 2020 and During the COVID-19 Pandemic
In January and February 2020, our performance continued with the same momentum experienced in 2019, with same-store sales growth of 11.1% and
10.8%, compared to the prior year periods. At the onset of the pandemic in March 2020, however, all of our centers temporarily closed due to the
implementation of certain mandated closure requirements across the United States. In response to the pandemic, our management team developed and
executed a detailed response plan focused on raising our already industry-leading hygiene standards and ensuring the safety of our guests, franchisees and
associates.
By May 2020, our centers began to re-open as local health and safety guidance allowed and we saw an immediate rebound in performance. While the
trajectory of our same-store sales performance fluctuated during the second half of 2020 in conjunction with state-specific loosening or tightening of
COVID-19 restrictions in response to subsequent waves of COVID-19, our overall recovery demonstrates our guests consistently wanted to get back to
their regular waxing routines at European Wax Center. By March 2021, nearly all of our nationwide network had re-opened and we were generating
system-wide sales of approximately 101% of what they had been in March 2019 suggesting a nearly complete rebound from COVID-19 impacted
performance in 2020. 87% of the 52 opened centers came from our existing franchise base, reinforcing our network’s belief in the stability and future
success of our brand. During 2020, despite the challenges from COVID-19, our platform delivered strong growth in new centers as well as resilience in
revenues and profit margins. All corporate-owned centers had re-opened as of December 26, 2020.
• Center count increased from 750 in 2019 to 796 in 2020;
• System-wide sales decreased from $687 million in 2019 to $469 million in 2020;
• Net revenue decreased from $154 million in 2019 to $103 million in 2020;
• Net loss decreased from $24 million in 2019 to $21 million in 2020; and
• Adjusted EBITDA decreased from $34 million in 2019 to $20 million in 2020.
1
Performance during 2021
As conditions resulting from the COVID-19 pandemic continued to improve, our platform delivered growth in revenue and profitability, as well as an
increase in new centers during fiscal year 2021. As of December 25, 2021 all of our centers had reopened, and we expect that our future financial results
will continue to strengthen as COVID-19 related capacity restrictions were lifted and guests are able to return to our centers at full capacity levels.
• Center count increased from 796 as of December 26, 2020 to 853 as of December 25, 2021;
• System-wide sales increased from $469 million in fiscal year 2020 to $797 million in fiscal year 2021;
• The Company’s total revenue increased from $103 million for the year ended December 26, 2020 to $179 million for the year ended
December 25, 2021;
• Consolidated net income improved from a net loss of $21 million in 2020 to net income of $4.0 million in 2021; and
• Adjusted EBITDA increased from $20 million for the year ended December 26, 2020 to $64 million for the year ended December 25,
2021.
Our Growing Market Opportunity
Hair removal is an integral and recurring part of the personal-care and beauty regimens for most women and many men in the United States, and hair
removal solutions are consistently in demand, given the recurring nature of hair growth.
We estimate that our $18 billion total addressable domestic market includes approximately 69 million U.S. adults who are currently waxing or are
interested in waxing. The OOH waxing market, in which European Wax Center competes, is the fastest growing hair removal alternative and grew at an
estimated compound annual growth rate ("CAGR") of 8% between 2015 and 2019, compared to an estimated CAGR of 3% over the same time period for
the total hair removal market.
Although European Wax Center currently represents only 4% of our addressable market, we estimate we are approximately six times larger than our closest
waxing-focused competitor within OOH waxing by center count and approximately 13 times larger by system-wide sales. Our market remains highly
fragmented, with more than 10,000 independent waxing-focused operators that lack scale and almost 100,000 beauty salons that only provide waxing as a
small part of their broader service offering. For many beauty salons and other similar operators, waxing is not their core competency, with services
frequently provided in “backrooms” and without significant investment in the overall experience. This fragmentation results in a marketplace characterized
by inconsistent quality, lack of technological accessibility and scheduling, and one-time transactional services that fail to instill customer trust and
engagement. European Wax Center’s singular focus on waxing services and unmatched scale allow us to capitalize on this opportunity.
Our Differentiated Brand Experience
We believe our approach to OOH waxing has revolutionized the category. Our brand experience is differentiated because we are:
• Experts in Wax: Our service model is focused exclusively on wax-based hair removal. We obsess over every element of the waxing services we
deliver for our guests:
• Expert Line-up of Waxing Services & Products: We provide a comprehensive assortment of body and facial waxing services using our
Comfort Wax formulation, which features a unique blend of the highest quality natural beeswax combined with other skin-soothing
ingredients for the most comfortable waxing experience. We provide a line of proprietary pre- and post-service products, including ingrown
hair serums, exfoliating gels, brow shapers and skin treatments, which ensure the full benefits of the waxing experience are realized by our
guests.
• Expert Training of our Licensed Wax Specialists: Our franchisees employ over 8,000 licensed, highly-trained and knowledgeable wax
specialists committed to delivering an exceptional guest experience. In addition to being licensed, every EWC wax specialist must
successfully complete our proprietary training program to ensure consistency and quality of service for every guest. Our wax-focused
education modules provide time-intensive training that substantially builds upon cosmetology licensing programs. We view our training as a
key competitive differentiator enabling guests to receive a consistent service delivery regardless of the wax specialist with whom they are
scheduled. Through the delivery of personalized services and education about the benefits of regular waxing, our wax specialists help
strengthen guest loyalty to our brand.
• Expert Hygiene and Safety Standards: We adhere to the highest safety and hygiene standards in the industry. We from time to time engage
third-party safety experts to review and enhance our hygiene protocols. Wax Specialists utilize disposable gloves and masks to administer
services and we strictly adhere to single use wax applicator protocols (we never double dip the applicator blades in wax pots). Our wax
suites are sanitized and disinfected after each guest visit. In addition, our centers are equipped with socially-distanced seating arrangements
and multiple sanitary stations, and our mobile app facilitates a contactless experience with self-check-in.
2
• Champions of Confidence and Guest Experience: According to consumer surveys, our guests feel better and more confident after a service
visit at one of our centers. We have focused on enhancing the guest experience across all touchpoints within our brand:
• Champions of Accessibility: Our growing network of 853 centers across 44 states enables convenience and accessibility for our customers.
Whether our guests move across town or across the country, our brand can serve their ongoing waxing needs with more access points than
any other provider of OOH waxing services in the United States. Our Wax Pass program is portable across our network and guests often
redeem services through a Wax Pass across multiple European Wax Center locations. Our mobile app technology further enhances
accessibility by enabling guests to easily book appointments on-line at a time and location most convenient to them.
• Champions of the In-Center Experience: Our in-center atmosphere is designed to be refined, clean and easy to use, with mobile app self-
check-in available at all centers. Our lobby features an inviting product wall with take-home sampling. Our guests can choose to wait for
their appointment in their car until a text alerts them to walk directly to their designated suite where their wax specialist awaits. Our iPad-
equipped suites provide our wax specialists with detailed insights on each of their guests, empowering them to personalize product
recommendations, for example.
• Champions of Guest Retention and Repeat Visits: We encourage guests to schedule future visits on a regular basis and reward them for
their use of our pre-paid Wax Pass program. We believe Wax Pass holders visit us more frequently, have meaningfully higher retention rates
and represent our most valuable guests. Additionally, we expect to further amplify our guest experience and drive retention with our EWC
Rewards Loyalty Program that launched in October 2021.
Our Competitive Strengths
We attribute our success to the following strengths that we believe provide us with a competitive advantage in our industry:
Trusted National Brand that Inspires Confidence
We believe revealing beautiful skin is the first step to revealing one’s best self, and our brand stands for delivering unapologetic confidence to our guests.
Waxing is an intimate experience, and our guests seek a dependable, safe, and clean setting with a professional wax specialist they trust. Our unmatched
scale provides us with a nationwide footprint to serve our loyal guest base wherever they may be. Our singular commitment to delivering best-in-class
service is reinforced by our marketing efforts driving national brand awareness and consideration. We are so confident in our ability to delight that we have
always offered all our guests their first wax free.
Committed Franchisees Achieving Attractive and Predictable Unit-Level Economics
Our simple, yet difficult to replicate, operating model translates into an attractive return on our franchisees’ invested capital. Our high-quality franchisee
base consists of 239 franchisees as of December 25, 2021, with 159 franchisees operating multiple European Wax Center locations. Our centers require a
modest upfront investment cost, then rapidly achieve profitability and generate superior unit-level economics. We generate revenue from our franchisees
through the sale of branded products as well as the payment of ongoing fees, including royalty and marketing fund contributions, which are determined by
the service sales of each center. For the year ended December 25, 2021, we received revenue from our franchisees as follows: $99.7 million, or 58%, of our
revenue came from product sales, $43.6 million, or 25%, of our revenue through franchisee royalty payments, $24.6 million, or 14%, of our revenue
through marketing fund contributions, and $4.6 million, or 3%, of our revenue came from other sources. Our remaining revenue for the year ended
December 25, 2021 was generated from corporate-owned centers.
Our centers experience a highly predictable maturation curve that is consistent across cohorts and geographies, providing our franchisees with a high
degree of confidence in realizing attractive returns. We believe our value proposition has created a franchisee base that is committed to growing with our
brand, with more than 79% of new centers opened in 2019, 87% of new centers opened in 2020 and 93% of new centers opened in 2021 coming from
existing franchisees.
Recurring Nature of Services Combined with Scaled Footprint and Consistent Demand Drives Revenue Predictability
Hair removal is an integral part of the personal-care and beauty regimens for most women and many men in the United States. Given the recurring nature
of hair growth, hair removal solutions are regularly in demand and our guests trust European Wax Center to meet their routine hair removal needs. Our
national scale and exclusive focus on wax-based hair removal enables us to provide a highly consistent waxing experience across each of our centers. The
reliability of our guest experience ensures consistent demand for our services, which drives uniform unit-level economics for our franchisees which in turn
drives revenue predictability for European Wax Center. We further facilitate repeat visits through the use of our pre-paid Wax Pass program, which we
believe promotes meaningfully higher guest retention rates.
3
Asset-Light Franchise Platform with Resilient Free Cash Flow Generation
Our asset-light franchise platform delivers capital-efficient growth, significant cash flow, and resilience through economic cycles. Due to the impacts of
COVID-19, including the temporary closure of all of our centers, our networks experienced the first year of negative same-store sales growth in 2020.
However, positive same-store sales growth, calculated against both 2020 and 2019, resumed in 2021. In addition, given our low capital expenditures and
working capital needs, we are able to drive strong free cash flow generation throughout economic cycles. In 2020, for example, through disciplined cost
management, our business remained profitable on an EBITDA basis and sustained strong EBITDA margins despite the decline in system- wide sales driven
by the COVID-19 pandemic. Our ability to drive robust financial performance through 2020 is a testament to the resilience of our platform, which enables
us to invest in technology and digital enablement, training programs, and marketing initiatives. This is a key differentiator of our scaled platform relative to
independent operators in our market, and a significant reason why we believe we are the franchisor of choice in OOH waxing.
Experienced and Passionate Management Team Investing in the Next Phase of Our Growth
We are led by a best-in-class management team and our culture of performance, success and inclusivity is established by our CEO David Berg, who
previously served as the CEO of Carlson Hospitality and has extensive retail, hospitality and franchising experience. Since joining us in 2018, Mr. Berg has
led the acceleration of our center growth, the expansion of our franchisee network and our heightened cultural obsession with guest satisfaction.
The other members of our leadership team have been assembled at European Wax Center from senior positions at leading organizations including Sally
Beauty, Luxottica, Jamba Juice, and American Eagle Outfitters. Our team has encouraged investment in tech-forward systems and corporate infrastructure
to support the anticipated continued growth of our network. We believe our guests and franchisees are better connected with one another as a result of our
scale advantages and we are only in the early innings of truly unlocking the potential of our unique platform.
Our Growth Strategies
We intend to deliver sustainable growth in revenue and profitability by executing on the following basic strategies:
Grow Our National Footprint Across New and Existing Markets
We believe our franchisees’ track record of successfully opening new centers and consistently generating attractive unit-level economics validates our
strategy to expand our footprint and grow our capacity to serve more guests. Our center count grew 7%, 6% and 5% during fiscal years 2021, 2020 and
2019, respectively, and has grown every year since 2010. Our thoughtful approach to growth ensures each center is appropriately staffed with the high-
quality team and licensed, highly trained wax specialists that our brand has been known for since our initial opening.
We believe that none of our existing markets are fully penetrated and approximately 75% of our whitespace opportunity is in markets where we already
have a presence today, which provides us with a high degree of confidence for the likely receptivity and success of new openings.
Our new centers require a modest upfront investment and follow a highly predictable maturation curve across cohorts and geographies, providing us and
our franchisees with a high degree of visibility into the embedded earnings potential of newly opened centers. Historically, our centers reach maturity after
five years, and as of December 25, 2021, 67% of our centers were mature.
Continue to Grow Our Brand Awareness and Accelerate Our Guest Acquisition
We believe that influential consumer trends will continue to expand the market for OOH waxing and that the OOH market will continue to take share from
alternative hair removal solutions. Although our brand is nationally recognized, there are still significant opportunities to further drive brand awareness to
attract new guests while increasing engagement of existing guests through increased visit frequency and spend.
To drive brand awareness with all consumers, we employ several strategies, including:
• Performance marketing: We deploy data-driven marketing dollars across multiple forms of media with an attractive return on advertising
spend;
• Digital content: We partner with select digital media content creators and social media influencers, thereby encouraging positive testimonials
from our guests; and
• Market densification: We are strategically densifying existing target markets with new centers thus increasing regional brand awareness and
word-of-mouth referrals.
Employ Strategies to Continue Driving Same-Store Sales Growth
We are continuously employing strategies to increase guest visit frequency and drive higher guest spend with the aim of sustaining our same-store sales
growth, including:
4
• Increase Wax Pass Adoption Rates: Our Wax Pass program provides guests with preferential pricing through either pre-paid or unlimited wax
passes and provides us with a recurring and predictable revenue stream. We continue to expand and refine the program to drive increased
adoption from non- member guests and we have grown the share of transactions conducted using Wax Passes to more than 57% in 2021.
• Expand our Share of our Guests’ Personal-Care Expenditures: The trusted relationships between guests and wax specialists results in an
authentic channel through which we can increase our share of our guests’ spend on personal-care. Over time, we believe the relationship
between guest and wax specialist provides us a strong foundation to broaden our offerings across the personal-care category.
• Increase our Transaction Attachment Rate: Approximately 14%, 15% and 11% of transactions in 2021, 2020 and 2019, respectively, resulted in
purchases of retail products. In April 2021, we launched a refreshed portfolio of retail products complementing our core waxing services across
all centers. We expect to drive greater attachment rates from this new product line-up through the right product innovation, attractive pricing, and
expert consultative selling by our trained wax specialists. We define the term “attachment rate” as the percentage of transactions that include the
purchase of a retail product to the total number of transactions.
• Drive Greater Guest Engagement Using Data Analytics: We are continuously developing new use cases from our guest database. As our data
capabilities mature, we believe we will learn more about our guests’ preferences and behaviors, unlocking more high-quality interaction
opportunities. We are in the process of expanding our advanced data analysis capabilities to improve guest visit frequency and loyalty by
deploying timely and hyper-personalized communications and relevant reminders to our guests.
Expand Our Profit Margins and Generate Robust Free Cash Flow
We have invested in building our scalable support infrastructure, and we currently have the capabilities and systems in place to drive revenue growth and
profitability across our existing and planned franchise centers. Given our unmatched scale within the OOH waxing market, we can procure the highest
quality products and supplies used to administer our services at lower prices than smaller independent providers of the same services. We expect to
generate operating leverage given our fixed corporate cost structure, and we expect that incremental leverage, combined with our low capital expenditure
and working capital needs, will allow us to generate improved operating margins and robust free cash flow.
Our Guests
Approximately 96% of our guests are women, with our brand appealing to female guests across age groups, ethnicities and income brackets. At every
touchpoint, we embody our mission by concentrating key media communications on passion points that bolster guest affinity for European Wax Center and
deliver personalized messaging to inspire action. While we estimate that male waxing constitutes approximately 20% of our total addressable market, our
current guest base is only 4% male, representing an attractive growth opportunity. We believe there has been a significant increase in male interest in OOH
waxing over the past five years. We intend to increase our share of male guests, with specific male-focused marketing collateral and service offerings.
Our Centers
We have a leading portfolio of centers operating in 853 locations across 44 states as of December 25, 2021. Of these locations, 848 are franchised centers
operated by franchisees and five are corporate-owned centers.
On average, our centers are approximately 1,200 to 1,600 square feet with six to seven wax suites and are typically staffed with one wax specialist per suite
in addition to one or two guest service associates. Our centers are designed to provide a seamless guest experience from the moment our guests walk in, to
the moment they strut out of our centers. Upon entry, guests are greeted by a friendly service associate in a clean and modern lobby. The lobby offers
refined colors and textures that align with the European Wax Center brand ethos. Our guests can self-check-in through our mobile app, which increases the
swiftness of guest intake while allowing our team members to focus on servicing guests.
We ensure our centers offer socially distant seating and sanitation stations, underscoring our commitment to industry-leading hygiene and safety standards.
Once checked-in, our guests enter a private, sanitized waxing suite where wax specialists offer a personalized experience. In-suite iPads provide our wax
specialists with detailed insights on each of their guests, empowering them to provide “concierge-like” services such as personalized add-on services and
product recommendations, driving increased guest spend. After each service, our guests are encouraged to test our retail products with samples from our
touch-free sample bar, promoting our transaction attachment rate.
We continuously evaluate and enhance our center layout, imagery and cost build-out to ensure we have the best experience for our guests which drives
continued robust financial performance for our franchisees.
5
Center Selection Criteria
We have a scaled and diverse footprint with ample whitespace for center growth in new markets, as well as densification within our existing markets. Site
selection for new centers are typically proposed by our franchisees and reviewed and approved by European Wax Center as the franchisor. We determine
whether a site is appropriate for a European Wax Center location based on the condition of the premises, ease of access, visibility, proximity to other
centers, proximity to other competitive businesses, lease requirements, co-tenants, traffic patterns, demographics and population density, among other
factors.
Our Services and Retail Products
We offer our guests a variety of elevated body and facial waxing services focused on the most critical areas of their bodies needing hair removal. We also
offer skincare retail products to ensure that the full benefits of the waxing experience are realized by our guests.
Services
Our waxing services are administered by licensed wax specialists who are employed by our franchisees. In addition, prior to performing our services, our
wax specialists go through a rigorous, proprietary EWC training regime. Continuous training education is also a part of our ongoing operating plan to
ensure the highest quality service can constantly be delivered across our network of centers. Our wax specialists utilize our Comfort Wax formulation
during the waxing service. This wax product features a blend of the highest quality natural beeswax combined with other skin-soothing ingredients and is
co-manufactured for us by suppliers in Europe. Unlike other wax formulations, our wax is designed to specifically attach only to hair, not skin, providing a
differentiated and more comfortable waxing experience.
Retail Products
Our centers sell a comprehensive assortment of proprietary EWC-branded retail products that allow guests to maintain healthy post-wax skin between
visits. These products are specifically tailored to enhance the services we provide. Our products are dermatologist-tested and are formulated without
parabens, mineral oil, phthalates, hydroquinone, triclosan, formaldehyde and gluten. We exclusively distribute these retail products to our franchisees for
sale in-center and sell them direct-to-consumer through our website. We have approximately 34 full-sized SKUs in our branded product portfolio.
We partner with a leading co-manufacturer in North America to coordinate the manufacturing of our retail product offerings. While our suppliers support us
in formulation, sourcing, manufacturing, package development, safety testing and quality assurance, we own all of our retail product formulas and lead the
new product development processes to align our innovation capabilities with our strategic priorities.
Marketing Support
Based on our deep guest understanding and longevity in the OOH waxing market, we believe we have developed a highly effective marketing strategy that
is designed to promote awareness and consideration of our brand by new guests and encourage retention by existing guests.
We employ a variety of marketing techniques to build awareness of, and create demand for, our brand, and the services and products we offer. We have
implemented sophisticated data-driven marketing practices in support of this framework and we deploy the dedicated marketing funds contributed by our
franchisees across each of our marketing strategies. In 2019, we collected and spent approximately $20 million for marketing through our centralized
marketing fund, of which 61% was deployed through digital channels. Due to center closures in 2020 driven by the COVID-19 pandemic, we paused our
marketing fund collections from April 2020 to June 2020. As a result, we do not believe that the amounts collected and spent through our centralized
marketing fund in 2020 are representative of our historical or expected future marketing collections and spend. In 2021, we collected and spent
approximately $25 million for marketing through our centralized marketing fund, of which 44% was deployed through digital channels.
In addition to our corporate marketing strategy, many of franchisees choose to make additional investments in local marketing. We provide support to
ensure that their marketing aligns with our overall image and strategy.
Our Franchise Platform
Franchising Strategy
Our asset-light franchise platform delivers capital-efficient growth and our footprint expansion is supported by robust unit-level economics. Our simple, yet
difficult to replicate, operating model and the recurring nature of our services translates into an attractive return on invested capital for our franchisees. Our
centers require a modest upfront investment cost and follow a highly predictable maturation curve that is consistent across cohorts and geographies.
We are intentionally shifting toward a larger mix of multi-unit development agreements as we grow our footprint, which will allow for consistent and
efficient growth as we continue to scale.
6
Franchise Agreements
For each of our franchisees, we enter into a franchise agreement stipulating a standard set of terms and conditions. The initial term of a franchise agreement
is generally ten years, with the option to renew their agreements at expiration (ten-year renewal option). All proposed new center sites require formal
approval from us. Franchisees pay us an initial franchise license fee and franchise royalties typically based on a percentage of gross sales less the sale of
retail products. Franchisees also make contributions to our centralized marketing fund based on a percentage of gross sales less the sale of retail products.
Our franchise agreements set forth the requirements franchisees must comply with, including, but not limited to, our standard operational policies and
procedures that govern the provision of services and use of suppliers and require franchisees to purchase specified products from us and/or designated
suppliers. Franchisees are required to conform to our established operational policies and procedures relating to, among other things, quality of service,
training, center design and décor and trademark usage. Outside of these operational policies and procedures, we do not control the day-to-day operations of
franchised centers, including, but not limited to, employment, benefits and wage determination, establishing prices to charge for products and services,
business hours, personnel management and capital expenditure decisions. However, the franchise agreements afford us, as franchisor, certain rights,
including, but not limited to, the right to approve locations, suppliers and the sale of a franchise. Additionally, our field personnel make periodic visits to
franchised centers to ensure that they are operating in conformity with the operational policies and procedures for our franchising program. All of the rights
afforded to us with regard to franchised operations allow us to protect our brand, but do not allow us to control the day-to-day operations of franchised
centers or make decisions that have a significant impact on the success of franchised centers.
Franchise Support Services
We enjoy a strong partnership with our franchisees. To support their collective and individual success, we provide our franchisees with meaningful support
services including pre-opening support, guest experience support, and ongoing back-end support.
Pre-opening support:
• Site selection and approval: we work in partnership with our franchisees to ensure prospective new center locations are adequately vetted ahead
of any initial investment. Each franchisee is responsible for selecting a location but must ultimately obtain approval from us.
• Other pre-opening support: we conduct business reviews with each franchisee eight weeks prior to new center openings to ensure construction
activities are in sync with recruitment plans, training programs and all other pre-opening marketing activities to ensure each center is best
positioned to open successfully and build momentum.
Guest experience support:
• Wax training: we require an intensive six-day training program for all new wax specialists as well as continued learning requirements to keep all
wax specialists performing at the consistent, high-quality standards for which we are known. Training is conducted by a corporate or peer trainer
both in-person as well as virtually. Franchisees also appoint in-house trainers who are expected to maintain an ongoing training system for wax
specialists within each center.
• Hygiene protocols: our health and safety standards were industry-leading even before the COVID-19 pandemic and continue to be industry-
leading. We engage with independent safety experts to ensure our continued leadership and to ensure our centers remain best-in-class from a
hygiene standard.
Ongoing support:
• Marketing and consumer insights: our centralized marketing strategy, funded by contributions from our franchisees based on a percentage of
gross sales, net of retail product sales, as defined in the franchise agreement, allows us to leverage our scale in media buying and utilize our
proprietary guest insights to maximize brand awareness and consideration.
• Uniform Point-of-Sales System: we leverage a consistent Point-of-Sales system across our entire network which is easy to adopt and results in a
streamlined approach to ongoing technical support for our franchisees.
• Procurement and supply chain: our operating leverage and our scale allows us to procure the highest quality products at lower prices than smaller
independent waxing-focused operators benefiting our franchisees.
• Performance management: our team of Franchise Business Consultants works closely with our franchisees across regional territories with
ongoing managerial support including: monthly business reviews, per-center brand health and voice-of-customer measurement and additional
one-on-one support as needed.
These support services allow our franchisees to focus on the day-to-day operations of their centers and to provide high-quality services that our guests have
come to associate with our brand. We also participate in a Brand Advisory council, through which we collect continuous feedback from our franchisees to
enhance our offering, business model and support services, and to ensure that our franchisees have an open channel of communication with us.
7
Franchise Unit-Level Economics
A European Wax Center location typically reaches maturity in year five of operations, at which point a center generates on average $1.0 million in revenue
and annual cash-on-cash returns in excess of 60%. A typical franchisee initially invests approximately $356,000 when opening a new center (excluding real
estate purchase or lease costs, pre-opening expenses and initial working capital investment), with ongoing fees that are determined by the service sales of
each center. These ongoing fees include royalty and marketing fund contributions, which are 6% and 3% of service sales, respectively. Our centers follow a
highly predictable maturation curve once open that is consistent across cohorts and geographies, with an average unit volume of $0.7 million and double-
digit EBITDA margins already in year two of operations.
Competition
The OOH waxing industry is highly fragmented with more than 10,000 independent waxing operators and almost 100,000 beauty salons that provide
waxing as a small part of their broader service offerings. Within OOH waxing, we compete with independent waxing operators, beauty salons, beauty
parlors, health clubs, spas, beauty supply stores and other independently owned companies. We believe that we compete favorably on the basis of a number
of factors, including the quality of our services, the trustworthiness of our brand, our best-in-class hygiene standards, convenience, accessibility, guest
experience and the depth of our experience as experts within OOH waxing.
We also compete with other types of hair removal alternatives, including laser hair removal, sugaring, threading, as well as in-home solutions, such as
shaving, chemical-based creams, epilators, at-home laser hair removal and at-home waxing. OOH laser hair removal is a semi-permanent solution that is
significantly more expensive than OOH waxing and presents potential safety risks. Sugaring and threading are both less effective options than OOH
waxing and have not been widely adopted among consumers. At-home shaving lasts for a significantly shorter time than waxing, and other at-home
solutions are frequently viewed as less effective, messier, more painful and more time-consuming than OOH services administered by highly-trained
specialists.
We also compete with other franchisors on the basis of the expected return on investment for franchisees and the value proposition that we offer them. We
compete to sell franchises to potential franchisees who may choose to purchase franchises from other service providers in other markets.
Suppliers and Distributors
To preserve brand integrity and consistency, we require our franchisees to purchase products related to the operation of their franchised centers, including
our wax and branded skin care products, either from us, our affiliates or approved suppliers. We maintain strong, longstanding relationships with our
suppliers to ensure market competitiveness and reliability in our supply chain. We leverage our sizeable spend to obtain favorable terms from our suppliers
and to provide competitive prices to our franchisees, thus improving profitability and providing a considerable advantage over competitors that lack our
scale. We believe that as our business continues to grow, our scale will continue to drive increased procurement benefits across our business.
Our products are manufactured by market leaders, and we partner with two overseas suppliers with multiple facilities in Spain and France to source our
wax and one supplier to source our branded retail products. We currently have a long-term contract with only one of our wax suppliers. Our manufacturing
partners arrange for delivery of products either to one of the three third-party distribution centers that supply our centers or directly to our franchised and
corporate-owned centers.
We typically keep three to six months of wax inventory at three third party distribution centers to sustain system-wide supply and protect against shortfalls
that could arise from unforeseen market unavailability. These three distribution centers are located in Pennsylvania, Tennessee, and Nevada to provide
optimal distribution capability for us to meet the demands from centers throughout the United States. We believe that the existing supply chain we have in
place is sufficient to support our future growth.
Information & Technology Systems
We utilize our information technology infrastructure to facilitate data-driven management decisions. Across our franchise system, we use a fully integrated
platform that helps franchisees with reporting, marketing, operations, guest service and center management. Our technology platform gives management
access to key reporting metrics across our network, providing comprehensive insight into system health. In addition, we recently rolled out a new point of
sale system that uses cloud-based technology to process and store information.
Governmental Regulation
Our operations are subject to numerous federal, state, local and municipal laws and regulations in the United States in areas such as consumer protection,
occupational licensing, environmental protection, data privacy, labor and employment, tax, permitting, and other laws and regulations. In certain
jurisdictions, we must obtain licenses or permits in order to comply with standards governing employee selection, training and business conduct.
We, as a franchisor, are subject to various federal and state laws, and the Federal Trade Commission (the “FTC”) regulates our franchising activities in the
United States. The FTC requires that franchisors make extensive disclosure to prospective franchisees
8
before the execution of a franchise agreement. Fourteen states require registration and, together with at least one other state, require specific disclosure in
connection with franchise offers and sales, and at least twenty states and U.S. territories have “franchise relationship laws” that limit the ability of
franchisors to terminate franchise agreements or withhold consent to the renewal or transfer of these agreements.
We are not aware of any federal, state, local, municipal or other laws or regulations that are likely to materially alter or impact our revenues, cash flow or
competitive positions, or result in any material capital expenditures. However, we cannot predict the effect on our operations, particularly on our
relationship with franchisees, of any pending or future legislation or regulations or the future interpretation of any existing laws, including any newly
enacted laws, that may impact us or our franchisees.
Human Capital
As of December 25, 2021, we employed approximately 111 full-time employees, including approximately five full-time employees at corporate-owned
centers. We also employ approximately 76 part-time associates. None of these employees are covered by a collective bargaining agreement. We consider
our relations with our employees to be good. Our human capital resources objectives include, as applicable, identifying, recruiting, retaining, incentivizing
and integrating our existing and prospective employees. The principal purposes of our incentive plans are to attract, retain and motivate selected employees,
executive officers and directors through the granting of stock-based compensation awards and cash-based performance bonus awards. We strive for
exceptional performance and results, which is why meritocracy is one of our core values. We provide employees the opportunity to grow and to be
rewarded based on results.
To ensure the safety of our and our franchisees’ employees during the COVID-19 pandemic, we refined our in-center atmosphere to allow for contactless
check-in at all centers and elevated our hygiene standards at all centers. We sanitize all wax suites with disinfectant wipes after each guest’s visit and
require our franchisees to carry an inventory of gloves, face masks and other personal protective equipment.
Our franchises are independently owned and operated businesses. As such, employees of our franchisees are not employees of European Wax Center, Inc.
or EWC Ventures.
Intellectual Property
Our trademarks are important to our marketing efforts and conduct of business. We own or have the rights to use certain trademarks, service marks and
trade names that are registered or for which registration applications are pending with the U.S. Patent and Trademark Office or exist under common law in
the United States. Trademarks that are important in identifying and distinguishing our products and services include, but are not limited to EUROPEAN
WAX CENTER
®
, EWC
®
, STRUT 365
®
, WAX PASS
®
and COMFORT WAX
®
. We also own domain names, including our primary domain
“www.waxcenter.com.”
Seasonality
Seasonal changes may moderately impact the demand for our waxing services. For example, our guests may come to our centers more frequently in the
summer months and during the November to December holiday season.
Available Information
We are subject to the informational requirements of the Securities Exchange Act of 1934, as amended, and in accordance therewith, we file reports, proxy
and information statements and other information with the SEC. Our annual reports on Form 10-K, quarterly reports on Form 10-Q, current reports on
Form 8-K, proxy and information statements and other information and amendments to those reports filed or furnished pursuant to Section 13(a) or 15(d)
of the Securities Exchange Act of 1934 are available through the investor relations section of our website. Our Internet address is www.waxcenter.com.
Reports are available on our website free of charge as soon as reasonably practicable after we electronically file them with, or furnish them to, the SEC. In
addition, our officers and directors file with the SEC initial statements of beneficial ownership and statements of change in beneficial ownership of our
securities, which are also available on our website at the same location. We are not including this or any other information on our website as a part of, nor
incorporating it by reference into, this Form 10-K or any of our other SEC filings.
In addition to our website, the SEC maintains an Internet site that contains our reports, proxy and information statements, and other information that we
electronically file with, or furnish to, the SEC at www.sec.gov.
Item 1A. Risk Factors.
Our operations and financial results are subject to various risks and uncertainties, including those described below. You should consider and carefully read
all the risks and uncertainties described below, together with all the other information contained in this Annual Report on Form 10-K, including the section
titled “Management’s Discussion and Analysis of Financial Condition and Results of Operations” and our consolidated financial statements and related
notes, before making an investment decision. The risks described below are not the only ones we face. The occurrence of any of the following risks or
additional risks and uncertainties not presently known to us or that we currently believe to be immaterial could materially and adversely affect our
business, financial condition, or results of operations. In such case, the trading price of our Class A common stock could decline.
9
SUMMARY RISK FACTORS
The following is a summary of some of the significant risks and uncertainties that could materially adversely affect our business, financial condition, results
of operations, cash flows and the market price of our common stock. You should read this summary together with the more detailed description of these and
other risk factors contained below.
Risks Relating to Our Business
• Our business is affected by the financial results of our franchisees.
• If our franchisees are unable to successfully enter new markets, select appropriate sites for new centers or open new centers, our growth
strategy may not succeed.
• Our success depends on the effectiveness of our marketing and advertising programs and the active participation of franchisees in such
marketing and promotional activities.
• Franchisees could take actions that could harm our brand, including failing to comply with their franchise agreements and policies, and
adversely affect our business.
• Our and our franchisees’ centers may be unable to attract and retain guests, which would materially and adversely affect our business, results
of operations and financial condition.
• Increased use of social media may adversely impact our reputation and adversely affect sales and operating results.
• The high level of competition we face could materially and adversely affect our business.
• Our ability to improve our financial performance depends on our ability to anticipate and respond to market trends and changes in consumer
preferences.
• Our planned growth could place strains on our management, employees, information systems and internal controls, which may adversely
impact our business.
• Our financial performance could be materially adversely affected if we fail to retain, or effectively respond to a loss of, key executives.
• If our technology-based guest services systems do not function effectively, our operating results could be materially adversely affected.
• We are heavily dependent on computer systems and information technology and any material failure, interruption or security breach of our
computer systems or technology could impair our ability to efficiently operate our business.
• The occurrence of cyber-incidents, or a deficiency in cybersecurity, could negatively impact our business by causing a disruption to our
operations, a compromise or corruption of confidential information, and/or damage to our employee and business relationships, all of which
could lead to loss and harm our business.
• If we fail to properly maintain the confidentiality and integrity of our data, including guest credit card, debit card and, bank account
information and other personally identifiable information, our reputation and business could be materially and adversely affected.
• We and our franchisees rely heavily on information systems, and any material failure, interruption or weakness may prevent us from
effectively operating our business and damage our reputation.
• We are subject to a number of risks related to ACH, credit card, debit card, and digital payment options it accepts.
• Changing regulations relating to privacy, information security and data protection could increase our costs, affect or limit how we collect and
use personal information and harm our brands in a manner that adversely affects our business.
• Our level of indebtedness could have a material adverse effect on our ability to generate sufficient cash to fulfill our obligations under such
indebtedness, to react to changes in our business and to incur additional indebtedness to fund future needs.
• Our 2026 Credit Agreement contains financial covenants and other restrictions on our actions that may limit our operational flexibility or
otherwise adversely affect our business, financial condition and results of operations.
Risks Relating to the Franchisees
• Nearly all of our centers are owned and operated by franchisees and, as a result, we are highly dependent upon our franchisees.
• It is important for us and our franchisees to attract, train, and retain talented wax specialists and managers.
10
• Franchisees are operating entities exposed to risk.
• Changes in labor costs, other operating costs, such as commodity costs, interest rates and inflation could adversely affect our results of
operations.
• We may not be able to retain franchisees or maintain the quality of existing franchisees.
• Our center development plans under development agreements may not be implemented effectively by franchisees.
Risks Relating to our Suppliers and Distributors
• We depend on a limited number of key suppliers, including international suppliers, to deliver high-quality products at prices similar to
historical levels.
• Changes in supply costs could adversely affect our results of operations.
• Decreases in our product sourcing revenue could adversely affect our results of operations.
• Supply chain shortages and interruptions could adversely affect our business.
• Operational failure at one of the distribution centers that supply our centers would impact our ability to distribute products.
Risks Relating to Intellectual Property
• Our success and the success of our franchisees depends on the adequate protection of our intellectual property and litigation to enforce our
intellectual property rights may be costly.
• If we are unable to adequately protect our intellectual property, the strength of our brand may be weakened, and our business could be
harmed significantly.
• If franchisees and other licensees do not observe the required quality and trademark usage standards, our brands may suffer reputational
damage, which could in turn adversely affect our business.
Risks Relating to Our Organization and Structure
• We are a holding company and our principal asset is our 58.0% equity interest in EWC Ventures, and we are accordingly dependent upon
distributions from EWC Ventures to pay dividends, if any, and taxes, make payments under the tax receivable agreement and cover other
expenses, including our corporate and other overhead expenses.
• Our organizational structure, including the TRA, confers certain benefits upon the EWC Ventures Pre-IPO Members that do not benefit
holders of our Class A common stock (other than the EWC Ventures Pre-IPO Members) to the same extent that it benefits the EWC Ventures
Pre-IPO Members.
• The General Atlantic Equityholders, whose interests in our business may be different than yours, hold a significant percentage of the
combined voting power of our common stock and certain statutory provisions afforded to stockholders are not applicable to us.
Risks Relating to our Class A Common Stock
• Our stock price may be volatile, and the value of our Class A common stock may decline.
• We cannot predict the effect our dual-class structure may have on the market price of our Class A common stock.
• Substantial future sales of shares of our Class A common stock in the public market could cause our stock price to fall.
• Failure to establish and maintain effective internal control over financial reporting could have a material adverse effect on our business,
financial condition, results of operations and stock price.
• Certain of our key operating metrics are subject to inherent challenges in measurement, and any real or perceived inaccuracies in our metrics
or the underlying data may cause a loss of investor confidence in such metrics and the market price of our Class A common stock may
decline.
• We are an “emerging growth company” and we cannot be certain if the reduced disclosure requirements applicable to emerging growth
companies will make our Class A common stock less attractive to investors.
11
Risks Relating to Our Business
Our business is affected by the financial results of our franchisees.
A substantial portion of our revenue comes from royalties generated by, and sales of wax and retail products to, our franchised centers. Accordingly, our
business is impacted by the operational and financial success of our franchisees, including the franchisees’ implementation of our strategic plans and their
ability to secure adequate financing. The employees of franchisees are not our employees. We provide training and support to franchisees, but the quality of
franchised center operations may be diminished by a number of factors beyond our control. Consequently, franchisees may not successfully operate centers
in a manner consistent with our standards and requirements or may not hire and train qualified managers and other center personnel. If they do not, our
image and reputation may suffer, and revenues could decline.
Additionally, if our franchisees are impacted by weak economic conditions and are unable to secure adequate sources of financing, their financial health
may worsen, our revenues may decline, and we may need to offer extended payment terms or make other concessions. Additionally, refusal on the part of
franchisees to renew their franchise agreements may result in decreased payments from franchisees. Furthermore, if our franchisees are not able to obtain
the financing necessary to complete planned remodel and construction projects, they may be forced to postpone or cancel such projects.
Furthermore, a bankruptcy of any multi-unit franchisee could negatively impact our ability to collect payments due under such franchisee’s agreements. In
a franchisee bankruptcy, the bankruptcy trustee may reject its franchise agreements under the applicable bankruptcy code, in which case there would be no
further royalty payments from such franchisee. The amount of the proceeds, if any, that may ultimately be recovered in a bankruptcy proceeding of such
franchisee may not be sufficient to satisfy a damage claim resulting from such rejection. See “—Nearly all of our centers are owned and operated by
franchisees and, as a result, we are highly dependent upon our franchisees.”
If our franchisees are unable to successfully enter new markets, select appropriate sites for new centers or open new centers, our growth strategy may
not succeed.
Our growth strategy includes entering into franchise agreements and development agreements with franchisees who will open additional centers in markets
where there are either an insufficient number or relatively few or no existing centers. We rely heavily on these franchisees and developers to grow our
franchise systems, and there can be no assurance that we will be able to successfully expand or acquire critical market presence for our brands in new
geographical markets in the United States. Consumer characteristics and competition in new markets may differ substantially from those in the markets
where we currently operate. Additionally, we may be unable to identify qualified franchisees, develop brand recognition, successfully market our products
or attract new guests in such markets and our franchisees may be unable to identify appropriate locations in such markets. See “—Our center development
plans under development agreements may not be implemented effectively by franchisees” herein.
Our franchisees face many other challenges in opening additional centers, including:
• availability of financing on acceptable terms;
• selection and availability of and competition for suitable center locations;
• negotiation of acceptable lease terms;
• securing required applicable governmental permits and approvals;
• impact of natural disasters and other acts of nature and terrorist acts or political instability;
• availability of franchise territories not prohibited by the territorial exclusivity provisions of existing franchisees;
• employment, training and retention of qualified personnel;
• exposure to liabilities arising out of sellers’ prior operations of acquired centers;
• incurrence or assumption of debt to finance acquisitions or improvements and/or the assumption of long-term, non-cancelable leases; and
• general economic and business conditions.
Should our franchisees not succeed in opening additional centers or improving existing centers, there may be adverse impacts to our growth strategy and to
our ability to generate additional profits, which in turn could materially and adversely affect our business and results of operations.
A component of our business strategy includes the construction of additional centers and the renovation and build-out of existing centers by our
franchisees, and a significant portion of the growth in our franchisees’ sales and profit margins will depend on growth in comparable sales for our centers.
Our franchisees face competition from other operators, retail chains, companies, and developers for desirable center locations, which may adversely affect
the cost, implementation, and timing of our franchisees’ expansion plans. If
12
our franchisees experience delays in the construction or remodeling processes, they may be unable to complete such activities at the planned cost, which
could adversely affect our franchisees’ business and results of operations. Additionally, our franchisees cannot guarantee that such remodeling will increase
the revenues generated by these centers or that any such increases will be sustainable. Likewise, our franchisees cannot be sure that the sites they select for
additional centers will result in centers that meet sales expectations. Our franchisees’ failure to add a significant number of additional centers or grow
comparable sales for our centers could materially and adversely affect our business and results of operations.
In particular, because nearly all of the development of additional centers is likely to be funded by franchisee investment, our growth strategy is dependent
on our existing and prospective franchisees’ ability to access funds to finance such development. We do not generally provide our franchisees with direct
financing and therefore their ability to access borrowed funds generally depends on their independent relationships with various financial institutions. In
addition, labor and material costs expended will vary by geographical location and are subject to general price increases. The timing of these improvements
can affect the performance of a center, particularly if the improvements require the relevant center to be closed. If our existing and prospective franchisees
are not able to obtain financing at commercially reasonable rates, or at all, they may be unwilling or unable to invest in the development of additional
centers. In addition, our growth strategy may take longer to implement and may not be as successful as expected. Both of these factors could reduce our
competitiveness and future sales and profit margins, which in turn could materially and adversely affect our business and results of operations.
Furthermore, the ability of our franchisees to enter new markets and grow our business may not be indicative of future growth. Our various business
strategies and initiatives, including our growth of franchisees, are subject to business, economic and competitive uncertainties and contingencies, many of
which are beyond our control. The historic conversion rate of signed commitments to new franchised centers may not be indicative of the conversion rates
we will experience in the future.
Our success depends on the effectiveness of our marketing and advertising programs and the active participation of franchisees in such marketing and
promotional activities.
Brand marketing and advertising significantly affect sales at our centers. Our marketing and advertising programs may not be successful, which may
prevent us from attracting new guests and retaining existing guests. We rely heavily on the active participation of our franchisees for the implementation of
marketing initiatives to be successful. Our inability to mandate franchisees to participate in marketing and promotional activities or our franchisees’
inability to successfully implement these initiatives could adversely affect our business results. Also, because many of the franchisees are contractually
obligated to pay advertising fees based on a percentage of their service revenues, our advertising budget depends on sales volumes at these centers. While
we and certain of our franchisees have sometimes voluntarily provided additional funds for advertising in the past, we are not legally obligated to make
such voluntary contributions or loan money to pay for advertising. If sales decline, we will have fewer funds available for marketing and advertising, which
could materially and adversely affect our revenues, business and results of operations.
As part of our marketing efforts, we rely on traditional, social and digital advertising, as well as search engine marketing, web advertisements, social media
platforms and other digital marketing to attract and retain guests. These efforts may not be successful, resulting in expenses incurred without the benefit of
higher revenues or increased employee or guest engagement. A failure to sufficiently innovate, develop guest relationship initiatives, or maintain adequate
and effective advertising could inhibit our ability to maintain our brand relevance and drive increased sales. Guests are increasingly using internet sites and
social media to inform their purchasing decisions and to compare prices, product assortment, and feedback from other guests about quality, responsiveness
and guest service before purchasing our services and products. If we are unable to continue to develop successful marketing and advertising strategies,
especially for online and social media platforms, or if our competitors develop more effective strategies, we could lose guests and sales could decline. In
addition, a variety of risks are associated with the use of social media and digital marketing, including the improper disclosure of proprietary information,
negative comments about or negative incidents regarding us, exposure of personally identifiable information, fraud or out-of-date information. The
inappropriate use of social media and digital marketing vehicles by us, our franchisees, our guests, employees or others could increase our costs, lead to
litigation or result in negative publicity that could damage our reputation. Many social media platforms immediately publish the content, videos and/or
photographs created or uploaded by their subscribers and participants, often without filters or checks on accuracy of the content posted. Information posted
on such platforms at any time may be adverse to our interests and/or may be inaccurate. The dissemination of negative information related to our brands
could harm our business, prospects, financial condition, and results of operations, regardless of the information’s accuracy. The harm may be immediate
without affording us an opportunity for redress or correction. The occurrence of any such developments could have an adverse effect on our business
results and on our profits.
Franchisees could take actions that could harm our brand, including failing to comply with their franchise agreements and policies, and adversely
affect our business.
Franchisees are contractually obligated to operate their centers for the contractual terms and in accordance with the standards set forth in the franchise
agreements, including specified service and product quality standards and other requirements, in order to protect our brand and to optimize its performance.
However, franchisees are independent third parties that we do not control, and the franchisees own, operate and oversee the daily operations of their
centers. As a result, the ultimate success and quality of any franchised center rests with the franchisee. If
13
franchisees provide substandard services, receive through the supply chain defective products or do not successfully operate centers for the contractual
terms and in a manner consistent with required standards, franchise royalty payments to us will be adversely affected and our image and reputation could
be harmed, which in turn could hurt our revenues, results of operations, business and financial condition.
In addition, we may be unable to successfully implement our business model, company policies, or brand development strategies that we believe are
necessary for further growth if franchisees do not participate in that implementation. Our revenues, results of operations, business and financial condition
could be adversely affected if a significant number of franchisees do not participate in brand strategies.
Our and our franchisees’ centers may be unable to attract and retain guests, which would materially and adversely affect our business, results of
operations and financial condition.
Our target market is people seeking regular out-of-home waxing services who consider waxing services a meaningful component of their personal-care and
beauty regimens. Our and our franchisees’ marketing efforts may not be successful in developing repeat guests and guest levels may materially decline
over time. In addition, we experience attrition and must continually engage existing guests and attract new guests in order to maintain profitability. Some of
the factors that could lead to a decline in guest retention include changing desires and behaviors of consumers or their perception of our brand, changes in
discretionary spending trends and general economic conditions, market maturity or saturation, a decline in our ability to deliver quality service at a
competitive price, direct and indirect competition in our industry, and a decline in the public’s interest in waxing services or personal-care, among other
factors.
Furthermore, the success of our business depends in part on our and our franchisees’ ability to grow the number of our Wax Pass holders. Our Wax Pass
program drives guest loyalty and provides valuable data and insights on our core guests, without which it may be difficult for us to adapt to changing guest
preferences or predict market trends. If we and our franchisees are not successful in optimizing prices or in adding new Wax Pass holders in new and
existing centers, growth in program fees may suffer. Any decrease in our guest attraction or retention levels or average program fees, or increase in
program costs, may adversely impact our results of operations and financial condition.
Increased use of social media may adversely impact our reputation and adversely affect sales and operating results.
There has been a substantial increase in the use of social media platforms, including blogs, social media websites and other forms of digital
communications, and the influence of social media influencers in the personal-care and beauty products industry, that allow individuals access to a broad
audience of consumers and other persons, including to our guests. Events reported in the media, including social media, whether or not accurate or
involving European Wax Center, could create and/or amplify negative publicity for us or for the industry or market segments in which we operate. Social
media, mobile and other emergent forms of communications can be used to spread negative publicity rapidly and with greater scope and give users the
ability to organize collective actions more effectively, such as boycotts and other brand-damaging events. Negative comments, whether or not accurate,
may be disseminated via social media relating not only to our business but to actions taken, or not taken, with respect to social, environmental and
community outreach issues and initiatives. Many, if not all, social media platforms immediately publish their participants’ posts, often without filters or
checks on the accuracy of the content posted. This could hamper our ability to correct misrepresentations timely or respond effectively to negative
publicity. Any failure to respond quickly and effectively to negative or potentially damaging social media content, especially if it goes “viral”, regardless of
the content’s accuracy, could damage our reputation, which in turn could harm our business, prospects, financial condition and results of operations. These
and other types of social media risks could reduce demand for our services and result in a decrease in guest traffic to our corporate and franchisee locations
as consumers shift their preferences to competitors. A decrease in guest traffic to our corporate and franchisee locations as a result of negative publicity
created or amplified by social media could result in a decline in sales and operating results. Social media risks could also arise from corporate or franchisee
employees, personnel, spokespeople, or other representatives not following defined policies for the use of social media during business operations, or
actions taken by our employees, personnel, spokespeople, or other individuals associated, or perceived to be associated with, us, including during personal
or other activities outside of their employment or engagement, but which could damage the perception or reputation of our brand.
As part of our marketing efforts, we rely on search engine marketing and social media platforms to attract and retain guests. For example, we maintain
Facebook, Twitter, Instagram, Pinterest, YouTube, LinkedIn and TikTok accounts. In addition, we have agreements with a variety of industry influencers,
and we feature industry influencers in our advertising and marketing efforts and may include them in some of our branding and we may be unable to fully
control such influencers’ efforts. Further, many industry influencers use our products and feature our products through their own platforms. Actions taken
by these individuals could harm our brand image, net revenues, profitability and may subject us to fines or other penalties. The availability of these
platforms may make it easier for smaller competitors to compete with us. These efforts may not be successful, and pose a variety of other risks, including
the improper disclosure of proprietary information, the posting of negative comments about us, respectively, exposure of personally identifiable
information, fraud or use of out of date information, hoaxes, or malicious dissemination of false information. The inappropriate use of social media
vehicles by franchisees, guests, spokespeople, or employees could increase costs incurred by us, lead to litigation or result in negative publicity that could
damage our reputation. In addition, laws, regulations and enforcement actions, including by the U.S. Federal Trade Commission (“FTC”), rapidly evolve to
govern social media platforms and communications. The
14
failure by us, our personnel, our Franchisees, its spokespeople and brand ambassadors or third parties acting at its direction to abide by applicable laws and
regulations in the use of social media could adversely impact our brand, reputation, financial condition and results of operations or subject us to fines or
other penalties. The occurrence of any such developments could have an adverse effect on business results.
The growing prevalence and importance of social media platforms, behavioral advertising, and mobile technology also pose challenges and risks for our
marketing, advertising, and promotional strategies; and failure to effectively use and gain traction on these platforms or technologies could cause our
advertising to be less effective than its competitors. Negative commentary regarding us or the products we sell may be posted on social media platforms or
other electronic means at any time and may be adverse to our reputation or business. Guests value readily available information and often act on such
information without further investigation and without regard to its accuracy. Any harm to us or the products we sell may be immediate without allowing it
an opportunity for redress or correction.
In addition, a failure of us, our employees, our franchisees or third parties acting at our direction to abide by applicable laws and regulations in the use of
social media could adversely impact our brand, reputation, marketing partners, financial condition, and results of operations or subject us or our franchisees
to fines or other penalties. Other risks associated with the use of social media include improper disclosure of proprietary information, exposure of
personally identifiable information, fraud, hoaxes or malicious dissemination of false information.
The high level of competition we face could materially and adversely affect our business.
We compete with more than 10,000 independent waxing operators and almost 100,000 beauty salons that provide waxing as a small part of their broader
service offerings. Within OOH waxing, we compete with independent waxing operators, beauty salons, beauty parlors, health clubs, spas, beauty supply
stores and other independently owned companies. We also compete with other types of hair removal alternatives, including laser hair removal, sugaring,
threading, as well as in-home solutions, such as shaving, chemical-based creams, epilators, at-home laser hair removal and at-home waxing. We may not be
able to compete effectively in the markets in which we operate. Competitors may attempt to copy our business model, or portions thereof, which could
erode our market share and brand recognition and impair our growth rate and profitability. Competitors, including companies that are larger and have
greater resources than us, may compete with us to attract guests in our markets. Luxury personal-care companies may attempt to enter our market by
lowering prices or creating lower price brand alternatives. Furthermore, due to the increased number of low-cost and independently owned waxing
alternatives, we may face increased competition if we increase our price or if discretionary spending declines. This competition may limit our ability to
attract and retain existing guests and Wax Pass holders and our ability to attract new guests and Wax Pass holders. Such increase in competition, in each
case, could materially and adversely affect our results of operations and financial condition.
In addition, we compete with other franchisors to attract and retain qualified franchisees. The inability to attract and retain qualified franchisees could
impact payments under the franchise documents and could have a material adverse effect on our business and results of operations. See “—We may not be
able to retain franchisees or maintain the quality of existing franchisees.”
Our ability to improve our financial performance depends on our ability to anticipate and respond to market trends and changes in consumer
preferences.
Our ability to improve our financial performance depends on our ability to anticipate, gauge and react in a timely and effective manner to changes in
consumer spending patterns and preferences for waxing and related personal-care services and products. We must continually work to develop, produce and
market new services and products, maintain and enhance the recognition of our brand, achieve a favorable mix of services and products, and refine our
approach as to how and where we market and sell our services and products. Consumer spending patterns and preferences cannot be predicted with
certainty and can change rapidly depending on factors outside our control, including general economic conditions, unemployment rates, wage levels and
disposable income levels. It is also possible that competitors could introduce new products and services that negatively impact consumer preference for our
business model, or that consumers could prefer hair removal services, such as less costly laser hair removal options or more effective at-home hair removal
options than are currently available, that do not align with our business model or compete with us. In addition, certain market trends may be short-lived.
There can be no assurance that we will be able to anticipate and respond to trends timely and effectively in the market for waxing and related personal-care
services and products and changing consumer demands and improve our financial results.
Furthermore, material shifts or decreases in market demand for our services and products, including as a result of changes in consumer spending patterns
and preferences or incorrect forecasting of market demand, could result in us carrying inventory that cannot be used by our wax specialists or sold at
anticipated prices or increased product returns by our guests. Failure to maintain proper inventory levels or increased product returns by our franchisees
could result in a material adverse effect on our business, prospects, financial condition, liquidity, results of operations and cash flows.
15
Our planned growth could place strains on our management, employees, information systems and internal controls, which may adversely impact our
business.
Over the past several years, we have experienced growth in our business activities and operations, including a significant increase in the number of system-
wide centers. Our past expansion has placed, and our planned future expansion may place, significant demands on our administrative, operational, financial
and other resources. Any failure to manage growth effectively could seriously harm our business. To be successful, we will need to continue to implement
management information systems and improve our operating, administrative, financial and accounting systems and controls. These changes may need to be
implemented quickly. Our inability to implement and maintain such systems and controls, including to accurately report our data, could harm consumer
confidence in our reporting and adversely affect our business. We will also need to train new employees and maintain close coordination among our
executive, accounting, finance, legal, human resources, risk management, marketing, technology, sales and operations functions. These processes are time-
consuming and expensive, increase management responsibilities and divert management attention, and we may not realize a return on our investment in
these processes. In addition, we believe the culture we foster at our and our franchisees’ centers is an important contributor to our success. However, as we
expand we may have difficulty maintaining our culture or adapting it sufficiently to meet the needs of our operations. These risks may be heightened as our
growth accelerates. In 2021, our franchisees opened 61 centers, compared to 52 centers in 2020 and 42 centers in 2019. Our failure to successfully execute
on our planned expansion of centers could materially and adversely affect our results of operations and financial condition.
Our financial performance could be materially adversely affected if we fail to retain, or effectively respond to a loss of, key executives.
The success of our business depends on the contributions of key executives and senior management. The departure of key executives or senior management
could have a material adverse effect on our business and long-term strategic plan. We have a succession plan that includes short-term and long-term
planning elements intended to allow us to successfully continue operations should any of our key executives or senior management become unavailable to
serve in their respective roles. However, there is a risk that we may not be able to implement the succession plan successfully or in a timely manner or that
the succession plan will not result in the same financial performance we currently achieve under the guidance of our existing executive team. Any lack of
management continuity could adversely affect our ability to successfully manage our business and execute our growth strategy, as well as result in
operational and administrative inefficiencies and added costs, and may make recruiting for future management positions more difficult.
If our technology-based guest services systems do not function effectively, our operating results could be materially adversely affected.
Our guests are increasingly using tablets and smart phones to interact with us before, during, and after their visits as a means to enhance their experience.
Our mobile app allows our guests to schedule their visits and facilitates a contactless experience with self-check-in. Any failure on our part to provide an
attractive, effective, reliable, and user-friendly digital platform that continually meets the changing expectations of our guests could place us at a
competitive disadvantage, result in the loss of sales, harm our reputation with our guests and could have a material adverse impact on our business and
results of operations. If we fail to implement changes to our mobile app in response to rapidly developing technology, fail to maintain a relevant consumer
experience in understanding and interacting with our mobile app or fail to effectively respond to telecommunications disruptions, including disruptions to
the operations of third-party software providers upon whom we rely, our operating results could be materially and adversely affected.
Furthermore, we continue to invest in digital platforms to deliver new digital experiences that provide better services and value to our franchisees. If we
move to a different partner to develop and maintain such platforms, or if the current partner's ability to provide its services is impaired, our operations could
increasingly be interrupted. The digital platforms are built on commercial cloud computing platforms and future digital services we may offer could also be
sourced from third-party platforms. These solutions depend on the internet, internet providers, and cloud computing providers to deliver ongoing services,
the interruption of which could disrupt our operations. Disruption to the aforementioned solutions and/or services could adversely impact the products and
services we offer to our guests and affect our guest sales and retention.
We are heavily dependent on computer systems and information technology and any material failure, interruption or security breach of our computer
systems or technology could impair our ability to efficiently operate our business.
We and our franchised centers are dependent upon our computer systems and other information technology to properly conduct our business, including, but
not limited to, point-of-sale processing in our centers, management of our supply chain, collection of cash, payment of obligations and various other
processes and procedures. See “—We do not own certain software that is used in operating our business” herein. Our ability to efficiently manage our
business depends significantly on the reliability and capacity of these information technology systems. The failure of these systems to operate effectively,
an interruption, problems with maintenance, upgrading or transitioning to replacement systems, fraudulent manipulation of sales reporting from our centers
or a breach in security of any of these systems could result in loss of sales and franchise royalty payments, cause delays in guest service, result in the loss of
data, create exposure to litigation and government investigation, reduce efficiency, cause delays in operations or otherwise harm our business. Significant
capital investments might be required to remediate any problems and to maintain and continue to update our information technology over time. Any
security breach involving any of our point-of-sale or other systems could result in a loss of consumer confidence and potential costs associated with fraud
or breaches of data security laws. Also, despite our considerable efforts
16
to secure our computer systems and information technology, security breaches, such as unauthorized access and computer viruses, may occur, resulting in
system disruptions, shutdowns or unauthorized disclosure of confidential information.
A future security breach of our computer systems or information technology could require us to notify our guests, employees or other groups, result in
adverse publicity, loss of sales and profits, could materially affect our operations, financial condition and performance and could result in penalties or other
costs that could adversely affect the operation of our business and results of operations.
The occurrence of cyber-incidents, or a deficiency in cybersecurity, could negatively impact our business by causing a disruption to our operations, a
compromise or corruption of confidential information, and/or damage to our employee and business relationships, all of which could lead to loss and
harm our business.
A cyber-incident is considered to be any adverse event that threatens the confidentiality, integrity or availability of information resources. More
specifically, a cyber-incident is an intentional attack or an unintentional event that can include an unauthorized party gaining unauthorized access to
systems to disrupt operations, corrupt data or steal confidential information about our guests, franchisees, our company, vendors or employees. As our
reliance on technology has increased, especially in light of an increase in work-from-home arrangements due to the novel coronavirus COVID-19
("COVID-19") pandemic, so have the risks posed to our systems, both internal and those we have outsourced. The company has been subject to attempted
cyber-attacks in the past and may continue to be subject to such attacks in the future. Such attacks have become more common, and many companies have
recently experienced serious cyber incidents and breaches of their information technology systems. We could also be subject to negative impacts to our
business caused by cyber incidents relating to our third-party service providers. A successful cyber-attack or other cyber-incident experienced by us or our
service providers could cause an interruption of our operations, could damage our relationship with franchisees, and could result in the exposure of private
or confidential data, potentially resulting in litigation or government investigation. In addition to maintaining insurance coverage to address cyber-
incidents, we have also implemented processes, procedures and controls to help mitigate these risks. However, these measures, as well as our increased
awareness of a risk of a cyber-incident, do not guarantee that our reputation and financial results will not be adversely affected by any incident or event that
occurs.
Because our centers accept electronic forms of payment from our guests, our business requires the collection of guest data, including credit and debit card
numbers and other personally-identifiable information in various information systems that we and our franchisees then transfer to third parties with whom
we contract to provide credit card processing services. We also maintain important internal company data, such as personally-identifiable information about
our employees, franchisees and guests and information relating to our operations. Our use of personally-identifiable information is regulated by federal and
state laws, as well as by certain third-party agreements. As privacy and information security laws and regulations change, we may incur additional costs to
ensure that we remain in compliance with those laws and regulations. If our security and information systems are compromised or if our employees or
franchisees fail to comply with these laws, regulations, or contract terms, and this information is obtained by unauthorized persons or used inappropriately,
it could adversely affect our reputation and could disrupt our operations and result in costly litigation, judgments, or penalties resulting from violation of
federal and state laws and payment card industry regulations. A cyber-incident could also require us to notify law enforcement agencies, our guests,
employees or other groups, result in fines or require us to incur expenditures in connection with remediation, require us to pay increased fees to third
parties, result in adverse publicity, loss of sales and profits, or require us to incur other costs, any of which could adversely affect the operation of our
business and results of our operations.
Our and our franchisees’ operations depend upon our ability, and the ability of our franchisees and third-party service providers, as well as franchisees’
third-party service providers, to protect computer equipment and systems against damage from theft, fire, power loss, telecommunications failure, and other
catastrophic or unanticipated events, as well as internal and external security incidents, viruses, denial-of-service attacks, phishing attacks, ransomware
attacks, and other intentional or unintentional disruptions. Because some of these systems are provided by third parties, their continued availability on
acceptable terms cannot be assured. The failure of these systems to remain available or operate effectively, including stemming from maintenance
problems, upgrading, replacing, or transitioning to new platforms, a compromise in security, or other unanticipated problems, could result in interruptions
to or delays in our and our franchisees’ operations or other costly or disruptive remediation activities. Our disaster recovery planning cannot account for all
eventualities. The occurrence of a natural disaster, intentional sabotage, or other unanticipated problems could result in lengthy interruptions in service. In
addition, the implementation of technology changes and upgrades to maintain and upgrade its systems, errors or vulnerabilities in its systems, or damage to
or failure of its systems, could result in interruptions in our and our franchisees’ services and non-compliance with certain laws or regulations, which could
reduce sales, revenues, profits, and damage our business and brand.
If we fail to properly maintain the confidentiality and integrity of our data, including guest credit card, debit card and, bank account information and
other personally identifiable information, our reputation and business could be materially and adversely affected.
In the ordinary course of business, we and our franchisees handle certain forms of highly sensitive personally identifiable information, in information
systems that we maintain and in those maintained by franchisees and third parties with whom we contract to provide services. See “The occurrence of
cyber-incidents, or a deficiency in cybersecurity, could negatively impact our business by causing a
17
disruption to our operations, a compromise or corruption of confidential information, and/or damage to our employee and business relationships, all of
which could lead to loss and harm our business” herein. In addition, we offer a mobile application and rewards program that allows our guests to schedule
their visits and facilitates a contactless experience with self-check-in, which may in the future track other personal information. Some of this data is highly
sensitive in nature and could be an attractive target of a criminal attack by malicious third parties with a wide range of motives and expertise, including
lone wolves, organized criminal groups, “hacktivists,” disgruntled current or former employees, and others. The integrity and protection of guest,
prospective guest and employee data is critical to us.
Despite the security measures we have in place to comply with applicable laws and rules, our facilities and systems, and those of our franchisees and third-
party service providers (as well as their third-party service providers), may be vulnerable to security breaches, acts of cyber terrorism or sabotage,
vandalism or theft, computer viruses, loss or corruption of data, programming or human errors or other similar events. See “The occurrence of cyber-
incidents, or a deficiency in cybersecurity, could negatively impact our business by causing a disruption to our operations, a compromise or corruption of
confidential information, and/or damage to our employee and business relationships, all of which could lead to loss and harm our business” herein.
Furthermore, the size and complexity of our information systems, and those of our franchisees and our third-party vendors (as well as their third-party
service providers), make such systems potentially vulnerable to security breaches from inadvertent or intentional actions by our employees, franchisees or
vendors, or from attacks by malicious third parties. Because such attacks are increasing in sophistication and change frequently in nature, We, our
franchisees and our third-party service providers may be unable to anticipate these attacks or implement adequate preventative measures, and any
compromise of our systems, or those of our franchisees and third-party vendors (as well as their third-party service providers), may not be discovered and
remediated promptly. Changes in consumer behavior following a security breach or perceived security breach, act of cyber terrorism or sabotage,
vandalism or theft, computer viruses, loss or corruption of data or programming or human error or other similar event affecting a competitor, large retailer
or financial institution may materially and adversely affect our business.
Additionally, the handling of personally identifiable information by us, or our franchisees’, businesses are regulated at the federal, state and international
levels as well as by certain industry groups, such as the Payment Card Industry Security Standards Council, the National Automated Clearing House
Association, and individual credit card issuers. Federal, state, international and industry groups may also consider and implement from time to time new
privacy and security requirements that apply to our businesses. Compliance with contractual obligations and evolving privacy and security laws,
requirements and regulations may result in cost increases due to necessary systems changes, new limitations or constraints on our business models and the
development of new administrative processes. They also may impose further restrictions on our handling of personally identifiable information that are
housed in one or more of our franchisees’ databases or those of our third-party service providers. Non-compliance with privacy laws or industry group
requirements or a security breach or perceived non-compliance or breach involving the misappropriation, loss or other unauthorized disclosure of personal,
sensitive or confidential information, whether by us or by one of our franchisees or vendors, could have material adverse effects on us and our franchisees’
business, operations, brand, reputation and financial condition, including decreased revenue, material fines and penalties, litigation, increased financial
processing fees, compensatory, statutory, punitive or other damages, adverse actions against our licenses to do business and injunctive relief by court or
consent order. Despite our efforts, the handling of personally identifiable information may not be in compliance with applicable law, or this information
could be disclosed or lost due to a hacking event or unauthorized access to our information system, or through publication or improper disclosure, any of
which could affect the value of our brand. We maintain cyber risk insurance, but in the event of a significant data security breach, this insurance may not
cover all of the losses that we would be likely to suffer.
We and our franchisees rely heavily on information systems, and any material failure, interruption or weakness may prevent us from effectively
operating our business and damage our reputation.
We and our franchisees increasingly rely on information systems, including point-of-sale processing systems in our centers and other information systems
managed by third parties, to interact with our franchisees and guests and collect, maintain and handle guest information, billing information and other
personally identifiable information, including for the operation of our centers, collection of cash, legal and regulatory compliance, management of its
supply chain, accounting, staffing, payment of obligations, credit and debit card transactions and other processes and procedures. To process payments by
our guests, we use a commercially available third-party point-of-sale system. Unforeseen issues, such as bugs, data inconsistencies, outages, changes in
business processes, and other interruptions with such point-of-sale system in the past have had, and could have an adverse impact on our business in the
future. Additionally, if we move to different third-party systems, or otherwise significantly modifies the point-of-sale system, our operations could be
interrupted. Our ability to efficiently and effectively manage our franchisees and corporate-owned centers depends significantly on the reliability and
capacity of these systems, and any potential failure of these third parties to provide quality uninterrupted service is beyond our control.
Our and our franchisees’ operations depend upon our ability, and the ability of our franchisees and third-party service providers (as well as their third-party
service providers), to protect our computer equipment and systems against damage from physical theft, fire, power loss, telecommunications failure or
other catastrophic events, as well as from internal and external security incidents, viruses, denial-of-service attacks and other disruptions. The failure of
these systems to operate effectively, stemming from maintenance problems, existing systems becoming obsolete, upgrading or transitioning to new
platforms, expanding our systems as it grows, a
18
compromise in security or other unanticipated problems could result in interruptions to or delays in our business and guest service and reduce efficiency in
its operations. In addition, the implementation of technology changes and upgrades to maintain current and integrate new systems may also cause service
interruptions, operational delays due to the learning curve associated with using a new system, transaction processing errors and system conversion delays
and may cause us to fail to comply with applicable laws. If our information systems, or those of our franchisees and third-party service providers (as well
as their third-party service providers), fail and our or our partners’ third-party back-up or disaster recovery plans are not adequate to address such failures,
our revenues and profits could be reduced and the reputation of our brand and our business could be materially adversely affected.
We are subject to a number of risks related to ACH, credit card, debit card, and digital payment options it accepts.
We and our franchisees accept payments through credit card, debit card and digital payment transactions. For such transactions, we and our franchisees pay
interchange and other fees, which may increase over time. An increase in those fees would require us to either increase the prices it charges for its products
or services, which could cause us to lose guests or suffer an increase in its operating expenses, either of which could harm its operating results.
If we or any of our processing vendors have problems with our billing software, or the billing software malfunctions, it could have an adverse effect on our
guest satisfaction and could cause one or more of the major credit card or digital payment companies to disallow our continued use of their payment
products. In addition, if our billing software fails to work properly and, as a result, we and our franchisees do not automatically charge its guests’ bank
accounts, credit cards, debit cards or digital payment provider on a timely basis or at all, we could lose revenue, which would harm our operating results.
If we fail to adequately control fraudulent credit card, debit card and digital payment transactions, we may face civil liability, diminished public perception
of its security measures and significantly higher credit card, debit card and digital payment related costs, each of which could adversely affect our business,
financial condition and results of operations. The termination of our ability to process payments through credit card, debit card or digital payment
transactions would significantly impair our ability to operate our business.
As consumer behavior shifts to use more modern forms of payment, there may be an increased reluctance to use credit cards or debit cards for point of sale
transactions which could result in decreased revenues as consumers choose to give their business to competition with more convenient forms of payment.
We may need to expand our information systems to support newer and emerging forms of payment methods, which may be time-consuming and expensive,
and may not realize a return on its investment.
Changing regulations relating to privacy, information security and data protection could increase our costs, affect or limit how we collect and use
personal information and harm our brands in a manner that adversely affects our business.
The jurisdictions in which we operate are increasingly adopting or revising privacy, information security and data protection laws and regulations (“Privacy
and Data Protection Laws”) that could have a significant impact on our current and planned privacy, data protection and information security related
practices, including our collection, use, sharing, retention and safeguarding of consumer and/or employee information, and some of our current or planned
business activities. This includes increased privacy related legislative and enforcement activity at both the federal level and the state level, including the
implementation of the California Consumer Protection Act (the “CCPA”), which came into effect in January 2020, the California Privacy Rights Act (the
“CPRA”) which will take effect on January 1, 2023, as well as other state data privacy and breach notification laws. The CCPA broadly defines personal
information, provides an expansive meaning to activity considered to be a sale of personal information, and gives California residents expanded privacy
rights and protections, including the right to opt out of the sale of personal information. The CCPA also provides for civil penalties for violations and a
private right of action for certain data breaches. The CPRA expands upon the CCPA by creating additional obligations relating to personal information and
establishing a new enforcement agency dedicated to consumer privacy. Additionally, comprehensive privacy laws akin to the CPRA have recently passed in
Virginia and Colorado, and it is quite possible that other U.S. states, Federal agencies, or the U.S. Congress will follow suit. New data privacy laws have
been proposed in more than half of the states in the United States and in the U.S. Congress, reflecting a trend toward more stringent privacy legislation in
the United States, which trend may accelerate under the current U.S. presidential administration. We, our affiliated entities and our service providers may
need to take measures to ensure compliance with new, evolving and existing requirements contained in the CCPA, the CPRA, and other Privacy and Data
Protection Laws and to address customer concerns related to their rights under any such Privacy and Data Protection Laws. We also may need to continue
to make adjustments to our compliance efforts as more clarification and guidance on the requirements of the CCPA, the CPRA and other Privacy and Data
Protection Laws becomes available. In addition to the foregoing, governments or other regulatory agencies may propose additional standards that apply to
the protection of customer and company information, and our systems may be unable to satisfy changing industry security requirements, applicable
regulations or employee and guest expectations without significant additional capital investments or time, which could have a material adverse effect on
our business and results of operations.
We and our franchisees are required to comply with the Payment Card Industry Data Security Standards (“PCI-DSS”) and card association operating rules.
Due to the number of credit card transactions processed by us and our franchisees, we are required to submit an annual Report on Compliance validating
our ability to satisfy the PCI DSS. If we fail to comply with these rules or requirements, or if our data security systems are breached or compromised, we
may be subject to fines and assessments or lose our ability to accept credit or debit card payments from our consumers. Any failure to comply with the PCI
DSS or other payment card
19
brand requirements could significantly harm our brand, reputation, business, and results of operations. Franchisees are separate businesses, and therefore
are subject to different requirements for documenting PCI compliance, any failure by them to maintain their required level of PCI compliance could result
in loss of personally identifiable information of guests, harm our reputation and result in loss of future revenue. All of these implications could adversely
affect our revenues, results of operations or business and financial condition.
Our level of indebtedness could have a material adverse effect on our ability to generate sufficient cash to fulfill our obligations under such
indebtedness, to react to changes in our business and to incur additional indebtedness to fund future needs.
On August 9, 2021, we entered into a credit agreement (the “2026 Credit Agreement”) consisting of a $180.0 million term loan (the “2026 Term Loan”)
and a $40.0 million revolving credit facility (the “2026 Revolving Credit Facility”). As of December 25, 2021, we had $180.0 million of outstanding
borrowings under the 2026 Term Loan and no outstanding borrowings under the 2026 Revolving Credit Facility. We have also announced our intention to
enter into a whole business securitization where we will issue $400.0 million principal amount of senior fixed-rate term notes and repay amounts
outstanding under the 2026 Credit Agreement. We will also issue $40.0 million principal amount of variable funding notes, which we do not expect to draw
as of the closing of the transaction. For more information, see “Management’s Discussion and Analysis of Financial Condition and Results of Operations.”
If our cash flows and capital resources are insufficient to fund our debt service obligations, we may be forced to reduce or delay investments and capital
expenditures or to sell assets, seek additional capital or restructure or refinance our indebtedness. Our ability to restructure or refinance our current or future
debt will depend on the condition of the capital markets and our financial condition at such time. Any refinancing of our debt could be at higher interest
rates and may require us to comply with more onerous covenants, which could further restrict our business operations. The terms of existing or future debt
instruments may restrict us from adopting some of these alternatives. We cannot assure you that our business will be able to generate sufficient levels of
cash or that future borrowings or other financings will be available to us in an amount sufficient to enable us to service our indebtedness and fund our other
liquidity needs. In addition, our indebtedness under the 2026 Credit Agreement bears and the variable funding notes under our planned whole business
securitization will bear interest at variable rates. Because we have variable rate debt, fluctuations in interest rates may affect our business, financial
condition and results of operations.
Our 2026 Credit Agreement contains financial covenants and other restrictions on our actions that may limit our operational flexibility or otherwise
adversely affect our business, financial condition and results of operations.
The terms of our 2026 Credit Agreement include a number of covenants that limit our ability to (subject to negotiated exceptions), among other things,
incur additional indebtedness or issue preferred stock, incur liens on assets, enter into agreements related to mergers and acquisitions, dispose of assets or
pay dividends and make distributions. The terms of the 2026 Credit Agreement require us to maintain a net leverage ratio that is at or below the one
specified in the agreement governing the facility and a minimum fixed charge coverage ratio. In addition, if we are successful in consummating our
announced whole business securitization, then our senior notes from that securitization will contain certain covenants and restrictions. The terms of our
2026 Credit Agreement and, if the whole business securitization is consummated successfully, the senior notes therefrom may restrict our current and
future operations and could adversely affect our ability to finance our future operations or capital needs. In addition, complying with these covenants may
make it more difficult for us to successfully execute our business strategy and compete against companies that are not subject to such restrictions.
A failure by us to comply with the covenants specified in the 2026 Credit Agreement and, if the whole business securitization is consummated successfully,
the senior notes therefrom, could result in an event of default under the agreement, which would give the lenders the right to terminate their commitments
to provide additional loans under the agreement and to declare all borrowings outstanding under the agreement, together with accrued and unpaid interest
and fees, to be immediately due and payable. If the debt under the agreement were to be accelerated, we may not have sufficient cash or be able to borrow
sufficient funds to refinance the debt or sell sufficient assets to repay the debt, which could adversely affect our business, financial condition and results of
operations.
Our announced whole business securitization financing and the use of proceeds therefrom is subject to important conditions.
Our ability to consummate our recently announced whole business securitization financing is subject to important conditions. No purchasers are currently
committed to invest in the notes we plan to offer. Our ability to successfully consummate the transaction on satisfactory terms or at all is subject to market
conditions, including sufficient interest from investors. We have also announced that we expect to use a portion of the proceeds to pay a one-time special
dividend to our equityholders. Any dividend is subject to the determination of our board of directors and applicable legal restrictions, and we can provide
no assurance regarding the size or timing of any dividend.
Our ability to raise capital in the future may be limited.
Our business and operations may consume resources faster than we anticipate. In the future, we may need to raise additional funds through the issuance of
new equity securities, debt or a combination of both. Additional financing may not be available on favorable terms or at all. If adequate funds are not
available on acceptable terms, we may be unable to fund our capital requirements. If we issue new debt securities, the debt holders would have rights senior
to holders of our common stock to make claims on our assets and the terms of any debt could restrict our operations, including our ability to pay dividends
on our common stock. If we issue additional
20
equity securities or securities convertible into equity securities, existing stockholders will experience dilution and the new equity securities could have
rights senior to those of our common stock. Because our decision to issue securities in any future offering will depend on market conditions and other
factors beyond our control, we cannot predict or estimate the amount, timing or nature of our future offerings. Thus, you bear the risk of our future
securities offerings reducing the market price of our common stock and diluting their interest.
Our failure or our franchisees’ failure to comply with health, employment and other federal, state, local and provincial laws, rules and regulations may
lead to losses and harm our brands.
We and our franchisees are subject to various federal, state, local, provincial and foreign laws and are subject to a variety of litigation risks, including, but
not limited to, guest claims, product liability claims, personal- injury claims, environmental claims, employee allegations of improper termination,
harassment and discrimination, wage and hour claims and claims related to violations of the Americans with Disabilities Act of 1990 (“ADA”), the Family
and Medical Leave Act (“FMLA”) and similar state, local and municipal laws, religious freedom, the Fair Labor Standards Act (“FLSA”), the National
Labor Relations Act (“NLRA”), Title VII of the Civil Rights Act (“Title VII”), the Age Discrimination in Employment Act (“ADEA”), the Dodd-Frank
Act, the Health Care Reform Act, the Electronic Funds Transfer Act, the Payment Card Industry Data Security Standards, franchise laws, ERISA and
intellectual property claims. The successful development and operation of our centers depends to a significant extent on the selection and acquisition of
suitable sites, which are subject to zoning, land use, environmental, traffic and other regulations. Our centers’ operations are also subject to licensing and
regulation by state, local and municipal departments relating to safety standards, federal, state and municipal labor and immigration law (including
applicable equal pay and minimum wage requirements, overtime pay practices, reimbursement for necessary business expense practices, classification of
employees, working and safety conditions and work authorization requirements), federal, state, local and municipal laws prohibiting discrimination and
other laws regulating the design and operation of facilities, such as the ADA, the Health Care Reform Act and applicable human rights and accessibility
legislation, and subsequent amendments.
The operation of our franchise system is also subject to franchise laws and regulations enacted by a number of states and rules promulgated by the U.S.
Federal Trade Commission. Any future legislation regulating franchise relationships may negatively affect our operations, particularly our relationships
with our franchisees.
Failure to comply with new or existing franchise laws and regulations in any jurisdiction or to obtain required government approvals could result in a ban
or temporary suspension on selling franchised centers, which could reduce the franchise fees we collect and corresponding profits, which in turn could
materially and adversely affect our business and results of operations.
In addition to the risk of adverse legislation or regulations being enacted in the future, we cannot predict how existing or future laws or regulations will be
administered or interpreted. Further, we cannot predict the amount of future expenditures that may be required in order to comply with any such laws or
regulations.
We and our franchisees are subject to the FLSA and similar state laws, which govern such matters as time keeping and payroll requirements, minimum
wage, overtime, employee and worker classifications and other working conditions, along with the ADA, FMLA and the Immigration Reform and Control
Act of 1986, various family leave, sick leave or other paid time off mandates and a variety of other laws enacted, or rules, regulations and decisions
promulgated or rendered, by federal, state, local and municipal governmental authorities that govern these and other employment matters, including labor
scheduling, meal and rest periods, working conditions and safety standards. We have experienced and expect further increases in payroll expenses as a
result of federal, state and municipal mandated increases in the minimum wage, and although such increases are not expected to be material, there can be
no assurance that there will not be material increases in the future. In addition, our vendors may be affected by higher minimum wage standards, which
may increase the price of goods and services they supply to our brands.
Companies that operate franchise systems may also be subject to claims under the NLRA, the FLSA, Title VII, the ADEA, the FMLA and state laws for
allegedly being a joint employer with a franchisee. We could face claims from our franchisees’ employees, alleging that we are a joint employer of our
franchisees. Such claims against franchisors are determined on a case-by-case basis with varying outcomes, depending on the facts of each case.
If we were found to be a joint employer of our franchisees’ employees for purposes of the NLRA, we could be liable or held responsible for unfair labor
practices brought by our franchisees’ employees, could be required to conduct collective bargaining negotiations regarding our franchisees’ employees,
could be subject to lawful primary picketing at locations of the joint employer, and could be liable for other NLRA violations of franchisees.
If we were found to be a joint employer of our franchisees’ employees for purposes of the FLSA, we could be held jointly and severally liable for
violations of wage and hour laws, and other FLSA violations of franchisees. Additionally, such franchisee’s employees may attempt to aggregate the
number of hours worked for us and the franchisee and consider it as one employment for determining the number of hours worked in a week, the
employee’s regular rate of pay, and the amount of overtime, if any, due to the employee.
21
If we were found to be a joint employer of our franchisees’ employees for purposes of Title VII or the ADEA, we could be liable or held responsible for
violations of discrimination, harassment, or retaliation of franchisees, and other state and local discrimination violations of franchisees. If we were found to
be a joint employer of our franchisees’ employees for purposes of the FMLA, we could be liable and held responsible for FMLA violations, even if the
employee only informed the franchisee of the employee’s plan to take FMLA leave.
A finding of joint employer (or similar) status could also have other legal implications under various federal, state, and local laws including, but not limited
to, our being held liable for common law torts committed by employees of franchisees.
Future changes in federal, state, or local law, or penalties associated with any failure to comply with legal requirements, could increase the Franchisor’s
labor costs or result in significant additional expense to us and our franchisees, due to required modifications to our business practices, increased litigation,
governmental investigations or proceedings, administrative enforcement actions, fines or civil liability.
Additionally, under federal and state laws, the franchisees may be considered our employees. In particular, there have been recent state law developments
in California. In 2020, the California legislature codified in Assembly Bill 5 (“AB-5”) a three-part test adopted by the California Supreme Court for
determining whether a worker is an independent contractor or employee. Assembly Bill 5 includes specific exemptions for certain types of business
relationships and activities, but the law currently has no exemption specific to franchisor-franchisee relationships. Depending upon the application of AB-
5, franchisors in certain industries could be deemed to be covered by the statute, in which event the franchisees could be deemed to be our employees. If
misclassification claims are successful against or applied to us, we could be liable to the franchisees (and potentially their employees) based upon the rights
and remedies available to employees under the NLRA, the FLSA, Title VII, the ADEA, the FMLA, and state laws, as discussed above. Enactment and
enforcement of various federal, state, local and municipal laws, rules and regulations on immigration and labor organizations may adversely impact the
availability and costs of labor in any of the countries in which we operate. Other labor shortages or increased employee turnover could also increase labor
costs. In addition, vendors may be affected by higher minimum wage standards or availability of labor, which may increase the price of goods and services
they supply to us. Evolving labor and employment laws, rules and regulations could also result in increased exposure on our part for labor and employment
related liabilities that have historically been borne by our franchisees.
These various laws and regulations could lead and have led to enforcement actions, fines, civil or criminal penalties or the assertion of litigation claims and
damages. In addition, improper conduct by our franchisees, employees or agents could damage our reputation and lead to litigation claims, enforcement
actions and regulatory actions and investigations, including, but not limited to, those arising from personal injury, loss or damage to personal property or
business interruption losses, which could result in significant awards or settlements to plaintiffs and civil or criminal penalties, including substantial
monetary fines. Such events could lead to an adverse impact on our financial condition, even if the monetary damage is mitigated by insurance coverage.
Non-compliance by us or our franchisees with any of the foregoing laws and regulations could lead to various claims and reduced profits as set forth in
more detail below under “—Complaints or litigation may adversely affect our business and reputation.”
If products sold by us or our franchisees are found to be defective in labeling or content, our credibility and that of the brands we sell may be harmed,
marketplace acceptance of our products may decrease, and we may be exposed to liability in excess of our products liability insurance coverage and
manufacturer indemnities.
We believe we have built a strong reputation for the quality and breadth of our product and service offerings as part of the total experience that guests enjoy
in our centers. We believe we must protect and grow the value of our brand to continue to be successful in the future. Any incident that erodes guest trust in
or affinity for our brand could significantly reduce the value of either. As we are concerned with the foregoing, we do not control the production process for
the products we sell. We may not be able to identify a defect in a product we purchase from a manufacturer before we offer such product to our franchisees
or for resale. In many cases, we rely on representations of manufacturers and fillers about the products we purchase for resale regarding the composition,
manufacture and safety of the products, as well as the compliance of our product labels with government regulations. Our and our franchisees sale of
certain products exposes us and our franchisees to potential product liability claims, recalls or other regulatory or enforcement actions initiated by federal,
state or foreign regulatory authorities or through private causes of action. Such claims, recalls or actions could be based on allegations that, among other
things, the products sold by us or our franchisees are misbranded, contain contaminants or impermissible ingredients, provide inadequate instructions
regarding their use or misuse, or include inadequate warnings concerning flammability or interactions with other substances. Claims against us or our
franchisees could also arise as a result of the misuse by purchasers of such products or as a result of their use in a manner different than the intended use.
We and our franchisees may be required to pay for losses or injuries actually or allegedly caused by the products we sell and to recall any product we sell
that is alleged to be or is found to be defective. Furthermore, such claims could have an adverse impact on our and franchisees reputation.
Any actual defects or allegations of defects in products sold by us or our franchisees could result in adverse publicity and harm our credibility or the
credibility of the manufacturer, which could adversely affect our business, financial condition and results of operations. Although we may have
indemnification rights against the manufacturers of many of the products we distribute and rights as an “additional insured” under the manufacturers’
insurance policies, it is not certain that any manufacturer or insurer will be
22
financially solvent and capable of making payment to any party suffering loss or injury caused by products sold by us or our franchisees or if all losses
would be covered by such indemnification rights or insurance policies. If we are forced to expend significant resources and time to resolve such claims or
to pay material amounts to satisfy such claims, it could have an adverse effect on our business, financial condition and results of operations.
Our operations and financial performance has been affected by, and is expected to continue to be affected by, the COVID-19 pandemic.
The global crisis resulting from the spread of COVID-19 has disrupted, and continues to significantly disrupt, local, regional, and global economies and
businesses in the locations in which we operate, as well as adversely affected workforces, guests, consumer sentiment, economies and financial markets,
and has impacted our financial results. Because personal-care services were generally not deemed “essential” by federal, state and local governmental
authorities in the United States, all of our centers temporarily closed during the ongoing COVID-19 pandemic. In accordance with applicable guidelines
from governmental authorities and the Center for Disease Control, our centers reopened as stay-at-home orders lifted on a state-by-state and county-by-
county basis with capacity limitations. As a result of the ongoing COVID-19 pandemic, our centers also experienced reduced guest traffic and sales volume
due to changes in consumer behavior as individuals decreased spending on discretionary spending and practiced social distancing and other behavioral
changes mandated by governmental authorities or independently undertaken out of an abundance of caution resulting in same-store sales in 2020
decreasing to -36%. While same-store sales increased 6.7% in 2021 as compared to 2019, future spikes in COVID-19 infections could materially and
adversely affect the ability of franchisees to pay, or disrupt the timely payment of, amounts owed to us or decrease the profitability of our centers.
The COVID-19 pandemic has the potential to cause a disruption in our supply chain and may adversely impact economic conditions in the United States.
These and other disruptions, as well as poor economic conditions generally, may lead to a decline in the sales and operating results of our centers. In
addition, the continuation of the COVID-19 pandemic may adversely affect the economies and financial markets of United States and could result in a
sustained reduction in the demand for our services and products, longer payment cycles, slower adoption of new products and services and/or increased
price competition, as well as a reduction of workforce at our centers. A decline in the sales and operating results of our centers could in turn materially and
adversely affect our ability to pursue our growth strategy. Each of these results would reduce our future sales and profit margins, which in turn could
materially and adversely affect our business and results of operations.
While COVID-19 negatively impacted our business and results of operations during fiscal year 2020, our results of operations improved in 2021. See
“Business—Our Recent Financial Performance—Performance in 2020 and During the COVID-19 Pandemic.” and "Business- Our Recent Financial
Performance- Performance during 2021." The full extent to which COVID-19 impacts us will depend on future developments, including the duration,
spread and severity of the pandemic, the extent of additional outbreaks, the effectiveness or duration of measures intended to contain or mitigate the spread
of COVID-19 or prevent future outbreaks, and the effect of these developments on overall demand in the waxing service and personal- care industries in
the geographic regions in which we operate, all of which are highly uncertain and difficult to accurately predict. These uncertainties may increase
variability in our future results of operations and adversely impact our ability to accurately forecast changes in our business performance and financial
condition in future periods. If we are not able to respond to and manage the impact of such events effectively, our business and results of operations could
be adversely affected.
Adverse economic conditions or a global debt crisis could adversely affect our business.
Our financial condition and results of operations are impacted by global markets and economic conditions over which neither we nor our franchisees have
control. An economic downturn may result in a reduction in the demand for our services and products, longer payment cycles, slower adoption of new
products and services and/or increased price competition. Declining economic conditions may cause our guests to defer seeking waxing services or other
personal-care services. As a result, poor economic conditions may lead to a decline in the sales and operating results of our centers, which could in turn
materially and adversely affect the ability of franchisees to pay franchise royalties or amounts owed to us, or have a material adverse impact on our ability
to pursue our growth strategy. Each of these results would reduce our profits, which could materially and adversely affect our business and results of
operations.
Changes in tax laws may adversely affect us, and the Internal Revenue Service (the “IRS”) or a court may disagree with tax positions taken by EWC
Ventures or us, which may result in adverse effects on our financial condition or the value of our common stock.
The Tax Cuts and Jobs Act (the “TCJA”), enacted on December 22, 2017, significantly affected U.S. tax law, including by changing how the U.S. imposes
tax on certain types of income of corporations and by reducing the U.S. federal corporate income tax rate to 21%. It also imposed new limitations on a
number of tax benefits, including deductions for business interest, use of net operating loss carry forwards, taxation of foreign income, and the foreign tax
credit, among others. The CARES Act, enacted on March 27, 2020, in response to the COVID-19 pandemic, further amended the U.S. federal tax code,
including in respect of certain changes that were made by the TCJA, generally on a temporary basis. There can be no assurance that future tax law changes
will not increase the rate of the corporate income tax significantly, impose new limitations on deductions, credits or other tax benefits, or make other
changes that may adversely affect our business, cash flows or financial performance. In addition, the IRS has yet to issue guidance on a number of
23
important issues regarding the changes made by the TCJA and the CARES Act. In the absence of such guidance, we will take positions with respect to a
number of unsettled issues. There is no assurance that the IRS, any other taxing authority or a court will agree with the positions taken by us, in which case
tax penalties and interest may be imposed that could adversely affect our business, cash flows or financial performance.
Our tax position could also be impacted by changes in accounting principles, changes in U.S. federal, state, or international tax laws applicable to corporate
multinationals, other fundamental law changes currently being considered by many countries, including the United States, and changes in taxing
jurisdictions' administrative interpretations, decisions, policies, and positions. Any of the foregoing changes could have a material adverse impact on our
results of operations, cash flows, and financial condition. For example, the Biden administration proposed to increase the U.S. corporate income tax rate
from 21% to 28%, increase U.S. taxation of international business operations, and impose a global minimum tax. Any of these developments or changes in
federal, state, or international tax laws or tax rulings could adversely affect our effective tax rate and our operating results.
Our future effective tax rates could be subject to volatility or adversely affected by a number of factors, including: (i) changes in the valuation of our
deferred tax assets and liabilities, (ii) expected timing and amount of the release of any tax valuation allowance, (iii) expiration of or detrimental changes in
research and development tax credit laws, (iv) tax effects of stock-based compensation, and (v) costs related to intercompany restructurings. We may be
subject to audits of our income, sales and other transaction taxes by U.S. federal and state tax authorities. Outcomes from these audits could have an
adverse effect on our operating results and financial condition.
Complaints or litigation may adversely affect our business and reputation.
We may be subject to claims, including class action lawsuits, filed by our guests, franchisees, employees, suppliers, landlords, governmental authorities and
others in the ordinary course of business, including as a result of violations of the laws set forth above under “—Our failure or our franchisees’ failure to
comply with health, employment, and other federal, state, and local laws, rules and regulations may lead to losses and harm our brands”. Significant claims
may be expensive to defend and may divert time and resources away from our operations, causing adverse impacts to our operating results. In addition,
adverse publicity related to litigation could negatively impact the reputation of our brands, even if such litigation is not valid, or a substantial judgment
against us could negatively impact the reputation of our brands, resulting in further adverse impacts to results of operations. Franchisees are subject to
similar litigation risks.
In the ordinary course of business, we will be, from time to time, the subject of complaints or litigation from franchisees, which could relate to alleged
breaches of contract or wrongful termination under the franchise documents. These claims may also reduce the ability of franchisees to enter into new
franchise agreements with us. In addition, litigation against a franchisee or their affiliates or against a corporate-owned center by third parties, whether in
the ordinary course of business or otherwise, may include claims against us by virtue of our relationship with the franchisee or corporate-owned center,
including, without limitation, for allegedly being a joint employer with a franchisee, resulting in vicarious liability for acts and omissions at centers over
which we have little or no control over day-to-day operations. Litigation may lead to a decline in the sales and operating results of our centers and divert
our management resources regardless of whether the allegations in such litigation are valid or whether we are liable.
Further, we may be subject to employee, franchisee and other claims in the future based on, among other things, discrimination, harassment, wrongful
termination and wage, rest break and meal break issues, including those relating to overtime compensation. We have been subject to these types of claims
in the past, and if one or more of these claims were to be successful or if there is a significant increase in the number of these claims, our business, financial
condition and operating results could be harmed.
Certain governmental authorities and private litigants have recently asserted claims against franchisors for provisions in their franchise agreements which
restrict franchisees from soliciting and/or hiring the employees of other franchisees or the applicable franchisor. Claims against franchisors for such “no-
poaching” clauses include allegations that these clauses violate state and federal antitrust and unfair practices laws by restricting the free movement of
employees of franchisees or franchisors (including both corporate employees and the employees of corporate-owned centers), thereby depressing the wages
of those employees. We have historically had no-poaching clauses in our franchise agreements. In 2018, the Attorney General of the State of Washington
issued civil investigative demands to a number of franchisors seeking information concerning no-poaching clauses in their franchise agreements. In
September 2018, we received a civil investigative demand requesting information concerning our use of no-poaching clauses. To resolve objections to these
clauses raised by the Washington Attorney General, we entered into an Assurance of Discontinuance (“AOD”) with the state agreeing to no longer include
such provision in any U.S. franchise agreement or renewal franchise agreement signed after the date of the AOD, to not enforce any such provisions in any
of our existing franchise agreements and to notify our franchisees of these changes. In the case of Washington-based franchisees, we agreed to seek
amendments to their franchise agreements removing the no-poaching clauses. No fines or other monetary penalties were assessed against us. Any adverse
results in any cases or proceedings that may be brought against us by any governmental authorities or private litigants may materially and adversely affect
our business and results of operations.
24
We are subject to payment-related risks.
For our and our franchisees’ sales to our guests, we and our franchisees accept a variety of payment methods, including credit cards, debit cards, electronic
funds transfers and electronic payment systems. Accordingly, we are, and will continue to be, subject to significant and evolving regulations and
compliance requirements, including obligations to implement enhanced authentication processes that could result in increased costs and liability, and
reduce the ease of use of certain payment methods. For certain payment methods, including credit and debit cards, as well as electronic payment systems,
we pay interchange and other fees, which may increase over time. We rely on independent service providers for payment processing, including credit and
debit cards. If these independent service providers become unwilling or unable to provide these services to us or if the cost of using these providers
increases, our business could be harmed. We are also subject to payment card association operating rules and agreements, including data security rules and
agreements, certification requirements and rules governing electronic funds transfers, which could change or be reinterpreted to make it difficult or
impossible for us to comply. If we fail to comply with these rules or requirements, or if our data security systems are breached or compromised, we may be
liable for losses incurred by card issuing banks or our guests, subject to fines and higher transaction fees, lose our ability to accept credit or debit card
payments from our guests, or process electronic fund transfers or facilitate other types of payments. Any failure to comply with the foregoing rules or
requirements could harm our brand, reputation, business and results of operations.
Our business is subject to seasonality.
Our results are subject to seasonality fluctuations in that services are typically in higher demand in periods leading up to holidays and the summer season.
The resulting demand trend yields higher results in the second and fourth quarter of our fiscal year. In addition, our quarterly results may fluctuate
significantly, because of several factors, including the timing of center openings, price increases and promotions, and general economic conditions.
Seasonal changes may continue to impact the demand for our waxing services and products, leading to continued fluctuations in quarterly results as a result
of many factors. Timing of consumer purchases will vary each year and sales can be expected to shift from one quarter to another. In addition, unusual
fluctuations in demand for our services and products could reduce our and our franchisees’ sales and profit margins, which in turn may materially and
adversely affect our business and results of operations.
Higher health care costs could adversely affect our results of operations.
Franchisees may, and in certain cases are required to, offer access to health care benefits to certain of their employees and we may offer access to health
care benefits to certain of our employees at corporate-operated centers. Changes in legislation, including government-mandated health care benefits under
the Patient Protection and Affordable Care Act (“Health Care Reform Act”) and changes in market practice may cause us and our franchisees to provide
health insurance to employees on terms that differ significantly from those of existing programs, and may increase the cost of health care benefits.
Additionally, some states and localities have passed state and local laws mandating the provision of certain levels of health benefits by some employers. We
and our franchisees may also be subject to increased health care costs as a result of litigation requiring the payment of additional health care costs.
We continue to review any potential amendments to the Health Care Reform Act to evaluate the potential impact of any amendment on our business, and to
accommodate various parts of the laws. Although we cannot currently determine with certainty what long-term impact any such potential amendment will
have on us, it is expected that costs will increase over the long term, as well as for franchisees and/or third-party suppliers and service providers. There are
no assurances that a combination of cost management and price increases can accommodate all of the costs associated with compliance with the Health
Care Reform Act or any potential amendment to such legislation. Increased health care costs could have a material adverse effect on our results of
operations, business, and financial condition.
Insurance coverage may not be adequate, and increased self-insurance and other insurance costs could adversely affect our results of operations.
We and our franchisees maintain insurance, and these insurance policies may not be adequate to protect us from liabilities that we incur in our business.
Certain extraordinary hazards, for example, may not be covered, and insurance may not be available (or may be available only at prohibitively expensive
rates) with respect to many other risks. Moreover, any loss incurred could exceed policy limits, and policy payments made to us or our franchisees may not
be made on a timely basis. Any such loss or delay in payment could lead to a decline in the sales and operating results of our centers, which could in turn
have a material and adverse effect on our revenues, results of operations, business, and financial condition.
In addition, in the future, insurance premiums may increase and we and our franchisees may not be able to obtain similar levels of insurance on reasonable
terms, or at all. Although we seek to manage our claims to prevent increases, such increases can occur unexpectedly and without regard to our efforts to
limit them. If such increases occur, our centers may be unable to pass them along to our guests through product or service price increases, resulting in
decreased profitability, which could have a material adverse effect on our business and results of operations.
25

In the event that liability to third parties arises, to the extent losses experienced by such third parties are either not covered by the franchisee’s or our
insurance or exceed the policy limits of the franchisee’s or our insurance, such parties could seek to recover their losses from us, whether or not they are
legally or contractually entitled to do so, which could increase litigation costs or result in liability for us. Additionally, a substantial unsatisfied judgment
could result in the bankruptcy of one or more of our operating entities, which could have a material adverse effect on our results of operations, business,
and financial condition.
Risks Relating to the Franchisees
Nearly all of our centers are owned and operated by franchisees and, as a result, we are highly dependent upon our franchisees.
While the franchise agreements are designed to maintain brand consistency, the high percentage of our centers owned by franchisees may expose us to risks
not otherwise encountered if we had owned and controlled the centers. In particular, we are exposed to the risk of defaults or late payments by franchisees
of franchisee payments. Other risks include limitations on enforcement of franchise obligations due to bankruptcy or insolvency proceedings; unwillingness
of franchisees to support marketing programs and strategic initiatives; inability to participate in business strategy changes due to financial constraints;
inability to meet rent obligations on subleases; failure to operate the centers in accordance with required standards; failure to report sales information
accurately; efforts by one or more large franchisees or an organized franchise association to cause poor franchise relations; and failure to comply with
quality and safety requirements that result in potential losses even when we are not legally liable for a franchisee’s actions or failure to act. Although we
believe that our current relationships with franchisees are generally good, there can be no assurance that we will maintain strong franchise relationships.
Our dependence on franchisees could adversely affect our business and financial condition, our reputation, and our brands.
It is important for us and our franchisees to attract, train, and retain talented wax specialists and managers.
In addition to the guest experience in our centers, guest loyalty is also dependent upon the wax specialists who serve our guests. We have developed a
specialized and brand specific training program for our wax specialists. Our ability to hire, train and retain qualified, licensed wax specialists is key to a
supportive guest experience that creates repeat visits. In order for our franchisees to profitably grow our business and our brand, it is important to
adequately staff our centers. Because the OOH waxing industry is highly fragmented and comprised of many independent operators, the market for wax
specialists is typically highly competitive. In addition, increases in minimum wage requirements may impact the number of wax specialists considering
careers outside the waxing industry. In some markets, we and our franchisees have experienced a shortage of qualified wax specialists. Offering
competitive wages, benefits, education and training programs are important elements to attracting and retaining qualified wax specialists. In addition, we
have observed that some wax specialists are not comfortable coming back to the center environment during COVID-19. If our corporate- owned centers or
franchisees are not successful in attracting, training and retaining wax specialists or in staffing our centers, our same-store sales or the performance of our
franchise business could experience periods of variability or sales could decline and our results of operations could be adversely affected.
Franchisees are operating entities exposed to risk.
Franchisees, as operating entities, may be natural persons or legal entities. Under certain of the franchise documents, franchisee entities are not required to
be limited-purpose entities, making them potentially subject to business, credit, financial and other risks, which may be unrelated to the operations of our
centers. These unrelated risks could materially and adversely affect a franchisee and its ability to make its franchisee payments in full or on a timely basis.
A decrease in franchisee payments could have a material adverse effect on our business and results of operations.
Changes in labor costs, other operating costs, such as commodity costs, interest rates and inflation could adversely affect our results of operations.
Increases in employee wages, benefits, and insurance and other operating costs such as commodity costs, legal claims, insurance costs and costs of
borrowing could adversely affect operations and administrative expenses at our centers. A significant number of the employees at our franchisee and
corporate-owned centers are paid at rates impacted by the applicable minimum wage. To the extent implemented, federal, state and local proposals that
increase minimum wage requirements or mandate other employee matters could materially increase labor and other costs for our franchisees. Several states
in which we operate have approved minimum wage increases that are above the federal minimum wage. As more jurisdictions implement minimum wage
increases, we expect our franchisees’ labor costs will continue to increase. Operating costs are susceptible to increases as a result of factors beyond our
control, such as weather conditions, natural disasters, disease outbreaks, global demand, product recalls, inflation, civil unrest, tariffs and government
regulations.
Any increase in such costs for our centers could reduce our and our franchisees’ sales and profit margins if we choose not, or are unable, to pass the
increased costs to our guests. In addition, increases in interest rates may impact land and construction costs and the cost and availability of borrowed funds
and leased centers, and thereby adversely affect our and our franchisees’ ability to finance the development of additional centers and maintenance of
existing centers. Inflation can also cause increased commodity, labor and benefits costs which could reduce the profitability of our centers. Increases in
labor costs could make it difficult to find new franchisees. Any of the foregoing increases could adversely affect our and our franchisees’ business and
results of operations.
26

We may not be able to retain franchisees or maintain the quality of existing franchisees.
Many of our franchised centers are heavily reliant on its franchisee, many of whom are individuals who have numerous years of experience addressing a
broad range of concerns and issues relevant to its business. We attempt to retain such franchisees by providing them with competitive franchising
opportunities. However, we cannot guarantee the retention of any, including the top-performing, franchisees in the future, or that we will maintain the
ability to attract, retain, and motivate sufficient numbers of franchisees of the same caliber, and the failure to do so could materially and adversely affect
our business and results of operations. In the event a franchisee leaves our franchise and a successor franchisee is not found, or a successor franchisee that
is approved is not as successful in operating the center as the former franchisee or franchisee principal, the sales of the center may be impacted and the
corresponding royalty and other fees we collect.
The quality of existing franchisee operations may be diminished by factors beyond our control, including franchisees’ failure or inability to hire or retain
qualified managers, wax specialists, and other personnel or franchisees experiencing financial difficulty, including those franchisees that become over-
leveraged. Training of managers, wax specialists, and other personnel may be inadequate. These and other such negative factors could reduce the
franchisees’ revenues, could impact payments under the franchise documents and could delay a new center’s ability to reach profitability in line with our
maturation curve, any of which could have a material adverse effect on our business and results of operations.
Our center development plans under development agreements may not be implemented effectively by franchisees.
We rely heavily on franchisees to develop our centers. Development involves substantial risks, including the following:
• the availability of suitable locations and terms for potential development sites;
• the availability of prospective franchisees who meet our recruiting criteria;
• the ability of franchisees to fulfill their commitments to build new centers in the numbers and the time frames specified in their development
agreements;
• the availability of financing, at acceptable rates and terms, to both franchisees and third-party landlords, for center development;
• delays in obtaining construction permits and in completion of construction;
• developed properties not achieving desired revenue or cash flow levels once opened;
• competition for suitable development sites;
• changes in governmental rules, regulations, and interpretations (including interpretations of the requirements of the ADA); and
• general economic and business conditions.
There is no assurance that franchisees’ development and construction of centers will be completed, or that any such development will be completed in a
timely manner. There is no assurance that present or future development plans will perform in accordance with expectations.
The opening and success of our centers depend on various factors, including the demand for our centers and the selection of appropriate franchisee
candidates, the availability of suitable sites, the negotiation of acceptable lease or purchase terms for new centers, costs of construction, permit issuance and
regulatory compliance, the ability to meet construction schedules, the availability of financing and other capabilities of franchisees. There is no assurance
that we will be able to identify, recruit or contract with suitable franchisees in our target markets on a timely basis or at all or that selected franchisees
planning the opening of centers will have the ability or sufficient access to financial resources necessary to open and operate the centers required by their
agreements. It cannot be assured that franchisees will successfully participate in our strategic initiatives or operate centers in a manner consistent with our
concepts and standards. If we are unable to recruit suitable franchisees or if franchisees are unable or unwilling to open new centers as planned, our growth
may be slower than anticipated, which could materially adversely affect our ability to increase our revenue and our business, financial condition and results
of operations.
Franchisee changes in control may cause complications.
The franchise documents prohibit “changes in control” of a franchisee without our consent. In the event we provide such consent, there is no assurance that
a successor franchisee would be able to perform the former franchisee’s obligations under such franchise documents or successfully operate its franchise. In
the event of the death or disability of a franchisee or the principal of a franchisee entity, the personal representative of the franchisee or principal of a
franchisee entity may not find an acceptable transferee. In the event that an acceptable successor franchisee is not identified, the franchisee would be in
default under its franchise documents or otherwise not be able to comply with its obligations under the franchise documents and, among other things, the
franchisee’s right to operate its franchise could be terminated. If a successor franchisee is not found, or a successor franchisee that is approved is not as
27
successful in operating the center as the former franchisee or franchisee principal, the sales of the center would be impacted and could adversely impact our
business and results of operations.
We may be liable for certain obligations of our franchisees.
We and our franchisees offer guests the option to purchase services in pre-paid packages, which may or may not be redeemed later and may be redeemed at
a center different from the center of purchase. Our franchise system includes a clearing house process that we control, where amounts received for pre-paid
services are applied to the center where the services are redeemed as opposed to where they may have been purchased. If a franchisee that has sold a pre-
paid package ceases to operate, we may decide to pay amounts to franchisees at other centers where the package is redeemed to minimize any associated
reputational damage. As a result, if multiple franchisees cease to operate, we may face significant payment obligations, which could materially and
adversely affect our business and results of operations.
Franchise documents are subject to termination and non-renewal.
The franchise documents are subject to termination by us in the event of a default generally after expiration of applicable cure periods. Under certain
circumstances, including unauthorized transfer or assignment of the franchise, breach of the confidentiality provisions or health and safety violations, a
franchise document may be terminated by the franchisor under the franchise document upon notice without an opportunity to cure. Generally, the default
provisions under the franchise documents are drafted broadly and include, among other things, any failure to meet operating standards and actions that may
threaten our intellectual property.
In addition, as of December 25, 2021, 223 franchised centers have terms that will expire by December 31, 2022. In such cases, the franchisees may renew
the franchise term and receive a “successor” franchise agreement for one additional successive term of ten years. Such option, however, is contingent on
the franchisee’s execution of our then-current form of franchise agreement (which may include increased franchise royalty rates, marketing fees and other
costs or requirements), the satisfaction of certain conditions (including, among other things, compliance with the terms of the existing agreement, the
payment of capital expenditures as necessary to maintain uniformity with our then-current standards, and others), compliance with any training
requirements and the payment of a renewal fee. If a franchisee is unable or unwilling to satisfy any of the foregoing conditions, such franchisee’s expiring
franchise agreement and the related franchisee payments will terminate upon expiration of the term of the franchise agreement unless we decide to
restructure the franchise documents in order to induce such franchisee to renew the franchise agreement.
Terminations or restructurings of franchise documents could reduce franchise payments or require us to incur expenses to solicit and qualify new
franchises, which in turn may materially and adversely affect our business and results of operations.
Our same-store sales and quarterly financial performance may fluctuate for a variety of reasons.
Our same-store sales and quarterly results of operations have fluctuated in the past and we expect them to continue to fluctuate in the future. A variety of
factors affect our same-store sales and quarterly financial performance, including:
• a portion of a typical new center’s sales (or sales we make over our e-commerce channels) coming from guests who previously visited our
other existing centers;
• the ability of new centers to reach profitability and maturity in line with our and our franchisees’ expectations;
• the timing and effectiveness of our marketing and promotional activities and those of our competitors;
• the effects of severe weather events or other natural disasters;
• fluctuations in the cost to us of products and services we sell;
• changes in our merchandising strategy or mix;
• center closures in response to state or local regulations due to the COVID-19 pandemic or other health concerns; and
• worldwide economic conditions and, in particular, the retail sales environment in the United States.
Accordingly, our results for any one fiscal quarter are not necessarily indicative of the results to be expected for any other quarter, and may even decrease,
which could have a material adverse effect on our business, financial condition and results of operations.
Our current centers may become demographically unattractive, and attractive new centers may not be available for a reasonable price, if at all, which
could adversely affect our business.
The success of any of our centers depends in substantial part on its location. There can be no assurance that our current centers will continue to be attractive
as demographic patterns and trade areas change. For example, neighborhood or economic conditions where our centers are located could decline in the
future, thus resulting in potentially reduced sales. In addition, rising real estate prices in some areas may restrict our ability or our franchisees’ ability to
purchase or lease new desirable locations. If desirable locations cannot be obtained at reasonable prices, our ability to execute our growth strategies could
be adversely affected, and we may be affected by
28
declines in sales as a result of the deterioration of certain locations, each of which could materially and adversely affect our business and results of
operations.
Opening new centers in close proximity may negatively impact our existing centers’ revenues and profitability.
As of December 25, 2021, we and our franchisees operated 853 centers in 44 states and the District of Columbia. We and our franchisees plan to open
many new centers in the future, some of which will be in existing markets and may be located in close proximity to centers already in those markets.
Although the franchise agreements provide franchisees with varying degrees of exclusive areas and territory exclusivity, these territories may be relatively
small, and overall there is a geographic concentration of our centers in certain states, regions and cities. Opening new centers in close proximity to existing
centers may attract some guests away from those existing centers, which may lead to diminished revenues and profitability for us and our franchisees rather
than increased market share. In addition, as a result of new centers opening in existing markets and because older centers will represent an increasing
proportion of our center base over time, our same-store sales increases may be lower in future periods than they have been historically.
Furthermore, economic conditions in particular areas may have a disproportionate impact on our business. Our centers are most concentrated in California,
Texas, New York, New Jersey and Florida. No single state accounted for more than 14% of system-wide sales and the top three states represented less than
36% of system-wide sales for the year ended December 25, 2021; however, adverse economic conditions in states, regions or cities that contain a high
concentration of our centers could have a material adverse impact on our sales and profit margins in the future, which in turn could materially and
adversely affect our business and results of operations.
Risks Relating to our Suppliers and Distributors
We depend on a limited number of key suppliers, including international suppliers, to deliver high-quality products at prices similar to historical levels.
We depend on two key suppliers, Perron Rigot, SAS and Grupo DRV—Phytolab S.L., to provide our Comfort Wax to our franchisees and one key supplier,
Batallure Beauty LLC, to provide branded retail products to our franchisees. Our success is dependent on, among other things, our continuing ability to
offer our services and products at prices similar to historical levels. We currently have a long-term contract with only one of the wax suppliers. Our
suppliers may be adversely impacted by economic weakness and uncertainty, such as increased commodity prices, increased fuel costs, tight credit markets
and various other factors. In such an environment, our suppliers may seek to change the terms on which they do business with us in order to lessen the
impact of any current and future economic challenges on their businesses or may cease or suspend operations. If we are forced to renegotiate the terms
upon which we conduct business with our suppliers or find alternative suppliers to provide key products or services, it could adversely impact the profit
margins at our and our franchised centers, which in turn could materially and adversely affect our business and results of operations.
Economic weakness and uncertainty may force suppliers to seek financing in order to stabilize their businesses, restructure or cease operations completely.
In addition, some of our key suppliers have significant operations overseas outside of the markets in which we operate, which could expose us to events in
the countries of those suppliers’ operations, including government intervention, increased tariffs and shipping costs and foreign currency fluctuation. For
instance, if products from suppliers with overseas operations become subject to tariffs, we may be unable or unwilling to offset the financial impact of these
tariffs through price increases to our guests. Moreover, if a key supplier suspends or ceases operations, or if one or more of our agreements with a key
supplier (for example, a supplier of wax) is terminated, then our remaining suppliers may not be able to cover a potential supply shortfall and meet our
supply demands, and we and our franchisees may have difficulty keeping our respective centers fully supplied as a result. If we and our franchisees were
forced to suspend one or more services offered to our guests, that could have a significant adverse impact on our sales and profit margins and the royalty
revenue we collect from franchisees, which in turn could materially and adversely affect our business and results of operations.
Changes in supply costs could adversely affect our results of operations.
The operation of our franchisees and corporate-owned centers requires large quantities of supplies for waxing and the other personal-care services we
provide. Our success depends in part on our ability to anticipate and react to changes in supply costs, and we are susceptible to increases in primary and
secondary supply costs as a result of factors beyond our control. These factors include general economic conditions, significant variations in supply and
demand, seasonal fluctuations, pandemics, weather conditions, fluctuations in the value of currencies in the markets in which we operate, commodity
market speculation, changes in raw materials costs and government regulations. Higher supply costs could reduce our profits, which in turn may materially
and adversely affect our business and results of operations. This volatility could also cause us and our franchisees to consider changes to our product
delivery strategy and result in adverse adjustments to pricing of our services.
Decreases in our product sourcing revenue could adversely affect our results of operations.
We supply our franchisees and corporate-owned centers certain products required to operate applicable centers. Our franchisees are required to purchase
waxing and other European Wax Center branded products from us. While it is our expectation that we will benefit from product sourcing income and
pricing arrangements, there can be no assurance that such income and arrangements will
29
continue, be renewed or replaced. Our failure to maintain our current product sourcing income could have a material adverse effect on our sales and profit
margins, which in turn could materially and adversely affect our business and results of operations. We currently purchase our wax that is used on-site for
services at our centers from two large wax suppliers at negotiated prices based on our scale. Our failure to negotiate beneficial terms in the future could
have a material adverse effect on our sales and profit margins. Decreases in the volume of our purchases by or increases in costs of products, labor or
shipping could have a material adverse effect on our sales and profit margins.
Supply chain shortages and interruptions could adversely affect our business.
We and our franchisees are dependent upon frequent deliveries of wax and other personal-care supplies that meet our quality specifications. Shortages or
interruptions in the supply of wax and other personal-care supplies caused by unanticipated demand, problems in production or distribution, acts of
terrorism, financial or other difficulties of suppliers, labor actions, inclement weather, natural disasters such as floods, drought and hurricanes, outbreak of
disease, including coronavirus and pandemics, or other conditions could adversely affect the availability, quality and cost of supplies for such products,
which could lower our revenues, increase operating costs, damage brand reputation and otherwise harm our business and the businesses of our franchisees.
Such shortages or interruptions could reduce our sales and profit margins and the royalty revenues we collect from franchisees which in turn may
materially and adversely affect our business and results of operations.
Operational failure at one of the distribution centers that supply our centers would impact our ability to distribute products.
We rely on three distribution centers to supply our franchisees and corporate-owned centers with retail products to sell and products used during waxing
services and pre- and post-treatment services. If there were a technology failure, natural disaster or other catastrophic event that caused one of the
distribution centers to be inoperable, it would cause a disruption in our business and could negatively impact our revenues. Furthermore, increases in the
cost of storing our products at these distribution centers or delivering products to and from these distribution centers, either as a result of operational
changes or otherwise, could materially and adversely affect our profit margins.
Risks Relating to Intellectual Property
Our success and the success of our franchisees depends on the adequate protection of our intellectual property and litigation to enforce our intellectual
property rights may be costly.
Our intellectual property is material to the conduct of our business. Our success depends on our and our franchisees’ continued ability to use our
intellectual property and on the adequate protection and enforcement of such intellectual property. We rely on a combination of trademarks, service marks,
copyrights, patents, trade secrets and similar intellectual property rights to protect our brands. The success of our business strategy depends, in part, on our
continued ability to use our existing trademarks and service marks in order to capitalize on their name recognition, increase brand awareness and further
develop our branded services and products in both existing and new markets. There can be no assurance that the steps we take to protect, maintain or
enforce our rights in our intellectual property will be adequate, or that third parties will not infringe, dilute, tarnish, misappropriate or violate our
intellectual property. If any of our efforts to protect our intellectual property is not adequate, or if any third party infringes, misappropriates or violates our
intellectual property, the value of our brands may be harmed. As a result, if we are unable to successfully protect, maintain, or enforce our rights in our
intellectual property, there could be a material adverse effect on our business and results of operations. Such a material adverse effect could result from,
among other things, consumer confusion, dilution of the distinctiveness of our brands, tarnishment of the goodwill associated with our brands, an inability
to obtain registered trademarks in new jurisdictions or for new or expanded good and services, or increased competition from unauthorized users of our
brands, each of which may result in decreased revenues and a corresponding decline in profits. In addition, to the extent that we do, from time to time,
institute litigation to enforce our intellectual property rights, such litigation could result in negative publicity and substantial costs and diversion of
resources and could negatively affect profits, regardless of whether we are able to successfully enforce such rights.
If we are unable to adequately protect our intellectual property, the strength of our brand may be weakened, and our business could be harmed
significantly.
Our brand is essential to the success and competitive position of our business. We have intellectual property rights, such as our numerous trademark and
service mark registrations for the “European Wax Center”, “EWC”, “Strut 365”, “Wax Pass”, and “Comfort Wax” name and related logos. We intend to
actively enforce and defend such intellectual property and, if violations are identified, to take appropriate action to preserve and protect them. However, we
cannot be sure that we will be able to successfully enforce our rights under such trademarks or other intellectual property. Moreover, there can be no
assurance that: (i) using our intellectual property has not, does not, or will not, violate others’ intellectual property, (ii) the registrations of such intellectual
property would be upheld if enforced or challenged, or (iii) we would not be prevented from using our trademarks or other intellectual property in
jurisdictions or for products or services in which others might have already established prior intellectual property rights.
We also possess certain proprietary product specifications, franchisee materials, vendor lists, cost information, market research and marketing strategies,
training programs, various operational procedures and other confidential information (including trade secrets)
30
relating to our franchise system. We share such information from time to time with suppliers, our franchisees and other third parties as necessary to operate
our business. The recipients of such information are numerous, and it is possible that further dissemination of such information by the recipients could
occur, which may jeopardize the value of such information, notwithstanding any efforts we may take to protect such information.
The success of our business strategy depends, in part, on our continued ability to use our intellectual property to increase brand awareness and further
develop European Wax Center-branded products and services in both existing and new markets. If we fail to protect our intellectual property adequately,
then we may lose an important advantage in the markets in which it competes. If third parties misappropriate our intellectual property, our image, brand
and the goodwill associated therewith may be harmed, then we may fail to achieve and maintain market recognition, and the competitive position of our
brand may be harmed, any of which could have a material adverse effect on our business. To protect our intellectual property from third party
infringement, we may become involved in litigation, which could result in substantial expenses, divert the attention of management, and adversely affect
our revenue, financial condition and results of operations.
Additionally, our ability to protect our trademarks and other intellectual property may be adversely affected by the COVID-19 pandemic. As a result of the
COVID-19 pandemic, certain domestic and foreign intellectual property offices have amended their filing requirements and other procedures, including,
but not limited to, extending deadlines and waiving fees. These accommodations have not been applied uniformly across all intellectual property offices
globally, and the effectiveness and duration of existing action is unclear. Further, the ongoing COVID-19 pandemic has created uncertainty with respect to
the uninterrupted operation of domestic and foreign intellectual property offices, which, among other things, may cause delayed processing of renewal and
application filings and other actions involving such offices. Our inability to establish, protect, maintain and/or enforce current and future trademark or other
intellectual property rights may have an adverse effect on the growth and reputation of our brand and business. Further, the constantly evolving nature of
the COVID-19 pandemic may change its effect on our trademarks and other intellectual property rights over time in ways that cannot be reasonably
anticipated or mitigated. This could have an adverse effect on our business, results of operations and financial condition.
If franchisees and other licensees do not observe the required quality and trademark usage standards, our brands may suffer reputational damage,
which could in turn adversely affect our business.
We license certain intellectual property to franchisees, advertisers and other third parties. The franchise agreements and other license agreements require
that each franchisee or other licensee use our trademarks in accordance with established or approved quality control guidelines and, in addition to supply
agreements, subject the franchisees, other licensees and suppliers that provide products to our brands, as applicable, to specified product quality standards
and other requirements in order to protect the reputation of our brands and to optimize the performance of our centers. We contractually require that our
franchisees and licensees maintain the quality of our brand, however, there can be no assurance that the permitted licensees, including franchisees,
advertisers and other third parties, will follow such standards and guidelines, and accordingly their acts or omissions may negatively impact the value of
our intellectual property or the reputation of our brands. Noncompliance by these entities with the terms and conditions of the applicable governing
franchise or other agreement that pertains to health and safety standards, quality control, product consistency, timeliness or proper marketing or other
business practices, may adversely impact the goodwill of our brands. For example, franchisees and other licensees may use our trademarks improperly in
communications, resulting in the weakening of the distinctiveness of our brands. Although we monitor and restrict franchisee activities through our
franchise agreements, franchisees or third parties may refer to or make statements about our brands that do not make proper use of trademarks or required
designations, that improperly alter trademarks or branding, or that are critical of our brands or place our brands in a context that may tarnish their
reputation. Franchisees or corporate-owned centers may also produce or receive through the supply chain defective products. This may result in
impairment, dilution, or tarnishment of our brands. Franchisees or other licensees may also seek to register or obtain registration for domain names, social
media accounts, and trademarks involving localizations, variations and versions of certain branding tools, and these activities may limit our ability to obtain
or use such rights in such territories or may weaken our ability to enforce our trademarks against infringement by third parties. There can be no assurance
that the franchisees or other licensees will not take actions that could have a material adverse effect on our intellectual property.
There can be no assurance that we will have an adequate remedy available, or that we will be successful, in the event that we take actions to prevent such
conduct by franchisees or other licensees. In addition, even if our franchisees or other licensees observe and maintain the quality and integrity of our brand
and other intellectual property in accordance with the relevant license and other agreements, we or our franchisees’ suppliers may be subject to regulatory
sanctions and other actions by third parties which can, in turn, negatively impact the perceived quality of our branded products or services and our brand’s
overall goodwill, regardless of the merits of the sanctions or other actions. Any such sanctions or actions could thereby materially reduce our revenues and
the results of our operations.
We may fail to establish trademark rights.
Our success depends on our and our franchisees’ continued ability to use our trademarks in order to capitalize on our name recognition, increase awareness
of our brands and further develop our brands in the countries in which we operate. We have registered certain trademarks and have other trademark
registration applications pending and some or all of the pending applications may be
31
refused by the applicable trademark authorities. Not all of the trademarks that we use have been registered in all of the countries in which we do business or
may do business in the future, and some trademarks may never be registered in all of these countries. Rights in trademarks are generally national in
character, and are obtained on a country-by-country basis by the first person to obtain protection through use or registration in that country in connection
with specified products and services. Some countries’ laws do not protect unregistered trademarks at all, or make them more difficult to enforce, and third
parties may have filed for trademarks that are the same, such as for “European Wax Center,” “EWC,” “Wax Pass” and “STRUT 365,” or similar to our
brands in countries where we have not registered our brands as trademarks. Some countries' laws also prohibit registration of trademarks that lack
distinctiveness or are descriptive of the goods and services for which registration is sought, and certain trademark authorities may decide that certain of our
trademarks are not eligible for registration Accordingly, we may not be able to adequately protect our brands everywhere in the world and use of our brands
may result in liability for trademark infringement, trademark dilution, misappropriation or unfair competition. In addition, the laws of some foreign
countries do not protect intellectual property to the same extent as the laws of the United States. All of the steps we have taken to protect our intellectual
property in the United States and in foreign countries may not be adequate.
Third parties may assert actions alleging infringement, misappropriation or violation of their intellectual property rights by us or our franchisees,
which could require us to expend significant resources, obtain costly licenses, or substantially change our operations.
We may in the future become the subject of claims asserted by third parties for infringement, misappropriation or other violation of their intellectual
property rights in areas where we or our franchisees operate or where we intend to conduct operations, including in foreign jurisdictions. Such claims,
whether or not they have merit, could be time-consuming, cause delays in introducing new products or services, harm our image, our brands, our
competitive position or our ability to expand our operations into other jurisdictions and lead to significant costs related to defense or settlement. As a result,
any such claim could harm our business and cause a decline in our results of operations and financial condition, which in turn may materially and adversely
affect our business and results of operations.
If such claims were decided against us, then we could be required to pay damages, cease offering infringing products or services on short notice, develop or
adopt non-infringing products or services, rebrand our products, services or even our businesses, and we could be required to make costly modifications to
advertising and promotional materials or acquire a license to the intellectual property that is the subject of the asserted claim, which license may not be
available on acceptable terms or at all. The attendant expenses that we bear could require the expenditure of additional capital, and there would be expenses
associated with the defense of any infringement, misappropriation, or other third-party claims, and there could be attendant negative publicity, even if
ultimately decided in our favor. In addition, third parties may assert that our intellectual property is invalid or unenforceable. If our rights in any of our
intellectual property were invalidated or deemed unenforceable, then third parties could be permitted to engage in competing uses of such intellectual
property which, in turn, could lead to a decline in center revenues and sales, and thereby negatively affect our business and results of operations.
We do not own certain software that is used in operating our business.
We utilize commercially available third-party software to run point-of-sale, information security and various other key functions. While such software can
be replaced, the delay, additional costs, and possible business interruptions associated with obtaining, renewing or extending software licenses or
integrating a large number of substitute software programs contemporaneously could adversely impact the operation of our centers, thereby reducing profits
and materially and adversely impacting our business and results of operations.
Risks Relating to Our Organization and Structure
We are a holding company and our principal asset is our 58.0% equity interest in EWC Ventures, and we are accordingly dependent upon distributions
from EWC Ventures to pay dividends, if any, and taxes, make payments under the tax receivable agreement and cover other expenses, including our
corporate and other overhead expenses.
We are a holding company and our principal asset is our ownership of 58.0% of the outstanding EWC Ventures Units. We have no independent means of
generating revenue. As the sole managing member of EWC Ventures, we intend to cause EWC Ventures to make distributions to its equityholders,
including affiliates of General Atlantic, to whom we refer to collectively as the "General Atlantic Post-IPO Members", EWC Founder Holdco, which we
refer to as the "Founder Post-IPO Member", certain other EWC Ventures Post-IPO Members and us, in amounts sufficient to cover all applicable taxes
payable by us and any payments we are obligated to make under the tax receivable agreement ("TRA") we entered into as part of the Reorganization
Transactions, but we are limited in our ability to cause EWC Ventures to make these and other distributions to us (including for purposes of paying
corporate and other overhead expenses) due to potential restrictions in our credit agreement and cash requirements and financial conditions of EWC
Ventures.
To the extent that we need funds and EWC Ventures is restricted from making such distributions to us, under applicable law or regulation, as a result of
covenants in our debt instruments or otherwise, we may not be able to obtain such funds on terms acceptable to us or at all and as a result could suffer a
material adverse effect on our liquidity and financial condition.
32

Under the Amended and Restated Limited Liability Company Agreement of EWC Ventures, we expect EWC Ventures from time to time to make pro rata
distributions in cash to its equityholders, including the General Atlantic Post-IPO Members, the Founder Post-IPO Member, certain other EWC Ventures
Post-IPO Members and us, in amounts sufficient to cover taxes on our allocable share of the taxable income of EWC Ventures and payments we are
obligated to make under the TRA. As a result of (i) potential differences in the amount of net taxable income allocable to us and to EWC Ventures’ other
equityholders, (ii) the lower tax rate applicable to corporations than individuals and (iii) the favorable tax benefits that we anticipate from (a) increases in
our allocable share of certain existing tax basis of the tangible and intangible assets of EWC Ventures and adjustments to the tax basis of the tangible and
intangible assets of EWC Ventures, in each case as a result of (a) the purchases of EWC Ventures Units (along with the corresponding shares of our Class B
common stock) from certain of the EWC Ventures Post-IPO Members using a portion of the net proceeds from the initial or secondary public offerings or
in any future offering or (b) Share Exchanges and Cash Exchanges by the EWC Ventures Pre-IPO Members (or their transferees or other assignees) in
connection with or after the initial public offering, (b) our utilization of certain tax attributes of the Blocker Companies (including the Blocker Companies’
allocable share of certain existing tax basis of the tangible and intangible assets of EWC Ventures) and (c) certain other tax benefits related to entering into
the TRA, including tax benefits attributable to payments under the TRA, we expect that these cash distributions will be in amounts that exceed our tax
liabilities. Our board of directors will determine the appropriate uses for any excess cash so accumulated, which may include, among other uses, the
payment of obligations under the TRA and the payment of other expenses. We have no obligation to distribute such cash (or other available cash) to our
stockholders. No adjustments to the exchange ratio for EWC Ventures Units and corresponding shares of common stock will be made as a result of any
cash distribution by us or any retention of cash by us, and in any event the ratio will remain one-to-one. To the extent we do not distribute such excess cash
as dividends on our Class A common stock or otherwise take ameliorative actions between EWC Ventures Units and shares of Class A common stock and
instead, for example, hold such cash balances, or lend them to EWC Ventures, this may result in shares of our Class A common stock increasing in value
relative to the value of EWC Ventures Units. The holders of EWC Ventures Units may benefit from any value attributable to such cash balances if they
acquire shares of Class A common stock in exchange for their EWC Ventures Units, notwithstanding that such holders may previously have participated as
holders of EWC Ventures Units in distributions that resulted in such excess cash balances.
Our organizational structure, including the TRA, confers certain benefits upon the EWC Ventures Pre-IPO Members that do not benefit holders of our
Class A common stock (other than the EWC Ventures Pre-IPO Members) to the same extent that it benefits the EWC Ventures Pre-IPO Members.
Our organizational structure, including the TRA, confers certain benefits upon the EWC Ventures Pre-IPO Members that do not benefit the holders of our
Class A common stock (other than the EWC Ventures Pre-IPO Members) to the same extent that it benefits the EWC Ventures Pre-IPO Members. We
entered into the TRA with EWC Ventures and the EWC Ventures Pre-IPO Members in connection with the completion of the initial public offering and the
Reorganization Transactions, which provides for the payment by us to the EWC Ventures Pre-IPO Members of 85% of the amount of tax benefits, if any,
that we actually realize, or in some circumstances are deemed to realize, in each case, computed using simplifying assumptions to address the impact of
state and local taxes, as a result of (i) increases in our allocable share of certain existing tax basis and adjustments to the tax basis of the tangible and
intangible assets of EWC Ventures, in each case as a result of (a) the purchases of EWC Ventures Units (along with the corresponding shares of our Class B
common stock) from certain of the EWC Ventures Post-IPO Members using a portion of the net proceeds from our initial and secondary public offerings or
in any future offering or (b) Share Exchanges and Cash Exchanges by the EWC Ventures Pre-IPO Members (or their transferees or other assignees) in
connection with or after the initial public offering, (ii) our utilization of certain tax attributes of the Blocker Companies (including the Blocker Companies’
allocable share of certain existing tax basis of the tangible and intangible assets of EWC Ventures) and (iii) certain other tax benefits related to entering into
the TRA, including tax benefits attributable to payments under the TRA. Although we will retain 15% of the amount of such tax benefits, this and other
aspects of our organizational structure may adversely impact the future trading market for the Class A common stock.
The General Atlantic Equityholders, whose interests in our business may be different than yours, hold a significant percentage of the combined voting
power of our common stock and certain statutory provisions afforded to stockholders are not applicable to us.
Approximately 43.5% of the combined voting power of our common stock is held by the General Atlantic Equityholders as of December 25, 2021. The
General Atlantic Equityholders’ interests may not be fully aligned with yours, which could lead to actions that are not in your best interest. Because the
General Atlantic Equityholders hold part of their economic interest in our business through EWC Ventures, rather than through the public company, they
may have conflicting interests with holders of shares of our Class A common stock. For example, the General Atlantic Equityholders may have different
tax positions from us, which could influence their decisions regarding whether and when we should dispose of assets or incur new or refinance existing
indebtedness, especially in light of the existence of the TRA that entered into in connection with our initial public offering, and whether and when we
should undergo certain changes of control within the meaning of the TRA or terminate the TRA. In addition, the structuring of future transactions may take
into consideration these tax or other considerations even where no similar benefit would accrue to us. In addition, the General Atlantic Equityholders’
significant ownership in us may discourage someone from making a significant equity investment in us, or could discourage transactions, including
transactions in which you as a holder of shares of our Class A common stock might otherwise receive a premium for your shares over the then-current
market price.
33
We have opted out of Section 203 of the General Corporation Law of the State of Delaware (the “Delaware General Corporation Law”); however, our
amended and restated certificate of incorporation prohibits us from engaging in a business combination transaction with an interested stockholder for a
period of three years after the interested stockholder became such unless the transaction fits within an applicable exemption, such as board approval of the
business combination or the transaction which resulted in such stockholder becoming an interested stockholder. Such restrictions shall not apply to any
business combination between General Atlantic and any affiliate thereof or their direct and indirect transferees, on the one hand, and us, on the other.
Therefore, the General Atlantic Equityholders are able to transfer their interests in us to a third party by transferring their shares of our common stock
(subject to certain restrictions and limitations), which would not require the approval of our board of directors or our other stockholders.
Our amended and restated certificate of incorporation contains a provision renouncing our interest and expectancy in certain corporate opportunities,
which could adversely affect our business or prospects.
Our amended and restated certificate of incorporation provides that, to the fullest extent permitted by law, the doctrine of “corporate opportunity” will not
apply against the General Atlantic Equityholders, any of our non-employee directors or any of their respective affiliates in a manner that would prohibit
them from investing in competing businesses, even if the opportunity is one that we might reasonably have pursued or had the ability or desire to pursue if
granted the opportunity to do so. To the extent that the General Atlantic Equityholders, our non-employee directors or any of their respective affiliates
invests in other businesses, they may have differing interests than our other stockholders.
As a result, the General Atlantic Equityholders, any of our non-employee directors or any of their respective affiliates may become aware, from time to
time, of certain business opportunities, such as acquisition opportunities, and may direct such opportunities to other businesses in which they have invested,
in which case we may not become aware of or otherwise have the ability to pursue such opportunity. Further, such businesses may choose to compete with
us for these opportunities. As a result, by renouncing our interest and expectancy in any business opportunity that may be from time to time presented to
any member of the General Atlantic Equityholders, any of our non-employee directors or any of their respective affiliates, our business or prospects could
be adversely affected if attractive business opportunities are procured by such parties for their own benefit rather than for ours.
We are required to pay the EWC Ventures Pre-IPO Members for certain tax benefits we may claim, and the amounts we may pay could be significant.
In connection with the Reorganization Transactions, we acquired existing equity interests in EWC Ventures from an affiliate of General Atlantic in the
Mergers. The Mergers resulted in our succeeding to certain valuable tax attributes held by the General Atlantic affiliate. In addition, we used a portion of
the net proceeds from the initial and secondary public offerings to purchase EWC Ventures Units and corresponding shares of Class B common stock from
certain EWC Ventures Post-IPO Members, including the General Atlantic Post-IPO Members. These acquisitions of interests in EWC Ventures resulted in
tax basis adjustments to the assets of EWC Ventures that will be allocated to us and our subsidiaries. In addition, future exchanges by the EWC Ventures
Post-IPO Members of EWC Ventures Units and corresponding shares of Class B common stock for shares of our Class A common stock are expected to
produce favorable tax attributes. These tax attributes would not be available to us in the absence of those transactions. Both the existing and anticipated tax
basis adjustments are expected to reduce the amount of tax that we would otherwise be required to pay in the future.
We entered into the TRA, which provides for the payment by us to the EWC Ventures Pre-IPO Members of 85% of the benefits, if any, that we realize, or
are deemed to realize (calculated using certain assumptions), as a result of (i) increases in our allocable share of certain existing tax basis of the tangible
and intangible assets of EWC Ventures and adjustments to the tax basis of the tangible and intangible assets of EWC Ventures, in each case as a result of (a)
the purchases of EWC Ventures Units (along with the corresponding shares of our Class B common stock) from certain of the EWC Ventures Post-IPO
Members using a portion of the net proceeds from the initial and secondary public offerings or in any future offering or (b) Share Exchanges and Cash
Exchanges by the EWC Ventures Pre-IPO Members (or their transferees or other assignees) in connection with or after the initial public offering, (ii) our
utilization of certain tax attributes of the Blocker Companies (including the Blocker Companies’ allocable share of certain existing tax basis of the tangible
and intangible assets of EWC Ventures) and (iii) certain other tax benefits related to entering into the TRA, including tax benefits attributable to payments
under the TRA. There is significant existing tax basis in the assets of EWC Ventures as a result of the prior acquisition of interests in EWC Ventures by the
General Atlantic Equityholders, and subsequent redemptions, exchanges or purchases of EWC Ventures Units are expected to result in increases in the tax
basis of the assets of EWC Ventures. The existing tax basis, increases in existing tax basis and tax basis adjustments generated over time may increase (for
tax purposes) the depreciation and amortization deductions available to us and, therefore, may reduce the amount of U.S. federal, state and local tax that we
would otherwise be required to pay in the future. Actual tax benefits realized by us may differ from tax benefits calculated under the TRA as a result of the
use of certain assumptions in the TRA, including the use of an assumed weighted- average state and local income tax rate to calculate tax benefits. This
payment obligation is an obligation of the Company and not of EWC Ventures.
With respect to future redemptions, exchanges and purchases, the ability to achieve benefits from any existing tax basis, the actual increase in tax basis or
other tax attributes, as well as the amount and timing of any payments under the agreement, will vary depending upon a number of factors, including the
timing of redemptions, exchanges or purchases by the EWC Ventures Pre-IPO
34
Members (or their transferees or other assignees) and purchases or redemptions of EWC Ventures Units and corresponding shares of Class B common
stock from EWC Ventures Pre-IPO Members (or their transferees or other assignees), the price of our Class A common stock at the time of the redemption,
exchange or purchase, the extent to which such redemptions, exchanges or purchases are taxable, the amount and timing of the taxable income we generate
in the future and the tax rate then applicable and the portion of our payments under the TRA constituting imputed interest.
The payments we will be required to make under the TRA could be substantial. Although estimating the amount and timing of payments that may become
due under the TRA is by its nature imprecise, we expect that, as a result of (i) increases in our allocable share of certain existing tax basis of the tangible
and intangible assets of EWC Ventures, and adjustments to the tax basis of the tangible and intangible assets of EWC Ventures, in each case as a result of
(a) the purchases of EWC Ventures Units (along with the corresponding shares of our Class B common stock) from certain of the EWC Ventures Post-IPO
Members using a portion of the net proceeds from the initial and secondary public offerings or in any future offering or (b) Share Exchanges and Cash
Exchanges by the EWC Ventures Pre-IPO Members (or their transferees or other assignees) in connection with or after the initial public offering, (ii) our
utilization of certain tax attributes of the Blocker Companies (including the Blocker Companies’ allocable share of certain existing tax basis of the tangible
and intangible assets of EWC Ventures) and (iii) certain other tax benefits related to entering into the TRA, including tax benefits attributable to payments
under the TRA. Assuming no material changes in the relevant tax law and that we earn sufficient taxable income to realize in full the potential tax benefit
described above, we estimate that payments under the TRA would aggregate to approximately $357.2 million over 18 years based on a closing share price
of $29.25 per share of Class A common stock and assuming all future Share Exchanges and Cash Exchanges would occur on December 25, 2021. The
payments under the TRA are not conditioned upon the EWC Ventures Pre-IPO Members’ continued ownership of us. The actual amounts we will be
required to pay may materially differ from these hypothetical amounts, because potential future tax savings that we will be deemed to realize, and the TRA
payments made by us, will be calculated based in part on the market value of our Class A common stock at the time of each Share Exchange or Cash
Exchange and the prevailing applicable federal tax rate (plus the assumed combined state and local tax rate) applicable to us over the life of the TRA and
will depend on our generating sufficient taxable income to realize the tax benefits that are subject to the TRA.
Finally, because we are a holding company with no operations of our own, our ability to make payments under the TRA is dependent on the ability of our
subsidiaries to make distributions to us. The 2026 Credit Agreement restricts and future debt instruments may restrict the ability of our subsidiaries to make
distributions to us, which could affect our ability to make payments under the TRA. We currently expect to fund these payments from cash flow from
operations generated by our subsidiaries as well as from excess tax distributions that we receive from our subsidiaries. To the extent we are unable to make
payments under the agreement for any reason (including because the 2026 Credit Agreement restricts the ability of our subsidiaries to make distributions to
us), under the terms of the TRA such payments will be deferred and accrue interest until paid. If we are unable to make payments due to insufficient funds,
such payments may be deferred indefinitely while accruing interest until paid, which could negatively impact our results of operations and could also affect
our liquidity in future periods in which such deferred payments are made.
We will not be reimbursed for any payments made to EWC Ventures Pre-IPO Members (or their transferees or assignees) under the TRA in the event
that any tax benefits are disallowed.
Payments under the TRA will be based on the tax reporting positions that we determine, and the IRS, or another tax authority may challenge all or part of
the tax basis increases or other tax benefits we claim, as well as other related tax positions we take, and a court could sustain such challenge. Although we
are not aware of any issue that would cause the IRS to challenge the tax basis increases or other benefits arising under the TRA, if the outcome of any such
challenge would reasonably be expected to materially affect a recipient’s payments under the TRA, then we will not be permitted to settle such challenge
without the consent (not to be unreasonably withheld or delayed) of the EWC Ventures Pre-IPO Members. The interests of the EWC Ventures Pre-IPO
Members in any such challenge may differ from or conflict with our interests and your interests, and the EWC Ventures Pre-IPO Members may exercise
their consent rights relating to any such challenge in a manner adverse to our interests and your interests. We will not be reimbursed for any cash payments
previously made to the EWC Ventures Pre-IPO Members (or their transferees or assignees) under the TRA in the event that any tax benefits initially
claimed by us and for which payment has been made to the EWC Ventures Pre-IPO Members (or their transferees or assignees) are subsequently
challenged by a taxing authority and are ultimately disallowed. Instead, any excess cash payments made by us to the EWC Ventures Pre-IPO Members (or
their transferees or assignees) will be netted against any future cash payments that we might otherwise be required to make to the EWC Ventures Pre-IPO
Members (or their transferees or assignees) under the terms of the TRA. However, we might not determine that we have effectively made an excess cash
payment to the EWC Ventures Pre-IPO Members (or its transferee or assignee) for a number of years following the initial time of such payment and, if any
of our tax reporting positions are challenged by a taxing authority, we will not be permitted to reduce any future cash payments under the TRA until any
such challenge is finally settled or determined. Moreover, the excess cash payments we previously made under the TRA could be greater than the amount
of future cash payments against which we would otherwise be permitted to net such excess. The applicable U.S. federal income tax rules for determining
applicable tax benefits we may claim are complex and factual in nature, and there can be no assurance that the IRS, any other taxing authority or a court
will not disagree with our tax reporting positions. As a result, payments could be made under the TRA significantly in excess of any tax savings that we
realize in respect of the tax attributes with respect to the EWC Ventures Pre-IPO Members (or their transferees or assignees) that are the subject of the
TRA.
35
In certain cases, payments under the TRA to the EWC Ventures Pre-IPO Members may be accelerated or significantly exceed any actual benefits we
realize in respect of the tax attributes subject to the TRA.
The TRA provides that in the case of a change in control of EWC Ventures or the material breach of our obligations under the TRA, we are required to
make a payment to the EWC Ventures Pre-IPO Members in an amount equal to the present value of future payments (calculated using a discount rate equal
to the lesser of (i) 6.5% per annum and (ii) one year LIBOR (or its successor rate) plus 100 basis points, which may differ from our, or a potential
acquirer’s, then-current cost of capital) under the TRA, which payment would be based on certain assumptions, including those relating to our future
taxable income. In these situations, our obligations under the TRA could have a substantial negative impact on our, or a potential acquirer’s, liquidity and
could have the effect of delaying, deferring, modifying or preventing certain mergers, asset sales, other forms of business combinations or other changes of
control. These provisions of the TRA may result in situations where the EWC Ventures Pre-IPO Members (or their transferees and assignees) have interests
that differ from or are in addition to those of our other stockholders. In addition, we could be required to make payments under the TRA that are substantial
and in excess of our, or a potential acquirer’s, actual cash savings in income tax. There can be no assurance that we will be able to fund or finance our
obligations under the TRA. We may need to incur debt to finance payments under the TRA to the extent our cash resources are insufficient to meet our
obligations under the TRA as a result of timing discrepancies or otherwise.
Decisions we make in the course of running our business, such as with respect to mergers, asset sales, other forms of business combinations or other
changes in control, may influence the timing and amount of payments made under the TRA. For example, the earlier disposition of assets following a
redemption of EWC Ventures Units may accelerate payments under the TRA and increase the present value of such payments, and the disposition of assets
before a redemption of EWC Ventures Units may increase the tax liability of EWC Ventures Pre-IPO Members (or their transferees or assignees) without
giving rise to any rights to receive payments under the TRA. Such effects may result in differences or conflicts of interest between the interests of EWC
Ventures Pre-IPO Members (or their transferees or assignees) and the interests of other stockholders.
Risks Relating to our Class A Common Stock
Our stock price may be volatile, and the value of our Class A common stock may decline.
The market price of our Class A common stock may be highly volatile and may fluctuate or decline substantially as a result of a variety of factors, some of
which are beyond our control, including:
• actual or anticipated fluctuations in our financial condition or results of operations;
• variance in our financial performance from expectations of securities analysts;
• changes in the pricing of our products and platform;
• changes in our projected operating and financial results;
• changes in laws or regulations applicable to our platform and products;
• announcements by us or our competitors of significant business developments, acquisitions, or new offerings;
• significant data breaches, disruptions to or other incidents involving our software;
• our involvement in litigation
• future sales of our Class A common stock by us or our stockholders, as well as the anticipation of any future contractual lock-up releases;
• changes in senior management or key personnel;
• the trading volume of our common stock;
• changes in the anticipated future size and growth rate of our market; and
• general economic and market conditions.
Broad market and industry fluctuations, as well as general economic, political, regulatory, and market conditions including those related to the recent
COVID-19 pandemic, may also negatively impact the market price of our Class A common stock. The continued spread of COVID-19, including new
variants of the virus and spikes in cases in the areas where we operate, could result in material adverse changes in our results of operations for an unknown
period of time.
Furthermore, recently, the stock market has experienced significant price and volume fluctuations. This volatility has had a significant impact on the market
price of securities issued by many companies, including companies in our industry. The changes frequently appear to occur without regard to the operating
performance of the affected companies. As such, the price of our Class A common
36

stock could fluctuate based upon factors that have little or nothing to do with us, and these fluctuations could materially reduce the price of our Class A
common stock and materially affect the value of your investment.
We cannot predict the effect our dual-class structure may have on the market price of our Class A common stock.
We cannot predict whether our dual-class structure will result in a lower or more volatile market price of our Class A common stock, in adverse publicity or
other adverse consequences. For example, certain index providers have announced restrictions on including companies with dual-class share structures in
certain of their indexes. S&P, Dow Jones and FTSE Russell have each announced changes to their eligibility criteria for inclusion of shares of public
companies on certain indices, including the S&P 500. These changes exclude companies with multiple classes of shares of common stock from being
added to these indices. In addition, several stockholder advisory firms have announced their opposition to the use of multiple class structures. As a result,
the dual-class structure of our capital stock may prevent the inclusion of our Class A common stock in these indices and may cause stockholder advisory
firms to publish negative commentary about our corporate governance practices or otherwise seek to cause us to change our capital structure. Any such
exclusion from indices could result in a less active trading market for our Class A common stock. Any actions or publications by stockholder advisory
firms critical of our corporate governance practices or capital structure could also adversely affect the trading price of our Class A common stock.
Substantial future sales of shares of our Class A common stock in the public market could cause our stock price to fall.
As of December 25, 2021, we had 36,932,423 shares of Class A common stock outstanding, which excludes 757,435 shares of Class A common stock
underlying outstanding equity awards and 26,700,477 shares of Class A common stock issuable upon potential exchanges and/or conversions. Of these
shares of Class A common stock, the 18,189,523 shares of Class A common stock sold in the initial and secondary public offering are freely tradable
without further restriction under the Securities Act. The remaining outstanding shares of Class A common stock not issued in our initial or secondary
public offerings, including shares of Class A common stock issuable upon exchange and/or conversion are deemed “restricted securities,” as that term is
defined under Rule 144 of the Securities Act. Such restricted securities can be resold in accordance with Rule 144 or any other exemption under the
Securities Act.
We have filed a registration statement under the Securities Act registering shares of our Class A common stock reserved for issuance under the 2021
Omnibus Incentive Plan, and entered into a registration rights agreement pursuant to which we granted demand and piggyback registration rights to the
General Atlantic Equityholders and the Founder Post-IPO Member and piggyback registration rights to certain of the other EWC Ventures Post-IPO
Members. The market price of our stock could decline if existing holders of shares sell them in significant quantities or are perceived by the market as
intending to engage in such selling activity.
Failure to establish and maintain effective internal control over financial reporting could have a material adverse effect on our business, financial
condition, results of operations and stock price.
We will be required, pursuant to Section 404 of the Sarbanes-Oxley Act of 2002 (“Section 404”) to furnish a report by management on, among other things,
the effectiveness of our internal controls over financial reporting for the fiscal year ending December 31, 2022. In addition, our independent registered
public accounting firm will be required to attest to the effectiveness of our internal controls over financial reporting in our first annual report required to be
filed with the SEC following the date we are no longer an “emerging growth company.” We have commenced the costly and challenging process of
compiling the system and processing documentation necessary to perform the evaluation needed to comply with Section 404, but we may not be able to
complete our evaluation, testing and any required remediation in a timely fashion. Our compliance with Section 404 will require that we incur substantial
expenses and expend significant management efforts. We will need to hire additional accounting and financial staff with appropriate public company
experience and technical accounting knowledge and compile the system and process documentation necessary to perform the evaluation needed to comply
with Section 404.
During the evaluation and testing process of our internal controls, if we identify one or more material weaknesses in our internal controls over financial
reporting, we will be unable to certify that our internal controls over financial reporting is effective. A material weakness is a deficiency, or combination of
deficiencies, in internal controls over financial reporting, such that there is a reasonable possibility that a material misstatement of the annual or interim
financial statements will not be prevented or detected on a timely basis.
We cannot assure you that the measures we have taken to date, and actions we may take in the future, will prevent or avoid potential future material
weaknesses in our internal controls over financial reporting in the future. Any failure to maintain internal controls over financial reporting could severely
inhibit our ability to accurately report our financial condition or results of operations. If we are unable to conclude that our internal controls over financial
reporting is effective, or if our independent registered public accounting firm determines we have a material weakness or significant deficiency in our
internal controls over financial reporting, we could lose investor confidence in the accuracy and completeness of our financial reports, the market price of
our common stock could decline, and we could be subject to sanctions or investigations by the SEC or other regulatory authorities. Failure to remedy any
material weakness in our internal controls over financial reporting, or to implement or maintain other effective control systems required of public
companies, could also restrict our future access to the capital markets.
37
In addition, we do not currently have an internal audit function. In order to implement any such function, we will need to hire additional personnel. If we
are unable to hire additional personnel to support our internal accounting and audit functions, our ability to report our results of operations on a timely and
accurate basis could be impaired and we could suffer adverse regulatory consequences or violate listing standards. There could also be a negative reaction
in the financial markets due to a loss of investor confidence in us and the reliability of our financial statements, which could have an adverse effect on our
business, financial condition and results of operations.
Certain of our key operating metrics are subject to inherent challenges in measurement, and any real or perceived inaccuracies in our metrics or the
underlying data may cause a loss of investor confidence in such metrics and the market price of our Class A common stock may decline.
We track certain key operating metrics using internal data analytics tools, which have certain limitations. In addition, we rely on data received from third
parties, including third-party platforms, to track certain performance indicators, and we may be limited in our ability to verify such data. In addition, our
methodologies for tracking metrics may change over time, which could result in changes to the metrics we report. If we undercount or overcount
performance due to the internal data analytics tools we use or issues with the data received from third parties, or if our internal data analytics tools contain
algorithmic or other technical errors, the data we report may not be accurate or comparable with prior periods. In addition, limitations, changes or errors
with respect to how we measure data may affect our understanding of certain details of our business, which could affect our longer-term strategies. If our
performance metrics are not, or are not perceived to be, accurate representations of our business, if we discover material inaccuracies in our metrics or the
data on which such metrics are based, or if we can no longer calculate any of our key performance metrics with a sufficient degree of accuracy, investors
could lose confidence in the accuracy and completeness of such metrics, which could cause the price of our Class A common stock to decline.
We are an “emerging growth company” and we cannot be certain if the reduced disclosure requirements applicable to emerging growth companies will
make our Class A common stock less attractive to investors.
We qualify as an “emerging growth company” under the JOBS Act. As a result, we are permitted to, and intend to, rely on exemptions from certain
disclosure requirements. As a result, our consolidated financial statements may not be comparable to the financial statements of issuers who are required to
comply with the effective dates for new or revised accounting standards that are applicable to public companies, which may make our Class A common
stock less attractive to investors. For so long as we are an emerging growth company, we will not be required to:
• provide an auditor attestation and report with respect to management’s assessment of the effectiveness of our internal controls over financial
reporting pursuant to Section 404(b) of the Sarbanes-Oxley Act of 2002;
• comply with any requirement that may be adopted by the Public Company Accounting Oversight Board regarding mandatory audit firm
rotation or a supplement to the auditor’s report providing additional information about the audit and the financial statements (i.e., an auditor
discussion and analysis); and
• submit certain executive compensation matters to stockholder advisory votes, such as “say-on-pay” and “say-on-frequency,” and disclose
certain executive compensation related items such as the correlation between executive compensation and performance and comparisons of
the Chief Executive Officer’s compensation to median employee compensation.
In addition, Section 107 of the JOBS Act also provides that an emerging growth company can take advantage of the extended transition period provided in
Section 7(a)(2)(B) of the Securities Act for complying with new or revised accounting standards. In other words, an emerging growth company can delay
the adoption of certain accounting standards until those standards would otherwise apply to private companies. We have elected to take advantage of this
extended transition period and therefore will not be subject to the same new or revised accounting standards as other public companies that are not
emerging growth companies.
We will remain an “emerging growth company” for up to five years, or until the earliest of (i) the last day of the first fiscal year in which our total annual
gross revenues exceed $1.07 billion, (ii) the date that we become a “large accelerated filer” as defined in Rule 12b-2 under the Securities Exchange Act of
1934, as amended (the “Exchange Act”), which would occur if the market value of our common stock that is held by non-affiliates exceeds $700 million as
of the last business day of our most recently completed second fiscal quarter or (iii) the date on which we have issued more than $1 billion in non-
convertible debt during the preceding three-year period.
Until such time, however, we cannot predict if investors will find our Class A common stock less attractive because we may rely on these exemptions. If
some investors find our Class A common stock less attractive, there may be a less active trading market for our Class A common stock and our stock price
may be more volatile.
Our 2026 Credit Agreement and any future debt agreements may preclude us from paying dividends.
The terms of existing or future debt agreements may preclude us from paying dividends. In addition, we generally intend to retain our future earnings, if
any, to fund the development and growth of our business and repay outstanding debt. Our 2026 Credit Agreement
38
contains restrictive covenants that impose significant operating and financial restrictions on us, including restrictions on our ability to pay dividends and
make other restricted payments. If we are successful in completing our announced whole business securitization, we expect to use a portion of the proceeds
therefrom to pay a one-time special dividend to our equityholders. Any determination to pay dividends in the future will be at the discretion of our board of
directors. As a result, capital appreciation, if any, of our Class A common stock may be your sole source of gain for the foreseeable future. Therefore, you
may not be able to realize any return on your investment in our Class A common stock for an extended period of time, if at all.
Provisions in our charter documents may delay or prevent our acquisition by a third party.
Certain provisions of Delaware law and our amended and restated certificate of incorporation and amended and restated by-laws contain several provisions
that may make it more difficult or expensive for a third party to acquire control of us without the approval of our board of directors. These provisions,
which may delay, prevent or deter a merger, acquisition, tender offer, proxy contest or other transaction that stockholders may consider favorable, include
the following, some of which became effective after the General Atlantic Equityholders and their affiliates and successors no longer collectively
beneficially own shares representing 40% of our issued and outstanding common stock (the “40% Triggering Event”):
• the division of our board of directors into three classes and the election of each class for three-year terms;
• the sole ability of the board of directors to fill a vacancy created by the expansion of the board of directors;
• advance notice requirements for stockholder proposals and director nominations;
• after the 40% Triggering Event, provisions limiting stockholders’ ability to call special meetings of stockholders, to require special meetings
of stockholders to be called and to take action by written consent;
• after the 40% Triggering Event, in certain cases, the approval of holders of at least 66 2/3% of the shares entitled to vote generally on the
making, alteration, amendment or repeal of our amended and restated certificate of incorporation or amended and restated by-laws will be
required to adopt, amend or repeal our amended and restated by-laws, or amend or repeal certain provisions of our amended and restated
certificate of incorporation;
• the required approval of holders of at least 66 2/3% of the shares entitled to vote at an election of the directors to remove directors, which
removal may only be for cause; and
• the ability of our board of directors to designate the terms of and issue new series of preferred stock without stockholder approval, which
could be used, among other things, to institute a rights plan that would have the effect of significantly diluting the stock ownership of a
potential hostile acquirer, likely preventing acquisitions that have not been approved by our board of directors.
These provisions of our amended and restated certificate of incorporation and amended and restated by-laws could discourage potential takeover attempts
and reduce the price that investors might be willing to pay for shares of our Class A common stock in the future, which could reduce the market price of
our Class A common stock.
In addition, we have opted out of Section 203 of the Delaware General Corporation Law, but our amended and restated certificate of incorporation provides
that engaging in any of a broad range of business combinations with any “interested” stockholder (any stockholder with 15% or more of our voting stock)
for a period of three years following the date on which the stockholder became an “interested” stockholder is prohibited, subject to certain exceptions. For
example, such restrictions shall not apply to any business combination between General Atlantic and any affiliate thereof or their direct and indirect
transferees, on the one hand, and us, on the other.
We may issue preferred stock whose terms could adversely affect the voting power or value of our Class A common stock.
Our amended and restated certificate of incorporation authorizes us to issue, without the approval of our stockholders, one or more classes or series of
preferred stock having such designations, preferences, limitations and relative rights, including preferences over our Class A common stock respecting
dividends and distributions, as our board of directors may determine. The terms of one or more classes or series of preferred stock could adversely impact
the voting power or value of our Class A common stock. For example, we might grant holders of preferred stock the right to elect some number of our
directors in all events or on the happening of specified events or the right to veto specified transactions. Similarly, the repurchase or redemption rights or
liquidation preferences we might assign to holders of preferred stock could affect the residual value of the Class A common stock.
We have incurred increased costs as a result of operating as a public company, and our management will be required to devote substantial time to
compliance with our public company responsibilities and corporate governance practices.
As a public company, we have incurred significant levels of legal, accounting and other expenses that we did not incur as a privately owned corporation,
which we expect to further increase after we are no longer an “emerging growth company”. Sarbanes-Oxley Act of 2002, the Dodd-Frank Wall Street
Reform and Consumer Protection Act and related rules of the SEC, together with the listing requirements of Nasdaq, impose significant requirements
relating to disclosure controls and procedures and internal control over
39
financial reporting for public companies. We expect that compliance with these public company requirements will increase our costs, require additional
resources and make some activities more time consuming than they have been in the past when we were privately owned. We are required to expend
considerable time and resources complying with public company regulations. In addition, these laws and regulations could make it more difficult or costly
for us to obtain certain types of insurance, including director and officer liability insurance, and we may be forced to accept reduced policy limits and
coverage or incur substantially higher costs to obtain the same or similar coverage. In addition, these laws and regulations could make it more difficult for
us to attract and retain qualified persons to serve on our board of directors or as executive officers and may divert management’s attention. Furthermore, if
we are unable to satisfy our obligations as a public company, we could be subject to delisting of our Class A common stock, fines, sanctions and other
regulatory actions.
If securities or industry analysts do not publish research or publish inaccurate or unfavorable research about us or our business, or publish projections
for our business that exceed our actual results, our stock price and trading volume could decline.
The trading market for our Class A common stock may be affected by the research and reports that securities or industry analysts publish about us or our
business. If securities or industry analysts fail to provide coverage of our Company, the trading price for our Class A common stock and the trading volume
could decline. If one or more of the analysts who covers us downgrades our Class A common stock or publishes inaccurate or unfavorable research about
our business, our stock price could decline. In addition, the analysts’ projections may have little or no relationship to the results we actually achieve and
could cause our stock price to decline if we fail to meet their projections. If one or more of these analysts ceases coverage of us or fails to publish reports
on us regularly, our stock price or trading volume could decline.
Our amended and restated certificate of incorporation provides that certain courts in the State of Delaware or the federal district courts of the United
States for certain types of lawsuits will be the sole and exclusive forum for substantially all disputes between us and our stockholders, which limits our
stockholders’ ability to obtain a favorable judicial forum for disputes with us or our directors, officers or employees.
Our amended and restated certificate of incorporation, provides that, unless we consent in writing to the selection of an alternative forum and subject to
certain exceptions, to the fullest extent permitted by law, the Court of Chancery of the State of Delaware is the sole and exclusive forum for (i) any
derivative action or proceeding brought on our behalf, (ii) any action asserting a claim of breach of a fiduciary duty owed by any of our directors, officers,
employees or stockholders to us or our stockholders, creditors, or other constituents, (iii) any action asserting a claim arising pursuant to any provision of
the Delaware General Corporation Law or of our amended and restated certificate of incorporation or our amended and restated by-laws (as either may be
amended and/or restated from time to time), or (iv) any action asserting a claim against us or any of our directors or officers that is governed by the internal
affairs doctrine. The exclusive forum provision provides that it will not apply to claims arising under the Securities Act, the Exchange Act or other federal
securities laws for which there is exclusive federal or concurrent federal and state jurisdiction. Unless we consent in writing to the selection of an
alternative forum, the federal district courts of the United States of America shall be the exclusive forum for the resolution of any complaint asserting a
cause of action arising under the Securities Act, the Exchange Act or such other federal securities laws.
Although we believe this exclusive forum provision benefits us by providing increased consistency in the application of Delaware law and federal
securities laws in the types of lawsuits to which each applies, the choice of forum provision may limit a stockholder’s ability to bring a claim in a judicial
forum that it finds favorable for disputes with us or our directors, officers, other employees or stockholders, which may discourage such lawsuits against us
and our directors, officers, other employees or stockholders. However, the enforceability of similar forum provisions in other companies’ certificates of
incorporation has been challenged in legal proceedings. If a court were to find the exclusive choice of forum provision contained in our amended and
restated certificate of incorporation to be inapplicable or unenforceable in an action, we may incur additional costs associated with resolving such action in
other jurisdictions, which could materially adversely affect our business, financial condition and results of operations.
Item 1B. Unresolved Staff Comments.
None.
Item 2. Properties.
As of December 25, 2021, we had 853 franchised and corporate-owned centers, and of these there are five actively operating corporate-owned centers, and
in addition, we hold a lease for one inactive corporate-owned center and one for a future corporate center. We held leases covering the building and/or land
for our five corporate-owned centers and three offices and training centers in the United States, including our corporate headquarters located in Plano,
Texas. The leases generally have initial expiration dates ranging from five and ten years, with certain renewal options available. We believe that the
properties are suitable and adequate for the Company’s business.
Item 3. Legal Proceedings.
We may be the defendant from time to time in litigation arising during the ordinary course of business, including, without limitation, employment-related
claims, claims based on theories of joint employer liability, data privacy claims, claims involving anti-poaching
40

allegations and claims made by former or existing franchisees or the government. In the ordinary course of business, we are also subject to regulatory and
governmental examinations, information requests and subpoenas, inquiries, investigations, and threatened legal actions and proceedings. Although the
outcomes of potential legal proceedings are inherently difficult to predict, the Company does not expect the resolution of these occasional legal proceedings
to have a material effect on its financial position, results of operations, or cash flow.
Item 4. Mine Safety Disclosures.
None.
41
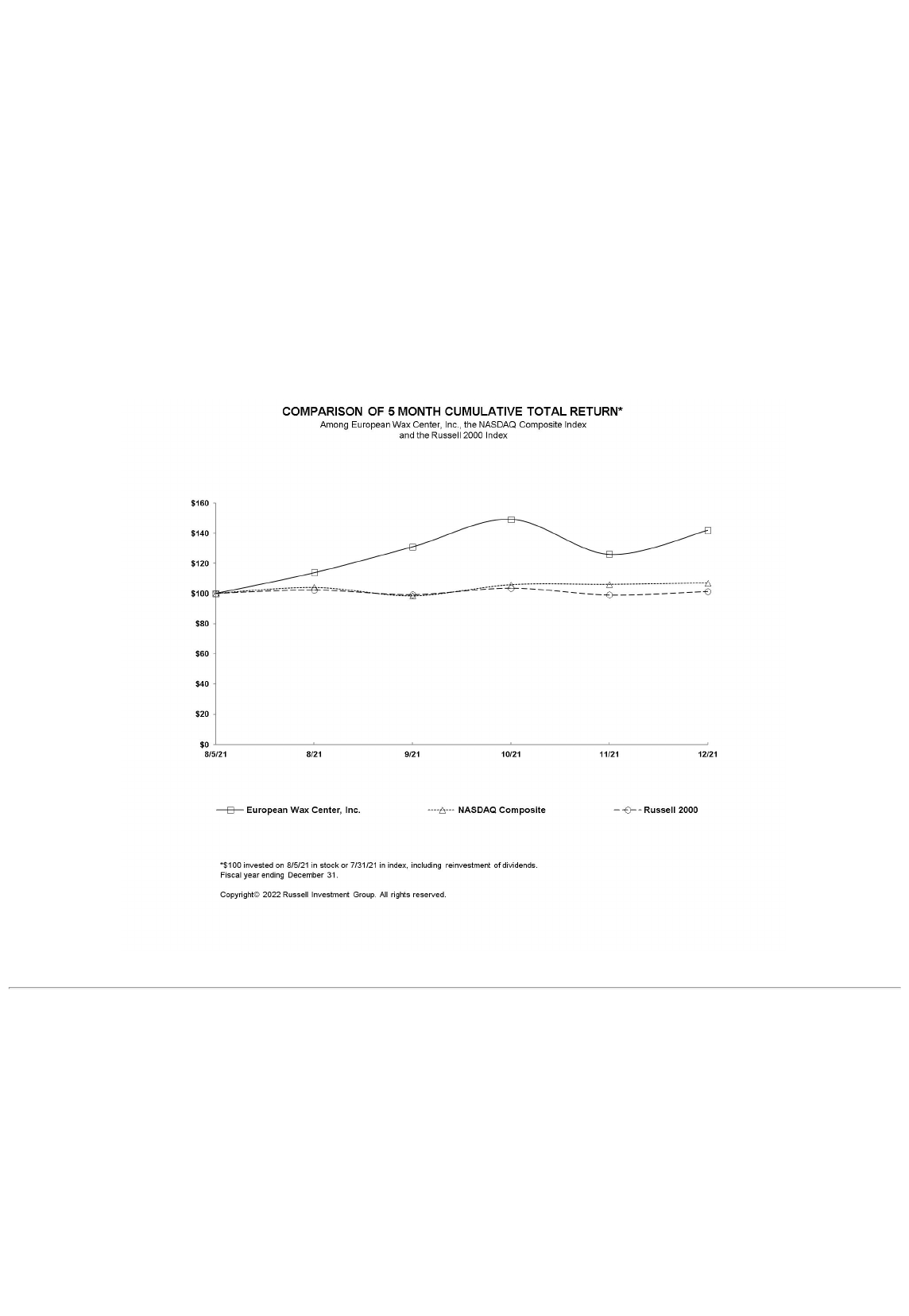
PART II
Item 5. Market for Registrant’s Common Equity, Related Stockholder Matters and Issuer Purchases of Equity Securities.
Our common stock is traded on the Nasdaq Stock Market LLC under the symbol “EWCZ”. The approximate number of stockholders of record of our Class
A common stock as of March 10, 2022 was ten. The approximate number of stockholders of record of our Class B common stock as of March 10, 2022
was six. There is no public market for shares of our Class B common stock. The number of holders of record is based upon the actual number of holders
registered at such date and does not include holders of shares in “street name” or other entities in security position listings maintained by depositories.
We previously have not paid dividends. However, if we are successful in consummating our announced whole business securitization, we expect to use a
portion of the proceeds therefrom for a one-time special dividend to equityholders. Any future determination relating to dividend policy will be made at the
discretion of our board of directors and will depend on a number of factors, including restrictions in our debt instruments, as well as our future earnings,
capital requirements, financial condition, prospects and other factors that our board of directors may deem relevant. Our debt agreements currently restrict
our ability to pay dividends. See “Management’s Discussion and Analysis of Financial Condition and Results of Operations — Liquidity and Capital
Resources” contained in Item 7 of this annual report on Form 10-K.
The information regarding securities authorized for issuance under equity compensation plans appears in our Definitive Proxy Statement for our annual
meeting of stockholders to be held on June 8, 2022, which information is incorporated herein by reference.
The graph below matches the cumulative five month total return of holders of our Class A common stock with the cumulative total returns of the Nasdaq
composite and the Russell 2000 index. We include a comparison against the Russell 2000 because there is no published industry or line-of-business index
for our industry and we do not have a readily definable peer group that is publicly traded. The graph assumes that the value of the investment in our
common stock, in each index, and in the peer group (including reinvestment of dividends) was $100 on August 5, 2021 (the date of our IPO) and tracks it
through December 31, 2021.
42
8/5/21
8/21
9/21
10/21
11/21
12/21
European Wax Center, Inc. 100.00 113.84 130.95 149.04 126.09 141.89
NASDAQ Composite 100.00 104.08 98.60 105.79 106.14 106.93
Russell 2000 100.00 102.24 99.22 103.44 99.13 101.35
Unregistered Sales of Equity Securities and Use of Proceeds
On August 9, 2021, we completed the initial public offering of our Class A common stock pursuant to a Registration Statement (File No. 333-257874),
which was declared effective on August 4, 2021.
Under the Registration Statement, we and the selling stockholders sold 12,190,000 shares of our Class A common stock at a price of $17.00 per share. This
included 1,590,000 shares sold by us and the selling stockholders pursuant to the underwriters' option to purchase additional shares of Class A common
stock. Morgan Stanley & Co. LLC, BofA Securities, Inc. and Jefferies LLC acted as representatives of the underwriters for the offering.
We received net proceeds of $155.4 million after deducting underwriting discounts and commissions and prior to paying any offering expenses. The initial
public offering terminated after the sale of all securities registered pursuant to the Registration Statement.
On November 15, 2021, we completed a secondary public offering of our Class A common stock pursuant to a Registration Statement (File No. 333-
260868), which was declared effective on November 10, 2021.
Under the Registration Statement, we and the selling stockholders sold 5,999,523 shares of our Class A common stock at a price of $26.25 per share. This
included 782,546 shares sold by us and the selling stockholders pursuant to the underwriters' option to purchase additional shares of Class A common
stock. Morgan Stanley & Co. LLC, BofA Securities, Inc. and Jefferies LLC acted as representatives of the underwriters for the offering.
We received net proceeds of $67.9 million after deducting underwriting discounts and commissions and prior to paying any offering expenses. The
secondary public offering terminated after the sale of all securities registered pursuant to the Registration Statement.
We used the net proceeds from these offerings as described in the notes to the consolidated financial statements included in this annual report on Form 10-
K. There was no material change in the use of the proceeds from these offerings as described in the Registration Statements.
Issuer Purchases of Equity Securities
None.
Item 6. Reserved.
Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations.
You should read the following discussion of our historical performance, financial condition and future prospects in conjunction with the audited
consolidated financial statements and the notes thereto included elsewhere in this Annual Report on Form 10-K. This discussion contains forward-looking
statements that are based on the views and beliefs of our management, as well as assumptions and estimates made by our management. Actual results could
differ materially from such forward-looking statements as a result of various risk factors, including those that may not be in the control of management.
For further information on items that could impact our future operating performance or financial condition, see the section titled “Risk Factors” included
elsewhere in this Annual Report on Form 10-K.
We conduct substantially all of our activities through our subsidiary, EWC Ventures, LLC and its subsidiaries. We operate on a fiscal calendar that results
in a given fiscal year consisting of a 52- or 53-week period ending on the Saturday closest to December 31. Our fiscal quarters are composed of 13 weeks
each, except for 53-week fiscal years for which the fourth quarter will be composed of 14 weeks.
A discussion regarding our financial condition and results of operations for the year ended December 25, 2021 compared to the year ended December 26,
2020 is presented in the following sections. A discussion regarding our financial condition and results of operations for the year ended December 25, 2020
compared to the year ended December 28, 2019 can be found in our prospectus dated August 4, 2021, filed with the Securities and Exchange Commission
(the "SEC") on August 6, 2021 pursuant to Rule 424(b)(4) of the Securities Act of 1933, as amended (referred to herein as the “Prospectus”).
Overview
We are the largest and fastest-growing franchisor and operator of out-of-home (“OOH”) waxing services in the United States by number of centers and
system-wide sales. We delivered over 20 million waxing services in 2021 and over 13 million waxing services in 2020 generating $797 million and $469
million of system-wide sales, respectively, across our highly-franchised network. We have a leading portfolio of centers operating in 853 locations across
44 states as of December 25, 2021. Of these locations, 848 are franchised centers operated by franchisees and five are corporate-owned centers.
43

The European Wax Center brand is trusted, efficacious and accessible. Our culture is obsessed with our guest experience and we deliver a superior guest
experience relative to smaller chains and independent salons. We offer guests high-quality, hygienic waxing services administered by our licensed, EWC-
trained estheticians (our “wax specialists”), at our accessible and welcoming locations (our “centers”). Our technology-enabled guest interface simplifies
and streamlines the guest experience with automated appointment scheduling and remote check-in capabilities, ensuring guest visits are convenient, hassle-
free, and consistent across our network of centers. Our well-known, pre-paid Wax Pass program makes payment easy and convenient, fostering loyalty and
return visits. Guests view us as a non-discretionary part of their personal-care and beauty regimens, providing us with a highly predictable and growing
recurring revenue model.
Our asset-light franchise platform delivers capital-efficient growth, significant cash flow generation and resilience through economic cycles. Our centers
are 99% owned and operated by our franchisees who benefit from superior unit-level economics, with mature centers generating annual cash-on-cash
returns in excess of 60%.
In partnership with our franchisees, we fiercely protect our points of differentiation that attract new guests, build meaningful relationships and promote
lasting retention. Our net promoter score (“NPS”) demonstrates our guests’ devotion to our brand. We are so confident in our ability to delight that we have
always offered all of our guests their first wax free.
Hair removal solutions are consistently in demand, given the recurring nature of hair growth. The OOH waxing market is the fastest-growing hair removal
solution in the United States, defined by a total addressable market of $18 billion with annualized growth that is more than double other hair removal
alternatives. European Wax Center has become the category-defining brand within this rapidly growing market and became so by professionalizing a
highly fragmented sector where service consistency, hygiene, and customer trust were not historically offered. We are approximately six times larger than
the next largest waxing-focused competitor by center count and approximately 13 times larger by system-wide sales. Our unmatched scale enables us to
drive broader brand awareness, ensures our licensed wax specialists are universally trained at the highest standards and drive consistent financial
performance across each center.
Under the stewardship of our CEO, David Berg, and the other management team members, we have prioritized building a culture of performance, success,
and inclusivity. Additionally, we have intensified our focus on enhancing the guest experience and have invested significantly in our corporate
infrastructure and marketing capabilities to continue our track record of sustainable growth. The foundation for our next chapter of growth is firmly in
place.
Growth Strategy and Outlook
We plan to grow our business primarily by opening new franchised centers and then additionally increasing our same-store sales and leveraging our
corporate infrastructure to expand our profit margins and generate robust free cash flow.
We believe our franchisees’ track record of successfully opening new centers and consistently generating attractive unit-level economics validates our
strategy to expand our footprint and grow our capacity to serve more guests. We aspire to grow between 7% to 10% of our center count each year. Our
center count grew 7% and 6% during fiscal year 2021 and fiscal year 2020, respectively, and has grown each year since 2010. Our thoughtful approach to
growth ensures each center is appropriately staffed with the high-quality team and licensed, highly-trained wax specialists that our brand has been known
for since our initial opening. We believe that none of our existing markets are fully penetrated, and that we have a significant whitespace opportunity of
more than 3,000 locations for our standard center format across the United States. Our centers have a long track record of sustained growth delivering ten
consecutive years of positive same-store sales growth through 2019 with resilient performance through economic cycles.
Our straightforward, asset-light franchise platform and our proven track record of increasing profitability will continue to drive EBITDA margin accretion
and free cash flow generation as we expand our national footprint. We have invested in building our scalable support infrastructure, and we currently have
the capabilities and systems in place to drive revenue growth and profitability across our existing and planned franchise centers.
Key Business Metrics
We track the following key business metrics to evaluate our performance, identify trends, formulate financial projections, and make strategic decisions.
Accordingly, we believe that these key business metrics provide useful information to investors and others in understanding and evaluating our results of
operations in the same manner as our management team. These key business metrics are presented for supplemental information purposes only, should not
be considered a substitute for financial information presented in accordance with GAAP, and may be different from similarly titled metrics or measures
presented by other companies.
Number of Centers. Number of centers reflects the number of franchised and corporate-owned centers open at the end of the reporting period. We review
the number of new center openings, the number of closed centers and the number of relocations of centers to assess net new center growth, and drivers of
trends in system-wide sales, royalty and franchise fee revenue and corporate-owned center sales.
System-Wide Sales. System-wide sales represent sales from same day services, retail sales and cash collected from wax passes for all centers in our
network, including both franchisee-owned and corporate-owned centers. While we do not record franchised center sales as revenue, our royalty revenue is
calculated based on a percentage of franchised center sales, which are 6.0% of sales, net of retail
44
product sales, as defined in the franchise agreement. This measure allows us to better assess changes in our royalty revenue, our overall center
performance, the health of our brand and the strength of our market position relative to competitors. Our system-wide sales growth is driven by net new
center openings as well as increases in same-store sales.
Same-Store Sales. Same-store sales reflect the change in year-over-year sales from services performed and retail sales for the same-store base. We define
the same-store base to include those centers open for at least 52 full weeks. This measure highlights the performance of existing centers, while excluding
the impact of new center openings and closures. We review same-store sales for corporate-owned centers as well as franchisee-owned centers. Same-store
sales growth is driven by increases in the number of transactions and average transaction size.
New Center Openings. The number of new center openings reflects centers opened during a particular reporting period for both franchisee-owned and
corporate-owned centers, less centers closed during the same period. Opening new centers is an integral part of our growth strategy, and we expect the
majority of our future new centers to be franchisee-owned. Before we obtain the certificate of occupancy or report any revenue from new corporate-owned
centers, we incur pre-opening costs, such as rent expense, labor expense and other operating expenses. Some of our centers open with an initial start-up
period of higher-than-normal marketing and operating expenses, particularly as a percentage of monthly revenue.
Average Unit Volume (“AUV”). AUV consists of the average annual system-wide sales of all centers that have been open for a trailing 52-week period or
longer. This measure is calculated by dividing system-wide sales during the applicable period for all centers being measured by the number of centers being
measured. AUV allows management to assess our franchisee-owned and corporate-owned center economics. Our AUV growth is primarily driven by
increases in services and retail product sales as centers fill their books of reservations, which we refer to as maturation of centers.
Wax Pass Utilization. We define Wax Pass utilization as the adoption of our Wax Pass program by guests, measured as a percentage of total transactions
conducted using a Wax Pass. Wax Pass utilization allows management to better assess the recurring nature of our business model because it is an indication
of the magnitude of transactions by guests who have made a longer-term commitment to our brand by purchasing a Wax Pass.
Year Ended
(in thousands, except operating data and percentages)
December 25,
2021
December 26,
2020
Number of system-wide centers (at period
end) 853 796
System-wide sales $ 796,507 $ 468,764
Same-store sales 6.7 % (35.6 )%
New center openings 57 46
AUV $ 966 $ 606
(1) Same-store sales increase for the year ended December 25, 2021 is calculated in comparison to the year ended December 28, 2019 due to the significant decline in our sales in 2020 due
to COVID-19. We believe this presents a more meaningful comparison of same-store sales. As described below, we typically remove stores from our calculation of same-store sales if
they are closed for more than six consecutive days. However, given the widespread and unprecedented impact of COVID-19 same-store sales for the year ended December 26, 2020 were
calculated without removing stores that were closed for longer than six days due to COVID-19.
The table below presents changes in the number of system-wide centers for the periods indicated:
Year Ended
December 25,
2021
December 26,
2020
System-wide Centers
Beginning of Period 796 750
Openings 61 52
Closures
(4 )
(6 )
End of Period
853
796
Recent Developments
As more fully described in the notes to consolidated financial statements included in this annual report on Form 10-K, in fiscal year 2021 we completed a
series of transactions including:
• Reorganization Transactions, which among other things, resulted in the Company being appointed as the sole managing member of the EWC
Ventures and the Company entering into the tax receivable agreement ("TRA").
• The initial and secondary public offerings of the Company’s class A common stock; and
45
(1)
• The entry into a new credit agreement consisting of a $180.0 million term loan (“2026 Term Loan”) and a $40.0 million revolving credit facility
(“2026 Revolving Credit Facility”) (together, the “2026 Credit Agreement”) which replaced our previous senior secured credit agreement.
On March 15, 2022, the Company announced that certain of its subsidiaries intend to complete a refinancing of our existing 2026 Credit Agreement with a
new securitized financing facility. The Company intends to replace the 2026 Credit Agreement with a new securitized financing facility expected to be
comprised of $400.0 million principal amount of senior fixed-rate term notes and $40.0 million principal amount of variable funding notes.
For additional information regarding these transactions, see Notes to Consolidated Financial Statements included in this annual report on Form 10-K.
COVID-19 Impact
The Company is continuing to monitor the ongoing COVID-19 pandemic and its impact on its business. Beginning in March 2020, in response to the
COVID-19 pandemic, most franchisees temporarily closed their centers in order to promote the health and safety of its members, team members and their
communities. In April 2020, the entire franchise network was temporarily closed. Beginning in May 2020, certain governors announced steps to restart
non-essential business operations in their respective states and certain centers began to re-open. By June 2021, all of the Company’s nationwide network of
centers had re-opened.
There is a significant amount of uncertainty about the duration and severity of the consequences caused by the COVID-19 pandemic. While governmental
and non-governmental organizations are engaging in efforts to combat the spread and severity of the COVID-19 pandemic and related public health issues,
the full extent to which outbreaks of COVID-19 could impact our business, results of operations and financial condition is still unknown and will depend
on future developments, including new variants of the virus and spikes in cases in the areas where we operate, which are highly uncertain and cannot be
predicted. However, such effects may be material. Our financial statements reflect judgments and estimates that could change in the future as a result of the
COVID-19 pandemic.
Significant Factors Impacting Our Financial Results
We believe there are several important factors that have impacted, and that we expect will continue to impact, our business and results of operations. These
factors include:
New Center Openings. We expect that new centers will be a key driver of growth in our future revenue and operating profit results. Opening new centers is
an important part of our growth strategy, and we expect the majority of our future new centers will be franchisee-owned. Our results of operations have
been and will continue to be materially affected by the timing and number of new center openings each period. As centers mature, center revenue and
profitability increase significantly. The performance of new centers may vary depending on various factors such as the effective management and
cooperation of our franchisee partners, whether the franchise is part of a multi-unit development agreement, the center opening date, the time of year of a
particular opening, the number of licensed wax specialists recruited, and the location of the new center, including whether it is located in a new or existing
market. Our planned center expansion will place increased demands on our operational, managerial, administrative, financial, and other resources.
Same-Store Sales Growth. Same-store sales growth is a key driver of our business. Various factors affect same-store sales, including:
• consumer preferences and overall economic trends;
• the recurring, non-discretionary nature of personal-care services and purchases;
• our ability to identify and respond effectively to guest preferences and trends;
• our ability to provide a variety of service offerings that generate new and repeat visits to our centers;
• the guest experience we provide in our centers;
• the availability of experienced wax specialists;
• our ability to source and deliver products accurately and timely;
• changes in service or product pricing, including promotional activities;
• the number of services or items purchased per center visit;
• center closures in response to state or local regulations due to the COVID-19 pandemic or other health concerns; and
• the number of centers that have been in operation for more than 52 full weeks.
46
A new center is included in the same-store sales calculation beginning 52 full weeks after the center’s opening. If a center is closed for greater than six
consecutive days, the center is deemed a closed center and is excluded from the calculation of same-store sales until it has been reopened for a continuous
52 full weeks.
Overall Economic Trends. Macroeconomic factors that may affect guest spending patterns, and thereby our results of operations, include employment rates,
business conditions, changes in the housing market, the availability of credit, interest rates, tax rates and fuel and energy costs. However, we believe that
our guests see our services as non-discretionary in nature, given the rebound in performance in the second half of fiscal year 2020 despite the COVID-19
pandemic. Therefore, we believe that overall economic trends and related changes in consumer behavior have less of an impact on our business than they
may have for other industries subject to fluctuations in discretionary consumer spending.
Guest Preferences and Demands. Our ability to maintain our appeal to existing guests and attract new guests depends on our ability to develop and offer a
compelling assortment of services responsive to guest preferences and trends. We estimate that more than two-thirds of OOH waxing consumers start
waxing by age 29 or earlier. We also believe that OOH waxing is a recurring need that brings guests back for services on a highly recurring basis which is
reflected in the predictability of our financial performance over time. Our guests’ routine personal-care need for OOH waxing is further demonstrated by
the top 20% of guests who visit us, on average, approximately every four weeks.
Our Ability to Source and Distribute Products Effectively. Our revenue and operating income are affected by our ability to purchase our products and
supplies in sufficient quantities at competitive prices. While we believe our vendors have adequate capacity to meet our current and anticipated demand,
our level of revenue could be adversely affected in the event we face constraints in our supply chain, including the inability of our vendors to produce
sufficient quantities of some products or supplies in a manner that matches market demand from our guests, leading to lost revenue. We depend on two key
suppliers to source our Comfort Wax and one key supplier to source our branded retail products and we are thus exposed to concentration of supplier risk.
Our Ability to Recruit and Retain Qualified Licensed Wax Specialists for our Centers. Our ability to operate our centers is largely dependent upon our
ability to attract and retain qualified, licensed wax specialists. Our unmatched scale enables us to ensure that we universally train our wax specialists at the
highest standards, ensuring that our guests experience consistent level of quality, regardless of the specific center they visit. The combination of consistent
service delivery, across our trained base of wax specialists, along with the payment ease and convenience of our well-known, pre-paid Wax Pass program
fosters loyalty and return visits across our guest base. Over time, our ability to build and maintain a strong pipeline of licensed wax specialists is important
to preserving our current brand position.
Seasonality. Our results are subject to seasonality fluctuations in that services are typically in higher demand in periods leading up to holidays and the
summer season. The resulting demand trend yields higher system-wide sales in the second and fourth quarter of our fiscal year. In addition, our quarterly
results may fluctuate significantly, because of several factors, including the timing of center openings, price increases and promotions, and general
economic conditions.
Components of Results of Operations
Revenue
Product Sales: Product sales consist of revenue earned from sales of our Comfort Wax, other products consumed in administering our wax services and
retail merchandise to franchisees, as well as retail merchandise sold in corporate-owned centers. Revenue on product sales is recognized upon transfer of
control. Our product sales revenue comprised 55.8% and 55.1% of our total revenue for the years ended December 25, 2021 and December 26, 2020,
respectively.
Royalty Fees: Royalty fees are earned based on a percentage of the franchisees’ gross sales, net of retail product sales, as defined in the applicable
franchise agreement, and recognized in the period the franchisees’ sales occur. The royalty fee is 6.0% of the franchisees’ gross sales for such period and is
paid weekly. Our royalty fees revenue comprised 24.4% and 24.8% of our total revenue for the years ended December 25, 2021 and December 26, 2020,
respectively.
Marketing Fees: Marketing fees are earned based on 3.0% of the franchisees’ gross sales, net of retail product sales, as defined in the applicable franchise
agreement, and recognized in the period the franchisees’ sales occur. Additionally, the Company charges a fixed monthly fee to franchisees for search
engine optimization and search engine marketing services, which is due on a monthly basis and recognized in the period when services are provided. Our
marketing fees revenue comprised 13.8% and 13.0% of our total revenue for the years ended December 25, 2021 and December 26, 2020, respectively.
Other Revenue: Other revenue primarily consists of service revenues from our corporate-owned centers and franchise fees, as well as technology fees,
annual brand conference revenues and training, which together represent 6.0% and 7.1% of our total revenue for the years ended December 25, 2021 and
December 26, 2020, respectively. Service revenues from our corporate-owned centers are recognized at the time services are provided. Amounts collected
in advance of the period in which service is rendered are recorded as deferred revenue. Franchise fees are paid upon commencement of the franchise
agreement and are deferred and recognized on a straight-line basis commencing at contract inception through the end of the franchise license term.
Franchise agreements generally have terms of 10 years beginning on the date the center is opened and the initial franchise fees are amortized over a period
47
approximating the term of the agreement. Deferred franchise fees expected to be recognized in periods greater than 12 months from the reporting date are
classified as long-term on the Consolidated Balance Sheets. Technology fees, annual brand conference revenues and training are recognized as the related
services are delivered and are not material to the overall business.
Costs and Expenses
Cost of Revenue: Cost of revenue primarily consists of the direct costs associated with wholesale product and retail merchandise sold, including
distribution and outbound freight costs and inventory obsolescence charges, as well as the cost of materials and labor for services rendered in our corporate-
owned centers.
Selling, General and Administrative Expenses: Selling, general and administrative expenses primarily consist of wages, benefits and other compensation-
related costs, rent, software, and other administrative expenses incurred to support our existing franchise and corporate-owned centers, as well as expenses
attributable to growth and development activities. Also included in selling, general and administrative expenses are accounting, legal, marketing operations,
and other professional fees.
Advertising Expenses: Advertising expenses consist of advertising, public relations, and administrative expenses incurred to increase sales and further
enhance the public reputation of the European Wax Center brand.
Depreciation and Amortization: Depreciation and amortization includes depreciation of property and equipment and capitalized leasehold improvements,
as well as amortization of intangible assets, including franchisee relationships and reacquired area representative rights. Area representative rights represent
an agreement with area representatives to sell franchise licenses and provide support to franchisees in a geographic region. From time to time, the Company
enters into agreements to reacquire certain area representative rights.
Interest Expense: Interest expense consists of interest on our long-term debt, including amounts outstanding under our revolving credit facility,
amortization of debt discount and deferred financing costs and gain and losses on debt extinguishment.
Income Tax Expense: We are subject to U.S. federal, state and local income taxes with respect to our allocable share of any taxable income of EWC
Ventures and are taxed at the statutory corporate tax rates. Income tax expense includes both current and deferred income tax expense.
Noncontrolling Interest: We are the sole managing member of EWC Ventures. Because we manage and operate the business and control the strategic
decisions and day-to-day operations of EWC Ventures and also have a substantial financial interest in EWC Ventures, we consolidate the financial results
of EWC Ventures, and a portion of our net income (loss) is allocated to the non-controlling interest to reflect the entitlement of the EWC Ventures Post-IPO
Members to a portion of EWC Ventures’ net income (loss).
48
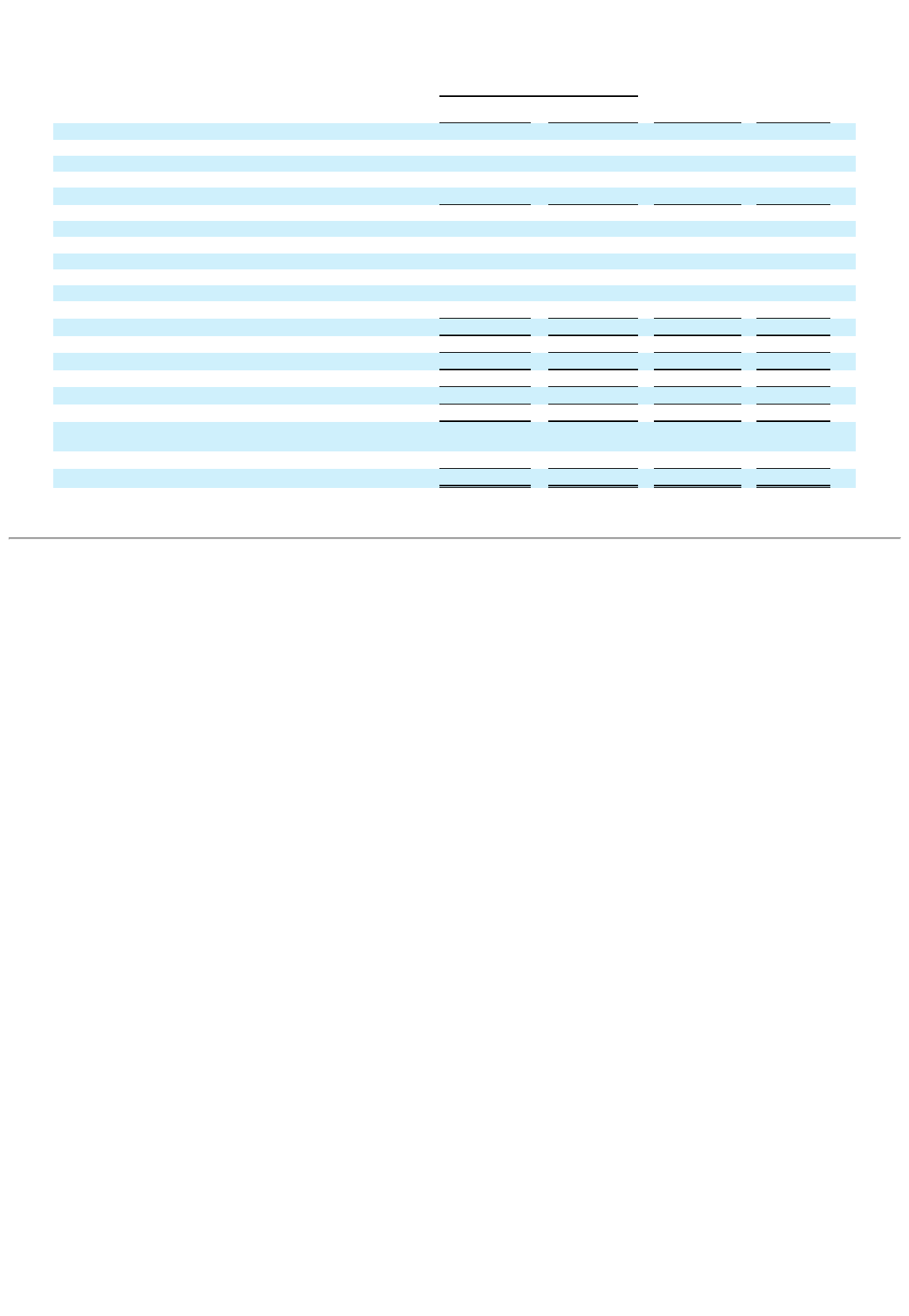
Results of Operations
The following tables presents our Consolidated Statements of Operations for each of the periods indicated (amounts in thousands, except percentages):
For the Years Ended
December 25,
2021
December 26,
2020
$
Change
%
Change
Revenue:
Product sales $ 99,740 $ 56,977 $ 42,763 75.1 %
Royalty fees 43,648 25,674 17,974 70.0 %
Marketing fees 24,610 13,465 11,145 82.8 %
Other revenue
10,680
7,291
3,389
46.5 %
Total revenue 178,678 103,407 75,271 72.8 %
Operating expenses:
Cost of revenue 46,841 35,508 11,333 31.9 %
Selling, general and administrative 61,812 38,997 22,815 58.5 %
Advertising 24,990 11,495 13,495 117.4 %
Depreciation and amortization 20,333 19,582 751 3.8 %
Loss on disposal of assets and non-cancellable contracts
335
1,044
(709 )
(67.9 )%
Total operating expenses
154,311
106,626
47,685
44.7 %
Income (loss) from operations
24,367
(3,219 )
27,586
857.0 %
Interest expense
20,286
18,276
2,010
11.0 %
Income (loss) before income taxes
4,081
(21,495 )
25,576
119.0 %
Income tax expense
114
—
114
—
Net income (loss)
$ 3,967
$ (21,495 )
$ 25,462
118.5 %
Less: net income (loss) attributable to EWC Ventures, LLC prior
to the Reorganization Transactions 10,327 (21,495 ) 31,822 148.0 %
Less: net loss attributable to noncontrolling interests
(2,945 )
—
(2,945 )
—
Net loss attributable to European Wax Center, Inc.
$ (3,415 )
$ —
$ (3,415 )
—
49
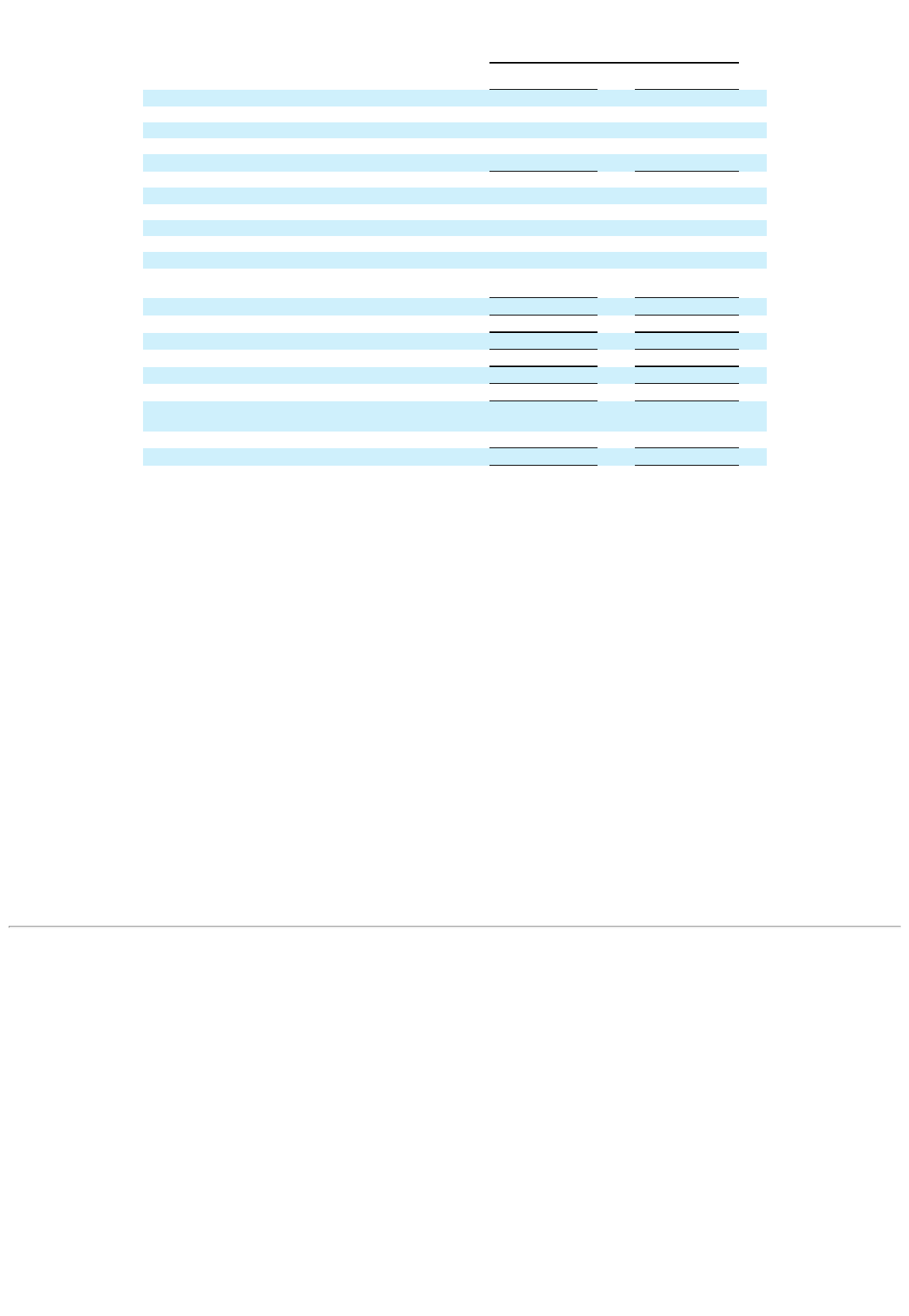
The following table presents the components of our Consolidated Statements of Operations for each of the periods indicated, as a percentage of revenue:
For the Years Ended
December 25,
2021
December 26,
2020
Revenue:
Product sales 55.8 % 55.1 %
Royalty fees 24.4 % 24.8 %
Marketing fees 13.8 % 13.0 %
Other revenue
6.0 %
7.1 %
Total revenue 100.0 % 100.0 %
Costs and expenses:
Cost of revenue 26.2 % 34.3 %
Selling, general and administrative 34.6 % 37.7 %
Advertising 14.0 % 11.1 %
Depreciation and amortization 11.4 % 18.9 %
Loss on disposal of assets and non-cancellable
contracts
0.2 %
1.0 %
Total operating expenses
86.4 %
103.1 %
Income (loss) from operations
13.6 %
(3.1 )%
Interest expense
11.4 %
17.7 %
Income (loss) before income taxes
2.3 %
(20.8 )%
Income tax expense
0.1 %
—
Net income (loss)
2.2 %
(20.8 )%
Less: net income (loss) attributable to EWC Ventures,
LLC prior to the Reorganization Transactions 5.7 % (20.8 )%
Less: net loss attributable to noncontrolling interests
(1.6 )%
—
Net loss attributable to European Wax Center, Inc.
(1.9 )%
—
Comparison of the Years Ended December 25, 2021 and December 26, 2020
Revenue
Total revenue increased $75.3 million, or 72.8%, to $178.7 million during the year ended December 25, 2021, compared to $103.4 million for the year
ended December 26, 2020. The increase in total revenue was largely due to our results for the year ended December 26, 2020 being impacted by center
closures and restrictions stemming from the COVID-19 pandemic. In addition, we had 57 new center openings which became operational during the period
from December 27, 2020 to December 25, 2021.
Product Sales
Product sales increased $42.8 million, or 75.1%, to $99.7 million during the year ended December 25, 2021, compared to $57.0 million for the year ended
December 26, 2020. The increase in product sales during the year ended December 25, 2021 was primarily due to the negative impact of center closures
and restrictions resulting from the COVID-19 pandemic on product sales during the year ended December 26, 2020. In addition, the increase in product
sales was also partially attributable to shipments of a new product line to franchisees in the current year and new center openings which became operational
during the period from December 27, 2020 to December 25, 2021.
Royalty Fees
Royalty fees increased $18.0 million, or 70.0%, to $43.6 million during the year ended December 25, 2021, compared to $25.7 million for the year ended
December 26, 2020. The increase in royalty fees during the year ended December 25, 2021 was the result of the negative impact of the COVID-19
pandemic on network revenues during the year ended December 26, 2020. In addition, the increase in royalty fees was also partially attributable to new
center openings which became operational during the period from December 27, 2020 to December 25, 2021.
Marketing Fees
Marketing fees increased $11.1 million, or 82.8%, to $24.6 million during the year ended December 25, 2021, compared to $13.5 million for the year
ended December 26, 2020. Marketing fees increased primarily due to the negative impact of the COVID-19 pandemic on network revenues during the year
ended December 26, 2020.
50
Other Revenue
Other revenue increased $3.4 million or 46.5%, to $10.7 million during the year ended December 25, 2021, compared to $7.3 million for the year ended
December 26, 2020. The increase in other revenue during the year ended December 25, 2021 was primarily due to the continuing negative impact of
corporate-owned center closures and restrictions resulting from the COVID-19 pandemic during the year ended December 26, 2020. In addition, we waived
technology fees for closed centers in 2020 to provide relief to our franchisees from the adverse impact of the COVID-19 pandemic.
Costs and Expenses
Cost of Revenue
Cost of revenue increased $11.3 million, or 31.9%, to $46.8 million during the year ended December 25, 2021, compared to $35.5 million for the year
ended December 26, 2020. The increase in cost of revenue was largely the result of higher revenues in the current year period as compared to our revenues
for the year ended December 26, 2020, which were impacted by center closures and restrictions stemming from the COVID-19 pandemic. This increase in
cost of revenue was partially offset by an in increase in the inventory obsolescence reserve during the year ended December 26, 2020 related to a pilot
program for certain products with a limited shelf-life that did not have a chance to scale due to COVID-19, as well as a planned product restaging effort
approved by management in the prior year.
Selling, General and Administrative
Selling, general and administrative expenses increased $22.8 million, or 58.5%, to $61.8 million during the year ended December 25, 2021, compared to
$39.0 million for the year ended December 26, 2020. The increase in selling, general and administrative expenses was primarily due to increased payroll
and benefits, professional fees and insurance expenses. The increase in payroll and benefits expense resulted from increased equity-based compensation
due to the modification of certain pre-IPO equity awards and the issuance of new equity awards, cash bonus payments made in connection with our IPO
and increased headcount at our corporate office as we prepared to become a public company. In addition, payroll and benefits expense during the year
ended December 26, 2020 was lower due to our reduction and temporary furlough of certain corporate employees resulting from the impact of COVID-19.
The increase in professional fees in the current year was attributable to preparations for our initial public offering. The increase in insurance expense was
primarily attributable to the purchase of additional lines of coverage due to becoming a public company. These increases were partially offset by a decrease
in commissions resulting from the reacquisition of rights from certain area representatives and a decrease in relocation costs in fiscal year 2021 compared
to fiscal year 2020.
Advertising
Advertising expenses increased $13.5 million, or 117.4%, to $25.0 million during the year ended December 25, 2021, compared to $11.5 million for the
year ended December 26, 2020. The increase in advertising expense was largely attributable to our suspension of marketing activities in the prior year
commensurate with the center closures caused by the COVID-19 pandemic.
Depreciation and Amortization
Depreciation and amortization increased $0.8 million, or 3.8%, to $20.3 million during the year ended December 25, 2021, compared to $19.6 million for
the year ended December 26, 2020. The increase in depreciation and amortization expense was primarily driven by an increase in amortization expense for
the additional reacquired rights from area representatives completed during fiscal years 2020 and 2021.
Interest expense
Interest expense increased $2.0 million, or 11.0%, to $20.3 million during the year ended December 25, 2021, compared to $18.3 million for the year ended
December 26, 2020. The increase in interest expense was primarily due to a $6.3 million loss on debt extinguishment incurred with our refinancing
transaction executed in fiscal year 2021. However, this increase was partially offset by lower interest expense on the 2026 Term Loan due to the reduced
principal balance and interest rate on the Previous Term Loan and the payoff of our Previous Revolving Credit Facility.
Income Tax Expense
We recorded $0.1 million in income tax expense for the year ended December 25, 2021 primarily due to state income taxes. This differs from the federal
statutory income tax rate primarily as a result of the impact of the Company’s full valuation allowance against its net federal and state deferred taxes. Other
drivers of the effective tax rate include non-taxable income generated prior to the Reorganization Transactions, non-taxable income attributable to non-
controlling interest, and the tax effects of stock compensation.
Prior to the Reorganization Transactions, EWC Ventures, our financial reporting predecessor, was a pass-through entity and not subject to income tax. As
such, there was no income tax expense for periods prior to August 4, 2021. We estimate that in future annual periods, our blended statutory tax rate, prior to
valuation allowance consideration, will be approximately 15% of EWC Ventures income or loss before income taxes. This estimated blended statutory tax
rate is based on the current capital structure, excludes discrete or other rate impacting adjustments which may impact the company’s income tax provision
in the future and is based on our
51

blended federal and state statutory tax rates reduced to exclude our non-taxable noncontrolling interest percentage. We expect this estimated blended
statutory tax rate to increase as EWC Ventures Units and the corresponding shares of Class B common stock are exchanged for shares of Class A common
stock because our nontaxable noncontrolling interest earnings will decrease.
Non-GAAP Financial Measures
In addition to our GAAP financial results, we believe the non-GAAP financial measures EBITDA and Adjusted EBITDA are useful in evaluating our
performance. Our non-GAAP financial measures should not be considered in isolation from, or as substitutes for, financial information prepared in
accordance with GAAP. These non-GAAP financial measures are presented for supplemental information purposes only and may be different from
similarly titled metrics or measures presented by other companies. A reconciliation of the non-GAAP financial measures to the most directly comparable
financial measure stated in accordance with GAAP and a further discussion of how we use non-GAAP financial measures is provided below.
EBITDA and Adjusted EBITDA. We define EBITDA as net income (loss) before interest, taxes, depreciation and amortization. We believe that EBITDA,
which eliminates the impact of certain expenses that we do not believe reflect our underlying business performance, provides useful information to
investors to assess the performance of our business. We define Adjusted EBITDA as net income (loss) before interest, taxes, depreciation and amortization,
adjusted for the impact of certain additional non-cash and other items that we do not consider in our evaluation of ongoing performance of our core
operations. These items include exit costs related to leases of abandoned space, IPO-related costs, non-cash equity-based compensation expense, corporate
headquarters office relocation, and other one-time expenses. We believe that Adjusted EBITDA is an appropriate measure of operating performance in
addition to EBITDA because it eliminates the impact of other items that we believe reduce the comparability of our underlying core business performance
from period to period and is therefore useful to our investors in comparing the core performance of our business from period to period. EBITDA and
Adjusted EBITDA may not be comparable to other similarly titled captions of other companies due to differences in methods of calculation.
A reconciliation of net income (loss) to EBITDA and Adjusted EBITDA is set forth below for the periods indicated:
Year Ended
December 25,
2021
December 26,
2020
(in thousands)
Net income (loss) $ 3,967 $ (21,495 )
Interest expense 20,286 18,276
Provision for income taxes 114 —
Depreciation 1,490 1,649
Amortization
18,843
17,933
EBITDA $ 44,700 $ 16,363
Exit costs - lease abandonment — 159
Corporate headquarter relocation — 671
Share-based compensation 11,135 2,052
IPO-related costs 4,971 179
IPO-related compensation expense 2,343 —
Other compensation-related costs 380 577
Other
596
—
Adjusted EBITDA
$ 64,125
$ 20,001
(1) Represents exit costs related to abandoned leases resulting from our corporate headquarters relocation.
(2) Represents costs related to employee relocation, severance and moving fees resulting from our corporate headquarter relocation.
(3) Represents non-cash equity-based compensation expense.
(4) Represents legal, accounting and other costs incurred in preparation for the initial public offering.
(5) Represents cash-based compensation expense recorded in connection with the initial public offering.
(6) Represents costs related to reorganization driven by COVID-19 and buildup of executive leadership team.
(7) Represents non-core operating expenses identified by management. For fiscal year 2021 these costs relate to the settlement of a legal matter and
remeasurement of our tax receivable agreement liability.
Liquidity and Capital Resources
We measure liquidity in terms of our ability to fund the cash requirements of our business operations, including working capital needs, capital expenditures,
contractual obligations and debt service with cash flows from operations and other sources of funding. Our primary sources of liquidity and capital
resources are cash provided from operating activities, cash and cash equivalents on hand,
52
(1)
(2)
(3)
(4)
(5)
(6)
(7)
proceeds from our secured term loan and revolving credit facility and proceeds from the issuance of equity to our members. We had cash and cash
equivalents of $43.3 million as of December 25, 2021.
In August 2021, concurrent with our initial public offering, we entered into a new credit agreement providing for the 2026 Term Loan and 2026 Revolving
Credit Facility. The proceeds from the new term loan were used together with proceeds from our initial public offering to fully repay the Previous Term
Loan and Previous Revolving Credit Facility. See the notes to the consolidated financial statements (Note 10 —Long-Term Debt) contained elsewhere in
this annual report on Form 10-K for more information.
Future payments under the TRA with respect to the purchase of EWC Ventures Units which occurred as part of the IPO and through December 25, 2021
are currently expected to be $115.0 million. Such amounts will be paid when such deferred tax assets are realized as a reduction to income taxes due or
payable. That is, payments under the TRA are only expected to be made in periods following the filing of a tax return in which we are able to utilize certain
tax benefits to reduce our cash taxes paid to a taxing authority. The impact of any changes in the projected obligations under the TRA as a result of changes
in the geographic mix of the Company’s earnings, changes in tax legislation and tax rates or other factors that may impact the Company’s tax savings will
be reflected in income (loss) before income taxes on the Consolidated Statements of Operations in the period in which the change occurs. We recorded a
liability of $59.2 million based on current projections of future taxable income taking into consideration the Company’s full valuation allowance against its
net deferred tax asset.
We believe that our sources of liquidity and capital will be sufficient to finance our continued operations and growth strategy for at least the next twelve
months. Our primary requirements for liquidity and capital are working capital, capital expenditures to grow our network of centers, debt servicing costs,
and general corporate needs. We have in the past, and may in the future, refinance our existing indebtedness with new debt arrangements and utilize a
portion of borrowings to return capital to our stockholders.
We expect capital expenditures for the year ending December 31, 2022 (“fiscal year 2022”) to be approximately $2.5 million. The majority of these capital
expenditures will be to support investments in technology, including enhancements to data infrastructure and our e-commerce platform, as well as general
investments in our corporate-owned centers. We anticipate our cash on hand and future cash flows from operations will provide the funds needed to meet
our anticipated capital expenditure needs in fiscal year 2022.
We also have contractual obligations, including non-cancellable operating leases for office space and various retail locations, with terms expiring through
2032. Rent expense from our operating leases was $2.4 million and $3.1 million for fiscal years 2021 and 2020, respectively, included in selling, general
and administrative expense on the Consolidated Statements of Operations. Future minimum annual rental payments required under these operating lease
agreements as of December 25, 2021 is presented within the notes to our audited consolidated financial statements (Note 12—Commitments and
contingencies), included elsewhere in this annual report on Form 10-K. Additionally, we have various contractual commitments with third parties whereby
we expect to pay $11.3 million in fiscal year 2022, through cash on hand and operating cash flows.
Our assessment of the period of time through which our financial resources will be adequate to support our operations is a forward-looking statement and
involves risks and uncertainties. Our actual results and our future capital requirements could vary because of many factors, including our growth rate, the
timing and extent of spending to acquire new centers and expand into new markets, and the expansion of sales and marketing activities. We may, in the
future, enter into arrangements to acquire or invest in complementary businesses, services and technologies. We have based this estimate on assumptions
that may prove to be wrong, and we could use our available capital resources sooner than we currently expect. We may be required to seek additional
equity or debt financing. In the event that additional financing is required from outside sources, we may not be able to raise it on terms acceptable to us or
at all. If we are unable to raise additional capital when desired, or if we cannot expand our operations or otherwise capitalize on our business opportunities
because we lack sufficient capital, our business, results of operations and financial condition would be adversely affected.
2026 Credit Agreement
Our 2026 Credit Agreement consists of the 2026 Term Loan and the 2026 Revolving Credit Facility. Borrowings under the 2026 Term Loan bear interest at
an index rate as defined in the credit agreement plus an applicable margin of 3.0% (The all-in rate was 3.1% at December 25, 2021). The 2026 Term Loan
requires principal payments payable in quarterly installments with the final scheduled principal payment on the outstanding 2026 Term Loan borrowings
due on August 9, 2026. There were no outstanding borrowings under the 2026 Revolving Credit Facility as of December 25, 2021.
The 2026 Credit Agreement contains certain customary events of default, including in the event of a change of control, and certain covenants and
restrictions that limit the Borrower’s and its subsidiaries’ ability to, among other things, incur additional debt; create liens on certain assets; pay dividends
on or make distributions in respect of their capital stock or make other restricted payments; consolidate, merge, sell, or otherwise dispose of all or
substantially all of their assets; and enter into certain transactions with their affiliates.
The Company is also subject to certain financial maintenance covenants under the 2026 Credit Agreement, which require the Company and its subsidiaries
to (i) not exceed certain specified total net leverage ratios and (ii) not fall below a certain fixed charge coverage ratio, in each case, at the end of each fiscal
quarter.
53
If the Company fails to perform its obligations under these and other covenants, or should any event of default occur, the term loan and revolving credit
facility commitments under the 2026 Credit Agreement may be terminated and any outstanding borrowings, together with accrued interest, under the 2026
Credit Agreement could be declared immediately due and payable. For additional information regarding our long-term debt activity, see Note to
Consolidated Financial Statements (Note 10—Long-term debt) contained elsewhere in this annual report on Form 10-K.
Derivative Instruments and Hedging Activities
In December 2018, we entered an interest rate cap derivative instrument which was designated as a cash flow hedge at inception. Our objective is to
mitigate the impact of interest expense fluctuations on our profitability resulting from interest rate changes by capping the LIBOR component of the
interest rate at 4.5% on $175.0 million of our long-term debt, as the interest rate cap provides for payments from the counterparty when LIBOR rises above
4.5%. The interest rate cap has a $175.0 million notional amount and is effective December 31, 2018, for the monthly periods from and including January
31, 2019 through September 25, 2024. The interest rate cap has a deferred premium; accordingly, the Company will pay a monthly premium for the interest
rate cap over the term of the agreement. The annual premium is equal to 0.11486% on the notional amount.
Changes in the cash flows of interest rate cap derivatives designated as hedges are expected to be highly effective in offsetting the changes in interest
payments on a principal balance equal to the designated derivative’s notional amount, attributable to the hedged risk.
We recognize as assets or liabilities at fair value the estimated amounts we would receive or pay upon a termination of the interest rate cap prior to the
scheduled maturity date. As of December 25, 2021, the fair value of the interest rate cap derivative instrument was estimated to be a liability of $0.3
million, with $0.2 million classified within Other current liabilities and $0.1 million within Other long-term liabilities on the Consolidated Balance Sheet.
The fair value is based on information that is model-driven and whose inputs were observable.
Tax Receivable Agreement
Generally, we are required under the TRA, which is described more fully in “Risk Factors—Risks Related to Our Organization and Structure—We are
required to pay the EWC Ventures' pre-IPO members for certain tax benefits we may claim, and the amounts we may pay could be significant” included
elsewhere in this annual report on Form 10-K to make payments to the EWC Ventures pre-IPO members that are generally equal to 85% of the applicable
cash tax savings, if any, that we actually realize (or are deemed to realize, calculated using certain assumptions) as a result of (i) increases in our allocable
share of certain existing tax basis of the tangible and intangible assets of the Company and adjustments to the tax basis of the tangible and intangible assets
of the Company, in each case as a result of (a) the purchases of EWC Ventures Units (along with the corresponding shares of our Class B common stock)
from certain of the EWC Ventures Post-IPO Members using a portion of the net proceeds from the initial and secondary public offerings or in any future
offering or (b) Share Exchanges and Cash Exchanges by the EWC Ventures pre-IPO members (or their transferees or other assignees) in connection with or
after the initial public offering, (ii) our utilization of certain tax attributes of the Blocker Companies (including the Blocker Companies' allocable share of
certain existing tax basis of EWC Ventures' assets) and (iii) certain other tax benefits related to entering into the TRA, including tax benefits attributable to
payments under the TRA.
Subject to the discussion in the following paragraph below, payments under the TRA will occur only after we have filed our U.S. federal and state income
tax returns and realized the cash tax savings from the favorable tax attributes. The first payment would be due after the filing of our tax return for the year
ended December 25, 2021, which is due March 15, 2022, but the due date can be extended until September 15, 2022. Future payments under the TRA in
respect of future purchases of EWC Ventures Units, Share Exchanges and Cash Exchanges would be in addition to these amounts. Payments under the
TRA are computed by reference to realized tax benefits from attributes subject to the TRA and are expected to be funded by tax distributions made to us by
our subsidiaries similar to how cash taxes would be funded to the extent these attributes did not exist. To the extent we are unable to make payments under
the TRA for any reason (including because our credit agreement restricts the ability of our subsidiaries to make distributions to us), under the terms of the
TRA such payments will be deferred and accrue interest until paid. If we are unable to make payments due to insufficient funds, such payments may be
deferred indefinitely while accruing interest until paid, which could negatively impact our results of operations and could also affect our liquidity in future
periods in which such deferred payments are made.
Under the TRA, as a result of certain types of transactions and other factors, including a transaction resulting in a change of control, we may also be
required to make payments to the EWC Ventures pre-IPO members in amounts equal to the present value of future payments we are obligated to make
under the TRA. If the payments under the TRA are accelerated, we may be required to raise additional debt or equity to fund such payments. To the extent
that we are unable to make payments under the TRA for any reason (including because our credit agreement restricts the ability of our subsidiaries to make
distributions to us), under the terms of the TRA Agreement such payments will be deferred and will accrue interest until paid. If we are unable to make
payments due to insufficient funds to make such payments, such payments may be deferred indefinitely while accruing interest until paid, which could
negatively impact our results of operations and could also affect our liquidity in future periods in which such deferred payments are made.
54
Summary Statements of Cash Flows
The following table sets forth the major components of our Consolidated Statements of Cash Flows for the periods presented (amounts in thousands):
Year Ended
December 25,
2021
December 26,
2020
Net cash provided by (used in):
Operating activities $ 41,346 $ 1,397
Investing activities (8,203 ) (36,843 )
Financing activities
(26,562 )
61,902
Net increase in cash
$ 6,581
$ 26,456
Operating Activities
During the year ended December 25, 2021, net cash provided by operating activities was $41.3 million compared to net cash provided by operating
activities of $1.4 million for the year ended December 26, 2020, an increase of $39.9 million. This improvement was largely attributable to our improved
operating results in fiscal year 2021 compared to the fiscal year 2020, which was severely impacted by the COVID-19 pandemic. In addition, the increase
in working capital requirements in fiscal year 2021 was less than the working capital increase in fiscal year 2020. The increase in working capital in 2021
was primarily attributable to increases of $2.2 million and $9.5 million in accounts receivable and inventory, respectively, resulting from our improved
performance in 2021. These increases in working capital were partially offset by an $8.7 million increase in accounts payable and accrued expenses largely
driven by increased inventory purchases and accrued professional fees.
Investing Activities
During the year ended December 25, 2021 and December 26, 2020, we used $7.6 million and $34.7 million of cash, respectively, for the reacquisition of
area representative rights. Investing activities related to capital expenditures were $0.6 million in fiscal year 2021 and $2.2 million in fiscal year 2020,
respectively.
Financing Activities
During the year ended December 25, 2021 cash used in financing activities was $26.6 million compared to net cash provided by financing activities of
$61.9 million for the for the year ended December 26, 2020. Financing activities during the year ended December 25, 2021 were largely the result of the
Reorganization Transactions, the IPO and secondary public offerings and the debt refinancing transactions and consisted of the following:
• The receipt of cash proceeds from the following sources:
• $212.9 million from our initial and secondary public offerings of Class A common stock, net of underwriting discounts and offering
expenses
• $179.4 million from the 2026 term loan, net of debt discount
• Payments made for the following items:
• $270.6 million to fully repay our Previous Term Loan and Previous Revolving Credit Facility
• $2.4 million for debt extinguishment costs related to the Previous Term Loan
• $1.3 million in deferred financing costs related to the 2026 Term Loan and 2020 Revolving Credit Facility
• $138.4 million to repurchase Class B common stock and an equivalent number of EWC Ventures common units from certain EWC Ventures
members
• $0.9 million to repurchase EWC Class A units which were outstanding prior to the Reorganization Transactions
• $5.3 million in net tax distribution payments made to EWC Ventures members
Financing activities during the year ended December 26, 2020 primarily consisted of additional funding obtained to optimize our cash position in
preparation for a potential, prolonged impact of the COVID-19 pandemic on our business, and to support our investments in the reacquisition of area
representative rights. In fiscal year 2020 we drew down $27.0 million on our revolving credit facility and increased our term loan by $15.0 million. In
addition, we received $24.9 million in contributions from members in exchange for the issuance of the Class D units during the year ended December 26,
2020.
55
Critical Accounting Policies and Estimates
Our financial statements are prepared in accordance with GAAP. The preparation of these financial statements requires us to make estimates and
assumptions that affect the reported amounts of assets, liabilities, revenue, expenses, and related disclosures. We evaluate our estimates and assumptions on
an ongoing basis. Our estimates are based on historical experience and various other assumptions that we believe to be reasonable under the circumstances.
Our actual results could differ from these estimates.
The critical accounting policies requiring estimates, assumptions and judgements that we believe have the most significant impact on our financial
statements are described below.
Revenue Recognition: Revenue from contracts with customers consists primarily of product sales, royalties, marketing fees and other fees resulting from
our franchise agreements.
Product sales primarily include the sale of wax and other products used in the provision of wax services to franchisees, as well as retail merchandise sold in
corporate-owned centers. Revenue on product sales is recognized when control transfers. Generally, customers take control when the risk of loss, title and
insurable risks have transferred to the customer.
Royalty fees are earned based on a percentage of franchisees’ gross sales, net of retail product sales, as defined in the applicable franchise agreement. Our
franchise agreement royalties represent sales-based royalties that are related entirely to our performance obligation under the applicable franchise
agreement and are recognized as franchise sales occur.
Marketing fees are primarily earned based on a percentage of franchisees’ gross sales, net of retail product sales and a fixed fee for search engine
optimization and marketing services.
Franchise fees consist primarily of revenues earned from the delivery of services to franchisees over the franchise license term. The Company’s primary
performance obligations under the franchise license center are granting the use of the European Wax Center trademarks, system, training, preopening
assistance and operating assistance in exchange for franchise fees. The rights to use the Company’s intellectual property and all other services the Company
provides under the applicable franchise agreement are highly interrelated, not distinct within the contract, and therefore accounted for under ASC 606 as a
single performance obligation, which is satisfied by granting certain rights to use our intellectual property over the term of each franchise agreement.
Initial franchise fees paid by the franchisee are recognized as revenue on a straight-line basis commencing at contract inception through the end of the
franchise license term. Franchise agreements generally have terms of ten years. These agreements also convey one extension term up to ten years,
depending on contract terms and if certain conditions are met. Amounts collected in advance for franchise fees are recorded as deferred revenue on the
Consolidated Balance Sheets.
Inventory Valuation: Our inventories are substantially comprised of wax, wholesale products consumed in the application of wax services and European
Wax Center branded products including in-grown hair serums, exfoliates, body washes, lotions, and creams. Inventory is recorded at the lower of cost or
net realizable value using the FIFO method. Net realizable value is the estimated selling price in the ordinary course of business, less reasonably
predictable costs of completion, disposal, and transportation. We record adjustments to our inventory reserves if the cost of a specific product on hand
exceeds the amount we expect to realize from the ultimate sale or disposal of the inventory. These estimates are based on management’s judgment
regarding future demand, age of inventory, and analysis of historical experience. If actual demand or market conditions are different than those projected by
management, future results may be unfavorably or favorably affected by adjustments to these estimates. We do not believe that there is a reasonable
likelihood that there will be a material change in the future estimates or assumptions we use to calculate our inventory reserves.
Goodwill: Goodwill is recognized for the excess of the fair value of an acquired entity over the amounts assigned to identifiable assets acquired and
liabilities assumed in a business combination and is not subject to amortization. Goodwill and intangible assets with indefinite useful lives are not
amortized, but instead are tested for impairment annually on October 1 of the fiscal year, or more frequently if impairment indicators arise. Factors that
could trigger an impairment test include, but are not limited to, underperformance relative to historical or projected future operating results, significant
changes in the manner of use of the acquired assets or the overall business and significant negative industry or economic trends.
Goodwill is tested for impairment annually at a reporting unit level. We have determined that we have one reporting unit which is the same as our sole
operating segment. We first perform a qualitative assessment of goodwill, a Step 0 analysis, to determine whether it is more likely than not that the fair
value of a reporting unit is less than its carrying amount. If we determine that is more likely than not that the fair value of a reporting unit is less than its
carrying value we perform a quantitative impairment test. This test identifies both the existence of and the amount of goodwill impairment by comparing
the fair value of a reporting unit to its carrying amount, including goodwill. If the fair value of a reporting unit exceeds its carrying amount goodwill is not
impaired. If the carrying amount of a reporting unit exceeds its fair value an impairment loss is recognized in amount equal to that excess, limited to the
amount of goodwill allocated to that reporting unit. It is possible that changes in circumstances or changes in management’s judgments, assumptions and
estimates could result in an impairment charge of a portion or all of its goodwill.
56
When performing a quantitative impairment test we make various estimates and assumptions in determining the estimated fair value of our reporting unit
using a combination of discounted cash flow models and valuations based on earnings multiples for guideline public companies and transactions in our
reporting unit’s industry peer group, when externally quoted market prices are not readily available. Discounted cash flow models are highly reliant on
various assumptions, including projected business results, long-term growth factors and discount rate. Management judgement is involved in estimating
these variables, and they include inherent uncertainties since they are forecasting future events. We perform sensitivity analyses by using a range of inputs
to confirm the reasonableness of the long-term growth rate and discount rate estimates.
We performed our annual goodwill impairment test using the qualitative approach as of October 1, 2021 and concluded there was no impairment as of that
date. Factors that we considered in determining that it was not more likely than not that the carrying value of our reporting unit exceeded its fair value
included the results of the quantitative test performed in fiscal year 2020, our forecasts of future operating performance, market conditions, and other
negative factors. In addition, we also considered our market capitalization relative to our net assets as of the testing date. Subsequent to this annual
impairment test, no additional indications of an impairment were identified.
No goodwill impairment charges were recognized for goodwill for fiscal years 2021, 2020 or 2019. For additional information related to our goodwill, see
Notes to Consolidated Financial Statements (Note 8—Goodwill and Intangible Assets, net) contained elsewhere in this annual report on Form 10-K.
Intangible Assets: Intangible assets primarily consist of franchisee relationships, trade names and reacquired area representative rights. Franchisee
relationships are amortized on a straight-line basis over their estimated useful life of ten years. Reacquired rights are amortized on a straight-line basis over
the remaining expected term of the agreement with the area representative. The initial term of the area representative agreements is ten years with an
additional ten-year renewal at the option of the area representative. Trade names were deemed to have an indefinite life. Intangible assets with indefinite
useful lives are not amortized, but instead are tested for impairment annually as of October 1 of the fiscal year, or more frequently if impairment indicators
arise. Factors that could trigger an impairment test include, but are not limited to, underperformance relative to historical or projected future operating
results, significant changes in the manner of use of the acquired assets or the overall business and significant negative industry or economic trends.
Indefinite-lived intangible assets, including our trade names, are tested for impairment at the unit of account. We first perform a qualitative assessment to
determine whether it is more likely than not that the fair value of the asset is less than its carrying amount. When necessary, a quantitative impairment test
is performed by determining the fair value of the intangible asset. If the fair value of the intangible asset is less than its carrying value, an impairment loss
is recognized in an amount equal to the difference. If an intangible asset that is not being amortized is subsequently determined to have a finite useful life,
that asset is tested for impairment. After recognition of the impairment, if any, the asset is amortized prospectively over its estimated remaining useful life
and accounted for in the same manner as other intangible assets that are subject to amortization.
When a quantitative analysis is performed, we test these assets using a “relief-from-royalty” valuation method to determine the fair value. Significant
assumptions inherent in the valuation methodologies include, but are not limited to, future projected business results, growth rates, the discount rate for a
market participant, and royalty rates.
We performed our annual impairment test for our trade name intangible asset using the qualitative approach as of October 1, 2021 and concluded there was
no impairment as of that date. Factors that we considered in determining that it was not more likely than not that the carrying value of our trade name
intangible asset exceeded its fair value included the results of the quantitative test performed in fiscal year 2020, our forecasts of future operating
performance, market conditions, and other negative factors. Subsequent to this annual impairment test, no additional indications of an impairment were
identified.
No impairment charges were recognized for our intangible assets for fiscal years 2021, 2020 or 2019. For additional information related to our intangible
assets, see Notes to the Consolidated Financial Statements (Note 8—Goodwill and Intangible Assets, net) contained elsewhere in this annual report on
Form 10-K.
Income taxes: We account for income taxes in accordance with ASC 740, “Accounting for Income Taxes” (“ASC 740”), using the asset and liability
method. Deferred income taxes are provided on temporary differences between the financial reporting and tax bases of its assets and liabilities. Such net tax
effects of temporary differences are reflected on the Company’s Consolidated Balance Sheets as deferred tax assets and liabilities and are measured by
applying the enacted tax rates in effect for the year in which the temporary differences are expected to reverse.
Deferred tax assets are reduced by a valuation allowance when the Company believes that it is more-likely- than-not that some portion or all of the deferred
tax assets will not be realized. In accordance with ASC 740 we assess whether it is more likely than not that some or all of our deferred tax assets will not
be realized. Significant judgment is required in estimating valuation allowances for deferred tax assets. The realization of a deferred tax asset ultimately
depends on the existence of sufficient taxable income in the applicable carryback or carryforward periods. We consider the nature, frequency, and severity
of current and cumulative losses as well as the reversal of existing deferred tax liabilities, historical and forecasted taxable income (exclusive of reversing
temporary differences and carryforwards) in our assessment. In evaluating such projections, the Company considers its history of profitability and
cumulative earnings/losses, the competitive environment, and general economic conditions. In addition, the Company considers
57
the time frame over which it would take to utilize the deferred tax assets prior to their expiration. To the extent the Company determines that, based on the
weight of available evidence, all or a portion of its valuation allowance is no longer necessary, the Company will recognize the change in the period such
determination occurs. It is possible that such change to the Company’s valuation allowance could have a material impact on our consolidated results of
operations and/or financial position.
Changes in existing tax laws or rates could affect our actual tax results, and future business results may affect the amount of our deferred tax liabilities or
the valuation of our deferred tax assets over time. Due to uncertainties in the estimation process, particularly with respect to changes in facts and
circumstances in future reporting periods it is possible that actual results could differ from the estimates used in previous analyses. Differences between the
anticipated and actual outcomes of these future results could have a material impact on our consolidated results of operations and/or financial position.
ASC 740 prescribes a two-step approach for the recognition and measurement of tax benefits associated with the positions taken or expected to be taken in
a tax return that affect amounts reported in the financial statements. The Company has reviewed and will continue to review the conclusions reached
regarding uncertain tax positions, which may be subject to review and adjustment at a later date based on ongoing analyses of tax laws, regulations and
interpretations thereof. To the extent that the Company’s assessment of the conclusions reached regarding uncertain tax positions changes as a result of the
evaluation of new information, such change in estimate will be recorded in the period in which such determination is made. The Company reports income
tax-related interest and penalties relating to uncertain tax positions, if applicable, as a component of income tax expense.
Tax Receivable Agreement: We entered into the TRA with the EWC Ventures Pre-IPO Members that provides for the payment by the Company to the
EWC Ventures Pre-IPO Members of 85% of the benefits, if any, that the Company realizes, or is deemed to realize (calculated using certain assumptions),
as a result of (i) increases in our allocable share of certain existing tax basis of the tangible and intangible assets of the Company and adjustments to the tax
basis of the tangible and intangible assets of the Company, in each case as a result of (a) the purchases of EWC Ventures Units (along with the
corresponding shares of our Class B common stock) from certain of the EWC Ventures Post-IPO Members using a portion of the net proceeds from the
initial and secondary public offerings or in any future offering or (b) Share Exchanges and Cash Exchanges by the EWC Ventures Pre-IPO Members (or
their transferees or other assignees) in connection with or after the initial public offering, (ii) our utilization of certain tax attributes of the Blocker
Companies (including the Blocker Companies’ allocable share of certain existing tax basis of EWC Ventures’ assets) and (iii) certain other tax benefits
related to entering into the TRA, including tax benefits attributable to payments under the TRA. We record liabilities for amounts payable under the TRA in
the period in which the payment is deemed to be probable.
As of December 25, 2021, future payments under the TRA with respect to the purchase of EWC Ventures Units which occurred as part of the initial public
offering and through December 25, 2021 are expected to be $115.0 million.
Payments made under the TRA represent payments that otherwise would have been made to taxing authorities in the absence of attributes obtained by us as
a result of exchanges by the EWC Ventures Pre-IPO Members. Such amounts will be paid only when a cash tax savings is realized as a result of attributes
subject to the TRA. That is, payments under the TRA are only expected to be made in periods following the filing of a tax return in which we are able to
utilize certain tax benefits to reduce our cash taxes paid to a taxing authority. Amounts payable under the TRA are contingent upon, among other things, the
generation of future taxable income. The projection of future taxable income involves significant judgment. In projecting future taxable income, we
consider our historical results and incorporate certain assumptions including the growth rate of the Company and the amount, character, and timing of the
taxable income in the future. Actual taxable income may differ from our estimates, which could significantly impact the liability under the TRA. The
impact of any changes in the projected obligations under the TRA as a result of changes in the geographic mix of the Company’s earnings, changes in tax
legislation and tax rates or other factors that may impact the Company’s tax savings will be reflected in income before taxes on the Consolidated
Statements of Operations in the period in which the change occurs.
As of December 25, 2021, the TRA liability recorded was $59.2 million based on current projections of future taxable income taking into consideration the
Company’s full valuation allowance against its net deferred tax asset.
JOBS Act
The Company is an emerging growth company as defined in the Jumpstart Our Business Startups Act of 2012 (“JOBS Act”) and may take advantage of
reduced reporting requirements that are otherwise applicable to public companies. Section 107 of the JOBS Act exempts emerging growth companies from
being required to comply with new or revised financial accounting standards until private companies are required to comply with those standards. We have
elected to use the extended transition period for complying with new or revised accounting standards. This may make it difficult to compare our financial
results with the financial results of another public company that is either not an emerging growth company or is an emerging growth company that has
chosen not to take advantage of the extended transition period exemptions because of the potential differences in accounting standards used.
Recent Accounting Pronouncements
See Note 2 to the consolidated financial statements included in this annual report on Form 10-K for more information about recent accounting
pronouncements, the timing of their adoption and our assessment, to the extent we have made one, of the potential impact of the pronouncements on our
financial condition and results of operations and cash flows.
58
Item 7A. Quantitative and Qualitative Disclosures About Market Risk.
Interest Rate Risk
We are exposed to market risk related to changes in interest rates. Our primary exposure to market risk is interest rate sensitivity, which is affected by
changes in the general level of U.S. interest rates, particularly because our term loan and revolving credit facility bear interest at a variable rate.
Our term loan and revolving credit facility bear interest at a variable index rate plus an applicable margin, as defined in the credit agreement. Accordingly,
increases in the variable index rate could increase our interest payments under the term loan and revolving credit facility. An increase of 100 basis points in
the variable index rate would not have a material impact on our financial position or results of operations.
To mitigate our exposure to rising interest rates, we entered into an interest rate cap agreement in December 2018 to limit the variable index rate (1-month
LIBOR) to 4.5% on $175.0 million of principal outstanding on our 2026 Term Loan. The agreement was effective on December 31, 2018 and applies to
interest payments from and including January 31, 2019 through September 25, 2024.
Foreign Currency Risk
We are not currently exposed to significant market risk related to changes in foreign currency exchange rates; however, we have contracted with and may
continue to contract with foreign vendors. Our operations may be subject to fluctuations in foreign currency exchange rates in the future.
Commodity Price Risk
We are exposed to market risk related to changes in commodity prices. Our primary exposure to commodity price risk is the pricing of our wax purchased
from our significant suppliers, which may be adjusted upwards or downwards based on changes in prices of certain raw materials used in the production
process. To date, there have been no price adjustments due to changes in raw material prices.
59
Item 8. Financial Statements and Supplementary Data.
INDEX TO CONSOLIDATED FINANCIAL STATEMENTS
Page
Report of Independent Registered Public Accounting Firm (PCAOB ID No. 34) 61
Consolidated Balance Sheets for the years ended December 25, 2021, and December 26, 2020 62
Consolidated Statements of Operations for the years ended December 25, 2021, December 26, 2020 and December 28, 2019 63
Consolidated Statements of Comprehensive Income (Loss) for the years ended December 25, 2021, December 26, 2020 and December 28,
2019 64
Consolidated Statements of Cash Flows for the years ended December 25, 2021, December 26, 2020 and December 28, 2019 65
Consolidated Statements of Mezzanine Equity and Stockholders’/Members’ Equity for the years ended December 25, 2021, December 26,
2020 and December 28, 2019 66
Notes to Consolidated Financial Statements 67
60
REPORT OF INDEPENDENT REGISTERED PUBLIC ACCOUNTING FIRM
To the stockholders and the Board of Directors of European Wax Center, Inc.
Opinion on the Financial Statements
We have audited the accompanying consolidated balance sheets of European Wax Center, Inc. and subsidiaries (the "Company") as of December 25, 2021
and December 26, 2020, the related consolidated statements of operations, comprehensive income (loss), mezzanine equity and stockholders'/members'
equity, and cash flows, for each of the three years in the period ended December 25, 2021, and the related notes (collectively referred to as the "financial
statements"). In our opinion, the financial statements present fairly, in all material respects, the financial position of the Company as of December 25, 2021
and December 26, 2020, and the results of its operations and its cash flows for each of the three years in the period ended December 25, 2021, in
conformity with accounting principles generally accepted in the United States of America.
Basis for Opinion
These financial statements are the responsibility of the Company's management. Our responsibility is to express an opinion on the Company's financial
statements based on our audits. We are a public accounting firm registered with the Public Company Accounting Oversight Board (United States)
(PCAOB) and are required to be independent with respect to the Company in accordance with the U.S. federal securities laws and the applicable rules and
regulations of the Securities and Exchange Commission and the PCAOB.
We conducted our audits in accordance with the standards of the PCAOB. Those standards require that we plan and perform the audit to obtain reasonable
assurance about whether the financial statements are free of material misstatement, whether due to error or fraud. The Company is not required to have, nor
were we engaged to perform, an audit of its internal control over financial reporting. As part of our audits, we are required to obtain an understanding of
internal control over financial reporting but not for the purpose of expressing an opinion on the effectiveness of the Company’s internal control over
financial reporting. Accordingly, we express no such opinion.
Our audits included performing procedures to assess the risks of material misstatement of the financial statements, whether due to error or fraud, and
performing procedures that respond to those risks. Such procedures included examining, on a test basis, evidence regarding the amounts and disclosures in
the financial statements. Our audits also included evaluating the accounting principles used and significant estimates made by management, as well as
evaluating the overall presentation of the financial statements. We believe that our audits provide a reasonable basis for our opinion.
/s/ DELOITTE & TOUCHE LLP
Dallas, Texas
March 15, 2022
We have served as the Company's auditor since 2019.
61
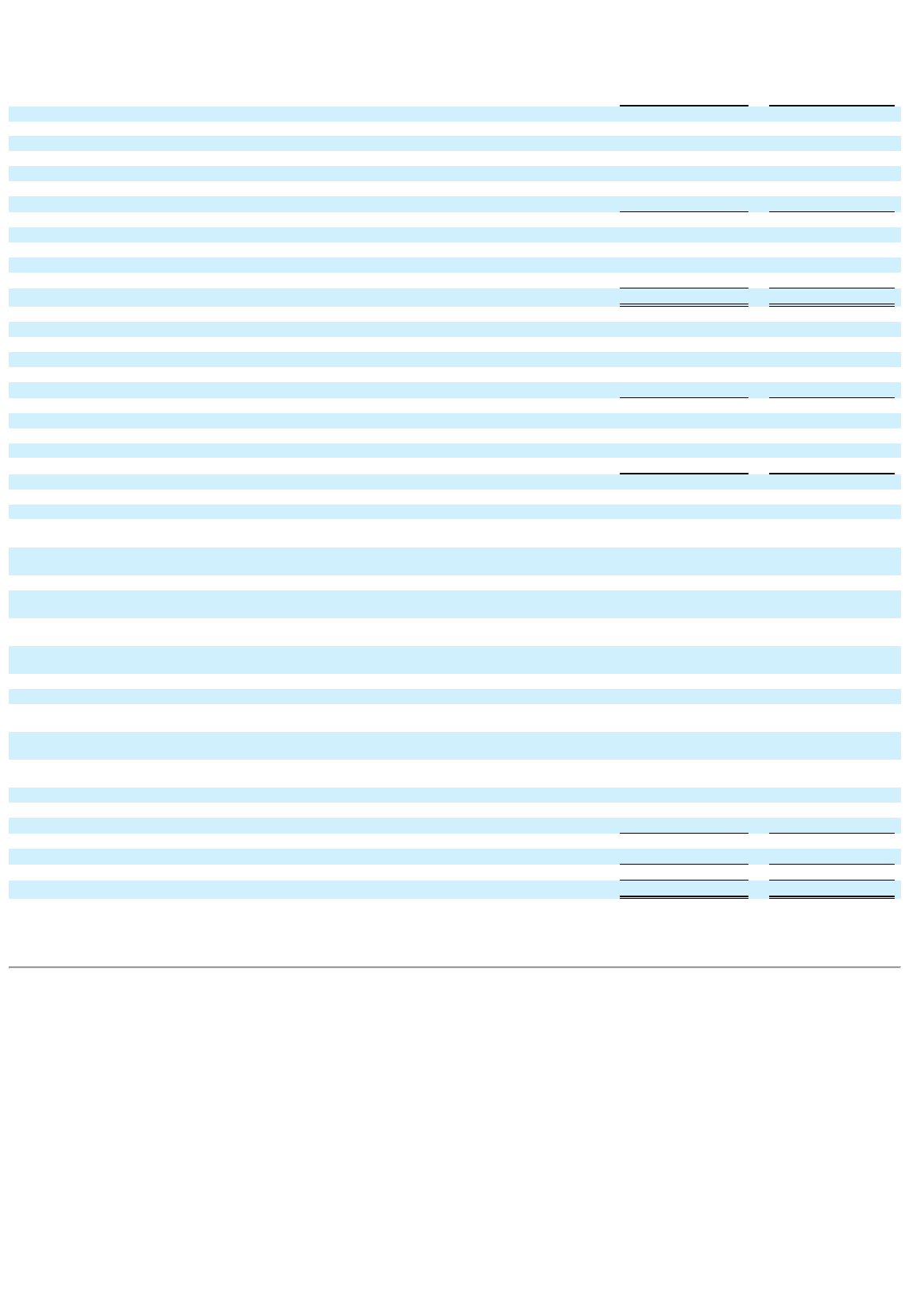
EUROPEAN WAX CENTER, INC. AND SUBSIDIARIES
CONSOLIDATED BALANCE SHEETS
(Amounts in thousands, except share/unit and per share/unit amounts)
December 25,
2021
December 26,
2020
ASSETS
Current assets:
Cash and cash equivalents $ 43,301 $ 36,720
Accounts receivable, net 6,656 5,070
Inventory, net 19,423 10,280
Prepaid expenses and other current assets 5,927 4,574
Advances to related parties
—
689
Total current assets 75,307 57,333
Property and equipment, net 3,863 5,039
Intangible assets, net 201,995 213,267
Goodwill 328,551 328,551
Other non-current assets
3,723
2,710
Total assets
$ 613,439
$ 606,900
LIABILITIES, MEZZANINE EQUITY, AND STOCKHOLDERS'/MEMBERS’ EQUITY
Current liabilities:
Accounts payable and accrued liabilities $ 23,155 $ 13,489
Long-term debt, current portion 5,625 2,428
Deferred revenue, current portion 3,004 2,351
Other current liabilities
182
181
Total current liabilities 31,966 18,449
Long-term debt, net 172,607 262,975
Tax receivable agreement liability 59,167 —
Deferred revenue, net of current portion 6,787 6,528
Other long-term liabilities
1,671
925
Total liabilities 272,198 288,877
Commitments and contingencies (Note 12)
Mezzanine equity:
Class A Founders’ Units (none and 8,309,193 Class A Founders’ Units authorized, issued and outstanding as of
December 25, 2021 and December 26, 2020, respectively) — 89,240
Class D Units (none and 2,500,000 Class D Units authorized, issued and outstanding as of December 25, 2021
and December 26, 2020, respectively; aggregate liquidation preference of $26,670 as of December 26, 2020) — 24,909
Members’ equity:
Class A Units (none and 26,401,089 Class A Units authorized, issued and outstanding as of December 25, 2021
and December 26, 2020, respectively) — 265,791
Class B Unit (none and 1 Class B Unit authorized, issued and outstanding as of December 25, 2021 and
December 26, 2020, respectively) — —
Class C Units (none and 1,000 Class C Units authorized, issued and outstanding as of December 25, 2021 and
December 26, 2020, respectively) — —
Members’ deficit: — (61,390 )
Stockholders’ equity:
Preferred stock ($0.00001 par value, 100,000,000 shares authorized, none issued and outstanding as of
December 25, 2021.) — —
Class A common stock ($0.00001 par value, 600,000,000 shares authorized, 36,932,423 shares issued and
outstanding as of December 25, 2021) 0 —
Class B common stock ($0.00001 par value, 60,000,000 shares authorized, 26,700,477 shares issued and
outstanding as of December 25, 2021) 0 —
Additional paid-in capital 182,919 —
Accumulated deficit (3,487 ) —
Accumulated other comprehensive loss
(45 )
(527 )
Total stockholders' equity attributable to European Wax Center, Inc. 179,387 —
Noncontrolling interests
161,854
—
Total stockholders' equity/member's equity
341,241
318,023
Total liabilities, mezzanine equity and stockholders'/member's equity
$ 613,439
$ 606,900
The accompanying notes are an integral part of these consolidated financial statements.
62
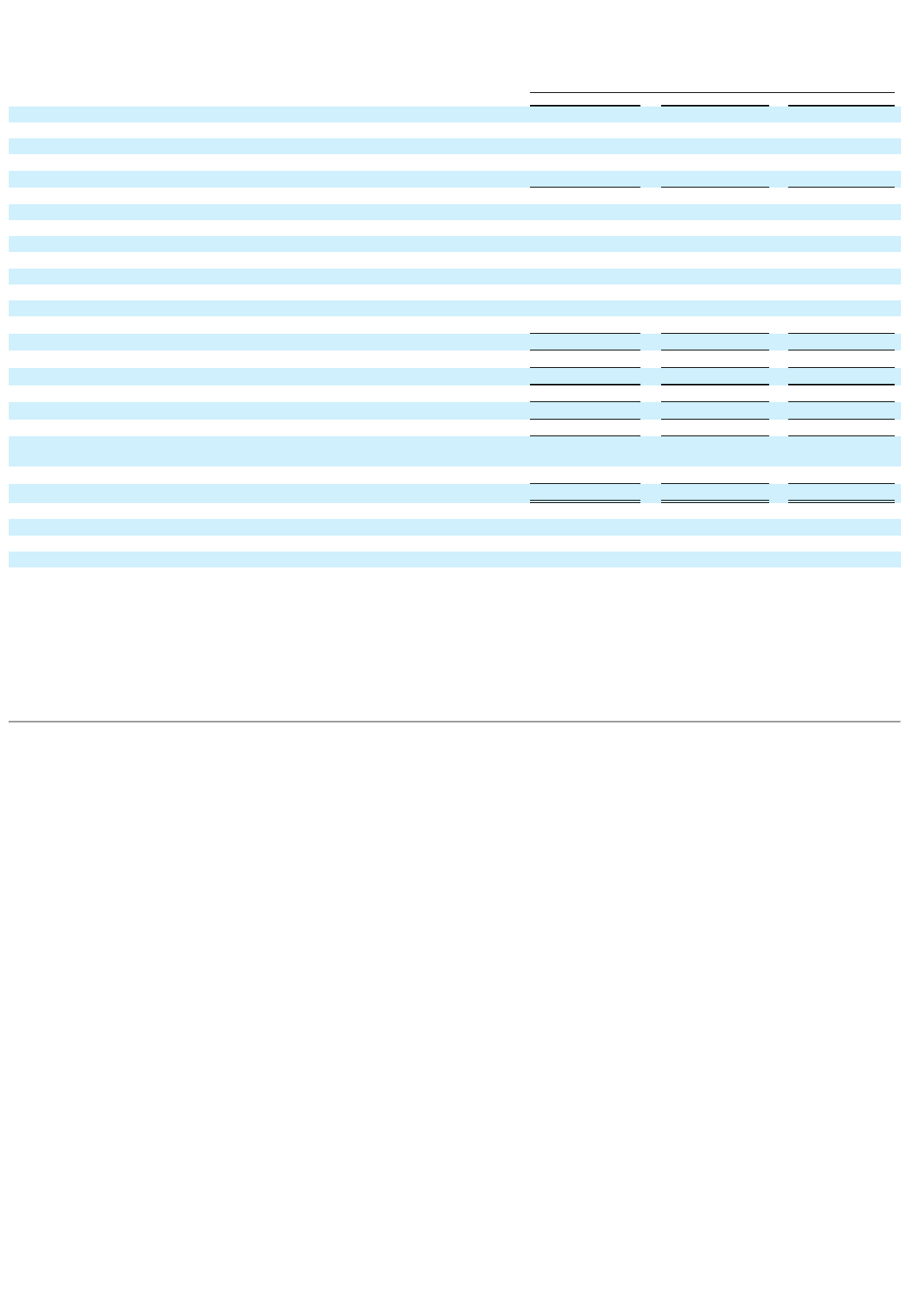
EUROPEAN WAX CENTER, INC. AND SUBSIDIARIES
CONSOLIDATED STATEMENTS OF OPERATIONS
(Amounts in thousands, except unit and per unit amounts)
For the Years Ended
December 25, 2021
December 26, 2020
December 28, 2019
REVENUE
Product sales $ 99,740 $ 56,977 $ 83,620
Royalty fees 43,648 25,674 36,737
Marketing fees 24,610 13,465 21,972
Other revenue
10,680
7,291
11,868
Total revenue 178,678 103,407 154,197
OPERATING EXPENSES
Cost of revenue 46,841 35,508 40,898
Selling, general and administrative 61,812 38,997 64,967
Advertising 24,990 11,495 21,132
Depreciation and amortization 20,333 19,582 15,534
Loss on disposal of assets and non-cancellable contracts 335 1,044 4,451
Impairment of internally developed software — — 18,183
Gain on sale of centers
—
—
(2,120 )
Total operating expenses
154,311
106,626
163,045
Income (loss) from operations
24,367
(3,219 )
(8,848 )
Interest expense
20,286
18,276
15,548
Income (loss) before income taxes
4,081
(21,495 )
(24,396 )
Income tax expense
114
—
—
NET INCOME (LOSS)
$ 3,967
$ (21,495 )
$ (24,396 )
Less: net income (loss) attributable to EWC Ventures, LLC prior to the Reorganization
Transactions 10,327 (21,495 ) (24,396 )
Less: net loss attributable to noncontrolling interests
(2,945 )
—
—
NET LOSS ATTRIBUTABLE TO EUROPEAN WAX CENTER, INC.
$ (3,415 )
$ —
$ —
Basic and diluted net loss per share
Class A Common Stock $ (0.11 ) — —
Basic and diluted weighted average shares outstanding
Class A Common Stock 32,234,507 — —
(1) Includes the following amounts paid to related parties, see Note 18 117 200 200
(2) EWC Ventures, our financial reporting predecessor, is not subject to income taxes. As such, there was no income tax expense recorded in fiscal years 2019, 2020 and the period prior to
August 4, 2021. See Note 19 for more information.
(3) Basic and diluted loss per share of Class A common stock is applicable only for the period from August 4, 2021 through December 25, 2021. See Note 20 for the calculation of the numbers of
shares used in computation of net loss per share of Class A common stock and the basis for computation of net loss per share.
The accompanying notes are an integral part of these consolidated financial statements.
63
(1)
(2)
(3)
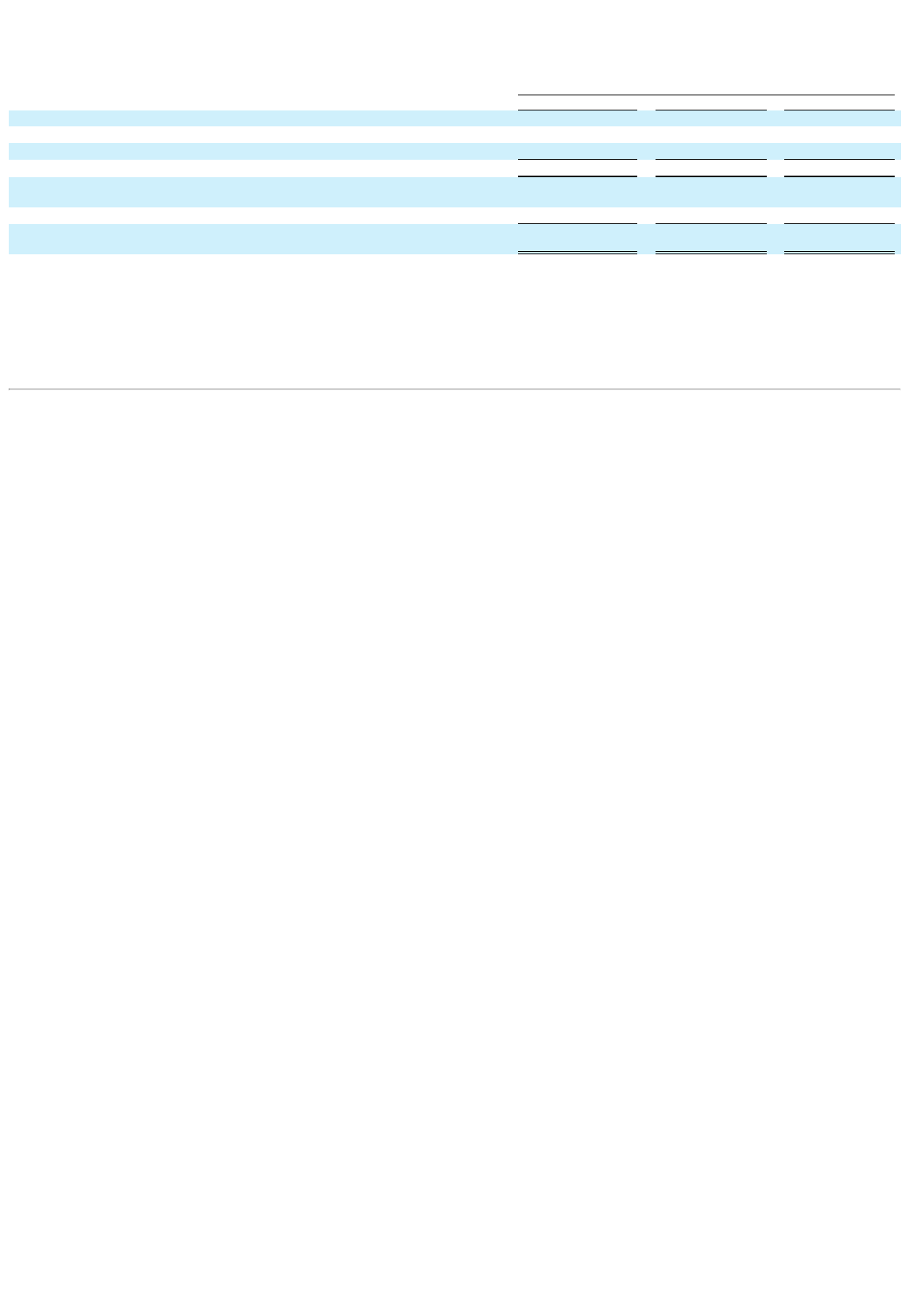
EUROPEAN WAX CENTER, INC. AND SUBSIDIARIES
CONSOLIDATED STATEMENTS OF COMPREHENSIVE INCOME (LOSS)
(Amounts in thousands)
For the Years Ended
December 25, 2021
December 26, 2020
December 28, 2019
NET INCOME (LOSS) $ 3,967 $ (21,495 ) $ (24,396 )
Items included in other comprehensive loss:
Unrealized gain (loss) on cash flow hedge
286
208
(405 )
TOTAL COMPREHENSIVE INCOME (LOSS)
$ 4,253
$ (21,287 )
$ (24,801 )
Less: total comprehensive income (loss) attributable to EWC Ventures, LLC prior to
the Reorganization Transactions 10,409 (21,287 ) (24,801 )
Less: total comprehensive loss attributable to non-controlling interests
(2,848 )
—
—
COMPREHENSIVE LOSS ATTRIBUTABLE TO EUROPEAN WAX CENTER,
INC.
$ (3,308 )
$ —
$ —
The accompanying notes are an integral part of these consolidated financial statements.
64
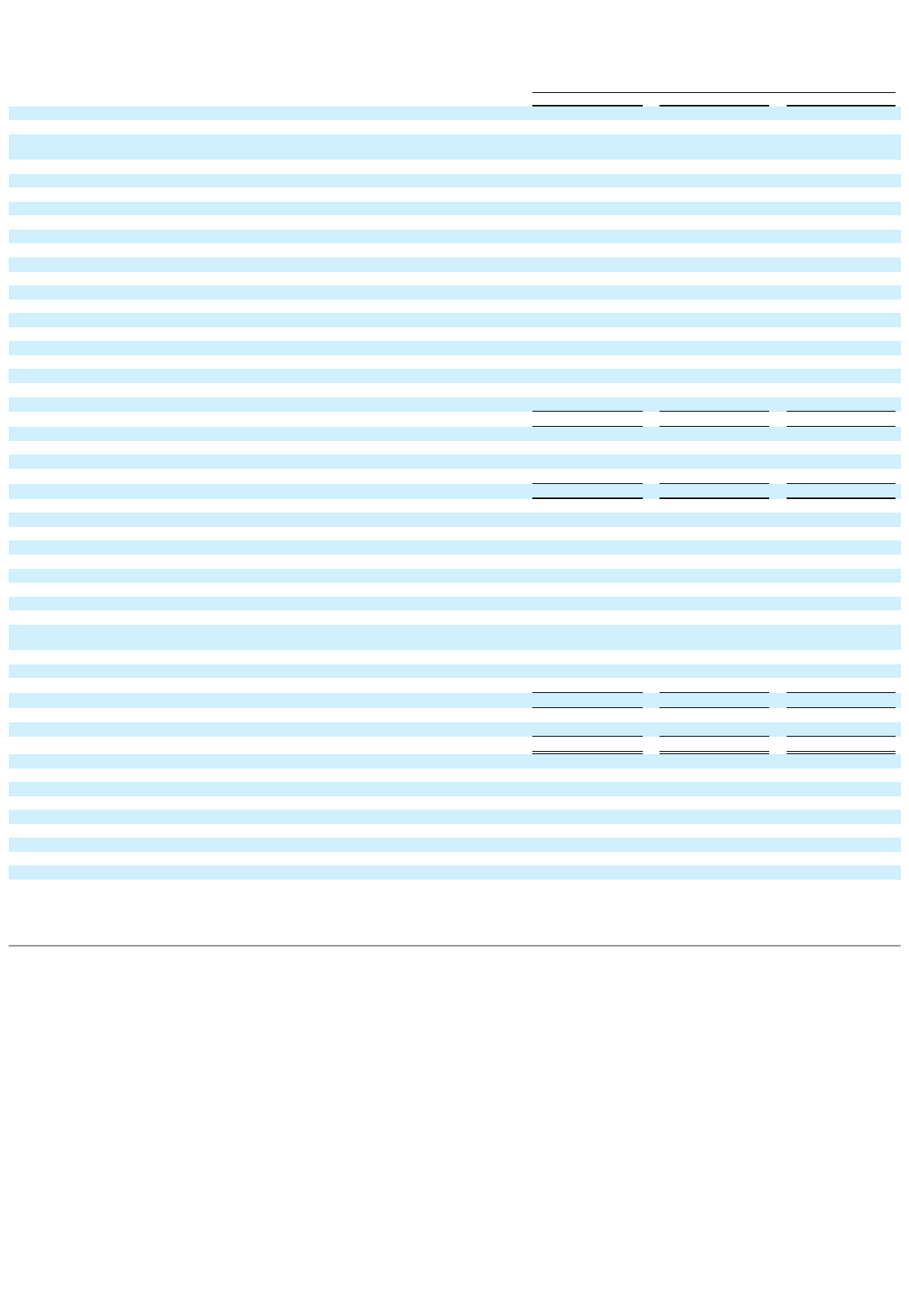
EUROPEAN WAX CENTER, INC. AND SUBSIDIARIES
CONSOLIDATED STATEMENTS OF CASH FLOWS
(Amounts in thousands)
For the Years Ended
December 25, 2021
December 26, 2020
December 28, 2019
Cash flows from operating activities:
Net income (loss) $ 3,967 $ (21,495 ) $ (24,396 )
Adjustments to reconcile net income (loss) to net cash provided by
operating activities:
Depreciation and amortization 20,333 19,582 15,534
Amortization of deferred financing costs 1,044 1,284 1,138
Loss on debt extinguishment 6,313 — —
Loss on noncancellable contracts — 1,085 2,532
Impairment of internally developed software — — 18,183
Loss on write-down of obsolete inventory 317 6,656 552
Provision for bad debts 616 — —
Loss (gain) on disposal of property and equipment 335 (41 ) 1,920
Gain on sale of centers — — (2,120 )
Remeasurement of tax receivable agreement liability 195 — —
Equity compensation 11,135 2,052 1,570
Changes in assets and liabilities:
Accounts receivable (2,185 ) 1,721 1,096
Inventory (9,460 ) 5,101 (5,355 )
Prepaid expenses and other assets (1,916 ) (2,124 ) (435 )
Accounts payable and accrued liabilities 8,707 (10,499 ) 2,076
Deferred revenue 912 (666 ) 1,250
Other long-term liabilities
1,033
(1,259 )
1,156
Net cash provided by operating activities
41,346
1,397
14,701
Cash flows from investing activities:
Purchases of property and equipment (559 ) (2,158 ) (9,343 )
Reacquisition of area representative rights (7,644 ) (34,685 ) (33,189 )
Cash received for sale of centers
—
—
1,838
Net cash used in investing activities
(8,203 )
(36,843 )
(40,694 )
Cash flows from financing activities:
Proceeds on line of credit — 27,000 —
Payments on line of credit (30,000 ) — (3,500 )
Proceeds on long-term debt 179,370 15,000 40,000
Principal payments on long-term debt (240,553 ) (2,397 ) (2,050 )
Deferred loan costs (1,294 ) (763 ) (638 )
Payments of debt extinguishment costs (2,446 ) — —
Distributions to EWC Ventures LLC members (5,270 ) (1,847 ) (5,194 )
Contributions from EWC Ventures LLC members — 24,909 —
Proceeds from public offerings of Class A common stock, net of underwriting discounts and offering
expenses 212,941 — —
Repurchase of Class A Units (942 ) — —
Repurchase of Class B common stock and EWC Ventures common units (138,368 ) — —
Advances to related parties, net
—
—
(811 )
Net cash (used in) provided by financing activities
(26,562 )
61,902
27,807
Net increase in cash 6,581 26,456 1,814
Cash, beginning of period
36,720
10,264
8,450
Cash, end of period
$ 43,301
$ 36,720
$ 10,264
Supplemental cash flow information:
Cash paid for interest $ 11,763 $ 16,469 $ 17,342
Cash paid for income taxes $ 10 $ — $ —
Non-cash investing activities:
Property purchases included in accounts payable and accrued liabilities $ 89 $ 33 $ 148
Reacquired rights purchased included in accounts payable and accrued liabilities $ — $ — $ 2,183
Non-cash financing activities:
Non-cash equity distributions $ 689 $ 122 $ —
Public offering expenses in accounts payable and accrued liabilities $ 870 $ — $ —
The accompanying notes are an integral part of these consolidated financial statements.
65
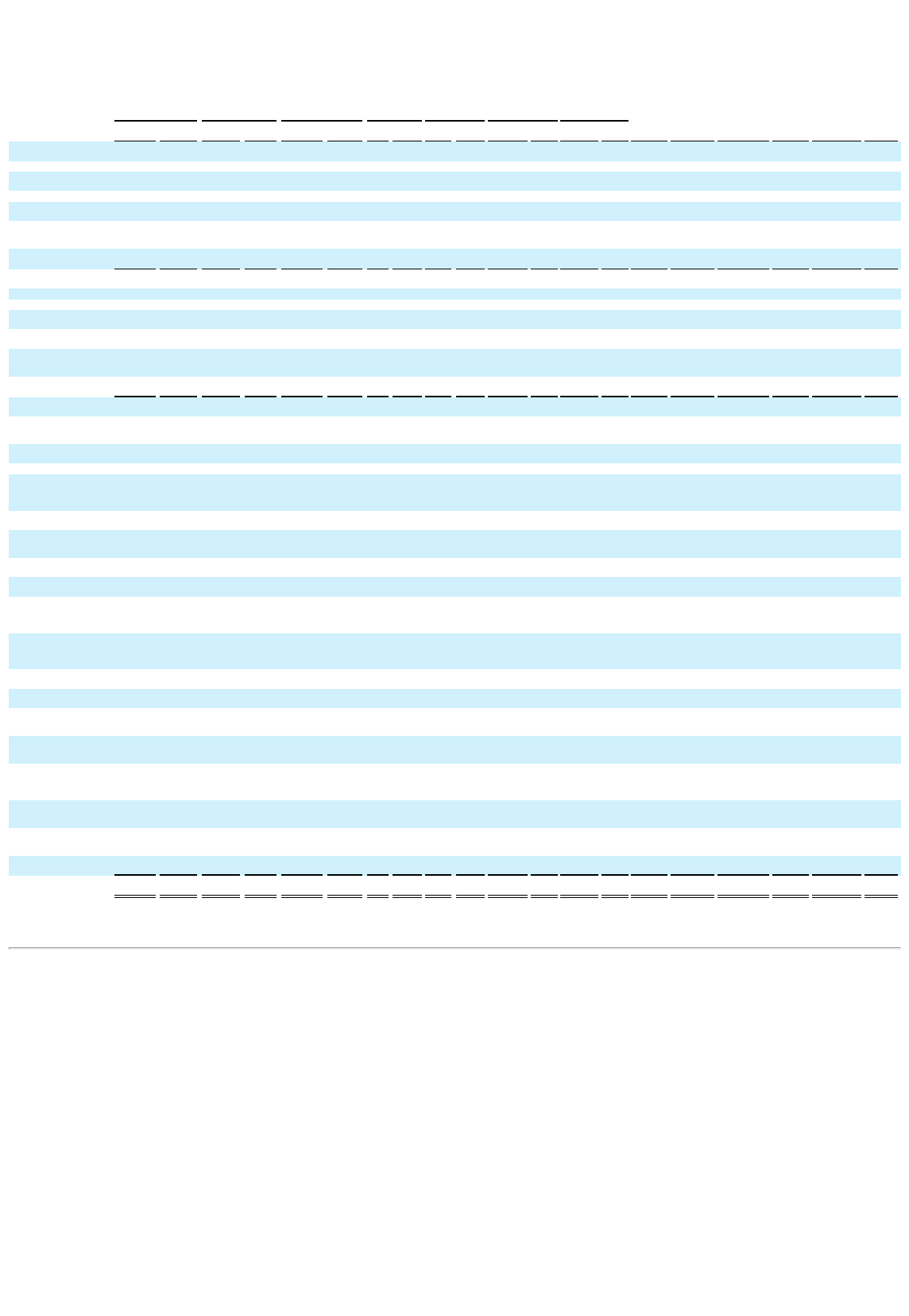
EUROPEAN WAX CENTER, INC. AND SUBSIDIARIES
CONSOLIDATED STATEMENTS OF MEZZANINE EQUITY AND STOCKHOLDERS'/MEMBERS’ EQUITY
(Amounts in thousands, except unit and per unit amounts)
Accumulated
MEZZANINE EQUITY STOCKHOLDERS'/MEMBERS’ EQUITY
Addition
al other
Class A Founders’
Units Class D Units Class A Units Class B Units Class C Units Class A Shares Class B Shares
paid-in
Accumulat
ed
comprehensi
ve
Member'
s
Noncontrolli
ng Total
Units Amount Units Amount Units Amount
Unit
s
Amou
nt Units
Amou
nt Shares
Amou
nt Shares
Amou
nt capital deficit loss Deficit interest equity
Balance at December 29,
2018 8,309,193 $ 83,652 — $ —
26,401,08
9 $
265,79
1 1 $ — 1,000 $ — — $ — — $ — $ — $ — $ (330 )$ (6,170 )$ — $
259,29
1
Equity compensation — — — — — — — — — — — — — — — — — 1,570 — 1,570
Cumulative impact of ASC
606 adoption — — — — — — — — — — — — — — — — — (200 ) — (200 )
Distributions — — — — — — — — — — — — — — — — — (5,194 ) — (5,194 )
Unrealized loss on cash flow
hedge — — — — — — — — — — — — — — — — (405 ) — — (405 )
Accretion of Class A
Founders’ Units to
redemption value — 20,628 — — — — — — — — — — — — — — — (20,628 ) —
(20,62
8 )
Net loss
— — — — — — — — — — — — — — — — — (24,396 ) —
(24,39
6 )
Balance at December 28,
2019 8,309,193 104,280 — —
26,401,08
9
265,79
1 1 — 1,000 — — — — — — — (735 ) (55,018 ) —
210,03
8
Equity compensation — — — — — — — — — — — — — — — — — 2,052 — 2,052
Distributions — — — — — — — — — — — — — — — — — (1,969 ) — (1,969 )
Unrealized gain on cash flow
hedge — — — — — — — — — — — — — — — — 208 — — 208
Contributions from members,
net of issuance costs of $91 — —
2,500,00
0 24,909 — — — — — — — — — — — — — — — —
Accretion of Class A
Founders’ Units to
redemption value — (15,040 ) — — — — — — — — — — — — — — — 15,040 — 15,040
Net loss
— — — — — — — — — — — — — — — — — (21,495 ) —
(21,49
5 )
Balance at December 26,
2020 8,309,193 89,240
2,500,00
0 24,909
26,401,08
9
265,79
1 1 — 1,000 — — — — — — — (527 ) (61,390 ) —
203,87
4
Equity Compensation prior to
the reorganization
transactions — — — — — — — — — — — — — — — — — 667 — 667
Distributions prior to the
reorganization transactions — — — — — — — — — — — — — — — — — (5,784 ) — (5,784 )
Repurchase of Class A Units — — — — (89,919 ) (942 ) — — — — — — — — — — — — — (942 )
Accretion of Class Founders’
Units to redemption value
prior to reorganization
transactions — 112,403 — — — — — — — — — — — — — — —
(112,40
3 ) —
(112,4
03 )
Net income prior to
reorganization transactions — 10,327 10,327
Unrealized gain on cash flow
hedge prior to reorganization
transactions — — — — — — — — — — — — — — — — 82 — — 82
Effect of reorganization
transactions
(8,309,19
3 )
(201,64
3 )
(2,500,00
0 )
(24,90
9 )
(26,311,1
70 )
(264,84
9 ) (1 ) —
(1,00
0 ) —
21,540,98
2 0
36,740,95
6 0 123,615 — 275 168,583 198,928
226,55
2
Issuance of Class A Common
Stock, net of offering costs — — — — — — — — — —
12,530,80
5 0 — — 212,071 — — — —
212,07
1
Repurchase of Class B
Common Stock and EWC
Ventures Units from selling
shareholders
(7,070,01
5 ) 0
(138,36
8 ) — —
(138,3
68 )
Exchange of Class B
Common Stock and EWC
Ventures Units for Class A
Common Stock — — — — — — — — — — 2,850,000 0
(2,850,00
0 ) 0 — — — — — —
Vesting of restricted stock
units — — — — — — — — — — 10,636 0 — — 0 — — — — —
Forfeiture of unvested
incentive units — — — — — — — — — — — — (120,464 ) 0 0 — — — — —
Equity compensation
subsequent to the
reorganization transactions — — — — — — — — — — — — — — 10,468 — — — — 10,468
Distributions subsequent to
the reorganization
transactions — — — — — — — — — — — — — — (103 ) (72 ) — — — (175 )
Establish tax receivable
agreement liability
subsequent to the
reorganization transactions — — — — — — — — — — — — — — (58,972 ) — —
(58,97
2 )
Unrealized gain on cash flow
hedge subsequent to the
reorganization transactions — — — — — — — — — — — — — — — — 107 — 97 204
Impact of change in
ownership on noncontrolling
interest — — — — — — — — — — — — — — 34,208 — 18 — (34,226 ) —
Net loss subsequent to the
reorganization transactions
— — — — — — — — — — — — — — — (3,415 ) — — (2,945 ) (6,360 )
Balance at December 25,
2021 — — — — — — — — — —
36,932,42
3 0
26,700,47
7 0 182,919 (3,487 ) (45 ) — 161,854
341,24
1
The accompanying notes are an integral part of these consolidated financial statements.
66
EUROPEAN WAX CENTER, INC. AND SUBSIDIARIES
NOTES TO CONSOLIDATED FINANCIAL STATEMENTS
(Amounts in thousands, except share/unit and per share/unit amounts)
1. Nature of business and organization
European Wax Center, Inc. (the “Company”) was formed as a Delaware corporation on April 1, 2021. The Company was formed for the purpose of
completing a public offering and related transactions in order to carry on the business of EWC Ventures, LLC ("EWC Ventures") and its subsidiaries.
Through its subsidiaries, the Company is engaged in selling franchises of European Wax Center, distributing facial and body waxing products to
franchisees which are used to perform waxing services and providing branded facial and body waxing products directly to consumers at various locations
throughout the United States.
The Company operates on a fiscal calendar which, in a given year, consists of a 52 or 53 week period ending on the Saturday closest to December 31st. The
fiscal years ended December 25, 2021 (“fiscal year 2021”), December 26, 2020 (“fiscal year 2020”) and December 28, 2019 (“fiscal year 2019”) all
consisted of 52 weeks.
Reorganization Transactions
On August 4, 2021, we completed an internal reorganization which is referred to as the (“Reorganization Transactions”). The Reorganization Transactions
are more fully described in our prospectus dated August 4, 2021 (referred to herein as the “Prospectus”), filed with the Securities and Exchange
Commission (the “SEC”) on August 6, 2021 pursuant to Rule 424(b)(4) of the Securities Act of 1933, as amended. The following actions were taken as a
result of the Reorganization Transactions:
• EWC Ventures made a distribution of $6,512 to its members for the purpose of funding their tax obligations for periods prior to closing of our
initial public offering of the Company's Class A common stock (the "IPO"). $5,823 of the distribution was paid in cash and $689 was made
through settlement of receivables due from related parties.
• The Company was appointed as the sole managing member of EWC Ventures.
• EWC Ventures' limited liability company agreement was amended and restated to provide that, among other things, all of the its outstanding
equity interests consisting of its Class A Units, Class B Unit, Class C Units and Class D Units were reclassified into EWC Ventures non-voting
common units (“EWC Ventures Units”).
• The Company’s certificate of incorporation was amended and restated under which the Company is authorized to issue up to 600,000,000 shares
of Class A common stock, par value $0.00001 per share (“Class A common stock”), 60,000,000 shares of Class B common stock, par value
$0.00001 per share (“Class B common stock”) and 100,000,000 shares of preferred stock, par value $0.00001 per share. The Class A common
stock and Class B common stock each provide holders with one vote on all matters submitted to a vote of stockholders. The holders of Class B
common stock do not have any of the economic rights provided to holders of Class A common stock.
• The Company consummated the mergers of subsidiaries with and into affiliates of General Atlantic (the “Blocker Companies”) and the surviving
entities then merged with and into us.
• As a result of the mergers, the Company acquired existing equity interests in the Company from the owners of the Blocker Companies in
exchange for 21,540,982 shares of the Company's Class A common stock and the rights to receive payments under a tax receivable agreement
(the “TRA”), which is described below.
• The continuing members of EWC Ventures (the “EWC Ventures Post-IPO Members”) subscribed for and purchased 36,740,956 shares of our
Class B common stock at a purchase price of $0.00001 per share. The amount of Class B common stock purchased was equal to the number of
EWC Ventures Units held by the EWC Ventures Post-IPO Members. Subject to certain restrictions EWC Ventures Post-IPO Members have the
right to exchange their EWC Ventures Units, together with a corresponding number of shares of our Class B common stock for, at our option, (i)
shares of the Company's Class A common stock on a one-for-one basis (the “Share Exchange”) or (ii) cash (based on the market price of the
Company's Class A common stock) (the “Cash Exchange”).
• We entered into the TRA with the EWC Ventures' pre-IPO members. See "Summary of Significant Accounting Policies" below and Note 19 -
Income Taxes for more information on the TRA.
Initial Public Offering and Debt Refinancing
On August 4, 2021, the Company's registration statement on Form S-1 was declared effective by the SEC related to the IPO of its Class A common stock.
In connection with the closing of the IPO on August 9, 2021, the following actions were taken:
• The Company issued and sold 9,829,204 shares of its Class A common stock at a price of $17.00 per share for net proceeds of $155,400 after
deducting underwriting discounts and commissions and prior to paying any offering expenses. In addition,
67
certain of the Company's stockholders (the "selling stockholders") sold an additional 2,360,796 shares of the Company's Class A common stock.
The Company received no proceeds from the sale of shares by the selling stockholders. The shares sold by the Company and the selling
stockholders were inclusive of 1,590,000 shares of the Company's Class A common stock sold pursuant to the underwriters' option to purchase
additional shares of the Company's Class A common stock.
• We entered into a new credit agreement consisting of a $180,000 term loan (“2026 Term Loan”) and a $40,000 revolving credit facility (“2026
Revolving Credit Facility”) (together, the “2026 Credit Agreement”). The 2026 term loan and the 2026 revolving credit facility are described in
more detail in Note 10- Long-Term Debt.
• The Company used the proceeds from its IPO to:
o Contribute $104,935 to EWC Ventures in exchange for 6,637,258 EWC Venture Units. EWC Ventures used these funds, together with
proceeds from the 2026 Term Loan and cash on hand to:
▪ Purchase 1,176,468 EWC Ventures Units and corresponding shares of Class B common stock for $20,000 from certain EWC Ventures
Post-IPO Members and employees in satisfaction of the Class C deferred payment obligations (as described in the Prospectus)
▪ Repay all $268,732 of the outstanding term and revolving loans under our previous credit facility
▪ Pay the offering expenses of $9,930
▪ Pay $6,869 of accrued interest, fees and expenses related to the refinancing, as well as other corporate expenses; and
o Purchase 3,191,946 EWC Ventures Units and corresponding shares of Class B common stock for $50,465 from certain EWC Ventures Post-
IPO Members
Immediately following the Reorganization Transactions and the closing of the IPO, EWC Ventures is the predecessor of the Company for financial
reporting purposes. We are a holding company, and our sole material asset is our equity interest in the EWC Ventures. As the sole managing member of
EWC Ventures, the Company operates and controls all of the businesses and affairs of EWC Ventures and has a substantial financial interest in EWC
Ventures. As such, we consolidate EWC Ventures on our consolidated financial statements and record a noncontrolling interest on our Consolidated
Balance Sheets and Consolidated Statements of Operations and Consolidated Statements of Comprehensive Income (Loss) to reflect the entitlement of the
EWC Ventures Post-IPO Members to a portion of EWC Ventures' net income (loss). The Reorganization Transactions were accounted for as a
reorganization of entities under common control and the Company recognized the assets and liabilities received in the reorganization at their historical
carrying amounts as reflected in the historical consolidated financial statements of EWC Ventures.
Secondary Public Offering
On November 15, 2021, we completed a secondary public offering (the “Secondary Offering”) of 2,701,601 shares of our Class A common stock to the
public at a price of $26.25 per share for net proceeds of $67,900 after deducting underwriting discounts and commissions and prior to paying any offering
expenses. In addition, certain of the Company's stockholders (the "selling stockholders") sold an additional 3,297,922 shares of the Company's Class A
common stock. The Company received no proceeds from the sale of shares by the selling stockholders. The shares sold by the Company and the selling
stockholders were inclusive of 782,546 shares of the Company's Class A common stock sold pursuant to the underwriters' option to purchase additional
shares of the Company's Class A common stock. The proceeds from the Secondary Offering were used to purchase to 2,701,601 EWC Ventures Units and
corresponding shares of Class B common stock for $67,900 from certain EWC Ventures Post-IPO Members. In connection with the Secondary Offering we
incurred offering expenses of $1,300.
Share Exchange Transactions
During the year ended December 25, 2021 certain EWC Ventures Post-IPO Members exercised their exchange rights and exchanged 2,850,000 EWC
Ventures Units and the corresponding shares of Class B common stock for 2,850,000 newly issued shares of Class A common stock. These exchange
transactions increased the Company’s ownership interest in EWC Ventures.
2. Summary of significant accounting policies
(a) Basis of presentation and consolidation
The accompanying consolidated financial statements have been presented in conformity with accounting principles generally accepted in the United States
(“GAAP”) and pursuant to the rules and regulations of the SEC and includes the operations of the Company and EWC Ventures and its wholly owned
subsidiaries. EWC Ventures is considered a variable interest entity. The Company is the primary beneficiary of EWC Ventures. As a result, the Company
consolidates EWC Ventures.
EWC Ventures has been determined to be the predecessor for accounting purposes and, accordingly, the consolidated financial statements for periods prior
to the Reorganization Transactions have been adjusted to combine the previously separate entities for presentation purposes. Amounts for the period from
December 30, 2018 through August 4, 2021 presented in the consolidated
68
financial statements and notes to consolidated financial statements herein represent the historical operations of EWC Ventures. The amounts as of
December 25, 2021 and for the period from August 4, 2021 reflect the consolidated operations of the Company.
(b) Use of estimates
The preparation of financial statements in conformity with GAAP requires management to make estimates and assumptions that affect the amounts
reported in the financial statements and accompanying notes. Although these estimates are based on management’s knowledge of current events and actions
it may undertake in the future, they may ultimately differ from actual results. Significant areas where estimates and judgments are relied upon by
management in the preparation of the financial statements include revenue recognition, inventory reserves, the expected life of franchise agreements, the
useful life of reacquired rights, valuation of equity-based compensation awards, and the evaluation of the recoverability of goodwill and long-lived assets,
including indefinite-lived intangible assets. Actual results could differ from those estimates.
(c) Concentrations
Financial instruments that potentially subject the Company to concentrations of credit risk consist principally of cash in financial institutions (in excess of
federally insured limits) and accounts receivable. Concentrations of credit risk with respect to accounts receivable is limited due to the Company’s large
number of franchisees and their dispersion across several geographic areas.
The Company enters into franchise agreements with unrelated third parties to build and operate centers using the European Wax Center brand within
defined geographical areas. The Company believes that franchising is an effective and efficient means to expand the European Wax Center brand. The
franchisee is required to operate its centers in compliance with its franchise agreement that includes adherence to operating and quality control procedures
established by the Company.
The Company has not provided material loans, leases or guarantees to any franchisee or any of the franchisee’s employees or vendors. However, the
Company may, from time to time, without obligation, provide relief for franchisees under the franchise agreement or acquire the assets of franchisees at fair
value as determined under the franchise agreement if the franchise agreement terminates, subject to applicable law. The Company has minimal financial
exposure for the collection of the royalty payments as royalties are generally collected weekly in arrears for the prior week’s sales.
(d) Segment information
The Company operates and manages its business as one reportable and operating segment. The Company’s chief operating decision maker (“CODM”) is
the Chief Executive Officer. The CODM reviews financial information presented on a consolidated basis for purposes of allocating resources and
evaluating financial performance.
(e) COVID-19 pandemic
The Company is continuing to monitor the ongoing COVID-19 pandemic and its impact on its business. Beginning in March 2020, in response to the
COVID-19 pandemic, most franchisees temporarily closed their centers in order to promote the health and safety of its members, team members and their
communities. In April 2020, the entire franchise network was temporarily closed. Beginning in May 2020, certain governors announced steps to restart
non-essential business operations in their respective states and certain centers began to re-open. By June 2021, all of the Company’s nationwide network
had re-opened. However, there is a significant amount of uncertainty about the effects a resurgence in COVID-19 cases could have on our business, our
industry and overall economic activity.
(f) Revenue recognition
Revenue from Contracts with Customers
The Company transitioned to Financial Accounting Standards Board (“FASB”) Accounting Standards Codification (“ASC”) Topic 606, Revenue From
Contracts with Customers (“ASC 606”), from ASC Topic 605, Revenue Recognition and ASC Subtopic 952-605, Franchisors—Revenue Recognition
(together, the “Previous Standards”) on December 30, 2018 using the modified retrospective transition method. The Company’s consolidated financial
statements reflect the application of ASC 606 guidance beginning in fiscal year 2019. Upon adoption, the Company applied the new standard to all
contracts not completed as of the adoption date.
Revenue Recognition Significant Accounting Policies
The Company’s revenues are comprised of product sales, royalty fees, marketing fees, and other revenues which includes technology fees, franchise fees,
and service revenues from corporate-owned European Wax Center locations.
Product sales
Product sales primarily include the sale of wax, wholesale products consumed in the application of wax services and retail merchandise to
franchisees, as well as retail merchandise sold in corporate-owned centers. Revenue on product sales is recognized upon transfer of control.
Generally, customers take control when the risk of loss, title and insurable risks have transferred to the customer.
69
Royalty fees
Royalty fees are earned based on a percentage of the franchisees’ gross sales, net of retail product sales. The royalty fee is 6.0% of the
franchisees’ gross sales for such period and payment is remitted to the Company on a weekly basis. Franchise agreement royalties represent
sales-based royalties that are related entirely to our performance obligation under the applicable franchise agreement and are recognized in the
period the franchisees’ sales occur.
Marketing fees
Marketing fees are primarily earned based on a percentage of the franchisees’ gross sales, net of retail product sales. The marketing fee is 3.0%
of the franchisees’ gross sales for such period and payment is remitted to the Company on a monthly basis and recognized in the period the
franchisees’ sales occur. Additionally, the Company charges a fixed monthly fee to franchisees for search engine optimization and search engine
marketing services which is remitted on a monthly basis and recognized in the period when services are provided.
Other revenue
Other revenue primarily consists of service revenue and franchise fees, as well as technology fees, annual brand conference revenues, and
training.
Service revenue from the Company’s corporate owned centers is recognized at the time services are provided. Amounts collected in advance of
the period in which service is rendered are recorded as deferred service revenue on the Consolidated Balance Sheets.
Franchise fees consist of initial franchise fees due at contract inception. The Company’s primary performance obligations under the franchise
license are granting the use of the European Wax Center trademarks, system, training, preopening assistance, and center operating assistance in
exchange for franchise fees. The rights to use the Company’s intellectual property, and all other services the Company provides under the
franchise agreement are highly interrelated, not distinct within the contract, and therefore accounted for under ASC 606 as a single performance
obligation, which is satisfied by granting certain rights to use our intellectual property over the term of each franchise agreement.
Initial franchise fees are payable by the franchisee upon signing a new franchise agreement and are recognized as revenue on a straight-line basis
commencing at contract inception through the end of the initial franchise license term. Franchise agreements generally have terms of 10 years
beginning on the date the center is opened and the initial franchise fees are amortized over a period approximating the term of the agreement.
These agreements also convey one extension term up to 10 years, depending on contract terms if certain conditions are met. Amounts collected
in advance for franchise fees are recorded as deferred revenues on the Consolidated Balance Sheets.
Technology fees, annual brand conference revenues, and training are recognized as the related services are delivered and are not material to the
overall business.
(g) Cost of revenue
Cost of revenue primarily consists of the direct costs associated with wholesale product and retail merchandise sold to franchisees, retail merchandise sold
in corporate-owned centers, distribution and outbound freight costs, direct labor and materials for services provided in corporate-owned centers, and
inventory obsolescence charges.
(h) Commissions
The Company pays commissions to its area representatives on a weekly basis based on gross sales as royalty revenue is recognized. The commissions are
calculated as 2.25% of the gross sales earned from franchisees in their territory, net of retail product sales which are excluded from franchisees’ royalty
calculations, and are recognized in the period the franchisees’ sales occur. Area representatives also receive commission associated with the sales of new
franchise licenses, which are amortized to expense over the expected life of the related franchise agreement. Commissions expense is included in selling,
general and administrative expenses on the Consolidated Statements of Operations. The amount of commissions paid in fiscal year 2021 has substantially
declined from fiscal years 2020 and 2019 following our reacquisition of area representative rights in fiscal years 2021 and 2020.
(i) Selling, general and administrative
Selling, general and administrative expenses consist of costs associated with administrative and franchisee support functions related to our existing
business as well as growth and development activities. These costs primarily consist of wages, benefits and other compensation-related costs, occupancy,
third-party warehousing costs, information technology, legal, accounting and other professional fees. Selling, general and administrative expenses
excluding equity- based compensation are expensed when incurred, refer to (k) below for discussion of equity-based compensation.
70
(j) Advertising expenses
The Company expenses advertising costs as incurred. Advertising expenses include print, digital and social media advertising costs. The Company
expenses the costs related to its advertising in the period the related promotional event occurs.
(k) Equity-based Compensation
The Company recognizes compensation expense for equity awards to employees based on the estimated fair value of the equity instrument at the time of
grant. For time-based awards, such expense is recognized over the requisite service period of the equity award, which is normally the vesting period.
Compensation expense for performance-based awards with a market condition is recognized on a straight-line basis over the estimated service period of the
award, regardless of whether the market condition is satisfied. The Company accounts for forfeitures as they occur by reversing compensation cost for
unvested awards when the award is forfeited. See Note 16- Equity Based Compensation for further information.
(l) Income Taxes
The Company accounts for income taxes in accordance with ASC 740, “Accounting for Income Taxes” (“ASC 740”), which requires the recognition of tax
benefits or expenses on temporary differences between the financial reporting and tax bases of its assets and liabilities by applying the enacted tax rates in
effect for the year in which the differences are expected to reverse. Such net tax effects on temporary differences are reflected on the Company’s
Consolidated Balance Sheets as deferred tax assets and liabilities. Deferred tax assets are reduced by a valuation allowance when the Company believes
that it is more-likely-than-not that some portion or all of the deferred tax assets will not be realized.
ASC 740 prescribes a two-step approach for the recognition and measurement of tax benefits associated with the positions taken or expected to be taken in
a tax return that affect amounts reported in the financial statements. The Company has reviewed and will continue to review the conclusions reached
regarding uncertain tax positions, which may be subject to review and adjustment at a later date based on ongoing analyses of tax laws, regulations and
interpretations thereof. To the extent that the Company’s assessment of the conclusions reached regarding uncertain tax positions changes as a result of the
evaluation of new information, such change in estimate will be recorded in the period in which such determination is made. The Company reports income
tax-related interest and penalties relating to uncertain tax positions, if applicable, as a component of income tax expense.
(m) Tax Receivable Agreement
We entered into the TRA with the EWC Ventures' pre-IPO members that provides for the payment by the Company to the EWC Ventures pre-IPO members
of 85% of the benefits, if any, that the Company realizes, or is deemed to realize (calculated using certain assumptions), as a result of (i) increases in the our
allocable share of certain existing tax basis of the tangible and intangible assets of the Company and adjustments to the tax basis of the tangible and
intangible assets of the Company, in each case as a result of (a) the purchases of EWC Ventures Units (along with the corresponding shares of our Class B
common stock) from certain of the EWC Ventures Post-IPO Members using a portion of the net proceeds from the initial public and secondary offerings or
in any future offering or (b) Share Exchanges and Cash Exchanges by the EWC Ventures pre-IPO members (or their transferees or other assignees) in
connection with or after the initial public offering, (ii) our utilization of certain tax attributes of the Blocker Companies (including the Blocker Companies'
allocable share of certain existing tax basis of EWC Ventures' assets) and (iii) certain other tax benefits related to entering into the TRA, including tax
benefits attributable to payments under the TRA. We record liabilities for amounts payable under the TRA in the period in which the payment is deemed to
be probable. Further, payments under the TRA are only expected to be made in periods following the filing of a tax return in which we are able to utilize
tax benefits described above to reduce our cash taxes paid to a taxing authority.
(n) Noncontrolling Interests
The noncontrolling interests represent the economic interests of EWC Ventures held by members other than the Company. Income or loss is attributed to
the noncontrolling interests based on their contractual distribution rights, and the relative percentages of EWC Ventures Units held by the Company and the
other holders of EWC Ventures Units during the period
(o) Net Loss Per Share
Basic net loss per share is calculated by dividing the net loss attributable to Class A common stockholders by the number of weighted-average shares of
Class A common stock outstanding. Shares of our Class B common stock do not share in the earnings or losses of the Company and are therefore not
participating securities. As such, separate presentation of basic and diluted net loss per share of Class B common stock under the two-class method has not
been presented.
Diluted net loss per share adjusts the basic net loss per share calculation for the potential dilutive impact of common shares, such as equity awards, using
the treasury stock method. Diluted net loss per share considers the impact of potentially dilutive securities except in periods in which there is a loss because
the inclusion of the potential common shares would have an anti-dilutive effect. Shares of our Class B common stock are considered potentially dilutive
shares of Class A common stock as they are convertible into shares of Class A common stock when exchanged with a corresponding number of EWC
Ventures Units.
71
(p) Cash and cash equivalents
Cash and cash equivalents are comprised of cash on hand, demand deposits with financial institutions, and short-term highly liquid investments with
original maturities of 90 days or less. The Company maintains its cash in bank deposit accounts which, at times, may exceed federally insured limits. The
Company has not experienced any losses in such accounts.
(q) Accounts receivable
Accounts receivable are recorded at net realizable value, consisting of the carrying amount less an allowance for doubtful accounts, as needed. The
Company evaluates its accounts receivable on an ongoing basis and may establish an allowance for doubtful accounts based on a combination of historical
experience, aging analysis and information related to specific accounts. Account balances are written off against the allowance after all means of collection
have been exhausted and it is determined that further collection efforts will be unsuccessful. Recoveries of receivables previously written off are recorded
as income when received. Historically, the Company has not had a significant amount of write-offs.
(r) Inventory
Inventory is substantially comprised of wax, wholesale products consumed in the application of wax services and European Wax Center branded products
including in-grown hair serums, exfoliates, body washes, lotions, and creams. Inventory is recorded at the lower of cost or net realizable value using the
FIFO method. Net realizable value is the estimated selling prices in the ordinary course of business, less reasonably predictable costs of completion,
disposal, and transportation. The Company determines inventory reserves by regularly reviewing and evaluating individual inventory items and their
movement history. Inventory is reserved when deemed obsolete or unsellable. The cost of inventories also includes freight-in and U.S. Customs fees for the
purchase of inventory.
(s) Leases
The Company leases various corporate-owned centers and office space to support ongoing business operations. Most lease arrangements contain tenant
improvement allowances, rent holidays and/or rent escalation clauses. For purposes of recognizing incentives and minimum rent payments on a straight-
line basis over the terms of the leases, the Company uses the date it takes possession of the leased space. For leases with renewal periods at the Company’s
option, the Company determines the expected lease term based on whether the renewal of any options are reasonably assured at the inception of the lease.
In addition to rent expense, certain leases require the Company to pay a portion of real estate taxes, utilities, building operating expenses, insurance and
other charges in addition to rent.
For tenant improvement allowances, rent escalations, and rent holidays, the Company records a deferred rent liability in its Consolidated Balance Sheets
and amortizes the deferred rent in the Consolidated Statements of Operations over the terms of the leases, included within selling, general and
administrative expense, for corporate-owned centers and corporate office space.
(t) Property and equipment, net
Property and equipment is recorded at cost and depreciated using the straight-line method over the estimated remaining useful life of the related asset,
which ranges from one to ten years, as shown in the table below.
Estimated useful lives for Property and equipment are as follows:
Computer and other equipment 3-5 years
Computer software 4-7 years
Furniture and fixtures 3-7 years
Leasehold improvements
Lesser of the estimated
useful life or the remaining
lease term.
Additions to property and equipment include betterments and purchases. When long-lived assets are sold or otherwise disposed of, the asset account and
related accumulated depreciation are relieved, and any gain or loss is included in operating income. Repairs and maintenance expenses are charged to
operations when incurred.
The Company invests in software solutions from third party software vendors. Typically, these software solutions may require significant configuration
and/or may require customization to integrate into the Company’s infrastructure. The Company includes these software purchases and direct consultant
configuration fees within property and equipment, net on the Consolidated Balance Sheets. These purchases are segregated and not amortized until the
software solution or significant components are ready for their intended use. Capitalized software costs are amortized on a straight-line basis over the
asset’s estimated useful life. Expenses related to software solutions that do not qualify for capitalization are expensed as incurred. Recurring licensing or
maintenance fees are expensed as incurred.
72
(u) Impairment or disposal of long-lived assets
The Company reviews long-lived assets, including property and equipment and amortizable intangible assets, for impairment whenever events or changes
in circumstances indicate that the carrying amount of an asset may not be recoverable. If circumstances require a long-lived asset or asset group to be tested
for impairment, then assets are required to be grouped and evaluated at the lowest level for which there are identifiable cash flows that are largely
independent of the cash flows of other groups of assets. Recoverability of assets to be held and used is measured by a comparison of the carrying amount of
an asset or asset group to the undiscounted future net cash flows expected to be generated by the asset or asset group. If such assets are considered to be
impaired, the impairment to be recognized is measured by the amount by which the carrying amount of the assets exceeds the fair value of the assets.
Assets to be disposed of are reported at the lower of the carrying amount or fair value less costs to sell.
(v) Goodwill and indefinite-lived intangible assets
The Company’s indefinite-lived intangible assets consist of goodwill and trade names, which are not subject to amortization. The Company reviews the
recoverability of goodwill and its trade names on an annual basis (October 1st of the fiscal year) and whenever events or changes in circumstances indicate
that the carrying amounts may not be recoverable. Impairment indicators that may necessitate impairment testing between the Company’s annual
impairment tests include, but are not limited to, underperformance relative to historical or projected future operating results, significant changes in the
manner of use of the acquired assets or the overall business, and significant negative industry or economic trends.
Goodwill is recognized for the excess of the fair value of an acquired entity over the amounts assigned to identifiable assets acquired and liabilities
assumed in a business combination and is not subject to amortization. Goodwill is tested for impairment at a reporting unit level. For all periods presented,
the Company concluded that we have one reporting unit, which is also our sole operating segment. The Company first performs a qualitative assessment of
goodwill, a Step 0 analysis, to determine whether it is more likely than not that the fair value of a reporting unit is less than its carrying amount. When
necessary, a quantitative impairment test of goodwill is performed, comparing the fair value of the reporting unit to the carrying value. If the reporting
unit’s carrying value exceeds its fair value, an impairment loss equal to the difference between the carrying value of the reporting unit and its fair value is
recorded against goodwill. No impairment was recorded against goodwill for the fiscal years 2021, 2020 or 2019.
Indefinite-lived intangible assets, including the Company’s trade names, are tested for impairment at the unit of account. The Company first performs a
qualitative assessment to determine whether it is more likely than not that the fair value of the asset is less than its carrying amount. When necessary, a
quantitative impairment test is performed by making a determination of the fair value of the intangible asset. If the fair value of the intangible asset is less
than its carrying value, an impairment loss is recognized in an amount equal to the difference. If an indefinite-lived intangible is subsequently determined
to have a finite useful life, the asset is first tested for impairment as described above and then amortized prospectively over its estimated remaining useful
life in the same manner as other intangible assets that are subject to amortization. No impairment was recorded against the Company’s trade names for the
fiscal years 2021, 2020 or 2019.
It is possible that changes in circumstances or changes in management’s judgments, assumptions and estimates could result in an impairment charge of a
portion or all of its goodwill or other intangible assets.
(w) Fair value measurements
ASC 820, Fair Value Measurements and Disclosures, establishes a three-level valuation hierarchy for disclosure of fair value measurements. The valuation
hierarchy is based upon the transparency of inputs to the valuation of an asset or liability as of the measurement date. Categorization within the valuation
hierarchy is based upon the lowest level of input that is significant to the fair value measurement. The three levels are defined as follows:
• (Level 1) Quoted prices in active markets for identical assets or liabilities.
• (Level 2) Observable inputs other than quoted prices included in Level 1, such as quoted prices for similar assets and liabilities in active markets,
similar assets and liabilities in markets that are not active or can be corroborated by observable market data.
• (Level 3) Unobservable inputs that are supported by little or no market activity and that are significant to the fair value of the assets or liabilities.
This includes valuation techniques that involve significant unobservable inputs.
Valuation techniques used need to maximize the use of observable inputs and minimize the use of unobservable inputs.
(x) Financial instruments
The carrying values of cash and cash equivalents, accounts receivable and accounts payable approximate fair value because of the short-term nature of
these instruments. Debt under the 2026 Term Loan of $180,000 approximates the fair value due to the variable rate and incorporates a measure of our credit
risk.
73
(y) Derivative instruments and hedging activities
The Company uses interest rate caps to manage its exposure to variable interest rates. The Company’s policy is to not use any financial instruments for
trading or other speculative purposes.
Derivatives are recorded at fair value. If a derivative is designated as a cash flow hedge, the changes in fair value are recognized as a component of
accumulated other comprehensive income/loss until the underlying hedge item is recognized in earnings. Fair values of derivative contracts are classified as
current or long-term, depending on the maturity date of the derivative contract, and are presented in Other current liabilities and Other long-term liabilities,
as applicable, on the Consolidated Balance Sheets. The cash flows from derivatives treated as hedges are classified on the Consolidated Statements of Cash
Flows in the same category as the item being hedged.
The Company has elected to use the income approach to value the derivatives, using observable Level 2 market expectations at measurement dates and
standard valuation techniques to convert future amounts to a single present discounted amount reflecting current market expectations about those future
amounts. Level 2 inputs for derivative valuations are limited to inputs other than those quoted prices that are observable for the asset or liability
(specifically LIBOR swap rates and credit risk at commonly quoted intervals). Mid-market pricing is used as a practical expedient. Derivatives are
discounted to present value at the measurement date at overnight index swap rates.
(z) Deferred financing costs
Deferred financing costs represent the cost of obtaining financing arrangements and are amortized over the term of the related debt agreement using the
straight-line method for revolving debt arrangements and the effective interest method for term debt arrangements. Deferred financing costs related to
revolving debt arrangements are recorded as a component of other non-current assets on the Consolidated Balance Sheets. Deferred financing costs related
to term debt arrangement are reflected as a direct reduction of the related debt liability on the Consolidated Balance Sheets. Amortization of deferred
financing costs are included in interest expense on the Consolidated Statements of Operations.
(aa) Accumulated other comprehensive loss
Accumulated other comprehensive loss is defined as the change in equity of a business enterprise during a period from transactions and other events and
circumstances from non-owner sources. Accumulated other comprehensive loss is entirely comprised of the cumulative change in the fair value of our cash
flow hedge. There were no reclassifications of other comprehensive income or loss to earnings during fiscal years 2021, 2020 and 2019.
(bb) Class A Founders’ Units and Class D Units subject to possible redemption
Prior to the Reorganization Transactions described in Note 1, the Company previously classified the Class A Founders’ Units and Class D Units as
temporary equity in the mezzanine section of the Consolidated Balance Sheets due to the contingently redeemable nature of the Class A Founders’ Units
and Class D Units. The Company believed that the related contingent events and the redemption of the Class A Founders’ Units is probable, and therefore
the Class A Founders’ Units were measured at fair value. The Company’s accounting policy was to record the shares at the current redemption value (i.e.
fair value) versus accreting over time to the redemption value. The Class A Founders’ Units and Class D Units are no longer outstanding as they were
converted to EWC Ventures Units concurrent with the Reorganization Transactions.
(cc)Malware incident
In December 2019, a malware incident occurred where certain wax center professionals were not able to access their workstations nor the point of sale
system. The Company engaged a third-party specialist to contain the incident and to conduct an investigation and concluded that there was no breach or
compromise of assets including client data and there was no impact to the internal control over financial reporting or financial data. As remediation to the
franchisees, the Company provided relief to help offset the impact of the outage in the form of royalty relief for half of December 2019 and waiver of the
monthly technology and marketing fees. The incident resulted in a $1,767 reduction of Royalty fee revenue, $112 reduction of Other revenues, and an
expense of $1,282 related to remediation efforts included in selling, general and administrative expense on the Consolidated Statements of Operations for
the year ended December 28, 2019.
(dd) Implications of being an Emerging Growth Company
The Company is an emerging growth company as defined in the Jumpstart Our Business Startups Act of 2012 (“JOBS Act”) and may take advantage of
reduced reporting requirements that are otherwise applicable to public companies. Section 107 of the JOBS Act exempts emerging growth companies from
being required to comply with new or revised financial accounting standards until private companies are required to comply with those standards. The
Company has elected to use the extended transition period for complying with new or revised accounting standards. We also intend to take advantage of
some of the reduced regulatory and reporting requirements of emerging growth companies pursuant to the JOBS Act so long as we qualify as an emerging
growth company, including, but not limited to, not being required to comply with the auditor attestation requirements of Section 404(b) of the
74
Sarbanes-Oxley Act, reduced disclosure obligations regarding executive compensation, and exemptions from the requirements of holding non-binding
advisory votes on executive compensation and golden parachute payments.
(ee) Recently adopted accounting pronouncements
In August 2018, the FASB issued ASU 2018-15, Intangibles—Goodwill and Other—Internal-Use Software (Subtopic 350-40): Customer’s Accounting for
Implementation Costs Incurred in a Cloud Computing Arrangement That Is a Service Contract. Under this standard, companies will apply the same criteria
for capitalizing implementation costs as they would for an arrangement that has a software license. The adoption of this new guidance prescribes the
balance sheet, statement of operations, and cash flow classification of the capitalized implementation costs and related amortization expense, and additional
quantitative and qualitative disclosures. This standard is effective for fiscal years beginning after December 15, 2021. This standard may be applied either
prospectively to eligible costs incurred on or after the date of the new guidance or retrospectively. The Company adopted this standard on December 27,
2020 (the beginning of its fiscal year 2021) on a prospective basis. The adoption of this standard did not have a significant impact on our financial
statements.
(ff) Recently issued accounting pronouncements not yet adopted
In February 2016, the FASB issued ASU 2016-02, Leases and established ASC Topic 842, Leases (“ASC 842”), which supersedes ASC Topic 840, Leases.
ASC 842 requires a lessee to recognize a lease right-of-use (“ROU”) asset and a corresponding lease liability on its balance sheet along with additional
qualitative and quantitative disclosures. ROU assets and lease liabilities are recognized at the commencement date based on the present value of future
payments. ASC 842 is effective for fiscal years beginning after December 15, 2021, and interim periods within fiscal years beginning after December 15,
2022, with early adoption permitted.
The Company adopted this guidance on December 26, 2021, which is the beginning of fiscal year 2022, by applying the provisions of this guidance on a
modified retrospective basis as of the effective date. As such, comparative periods will not be restated and the disclosures required under the new standard
will not be provided for periods prior to December 26, 2021. We elected the package of practical expedients whereby we are not be required to: i) reassess
whether any expired or existing contracts are or contain leases, ii) reassess the lease classification of existing leases and iii) reassess initial direct costs for
any existing leases. We did not elect to utilize the hindsight practical expedient. Upon adoption of the new standard we elected to account for non-lease
components related to real estate leases as a part of the related lease components for all of our leases. We also elected to not recognize leases with an initial
term of 12 months or less on our balance sheet. We have assessed and updated our business processes, systems and controls to ensure compliance with the
accounting and disclosure requirements of the new standard.
The Company’s leases are primarily accounted for as operating leases under existing guidance. The adoption of this new guidance will result in an impact
to our balance sheet in the range of approximately $7,000 to $8,000 related to the establishment of operating lease liabilities and the corresponding
operating lease right-of-use assets. The adoption of this guidance will not have a significant impact on our Consolidated Statements of Operations or on our
Consolidated Statements of Cash Flows as our leases will retain their classifications as determined under current guidance.
In June 2017, the FASB issued ASU 2016-13, Financial Instruments (Topic 326)—Measurement of Credit Losses on Financial Instruments, which requires
the measurement and recognition of expected credit losses for financial assets held at amortized cost. The standard replaces the existing incurred loss
impairment model with an expected loss methodology, which will result in more timely recognition of credit losses. ASU 2016-13, and related
amendments, are effective for fiscal years beginning after December 15, 2022. The Company has not completed its assessment of the standard but does not
expect the adoption to have a material impact on its financial statements.
In March 2020, the FASB issued ASU 2020-04, Reference Rate Reform: Facilitation of the Effects of Reference Rate Reform on Financial Reporting. The
amendments in this update, as well as subsequently issued amendments, provide temporary, optional guidance to ease the burden in accounting for
reference rate reform. The amendments provide optional expedients and exceptions for applying GAAP to transactions affected by reference rate reform if
certain criteria are met. The amendments primarily include relief related to contract modifications and hedging relationships. The relief provided by this
ASU does not apply to contract modifications made and hedging relationships entered into or evaluated after December 31, 2022. However, hedging
relationships that apply certain optional expedients prior to December 31, 2022, will be retained through the end of the hedging relationship, including for
periods after December 31, 2022. We will evaluate the impact of this guidance as contracts are modified through December 2022.
3. Sales of corporate-owned centers
In May 2019, the Company sold seven corporate-owned centers for an aggregate purchase price of $1,838. The assets sold had a negative carrying value, as
the carrying value of the centers’ liabilities exceeded the carrying value of the assets. The difference between the consideration received and the carrying
value of the net assets sold was $2,120, which was recognized as a gain in the Consolidated Statements of Operations. The Company had no sales of
corporate-owned centers during the years ended December 25, 2021 and December 26, 2020.
75
4. Fair value measurements
Fair value is the price that would be received to sell an asset or paid to transfer a liability in an orderly transaction between market participants at the
measurement date.
We use valuation techniques that are consistent with the market approach, the income approach and/or the cost approach. The market approach uses prices
and other relevant information generated by market transactions involving identical or comparable assets and liabilities. The income approach uses
valuation techniques to convert future amounts, such as cash flows or earnings, to their present value on a discounted basis. The cost approach is based on
the amount that currently would be required to replace the service capacity of an asset (replacement costs). Valuation techniques should be consistently
applied. Inputs to valuation techniques refer to the assumptions that market participants would use in pricing the asset or liability. Inputs may be
observable, meaning those that reflect the assumptions market participants would use in pricing the asset or liability developed based on market data
obtained from independent sources, or unobservable, meaning those that reflect the reporting entity’s own assumptions about the assumptions market
participants would use in pricing the asset or liability developed based on the best information available in the circumstances. These two types of inputs
create a three-tier fair value hierarchy that gives the highest priority to quoted prices in active markets for identical assets or liabilities and the lowest
priority to unobservable inputs. Refer to Fair Value discussion within the Significant Accounting Policies section of Note 2 for the three levels of the
valuation hierarchy.
The Company uses interest rate caps to manage its interest rate exposure. These interest rate caps are recorded at fair value. Changes in fair value of our
interest rate caps are recognized as a component of accumulated other comprehensive loss on the Consolidated Balance Sheets. The Company has elected
to use the income approach to value the interest rate cap, using observable Level 2 market expectations at measurement dates and standard valuation
techniques to convert future amounts to a single present discounted amount reflecting current market expectations about those future amounts. Level 2
inputs for derivative valuations are limited to inputs other than those quoted prices that are observable for the asset or liability (specifically LIBOR swap
rates and credit risk at commonly quoted intervals). Mid-market pricing is used as a practical expedient. Derivatives are discounted to present value at the
measurement date at overnight index swap rates. Refer to Note 11—Derivative instruments and hedging activity for additional discussion.
Fair value measurements are summarized below:
Fair
Market
Value
Quoted prices
in active
markets for
identical assets
(Level 1)
Significant
observable
inputs
(Level 2)
Significant
unobservable
inputs
(Level 3)
Interest rate cap
December 25, 2021 $ (242 ) $ — $ (242 ) $ —
December 26, 2020 $ (527 ) $ — $ (527 ) $ —
5. Prepaid expenses and other current assets
Prepaid expenses and other current assets consisted of the following:
December 25, 2021
December 26, 2020
Prepaid inventory $ — $ 2,000
Prepaid insurance 2,308 324
Prepaid other & other current assets
3,619
2,250
Total
$ 5,927
$ 4,574
The prepaid other & other current assets amounts are primarily composed of prepaid technology, marketing and maintenance contracts, sales taxes and rent.
6. Inventory
Inventory is comprised of finished goods. The allowance for obsolete inventory included in inventory on the Consolidated Balance Sheets was $5,055 and
$6,599 as of December 25, 2021 and December 26, 2020, respectively.
A summary of changes in the inventory obsolescence reserve for fiscal years 2021 and 2020 is as follows:
December 25, 2021
December 26, 2020
Balance, beginning of year $ 6,599 $ 1,229
Charged to costs and expenses 317 6,656
Write-offs of reserved inventory
(1,861 )
(1,286 )
Balance, end of year
$ 5,055
$ 6,599
76
The increase in the inventory obsolescence reserve during the year ended December 26, 2020 related to a pilot program for certain retail products with a
limited shelf-life that did not have a chance to scale, due to COVID-19, as well as a planned product restaging effort approved by management during the
year ended December 26, 2020.
7. Property and equipment, net
Property and equipment consisted of the following:
December 25, 2021
December 26, 2020
Computer and other equipment $ 583 $ 487
Computer software 7,458 8,700
Furniture and fixtures 1,162 974
Leasehold improvements 2,433 2,433
Construction in process 269 —
Software implementation in process
—
90
Property and equipment 11,905 12,684
Less: accumulated depreciation
(8,042 )
(7,645 )
Property and equipment, net
$ 3,863
$ 5,039
Depreciation and amortization expense related to property and equipment was $1,489, $1,649 and $2,198 for the years ended December 25, 2021,
December 26, 2020 and December 28, 2019, respectively. In fiscal year 2019, the Company recognized an impairment charge of $18,183 related to the
Company’s abandonment of an internally developed point- of-sale software system.
8. Goodwill and intangible assets, net
A summary of goodwill and intangible assets as of December 25, 2021 and December 26, 2020 is as follows:
December 25, 2021
Weighted Average
Remaining Useful
Life (Years)
Gross
Carrying
Value
Accumulated
Amortization
Net
Carrying
Value
Franchisee relationships 6.75 $ 114,594 $ (37,294 ) $ 77,300
Reacquired rights 8.31 76,545 (15,673 ) 60,872
Favorable lease assets
0.19
170
(161 )
9
191,309 (53,128 ) 138,181
Indefinite-lived intangible:
Trade name
N/A
63,814
—
63,814
Total intangible assets
$ 255,123
$ (53,128 )
$ 201,995
Goodwill $ 328,551 $ — $ 328,551
December 26, 2020
Weighted Average
Remaining Useful
Life (Years)
Gross
Carrying
Value
Accumulated
Amortization
Net
Carrying
Value
Franchisee relationships 7.74 $ 114,594 $ (25,870 ) $ 88,724
Reacquired rights 9.19 68,973 (8,304 ) 60,669
Favorable lease assets
1.24
170
(110 )
60
183,737 (34,284 ) 149,453
Indefinite-lived intangible:
Trade name
N/A
63,814
—
63,814
Total intangible assets
$ 247,551
$ (34,284 )
$ 213,267
Goodwill $ 328,551 $ — $ 328,551
Area representative rights represent an agreement with area representatives to sell franchise licenses and provide support to franchisees in a geographic
region. From time to time, the Company enters into agreements to reacquire certain area representative rights. These reacquisition costs totaled $7,644,
$32,791 and $36,182 for the years ended December 25, 2021, December 26, 2020 and December 28, 2019, respectively.
77
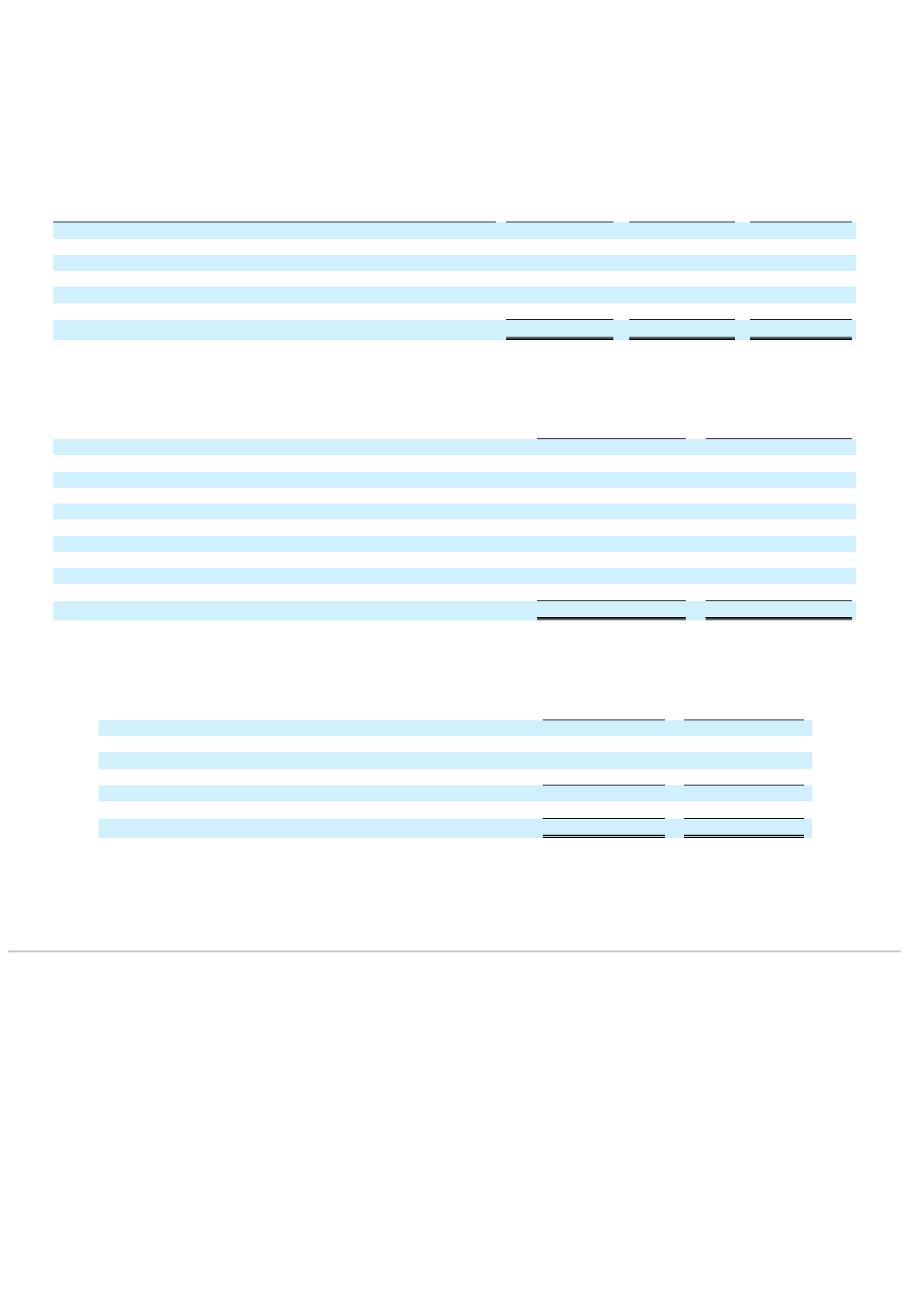
The initial term of the area representative agreements is ten years with an additional ten-year renewal at the option of the area representative. The
reacquired rights are amortized on a straight-line basis over the remaining expected term of the agreement prior to the reacquisition. Amortization expense
for reacquired rights was $7,368, $6,457 and $1,847 for the years ended December 25, 2021, December 26, 2020 and December 28, 2019, respectively.
Franchisee relationships are amortized on a straight-line basis over the estimated useful life of the asset. Amortization expense for franchisee relationships
was $11,424 for the year ended December 31, 2021 and $11,428 for each of the years ended December 26, 2020 and December 28, 2019, respectively.
Amortization expense for franchisee relationship, reacquired rights and favorable lease assets are included in depreciation and amortization expense on the
Consolidated Statements of Operations.
Future expected amortization expense of the Company’s intangible assets as of December 25, 2021 is as follows:
Fiscal Years Ending
Franchisee
Relationships
Reacquired
Rights
Favorable
Lease Assets
2022 $ 11,595 $ 7,362 $ 9
2023 11,595 7,362 —
2024 11,595 7,362 —
2025 11,595 7,362 —
2026 11,595 7,362 —
Thereafter
19,325
24,062
—
Total
$ 77,300
$ 60,872
$ 9
9. Accounts payable and accrued liabilities
Accounts payable and accrued liabilities consisted of the following:
December 25,
2021
December 26,
2020
Accounts payable $ 7,684 $ 615
Accrued inventory 2,665 3,321
Accrued compensation 5,401 2,169
Accrued taxes and penalties 1,432 1,732
Accrued lease termination costs 588 360
Accrued technology and subscription fees 196 1,536
Accrued interest 1,477 1,440
Accrued professional fees 2,090 967
Accrued marketing 489 688
Other accrued liabilities
1,133
661
Total Accounts payable and accrued liabilities
$ 23,155
$ 13,489
10. Long-term debt
Long-term debt consists of the following:
December 25,
2021
December 26,
2020
2026 Term Loan $ 180,000 $ —
Previous Term Loan — 240,552
Previous Revolving Credit Facility — 30,000
Less: current portion
(5,625 )
(2,428 )
Total long-term debt 174,375 268,124
Less: unamortized debt discount and deferred financing costs
(1,768 )
(5,149 )
Total long-term debt, net
$ 172,607
$ 262,975
On August 9, 2021, EW Intermediate Holdco, LLC, a Delaware limited liability company (“Holdings”), EW Holdco, LLC, a Delaware limited liability
company (the “Borrower”), as borrower (each indirect subsidiaries of the Company), entered into the 2026 Credit Agreement with the lenders party thereto,
Bank of America, N.A., as administrative agent (the “Administrative Agent”), and the other parties party thereto. The 2026 Credit Agreement is comprised
of the 2026 revolving credit facility and the 2026 term loan. The 2026 Credit Agreement will mature on August 9, 2026.
78
The proceeds from the new term loan were used together with proceeds from our initial public offering to fully repay and terminate the previous secured
term loan (the “Previous Term Loan”) and the previous secured revolving credit facility (the “Previous Revolving Credit Facility”). In connection with the
repayment and termination of the Previous Term Loan and Previous Revolving Credit Facility we incurred a loss on debt extinguishment of $6,313, which
was recorded as a component of interest expense in the accompanying Consolidated Statements of Operations. Of this loss, $2,446 was attributable to the
payment of the prepayment premium and related fees on the Previous Term Loan and $3,867 was due to the write-off of unamortized deferred financing
costs. We incurred $1,924 in various lender and third party fees in conjunction with this transaction. Of these fees, $1,574, along with $344 of unamortized
deferred issuance costs, related to the 2026 Term Loan and have been recorded as a reduction of long-term debt on the accompanying Consolidated Balance
Sheets. The remaining $350 of costs, along with $77 of unamortized deferred issuance costs, related to the 2026 revolving credit facility and have been
recorded as other non-current assets on the accompanying Consolidated Balance Sheets.
Obligations under the 2026 Credit Agreement are guaranteed by Holdings and the direct and indirect wholly-owned material domestic subsidiaries of the
Borrower, subject to certain exceptions. The obligations are secured by a pledge of the Borrower’s capital stock directly held by Holdings and a security
interest in substantially all of the assets of Holdings, the Borrower and its subsidiaries, subject to certain exceptions.
Borrowings under the 2026 Credit Agreement will bear interest at a rate equal to, at the Borrower’s option, either (a) a LIBOR rate determined by reference
to the cost of funds for Eurodollar deposits for the interest period relevant to such borrowing, adjusted for certain additional costs or (b) a base rate
determined by reference to the highest of (i) the federal funds rate plus 0.50%, (ii) the prime rate of Bank of America, N.A. and (iii) the one month adjusted
LIBOR plus 1.00%, in each case plus an applicable margin. In addition, the Credit Agreement requires the Borrower to pay a commitment fee in respect of
unused revolving credit facility commitments ranging between 0.30% and 0.45% per annum (determined based on the Borrower’s total net leverage ratio)
in respect of the unused commitments under the Credit Agreement.
Borrowings under the 2026 Term Loan bear interest at an index rate as defined above plus an applicable margin of 3.0% (The all-in rate was 3.1% at
December 25, 2021). The 2026 Term Loan requires principal payments payable in quarterly installments with the final scheduled principal payment on the
outstanding 2026 Term Loan borrowings due on August 9, 2026. The 2026 revolving credit facility has a maximum borrowing capacity of $40,000 and as
of December 25, 2021 there were no outstanding borrowings.
The 2026 Credit Agreement contains certain customary events of default, including in the event of a change of control, and certain covenants and
restrictions that limit the Borrower’s and its subsidiaries’ ability to, among other things, incur additional debt; create liens on certain assets; pay dividends
on or make distributions in respect of their capital stock or make other restricted payments; consolidate, merge, sell, or otherwise dispose of all or
substantially all of their assets; and enter into certain transactions with their affiliates.
The Company is also subject to certain financial maintenance covenants under the 2026 Credit Agreement, which require the Company and its subsidiaries
to (i) not exceed certain specified total net leverage ratios and (ii) not fall below a certain fixed charge coverage ratio, in each case, at the end of each fiscal
quarter.
If the Company fails to perform its obligations under these and other covenants, or should any event of default occur, the term loan and revolving credit
facility commitments under the 2026 Credit Agreement may be terminated and any outstanding borrowings, together with accrued interest, under the 2026
Credit Agreement could be declared immediately due and payable.
Annual future principal payments due on long-term debt as of December 25, 2021 are as follows:
Fiscal Years Ending
2022 $ 5,625
2023 6,750
2024 13,500
2025 13,500
2026
140,625
Total long-term debt principal
$ 180,000
11. Derivative instruments and hedging activities
In December 2018, the Company entered into an interest rate cap derivative instrument which was designated as a cash flow hedge. The Company’s
objective is to mitigate the impact of interest expense fluctuations on the Company’s profitability resulting from interest rate changes by capping the
LIBOR component of the interest rate at 4.5% on $175,000 of principal outstanding under its long-term debt arrangement, as the interest rate cap provides
for payments from the counterparty when LIBOR rises above 4.5%. The interest rate cap has a $175,000 notional amount and is effective December 31,
2018, for the monthly periods from and including January 31, 2019 through September 25, 2024. The interest rate cap has a deferred premium; accordingly,
the Company will pay a
79
monthly premium for the interest rate cap over the term of the agreement. The annual premium is equal to 0.11486% on the notional amount.
Changes in the cash flows of interest rate cap derivatives designated as hedges are expected to be highly effective in offsetting the changes in interest
payments on a principal balance equal to the designated derivative’s notional amount, attributable to the hedged risk. Changes in the fair value of the
interest rate cap are recognized in other comprehensive income and are reclassified out of accumulated other comprehensive income and into interest
expense when the hedged interest obligations affect earnings. Cash flows related to derivatives qualifying as hedges are included in the same section of the
Consolidated Statements of Cash Flows as the underlying assets and liabilities being hedged. Refer to Note 4—Fair value measurements for information on
the fair value of the Company’s interest rate cap derivative instrument.
Our cash flow hedge position related to the interest rate cap derivative instrument is as follows:
Balance Sheet
Classification December 25, 2021
December 26, 2020
Derivatives designated as hedging instruments:
Interest rate cap, current portion Other current liabilities $ (182 ) $ (181 )
Interest rate cap, non-current portion
Other long-term liabilities
(60 )
(346 )
Total derivative liabilities designated as hedging
instruments
$ (242 )
$ (527 )
The table below presents the net unrealized gain (loss) recognized in other comprehensive income (loss) (“OCI”) resulting from fair value adjustments of
hedging instruments:
Net Unrealized Gain (Loss)
Recognized in OCI
Year Ended
December 25, 2021
Year Ended
December 26, 2020
Year Ended
December 28, 2019
Derivatives designated as hedging instruments:
Interest rate cap
$ 286
$ 208
$ (405 )
Total
$ 286
$ 208
$ (405 )
12. Commitments and contingencies
Leases
The Company leases various retail locations and office space under non-cancellable lease agreements with terms expiring through 2032. The Company is
required, under the terms of certain of its lease agreements, to pay for common area maintenance. Common area maintenance rates are adjusted annually by
the landlords and calculated based on the monthly square footage occupied by the Company. Rent expense, including common area maintenance and
property taxes, was $2,429, $3,064 and $2,774 for the years ended December 25, 2021, December 26, 2020 and December 28, 2019, respectively, and is
included in selling, general and administrative expense on the Consolidated Statements of Operations.
Aggregate future minimum annual rental payments required under the lease agreements as of December 25, 2021, are as follows and do not include taxes
and common area maintenance:
Fiscal Years Ending
2022 $ 2,098
2023 1,524
2024 1,346
2025 1,232
2026 880
Thereafter
1,152
Total
$ 8,232
Exit or Disposal Activities
During fiscal year 2019, the Company relocated its corporate headquarters from Hallandale Beach, Florida to Plano, Texas. As a result of this relocation,
the Company vacated a portion of its leased properties in Hallandale Beach and recognized an exit obligation charge and related exit obligation liability on
the cease-use date, in accordance with ASC 420, Exit or Disposal Cost Obligations. In fiscal year 2020, the Company vacated the remaining portion of the
leased property in Hallandale Beach and recognized an exit obligation charge and related liability on the cease-use date for the remaining portion of the
property.
80
A summary of the exit liability and related activity for the periods presented is as follows:
Exit Cost
Obligation – Leases
Exit cost obligation at cease-use date in fiscal 2019
$ 778
Exit cost obligation at December 28, 2019
778
Additional exit cost obligation at cease-use date in fiscal 2020 159
Accretion during fiscal year 2020 11
Payments during fiscal year 2020
(333 )
Exit cost obligation at December 26, 2020
615
Reduction to exit cost obligation (172 )
Accretion during fiscal year 2021 6
Payments during fiscal year 2021
(331 )
Exit cost obligation at December 25, 2021
$ 118
The charges, recorded as selling, general and administrative expenses on the Consolidated Statements of Operations, primarily included the present value
of the remaining lease obligation on the cease use dates, net of estimated sublease income.
The current and non-current components of the exit liabilities related to the leased property were included within accounts payable and accrued liabilities
and other long-term liabilities on the Consolidated Balance Sheets, respectively, as follows:
December 25,
2021
December 26,
2020
Accounts payable and accrued liabilities $ 118 $ 360
Other long-term liabilities
—
255
Total exit cost obligation
$ 118
$ 615
Purchase Commitments
As of December 25, 2021, the Company had purchase commitments of approximately $13,992, primarily related to inventory and advertising, of which the
Company expects to pay $11,336 during fiscal year 2022.
Litigation
The Company is exposed to various asserted and unasserted potential claims encountered in the normal course of business. Although the outcomes of
potential legal proceedings are inherently difficult to predict, the Company does not expect the resolution of these occasional legal proceedings to have a
material effect on its financial position, results of operations, or cash flow.
13. Stockholder’s equity
Under the Company’s amended and restated certificate of incorporation the Company is authorized to issue up to 600,000,000 shares of Class A common
stock, par value $0.00001 per share (“Class A common stock”), 60,000,000 shares of Class B common stock, par value $0.00001 per share (“Class B
common stock”) and 100,000,000 shares of preferred stock, par value $0.00001 per share. The Class A common stock and Class B common stock each
provide holders with one vote on all matters submitted to a vote of stockholders. The holders of Class B common stock do not have any of the economic
rights provided to holders of Class A common stock.
Subject to certain restrictions EWC Ventures Post-IPO Members have the right to exchange their EWC Ventures Units, together with a corresponding
number of shares of our Class B common stock for, at our option, (i) shares of the Company's Class A common stock on a one-for-one basis (the “Share
Exchange”) or (ii) cash (based on the market price of the Company's Class A common stock) (the “Cash Exchange”).
14. Noncontrolling interest
In connection with the Reorganization Transactions, we became the sole managing member of EWC Ventures and, as a result of this control, and because
we have a substantial financial interest in EWC Ventures, we consolidate the financial results of EWC Ventures. We report noncontrolling interests
representing the economic interests in EWC Ventures held by the EWC Ventures Post-IPO Members. Income or loss is attributed to the noncontrolling
interests based on their contractual distribution rights, and the relative percentages of EWC Ventures Units by us and the other holders of EWC Ventures
Units during the period.
The EWC Ventures LLC Agreement permits the members of EWC Ventures to exchange EWC Ventures Units, together with related shares of our Class B
common stock, for shares of our Class A common stock on a one-for-one basis or, at the election of the Company, for cash at the current fair value on the
date of the exchange. Changes in the Company’s ownership interest in EWC Ventures while retaining control of EWC Ventures will be accounted for as
equity transactions. As such, future redemptions or direct
81
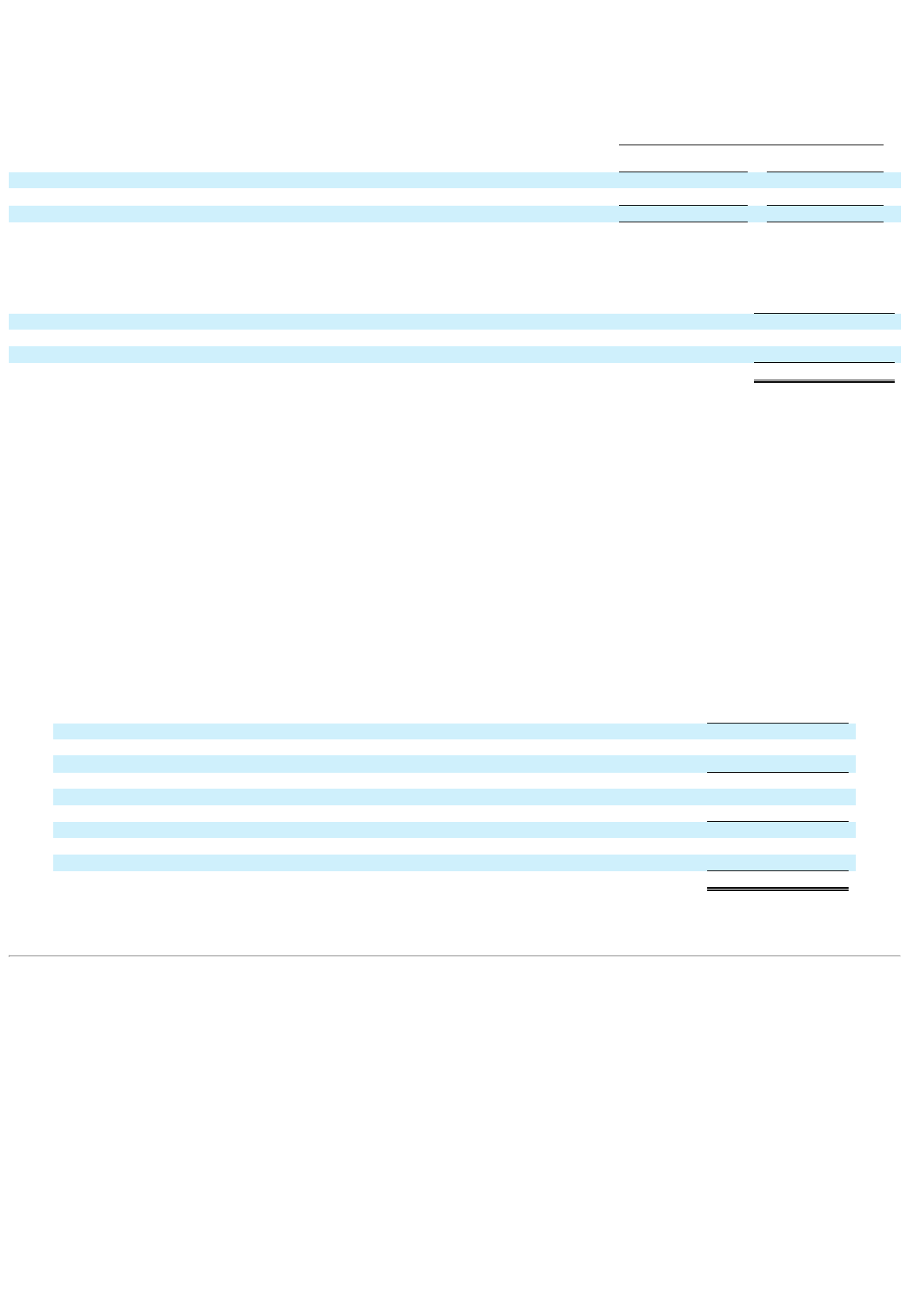
exchanges of EWC Ventures Units by the other members will result in a change in ownership and reduce the amount recorded as noncontrolling interest
and increase additional paid-in capital. Additionally, certain members of EWC Ventures hold unvested EWC Ventures Units that are subject to service,
performance, and/or market conditions (See Note 16—Equity Based Compensation). The vesting of EWC Ventures units will result in a change in
ownership and increase the amount recorded as noncontrolling interest and decrease additional paid-in capital.
The following table summarizes the ownership of EWC Ventures as of December 25, 2021:
December 25, 2021
Units Owned
Ownership
Percentage
European Wax Center, Inc. 36,932,423 59.6 %
Noncontrolling Interest
25,036,706
40.4 %
Total
61,969,129
100.0 %
The following table presents the effect of changes in the Company’s ownership interest in EWC Ventures on the Company’s equity for the periods
indicated:
Period of August 4-
December 25, 2021
Net loss attributable to European Wax Center, Inc. $ (3,415 )
Transfers from (to) noncontrolling interests:
Increase in additional-paid-in-capital as a result in ownership changes in EWC Ventures
34,208
Net increase in equity of European Wax Center, Inc. due to equity interest transactions with noncontrolling interests
$ 30,793
15. Revenue from contracts with customers
Costs to obtain a contract
Costs to obtain a contract include commissions paid to area representatives associated with the sale of franchises within the area representative’s respective
region. As of December 25, 2021 and December 26, 2020, $425 and $453 of commissions paid in connection with the sale of franchise licenses are
capitalized within prepaid expenses and other current assets (short-term portion) and $2,221 and $2,630 are capitalized within other non-current assets
(long-term portion), respectively. The commissions are amortized to expense over the expected life of the related franchise agreement. $437, $429 and
$395 of commissions was amortized to selling, general and administrative expenses during the years ended December 25, 2021, December 26, 2020 and
December 28, 2019, respectively.
Contract liabilities
Contract liabilities consist of deferred revenue resulting from franchise fees, which are generally recognized on a straight-line basis over the term of the
underlying franchise agreement. Also included are service revenues from corporate-owned centers, including customer prepayments in connection with the
Wax Pass program. Contract liabilities are classified as deferred revenue on the Consolidated Balance Sheets.
Deferred franchise fees are reduced as fees are recognized in revenue over the term of the franchise license for the respective center. Deferred service
revenues are recognized over time as the services are performed.
The following table reflects the change in contract liabilities for the periods indicated:
Contract liabilities
Balance at December 29, 2018 $ 8,179
Revenue recognized that was included in the contract liability at the beginning of the year (3,408 )
Increase, excluding amounts recognized as revenue during the period
4,486
Balance at December 28, 2019 9,257
Revenue recognized that was included in the contract liability at the beginning of the year (2,461 )
Increase, excluding amounts recognized as revenue during the period
2,083
Balance at December 26, 2020 8,879
Revenue recognized that was included in the contract liability at the beginning of the year (2,599 )
Increase, excluding amounts recognized as revenue during the period
3,511
Balance at December 25, 2021
$ 9,791
The weighted average remaining amortization period for deferred revenue is 3.9 years.
82
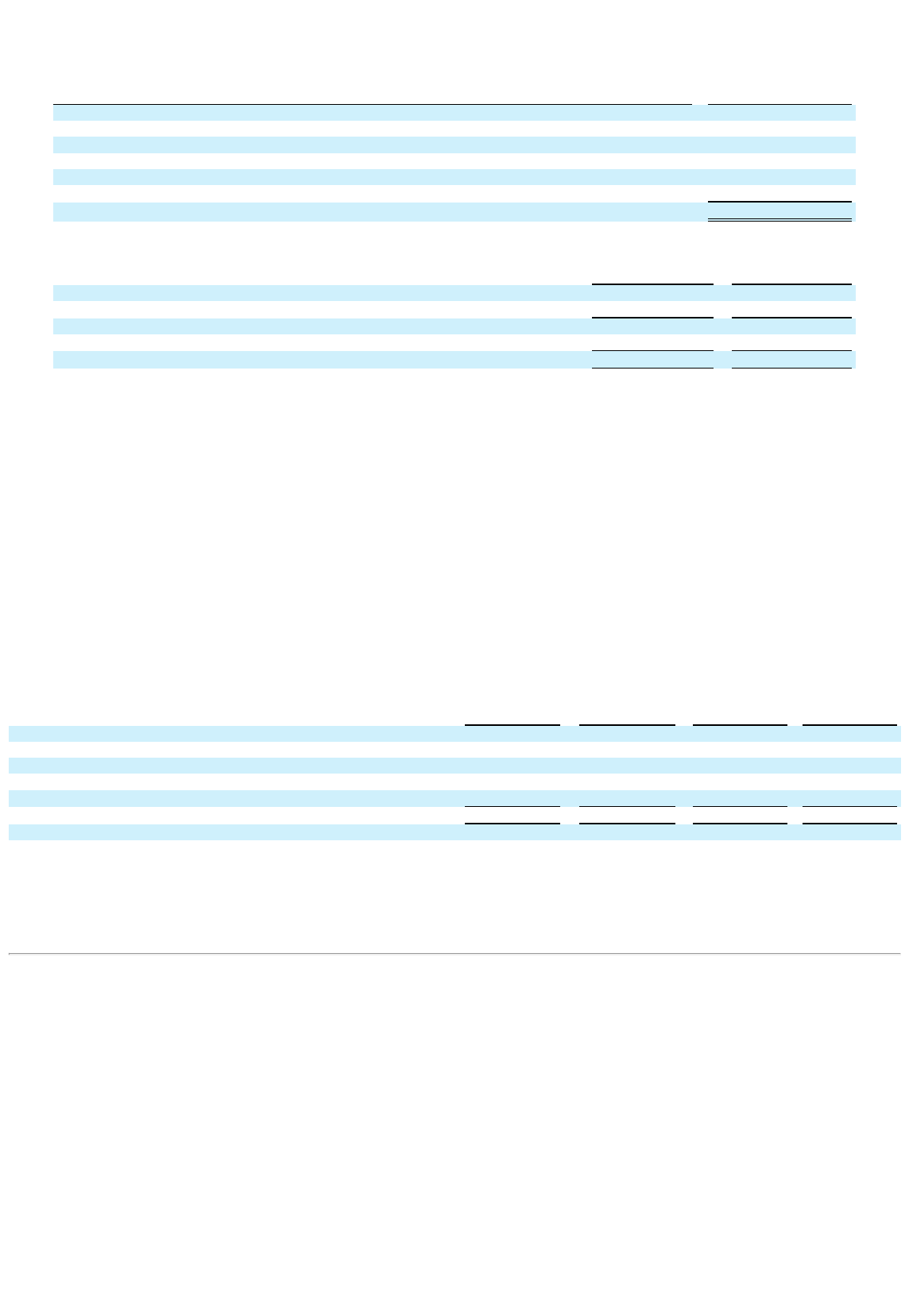
The following table illustrates estimated revenues expected to be recognized in the future related to performance obligations that are unsatisfied (or
partially unsatisfied) as of December 25, 2021. The Company has elected to exclude short term contracts and any other variable consideration recognized
on an “as invoiced” basis.
Contract liabilities to be recognized in: Amount
2022 $ 2,993
2023 1,082
2024 1,022
2025 952
2026 843
Thereafter
2,899
Total
$ 9,791
The summary set forth below represents the balances in deferred revenue as of December 25, 2021 and December 26, 2020:
December 25, 2021
December 26, 2020
Franchise fees $ 7,911 $ 7,542
Service revenue
1,880
1,337
Total deferred revenue 9,791 8,879
Long-term portion of deferred revenue
6,787
6,528
Current portion of deferred revenue
$ 3,004
$ 2,351
16. Equity Based Compensation
2021 Omnibus Incentive Plan
In August 2021, our board of directors adopted the 2021 Omnibus Incentive Plan (the “2021 Incentive Plan”) which became effective upon consummation
of our IPO and provides for the grant of equity-based awards to employees, consultants, and non-employee directors. The 2021 Incentive Plan provides for
an aggregate of 6,374,273 shares of Class A common stock that are reserved for issuance in respect of awards granted under the 2021 Incentive Plan. In
addition, the number of shares reserved for issuance under the 2021 Incentive Plan will automatically increase each fiscal year beginning with fiscal year
2022 and ending with fiscal year 2031 by the lesser of (a) 1% of the total number of shares outstanding on the last day of the immediately preceding fiscal
year on a fully diluted basis assuming that all shares available for issuance under the 2021 Incentive Plan are issued and outstanding or (b) such number of
shares determined by our board of directors. As of December 25, 2021 there were 5,606,202 shares available for issuance under the 2021 Incentive Plan.
Class A Common Stock Options
During the year ended December 25, 2021, we granted 322,997 stock options with an exercise price of $17.00 per share to certain directors and employees
under the 2021 Incentive Plan. The stock options granted will cliff vest on the third anniversary of the date of grant, subject in all cases to continued
employment on the applicable vesting date. The weighted average grant date fair value of the stock options was $7.48. The total grant date fair value of the
stock options will be recognized as equity-based compensation expense over the vesting period.
A summary of activity related to the options is as follows:
Number of
Options
Weighted Average
Exercise Price
Weighted Average
Remaining
Contractual Term
Aggregate
Intrinsic Value
(in thousands)
Outstanding at December 26, 2020 — —
Granted 322,997 $ 17.00
Exercised — —
Expired — —
Forfeited
(21,533 )
17.00
Outstanding at December 25, 2021
301,464
$ 17.00
9.6
$ 3,693
Exercisable at December 25, 2021 — — — —
During the year ended December 25, 2021, we recognized $305 of equity-based compensation expense related to the options in selling, general, and
administrative expense. As the options were granted in connection with the IPO, there was no expense recorded in fiscal years 2020 or 2019. As of
December 25, 2021, there was $1,941 of total unrecognized compensation expense related to outstanding stock options expected to be recognized over a
weighted average period of 2.6 years.
83
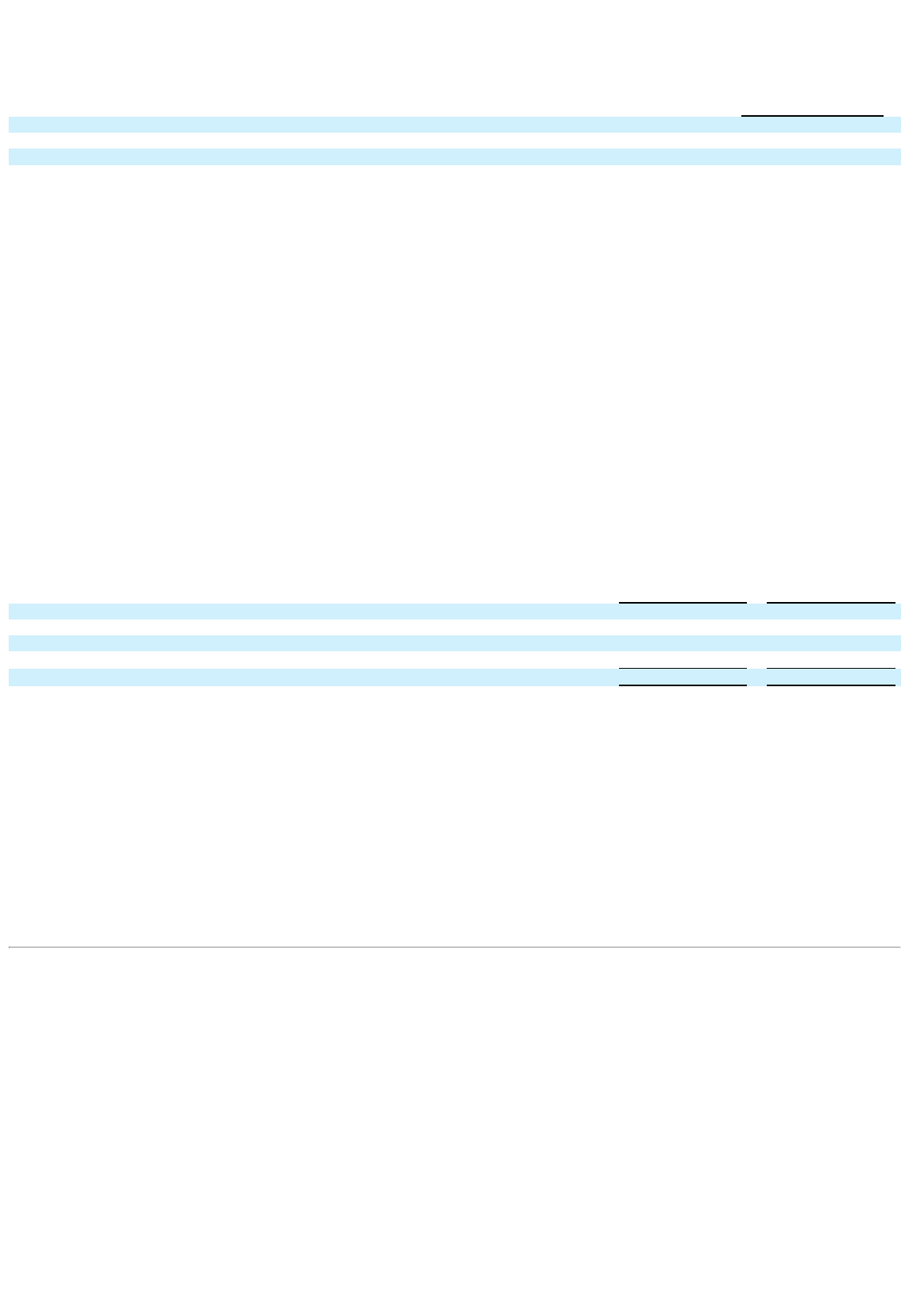
The Company estimates the fair value of the options using the Black-Scholes option pricing model. The following table presents the assumptions used in
the Black-Scholes model to determine the fair value of the stock options for the year ended December 25, 2021. Black-Scholes assumptions have not been
disclosed for any other periods presented as there were no stock options granted in those periods.
For the Year Ended
December 25, 2021
Expected dividend yield 0.0 %
Expected volatility 43.8 %
Risk-free rate 0.9 %
Expected term (in years) 6.5
A description of each of the inputs to the Black-Scholes model is as follows:
• Expected dividend yield - An increase in the expected dividend yield would decrease compensation expense.
• Expected volatility - This is a measure of the amount by which the price of the equity instrument has fluctuated or is expected to fluctuate. The
expected volatility was based on the historical volatility of a group of guideline companies. An increase in expected volatility would increase
compensation expense.
• Risk-free interest rate - This is the U.S. Treasury rate as of the measurement date having a term approximating the expected life of the award.
An increase in the risk-free interest rate would increase compensation expense.
• Expected term - The period of time over which the awards are expected to remain outstanding. The Company estimates the expected term as
the mid-point between actual or expected vesting date and the contractual term. An increase in the expected term would increase compensation
expense.
Restricted Stock Units
During the year ended December 25, 2021, we granted 494,388 restricted stock units (“RSUs”) to certain directors and employees under the 2021 Incentive
Plan. The majority of awards will vest in three equal installments of 33.33% on each of the first three anniversaries of the date of grant, subject in all cases
to continued employment on the applicable vesting date. Some awards will vest in quarterly installments of 21% for the first four quarters subsequent to the
grant date, and 4% for the 4 quarters thereafter, subject in all cases to continued employment on the applicable vesting date. The total grant date fair value
of the restricted stock units will be recognized as equity-based compensation expense over the vesting period. The grant date fair value of the restricted
stock units is determined based on the fair value of the underlying Class A common stock on the date of grant.
A summary of activity related to the RSUs is as follows:
Number of RSUs
Weighted Average Grant
Date
Fair Value
Outstanding at December 26, 2020 — $ —
Granted 494,388 17.42
Vested (10,636 ) 18.36
Forfeited
(27,781 )
17.21
Outstanding at December 25, 2021
455,971
$ 17.41
During the year ended December 25, 2021, we recognized $1,219 of equity-based compensation expense related to the RSUs in selling, general, and
administrative expense. As the RSUs were granted in connection with and subsequent to the IPO, there was no expense recorded in fiscal years 2020 or
2019. As of December 25, 2021, there was $6,895 of total unrecognized compensation expense related to outstanding RSUs expected to be recognized over
a weighted average period of 2.6 years.
Management Holdco Incentive Plan
On December 12, 2018, EWC Ventures LLC and Management Holdco adopted the Amended and Restated EWC Management Holdco, LLC Equity
Incentive Plan (the “LLC Incentive Plan”), under which Management Holdco granted units of Management Holdco (“Incentive Units”) to employees,
directors, and consultants of EWC Ventures LLC and its subsidiaries. In connection with the Reorganization Transactions, modifications to certain pre-
reorganization equity-based awards outstanding under the LLC Incentive Plan were made, primarily with respect to certain vesting conditions, which
resulted in the Company recording additional equity-based compensation expense of $8,489 during the year ended December 25, 2021. The terms of
awards outstanding under the LLC Incentive plan are described below. There will be no further grants made under the LLC Incentive Plan.
84
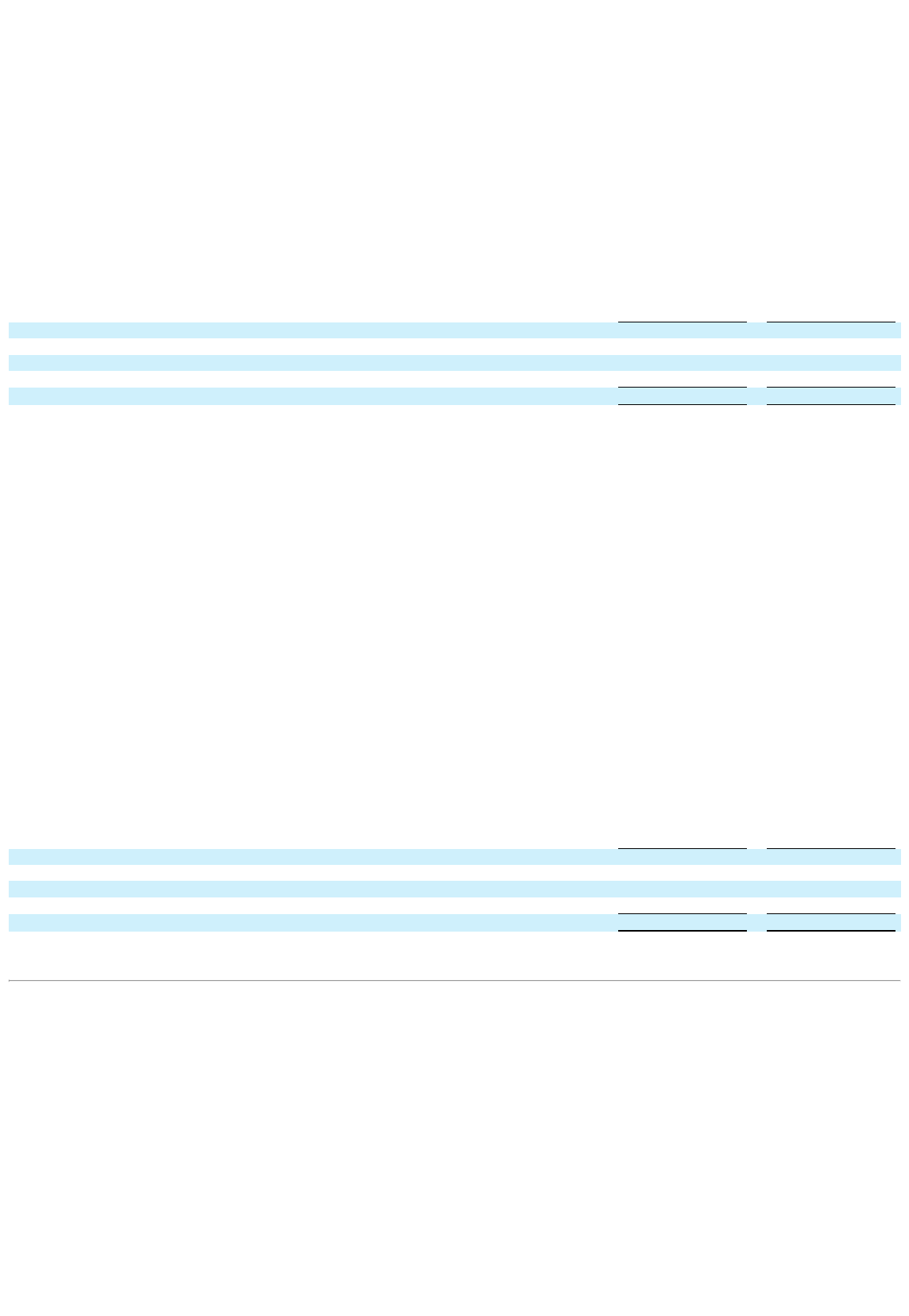
Time-based Units
Prior to the consummation of the Reorganization Transactions, EWC Ventures LLC granted time-based Incentive Units under the LLC Incentive Plan. The
time-based Incentive Units generally vest over 5 years, and the Company expenses time-based Incentive Units based on the grant date fair value of the
award on a straight-line basis over the associated service period of the award. In connection with the Reorganization Transactions, the time-based Incentive
Units were recapitalized into a new number of EWC Ventures Units (which we refer to as the “Time-based Units” both before and after the Reorganization
Transactions), equal to the same aggregate fair value as the award immediately prior to the Reorganization Transactions, and subject to the original vesting
schedules. No incremental expense was recognized as there was no change to the fair value of the awards as a result of the Reorganization Transactions.
Accordingly, we continue to recognize the original grant date fair value of the Time-based Units over the remaining service period. The Company
estimated the fair value of the Time-based Units as of the grant date based on a determination of the total fair value of the Company’s equity as of the
valuation date which was then run through a hypothetical liquidation model.
We determined that the activity for the period prior to the Reorganization Transactions would not be meaningful to the users of these consolidated financial
statements due to the significant nature of the Reorganization Transactions on the capital structure.
The following table sets forth the activity related to the Time-Based Units from August 4, 2021, to December 25, 2021, which represents the period
subsequent to the Reorganization Transactions:
Number of Time-Based
Units
Weighted Average Grant
Date
Fair Value
Outstanding at August 4, 2021 1,048,706 $ 2.56
Granted — —
Vested (223,452 ) 2.33
Forfeited
(47,493 )
2.66
Outstanding at December 25, 2021
777,761
$ 2.62
During the years ended December 25, 2021, December 26, 2020 and December 28, 2019 we recognized $1,122, $2,052 and $1,570, respectively, of equity-
based compensation expense related to Time-based Units in selling, general, and administrative expense. As of December 25, 2021, there was $2,420 of
total unrecognized compensation expense related to unvested time-based Incentive Units expected to be recognized over a weighted average period of 2.2
years.
2.0x Units and 2.5x Units
Prior to the consummation of the Reorganization Transactions, EWC Ventures LLC granted Incentive Units with performance-based vesting criteria that
vest in one or more tranches contingent upon the achievement of certain targets, including a tranche which vested upon the achievement of 2.0x multiple on
invested capital (“MOIC”) and a tranche which vested upon achievement of a 2.5x MOIC. Equity-based compensation expense was not previously
recognized for these awards, based on the projected probability of achievement of the respective target(s). In connection with the Reorganization
Transactions, these awards were recapitalized into a new number of EWC Ventures Units (which we refer to as the “2.0x Units” and 2.5x Units” both
before and after the Reorganization Transactions). The vesting conditions were modified to include a time-based vesting condition such that the units will
vest as if the units were time-based units on the initial date of grant; provided that, such units shall still fully vest upon achievement of the original
performance targets, as applicable. As a result of the modification, the Company recorded equity-based compensation expense of $5,645, which is the
modification date fair value of the awards which became immediately vested. The remainder of the modification date fair value of the 2.0x Units and 2.5x
Units is recognized straight line over the remaining service period. The modification date fair value was determined based on the fair value of the
underlying EWC Ventures Units on the modification date, which was determined based on the initial public offering price per share of the Company’s Class
A common stock.
We determined that the activity for the period prior to the Reorganization Transactions would not be meaningful to the users of these consolidated financial
statements due to the significant nature of the Reorganization Transactions on the capital structure.
The following table sets forth the activity related to the 2.0x and 2.5x Units from August 4, 2021, to December 25, 2021, which represents the period
subsequent to the Reorganization Transactions:
Number of 2.0x and 2.5x
Units
Weighted Average Grant
Date
Fair Value
Outstanding at August 4, 2021 355,134 $ 17.00
Granted — —
Vested (44,326 ) 17.00
Forfeited
(35,777 )
17.00
Outstanding at December 25, 2021
275,031
$ 17.00
85
During the year ended December 25, 2021, we recognized $7,240 of equity-based compensation expense related to the 2.0x Units and 2.5x Units included
in selling, general and administrative expense. As of December 25, 2021, there was $4,085 of total unrecognized compensation expense related to unvested
2.0x Units and unvested 2.5x Units expected to be recognized over a weighted average period of 2.6 years.
3.0x Units
Prior to the consummation of the Reorganization Transactions, EWC Ventures LLC granted Incentive Units with performance and market-based vesting
criteria that would have vested upon achievement of 3.0x MOIC. In connection with the Reorganization Transactions, these awards were recapitalized into
a new number of EWC Ventures Units (which we refer to as the “3.0x Units” both before and after the Reorganization Transactions). These awards were
modified such that the awards will also be eligible to vest upon the occurrence of either (i) the achievement of a 2.0x MOIC at such time as General
Atlantic’s investment in the Company is no less than 35% of the fully diluted units of the Company or (ii) the first of December 31, 2022, March 31, 2023,
June 30, 2023, September 30, 2023 or December 31, 2023 on which a specific volume weighted average trading price of our Class A common stock is
achieved. Equity-based compensation expense was not previously recognized for these awards, based on the projected probability of achievement of the
target.
The modified vesting conditions described above represent market conditions. Compensation expense for performance-based awards with a market
condition is recognized on a straight-line basis over the estimated service period of the award, regardless of whether the market condition is satisfied.
Accordingly, following the Reorganization Transactions, expense will be recognized prospectively based on the modification date fair value of the
modified award. The Company used a Geometric Brownian Motion simulation formula to determine the fair value and the derived service periods of these
3.0x Units as of the modification date.
We determined that the activity for the period prior to the Reorganization Transactions would not be meaningful to the users of these consolidated financial
statements due to the significant nature of the Reorganization Transactions on the capital structure.
The following table sets forth the activity related to the 3.0x Units from August 4, 2021, to December 25, 2021, which represents the period subsequent to
the Reorganization Transactions:
Number of 3.0x Units
Weighted Average Grant
Date
Fair Value
Outstanding at August 4, 2021 648,174 $ 7.75
Granted — —
Vested — —
Forfeited
(37,195 )
7.70
Outstanding at December 25, 2021
610,979
$ 7.75
During the year ended December 25, 2021 we recognized $1,249 of equity-based compensation expense related to the 3.0x Units in selling, general, and
administrative expense. As of December 25, 2021, total unrecognized equity-based compensation related to the 3.0x Units was $3,487, which is expected
to be recognized over a weighted-average period of approximately 0.8 years.
Summary of Equity-Based Compensation Expense
The Company recognized equity-based compensation expense in the following amounts within in selling, general and administrative expense on the
Consolidated Statements of Operations:
For the Years Ended
December 25, 2021
December 26, 2020
December 28, 2019
Class A Common Stock Options $ 305 $ — $ —
Restricted Stock Units 1,219 — —
Time-based Units 1,122 2,052 1,570
2.0x and 2.5x Units 7,240 — —
3.0x Units
1,249
—
—
Total
$ 11,135
$ 2,052
$ 1,570
17. Employee retirement plan
The Company offers its employees the opportunity to participate in a defined contribution retirement plan, where eligible employees may contribute a
percentage of their annual compensation subject to limitations set by the Internal Revenue Code. For the years ended December 25, 2021, December 26,
2020 and December 28, 2019, the employer match expense recognized under this plan was $349,
86

$301 and $375, respectively, of which, $330, $291 and $353, respectively, is included in selling, general and administrative expenses and $19, $10 and $22,
respectively, is included in Cost of revenue on the Consolidated Statements of Operations.
18. Related party transactions
The Company recognized advances to certain related party members of zero and $689 as of December 25, 2021 and December 26, 2020, respectively,
related to payments of fees on behalf of the members in connection with the GA Acquisition. These advances are reported in advances to related parties
within the Consolidated Balance Sheets. These advances were settled in August 2021 through a reduction of the tax distribution to members made in
connection with the Reorganization Transactions discussed in Note 1. Additionally, the Company paid fees to certain members for consulting services
provided to the Company. Related party consulting fees of $117, $200 and $200 for the years ended December 25, 2021, December 26, 2020 and December
28, 2019, respectively, are included in selling, general, and administrative expenses in the Consolidated Statements of Operations. The term of the
consulting services agreement ended in August 2021.
19. Income Taxes
EWC Ventures is a limited liability company that is treated as a partnership for U.S. federal income tax purposes and for most applicable state and local
income tax purposes. As a partnership, EWC Ventures is not subject to U.S. federal and certain state and local income taxes. Any taxable income or loss
generated by EWC Ventures is passed through to and included in the taxable income or loss of its members on a pro rata basis, subject to applicable tax
regulations. Because EWC Ventures is our financial reporting predecessor and not subject to entity level income tax, no current or deferred income taxes
were recorded in fiscal years 2019, 2020 and the period prior to August 4, 2021.
We were appointed the sole managing member of EWC Ventures in connection with the Reorganization Transactions on August 4, 2021. Following the
Reorganization Transactions the Company is now subject to U.S. federal income taxes, in addition to state and local income taxes, with respect to its
allocable share of any taxable income or loss of EWC Ventures. The remaining share of EWC Ventures income or loss remains non-taxable to the Company
and is not reflected in current or deferred income taxes.
The components of income tax expense for the year ended December 25, 2021 were as follows:
For the Year Ended December
25, 2021
Current:
Federal $ —
State
114
114
Deferred:
Federal —
State
—
—
Income Tax Expense
$ 114
A reconciliation of the statutory federal income tax rate to our effective rate for continuing operations is provided below:
For the Year Ended December
25, 2021
Statutory federal income tax rate 21.0 %
State income taxes, net 2.2 %
Pre-IPO period not subject to income tax (53.1 )%
Income attributable to noncontrolling interest 15.1 %
Nondeductible executive compensation 0.8 %
Investment in EWC Ventures 47.4 %
Valuation allowance
(30.6 )%
2.8 %
87
Deferred tax assets and liabilities, were as follows as of December 25, 2021:
December 25,
2021
Deferred tax assets
Net operating losses $ 7,396
Investment in EWC Ventures 30,750
Tax Receivable Agreement 9,540
Equity based compensation 349
Other
34
Total deferred tax assets before valuation allowance 48,069
Valuation allowance
(48,069 )
Total deferred tax assets after valuation allowance
—
Total deferred tax liabilities
—
Net deferred tax asset
$ —
Valuation Allowance
As of December 25, 2021, we continue to conclude that the negative evidence regarding our ability to realize our deferred tax assets outweighed the
positive evidence, and the Company has a full valuation allowance of $48,069 against its net deferred tax assets. The Company has a history of cumulative
pre-tax losses which we believe represents significant negative evidence in evaluating whether our deferred tax assets are realizable. Given these
cumulative losses and lack of forecast history we do not believe we can rely on projections of future taxable income exclusive of reversing taxable
temporary differences to support the realization of our deferred tax assets.
The change in our valuation allowance against our deferred tax assets for the year ended December 25, 2021 was as follows:
For the Year Ended December
25, 2021
Beginning balance $ —
Recorded to additional-paid-in-capital (50,373 )
Recorded to other comprehensive income 32
Recorded to income tax expense
2,272
Ending balance
$ (48,069 )
Net Operating Loss Carryforwards
As of December 25, 2021, the Company has $31,502 of gross federal net operating loss carryforwards and $16,808 of gross state net operating loss
carryforwards. The federal and certain state net operating losses have an indefinite carryforward period and are subject to an annual limitation of 80% of
current year taxable income. The remaining net operating losses expire at various dates through 2038.
Uncertain Tax Positions
As of December 25, 2021 the Company does not have any unrecognized tax benefits. The Company is subject to audit examinations at the federal and state
levels by the tax authorities for all tax years since formation of the Company.
Tax Receivable Agreement
As of December 25, 2021, future payments under the TRA with respect to the purchase of EWC Ventures Units which occurred as part of the IPO and
through December 25, 2021 are expected to be $115,027. Payments made under the TRA represent payments that otherwise would have been made to
taxing authorities in the absence of attributes obtained by us as a result of exchanges by our pre-IPO members. Such amounts will be paid only when a
cash tax savings is realized as a result of attributes subject to the TRA. That is, payments under the TRA are only expected to be made in periods following
the filing of a tax return in which we are able to utilize certain tax benefits to reduce our cash taxes paid to a taxing authority. The impact of any changes in
the projected obligations under the TRA as a result of changes in the geographic mix of the Company’s earnings, changes in tax legislation and tax rates or
other factors that may impact the Company’s tax savings will be reflected in income before taxes on the Consolidated Statement of Operations in the period
in which the change occurs. As of December 25, 2021, the TRA liability recorded was $59,167 based on current projections of future taxable income
taking into consideration the Company’s full valuation allowance against its net deferred tax asset.
88
20. Net loss per share
Basic net loss per share of Class A common stock is computed by dividing net loss attributable to Class A common shareholders for the periods subsequent
to the Reorganization Transactions by the weighted average number of shares of Class A common stock outstanding for the same period. Shares issued
during the period and shares reacquired during the period are weighted for the portion of the period in which the shares were outstanding. Diluted net loss
per share of Class A common stock is computed by dividing net loss attributable to Class A common shareholders by the weighted-average number of
shares of Class A common stock outstanding adjusted to give effect to potentially dilutive securities.
Prior to the Reorganization Transactions, the EWC Ventures capital structure included Class A, Class B, Class C, and Class D Units. We determined that
the presentation of net income (loss) per unit for the period prior to the Reorganization Transactions would not be meaningful to the users of these
consolidated financial statements due to the significant nature of the Reorganization Transactions on the capital structure. Therefore, net income (loss) per
unit information has not been presented for periods prior to the Reorganization Transactions.
The following table sets forth the computation of basic and diluted net loss per share of Class A common stock for the period from August 4, 2021 to
December 25, 2021, which represents the period subsequent to the Reorganization Transactions:
Period of August 4-
December 25, 2021
(in thousands, except for share and per share amounts)
Net loss $ (6,360 )
Less: net loss attributable to noncontrolling interests
(2,857 )
Net loss applicable to Class A common shareholders $ (3,503 )
Basic and diluted weighted average outstanding shares
Class A Common Stock 32,234,507
Basic and diluted net loss per unit applicable to shareholders:
Class A Common Stock $ (0.11 )
Shares of Class B common stock do not share in the earnings or losses attributable to the Company and are therefore not participating securities. As such,
separate presentation of basic and diluted net loss per share of Class B common stock under the two-class method has not been presented. Shares of Class B
common stock are, however, considered potentially dilutive shares of Class A common stock because shares of Class B common stock, together with the
related EWC Ventures Units, are exchangeable into shares of Class A common stock on a one-for-one basis. The 26,700,477 shares of Class B common
stock outstanding as of December 25, 2021 were determined to be anti-dilutive as we recorded a net loss for the period, and have therefore been excluded
from the computation of diluted net loss per share of Class A common stock.
In addition, 301,464 stock options and 455,971 restricted stock units were excluded from the computation of diluted net loss per share of Class A common
stock, because the effect would have been anti-dilutive as we recorded a net loss for the period.
21. Subsequent Events
On March 15, 2022, the Company announced that certain of its subsidiaries intend to complete a refinancing of our existing 2026 Credit Agreement with a
new securitized financing facility. As of December 25, 2021, the Company had an outstanding principal amount of $180.0 million on its 2026 Term Loan.
The Company intends to replace the 2026 Credit Agreement with a new securitized financing facility expected to be comprised of $400.0 million principal
amount of senior fixed-rate term notes and $40.0 million principal amount of variable funding notes. The net proceeds of the securitized financing facility
are expected to be used:
• to repay all of the existing indebtedness under the 2026 Credit Agreement,
• to pay the transaction costs associated with the securitized financing facility,
• and to fund a one-time special dividend to stockholders.
The consummation of the offering is subject to market and other conditions and is anticipated to close in the second fiscal quarter of 2022. However, there
can be no assurance that the Company will be able to successfully complete the refinancing transaction on the terms described or at all.
89
Item 9. Changes in and Disagreements With Accountants on Accounting and Financial Disclosure.
None.
Item 9A. Controls and Procedures.
Evaluation of Disclosure Controls and Procedures
Our management, with the participation of our Chief Executive Officer (“CEO”) and Chief Financial Officer (“CFO”), has evaluated the effectiveness of
our disclosure controls and procedures, as such term is defined in Rules 13a-15(e) and 15d-15(e) under the Exchange Act, as of the end of the period
covered by this annual report on Form 10-K.
There are inherent limitations to the effectiveness of any system of disclosure controls and procedures, including the possibility of human error and the
circumvention or overriding of the controls and procedures. Our disclosure controls and procedures are designed to provide reasonable assurance of
achieving their control objectives.
Based on that evaluation, our CEO and CFO concluded that as of December 25, 2021, our disclosure controls and procedures were effective to provide
reasonable assurance that the information required to be disclosed by the Company in the reports it files or submits with the Securities and Exchange
Commission is recorded, processed, summarized and reported within the time periods specified in Securities and Exchange Commission rules and forms
and is accumulated and communicated to our management, including the principal executive and principal financial officers, or persons performing similar
functions, as appropriate to allow timely decisions regarding required disclosure.
Management’s Report on Internal Control over Financial Reporting
This Annual Report on Form 10-K does not include a report of management’s assessment regarding internal control over financial reporting or an
attestation report of our independent registered public accounting firm due to a transition period established by rules of the SEC for newly public
companies.
Changes in internal control over financial reporting
There have been no changes in our internal control over financial reporting that occurred during the 13 weeks ended December 25, 2021, that have
materially affected, or are reasonably likely to materially affect, our internal control over financial reporting.
Item 9B. Other Information.
None.
Item 9C. Disclosure Regarding Foreign Jurisdictions that Prevent Inspections.
None.
90

PART III
Item 10. Directors, Executive Officers and Corporate Governance.
The information called for by Item 10 is incorporated herein by reference to our Definitive Proxy Statement relating to our 2021 Annual Meeting of
Stockholders to be held June 8, 2022. We intend to file such Definitive Proxy Statement with the Securities and Exchange Commission pursuant to
Regulation 14A within 120 days after the end of the fiscal year covered by this Annual Report on Form 10-K.
Item 11. Executive Compensation.
The information required by this Item 11 will be contained in the Definitive Proxy Statement referenced above in Item 10 and is incorporated herein by
reference.
Item 12. Security Ownership of Certain Beneficial Owners and Management and Related Stockholder Matters.
The information required by this Item 12 will be contained in the Definitive Proxy Statement referenced above in Item 10 and is incorporated herein by
reference.
Item 13. Certain Relationships and Related Transactions, and Director Independence.
The information required by this Item 13 will be contained in the Definitive Proxy Statement referenced above in Item 10 and is incorporated herein by
reference.
Item 14. Principal Accounting Fees and Services.
The information required by this Item 14 will be contained in the Definitive Proxy Statement referenced above in Item 10 and is incorporated herein by
reference.
91
PART IV
Item 15. Exhibits, Financial Statement Schedules.
(a) (1) See the index to consolidated financial statements provided in Item 8 of this annual report on Form 10-K for a list of the financial
statements filed as part of this report.
(2) Financial statement schedules are omitted because they are either not applicable or not material.
(3) The following documents are filed, furnished or incorporated by reference to this report as required by Item 601 of Regulation S-K.
Exhibit
Number Description
2.1
Reorganization Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the other parties thereto. (incorporated by reference
to Exhibit 2.1 to the Registrant's Quarterly Report on Form 10-Q filed on September 14, 2021).
2.2
Merger Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the other parties thereto (incorporated by reference to
Exhibit 2.2 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
2.3
Merger Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the other parties thereto (incorporated by reference to
Exhibit 2.3 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
3.1
Amended and Restated Certificate of Incorporation of the Registrant (incorporated by reference to Exhibit 4.1 to the Registrant’s Registration Statement
on Form S-8 filed on August 4, 2021).
3.2
Amended and Restated By-laws of the Registrant (incorporated by reference to Exhibit 4.2 to the Registrant’s Registration Statement on Form S-8 filed on
August 4, 2021).
4.1*
Description of Class A Common Stock.
10.1
Credit Agreement, dated as of August 9, 2021, among EW Intermediate Holdco, LLC, the several lenders from time to time party thereto, and Bank of
America, N.A., as administrative agent, collateral agent and a letter of credit issuer (incorporated by reference to Exhibit 10.1 to the Registrant’s Current
Report on Form 8-K filed on August 9, 2021).
10.2
Indemnification Agreement (incorporated by reference to Exhibit 10.5 to the Registrant’s Registration Statement on Form S-1 filed on July 28, 2021).
10.3
Stockholders Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the stockholders named therein (incorporated by
reference to Exhibit 10.3 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.4
Exchange Agreement, dated as of August 4, 2021, by and among EWC Ventures, LLC, European Wax Center, Inc. and the holders party thereto
(incorporated by reference to Exhibit 10.4 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.5
Registration Rights Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the holders party thereto (incorporated by
reference to Exhibit 10.5 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.6
Tax Receivable Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the other parties thereto (incorporated by reference
to Exhibit 10.6 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.7
Amended and Restated Limited Liability Company Agreement of EWC Ventures, LLC, dated as of August 4, 2021, by and among EWC Ventures, LLC
and the other parties thereto (incorporated by reference to Exhibit 10.7 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021)
10.8
Purchase Agreement, dated as of August 4, 2021, by and among EWC Ventures, LLC and the sellers named therein (incorporated by reference to Exhibit
10.8 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.9
Purchase Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the sellers named therein (incorporated by reference to
Exhibit 10.9 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.10
Class B Common Stock Subscription Agreement, dated as of August 4, 2021, by and among European Wax Center, Inc. and the subscribers named therein
(incorporated by reference to Exhibit 10.10 to the Registrant’s Quarterly Report on Form 10-Q filed on September 14, 2021).
10.11
European Wax Center, Inc. 2021 Omnibus Incentive Plan, effective as of August 4, 2021 (incorporated by reference to Exhibit 10.11 to the Registrant’s
Quarterly Report on Form 10-Q filed on September 14, 2021).
10.12+
Form of Employee Option Award Agreement for use with the 2021 Omnibus Incentive Plan (incorporated by reference to Exhibit 10.18 to the Registrant’s
Registration Statement on Form S-1 filed on July 13, 2021).
10.13+
Form of Employee Restricted Stock Unit Award Agreement for use with the 2021 Omnibus Incentive Plan (incorporated by reference to Exhibit 10.19 to
the Registrant’s Registration Statement on Form S-1 filed on July 13, 2021).
10.14*
Separation Agreement, dated as of January 17, 2022, by and among EWC Ventures LLC and Jennifer Vanderveldt
23.1*
Consent of Deloitte & Touche LLP, Independent Registered Public Accounting Firm
31.1*
Certification of Principal Executive Officer Pursuant to Rules 13a-14(a) and 15d-14(a) under the Securities Exchange Act of 1934, as Adopted Pursuant to
Section 302 of the Sarbanes-Oxley Act of 2002.
31.2*
Certification of Principal Financial Officer Pursuant to Rules 13a-14(a) and 15d-14(a) under the Securities Exchange Act of 1934, as Adopted Pursuant to
Section 302 of the Sarbanes-Oxley Act of 2002.
32.1**
Certification of Principal Executive Officer Pursuant to 18 U.S.C. Section 1350, as Adopted Pursuant to Section 906 of the Sarbanes-Oxley Act of 2002.
32.2**
Certification of Principal Financial Officer Pursuant to 18 U.S.C. Section 1350, as Adopted Pursuant to Section 906 of the Sarbanes-Oxley Act of 2002.
92
101.INS
Inline XBRL Instance Document – the instance document does not appear in the Interactive Data File because XBRL tags are embedded within the Inline
XBRL document.
101.SCH
Inline XBRL Taxonomy Extension Schema Document
101.CAL
Inline XBRL Taxonomy Extension Calculation Linkbase Document
101.DEF
Inline XBRL Taxonomy Extension Definition Linkbase Document
101.LAB
Inline XBRL Taxonomy Extension Label Linkbase Document
101.PRE
Inline XBRL Taxonomy Extension Presentation Linkbase Document
104
Cover Page Interactive Data File (embedded within the Inline XBRL document)
* Filed herewith.
** European Wax Center, Inc. is furnishing, but not filing, the written statement pursuant to Title 18 United States Code 1350, as added by Section 906 of the Sarbanes Oxley Act of 2002, of
David P. Berg, our Chief Executive Officer and David L. Willis, our Chief Financial Officer.
+ Indicates management contract or compensatory plan.
Item 16. Form 10-K Summary
None.
93
SIGNATURES
Pursuant to the requirements of Section 13 or 15(d) of the Securities Exchange Act of 1934, as amended, the Registrant has duly caused this Report to be
signed on its behalf by the undersigned, thereunto duly authorized.
European Wax Center, Inc.
Date: March 15, 2022 By: /s/ DAVID P. BERG
David P. Berg
Chief Executive Officer
Pursuant to the requirements of the Securities Exchange Act of 1934, as amended, this Report has been signed below by the following persons on behalf of
the Registrant in the capacities and on the dates indicated.
Name Title Date
/s/ DAVID P. BERG Chief Executive Officer
March 15, 2022
David P. Berg (Principal Executive Officer)
/s/ DAVID L. WILLIS Chief Financial Officer and Chief Operating Officer
March 15, 2022
David L. Willis (Principal Financial Officer)
/s/ CINDY THOMASSEE Chief Accounting Officer and Controller
March 15, 2022
Cindy Thomassee (Principal Accounting Officer)
/s/ ALEXA BARTLETT Director
March 15, 2022
Alexa Bartlett
/s/ ANDREW CRAWFORD Director
March 15, 2022
Andrew Crawford
/s/ LAURIE ANN GOLDMAN Director
March 15, 2022
Laurie Ann Goldman
/s/ SHAW JOSEPH Director
March 15, 2022
Shaw Joseph
/s/ DORVIN D. LIVELY Director
March 15, 2022
Dorvin D. Lively
/s/ NITAL SCOTT Director
March 15, 2022
Nital Scott
94
Exhibit 4.1
Description of Class A Common Stock
General
The following description of our capital stock is intended as a summary only and is qualified in its entirety by reference to our certificate of
incorporation and bylaws, which are filed as exhibits to the Annual Report on Form 10-K of which this Exhibit 4.1 is a part, and to the
applicable provisions of the Delaware General Corporation Law (the “DGCL”).
As of December 25, 2021, our authorized capital stock consisted of 600,000,000 shares of Class A common stock, par value $0.00001 per
share, and 60,000,000 shares of Class B common stock, par value $0.00001 per share, and 100,000,000 shares of preferred stock, par value
$.00001 per share.
Our Class A common stock is registered under Section 12 of the Securities Exchange Act of 1934 and is listed on the Nasdaq Stock Market
under the symbol “EWCZ.”
Common Stock
Voting
The holders of our Class A common stock and Class B common stock vote together as a single class on all matters submitted to stockholders
for their vote or approval, except (i) as required by applicable law or (ii) any amendment (including by merger, consolidation, reorganization
or similar event) to our amended and restated certificate of incorporation that would affect the rights of the Class A common stock in a
manner that is disproportionately adverse as compared to the Class B common stock, or vice versa, in which case the holders of Class A
common stock or the holders of Class B common stock shall vote together as a class.
Holders of our Class A common stock and Class B common stock are entitled to one vote on all matters submitted to stockholders for their
vote or approval.
Dividends
The holders of Class A common stock are entitled to receive dividends when, as and if declared by our board of directors out of legally
available funds, subject to the prior rights of holders of any preferred stock then outstanding.
The holders of our Class B common stock do not have any right to receive dividends other than dividends consisting of shares of our Class B
common stock, paid proportionally with respect to each outstanding share of our Class B common stock in connection with stock dividends.
Liquidation or Dissolution
Upon our liquidation or dissolution, the holders of our Class A common stock are entitled to share ratably in those of our assets that are
legally available for distribution to stockholders after payment of liabilities and subject to the prior rights of any holders of preferred stock
then outstanding. Other than their par value, the holders of our Class B common stock do not have any right to receive a distribution upon a
liquidation or dissolution of our company.
-1-
Other Provisions
None of the Class A common stock or Class B common stock has any pre-emptive or other subscription rights. There are no redemption or
sinking fund provisions applicable to the Class A common stock or Class B common stock.
Preferred Stock
Our board of directors is authorized, subject to limitations prescribed by Delaware law and our amended and restated certificate of
incorporation, to determine the terms and conditions of the preferred stock, including whether the shares of preferred stock will be issued in
one or more series, the number of shares to be included in each series and the powers, designations, preferences and rights of the shares. Our
board of directors also are authorized to designate any qualifications, limitations or restrictions on the shares without any further vote or
action by the stockholders. The issuance of preferred stock may have the effect of delaying, deferring or preventing a change in control of our
Company and may adversely affect the voting and other rights of the holders of our Class A common stock and Class B common stock,
which could have a negative impact on the market price of our Class A common stock. We have no current plan to issue any shares of
preferred stock.
Corporate Opportunity
Our amended and restated certificate of incorporation provides that, to the fullest extent permitted by law, the doctrine of “corporate
opportunity” will not apply against the General Atlantic Equityholders, stockholding affiliates and managed accounts of General Atlantic,
any of our non-employee directors or any of their respective affiliates in a manner that would prohibit them from investing in competing
businesses.
Anti-Takeover Provisions
The provisions of our amended and restated certificate of incorporation and amended and restated by-laws and of the Delaware General
Corporation Law summarized below may have an anti-takeover effect and may delay, defer or prevent a tender offer or takeover attempt that
you might consider in your best interest, including an attempt that might result in your receipt of a premium over the market price for your
shares of Class A common stock.
Anti-Takeover Effects of Our Amended and Restated Certificate of Incorporation and Amended and Restated By-laws
Some provisions of our amended and restated certificate of incorporation and amended and restated by-laws described below, contain
provisions that could make the following transactions more difficult: acquisitions of us by means of a tender offer, a proxy contest or
otherwise; or removal of our incumbent officers and directors. These provisions may also have the effect of preventing changes in our
management. It is possible that these provisions could make it more difficult to accomplish or could deter transactions that stockholders may
otherwise consider to be in their best interest or in our best interests, including transactions that might result in a premium over the market
price for our shares.
These provisions include:
-2-
Classified Board. Our amended and restated certificate of incorporation provides that our board of directors is divided into three classes of
directors, with the classes as nearly equal in number as possible. As a result, approximately one-third of our board of directors will be elected
each year. The classification of directors has the effect of making it more difficult for stockholders to change the composition of our board.
Our amended and restated certificate of incorporation also provides that, subject to any rights of holders of preferred stock to elect additional
directors under specified circumstances and the Stockholders Agreement, the number of directors will be fixed exclusively pursuant to a
resolution adopted by our board of directors.
Super-Majority Vote. The General Atlantic Equityholders and their affiliates and successors now no longer collectively beneficially own
shares representing 50% of our issued and outstanding common stock. Because their ownership has decreased below 50% (the “50%
Triggering Event”), according to our amended and restated certificate of incorporation, other than preferred stock directors and subject to
obtaining any required stockholder votes or consents under the Stockholders Agreement, directors may only be removed for cause and by the
affirmative vote of holders of 66
2⁄3
% of the total voting power of our outstanding shares of common stock, voting together as a single class.
This requirement of a super-majority vote to remove directors for cause could enable a minority of our stockholders to exercise veto power
over any such removal.
Action by Written Consent; Special Meetings of Stockholders. Our amended and restated certificate of incorporation provides that, following
the occurrence of when the General Atlantic Equityholders and their affiliates and successors no longer collectively beneficially own shares
representing 40% of our issued and outstanding common stock (the “40% Triggering Event”)—which 40% Triggering Event has not yet
occurred—stockholder action can be taken only at an annual or special meeting of stockholders and cannot be taken by written consent in
lieu of a meeting. Our amended and restated certificate of incorporation and amended and restated by-laws also provides that, subject to any
special rights of the holders of any series of preferred stock and except as otherwise required by law, special meetings of the stockholders can
only be called by the chairman or vice chairman of the board or the chief executive officer, or pursuant to a resolution adopted by a majority
of the board of directors or, until the occurrence of the 40% Triggering Event, at the request of the General Atlantic Equityholders. Except as
described above, stockholders are not permitted to call a special meeting or to require the board of directors to call a special meeting.
Advance Notice Procedures. Our amended and restated by-laws establish an advance notice procedure for stockholder proposals to be
brought before an annual meeting of our stockholders, including proposed nominations of persons for election to the board of directors.
Stockholders at an annual meeting will only be able to consider proposals or nominations specified in the notice of meeting or brought before
the meeting by or at the direction of the board of directors or by a stockholder who was a stockholder of record on the record date for the
meeting, who is entitled to vote at the meeting and who has given our Secretary timely written notice, in proper form, of the stockholder’s
intention to bring that business before the meeting. Although the amended and restated by-laws do not give our board of directors the power
to approve or disapprove stockholder nominations of candidates or proposals regarding other business to be conducted at a special or annual
meeting, the amended and restated by-laws may have the effect of precluding the conduct of certain business at a meeting if the proper
procedures are not followed or may discourage or deter a potential acquirer from conducting a solicitation of proxies to elect its own slate of
directors or otherwise attempting to obtain control of our Company.
Super-Majority Approval Requirements. The Delaware General Corporation Law generally provides that the affirmative vote of the holders
of a majority of the total voting power of the shares entitled to vote on any matter is required to amend a corporation’s certificate of
incorporation or amended and restated by-laws, unless either a corporation’s certificate of incorporation or by-laws require a greater
percentage. Our
-3-
amended and restated certificate of incorporation and amended and restated by-laws provides that, following the occurrence of the 40%
Triggering Event, the affirmative vote of holders of 66
2⁄3
% of the total voting power of our outstanding common stock eligible to vote in the
election of directors, voting together as a single class, will be required to amend, alter, change or repeal specified provisions, including those
relating to the classified board, actions by written consent of stockholders, calling of special meetings of stockholders and amendment of our
amended and restated certificate of incorporation and amended and restated by-laws. This requirement of a super-majority vote to approve
amendments to our amended and restated certificate of incorporation and amended and restated by-laws could enable a minority of our
stockholders to exercise veto power over any such amendments.
Authorized but Unissued Shares. Our authorized but unissued shares of common stock and preferred stock will be available for future
issuance without stockholder approval, subject to any limitations imposed by listing standards of the Exchange. These additional shares may
be utilized for a variety of corporate purposes, including future public offerings to raise additional capital, corporate acquisitions and
employee benefit plans. The existence of authorized but unissued shares of common stock and preferred stock could render more difficult or
discourage an attempt to obtain control of a majority of our common stock by means of a proxy contest, tender offer, merger or otherwise.
Business Combinations with Interested Stockholders. Our amended and restated certificate of incorporation provides that we are not subject
to Section 203 of the Delaware General Corporation Law, an antitakeover law. In general, Section 203 prohibits a publicly held Delaware
corporation from engaging in a business combination, such as a merger, with a person or group owning 15% or more of the corporation’s
voting stock for a period of three years following the date the person became an interested stockholder, unless (with certain exceptions) the
business combination or the transaction in which the person became an interested stockholder is approved in a prescribed manner.
Accordingly, we are not subject to any anti-takeover effects of Section 203. Nevertheless, our amended and restated certificate of
incorporation contains provisions that have the same effect as Section 203, except that they provide that the General Atlantic Equityholders,
their respective affiliates and successors and their transferees are not deemed to be “interested stockholders,” regardless of the percentage of
our voting stock owned by them, and accordingly are not subject to such restrictions.
Forum Selection
Our amended and restated certificate of incorporation provides that unless we consent to the selection of an alternative forum, the Court of
Chancery of the State of Delaware shall, to the fullest extent permitted by law, be the sole and exclusive forum for any (i) derivative action or
proceeding brought on behalf of us, (ii) action asserting a claim of breach of a fiduciary duty owed by any of our directors, officers,
employees or stockholders to us or our stockholders, creditors, or other constituents, (iii) action asserting a claim arising out of or relating to
any provision of the Delaware General Corporation Law or our amended and restated certificate of incorporation or our amended and restated
by-laws (as either may be amended and/or restated from time to time), or (iv) action asserting a claim against us or any of our directors or
officers that is governed by the internal affairs doctrine; provided, that, if the Court of Chancery of the State of Delaware does not have
jurisdiction, such action may be brought in another state court sitting in the State of Delaware, or if no state court of the State of Delaware
has jurisdiction, the federal district court for the District of Delaware, unless we consent in writing to the selection of an alternative forum.
Additionally, our amended and restated certificate of incorporation states that the foregoing provision will not apply to claims arising under
the Securities Act of 1933, as amended, and the Exchange Act of 1934, as amended, or other federal securities laws for which there is
exclusive federal or concurrent federal and state jurisdiction. Unless we consent in writing to the selection of an alternative forum, the federal
district courts of the United States of America shall be the exclusive forum for the resolution of any complaint asserting a cause of action
arising under the Securities Act, the Exchange Act
-4-

or such other federal securities law. The exclusive forum provisions may limit a stockholder’s ability to bring a claim in a judicial forum that
it finds favorable for disputes with us or any of our directors, officers or stockholders, which may discourage lawsuits with respect to such
claims. Our stockholders are not deemed to have waived our compliance with the federal securities laws and the rules and regulations
thereunder as a result of our exclusive forum provisions.
Transfer Agent and Registrar
The transfer agent and registrar for our Class A common stock is Computershare Trust Company, N.A.
-5-
EXHIBIT 10.14
January 17, 2022
Jennifer Vanderveldt
c/o Jeffrey M. Sone, Esq.
Jackson Walker L.L.P.
2323 Ross Avenue, Ste 600
Dallas, Texas 75201
Via Electronic Mail: jsone@jw.com
Re: Separation of Employment and General Release – Confidential
Dear Jen:
The purpose of this Separation Agreement (the “Agreement”) is to memorialize our mutual understanding of your
separation of employment with EWC Ventures, LLC and all of its affiliates (“EWC” or “we”). You and EWC are sometimes
hereinafter referred to as the “Parties.”
Reference is made the Employment Agreement between you and EWC, dated effective as of November 4, 2020
(“Employment Agreement”).
1. Separation of Employment. Your employment with EWC ended on January 12, 2020 (the “Date of
Separation”). We will pay to you, less all applicable withholdings, in accordance with our standard payroll processing procedures
(unless earlier payment is required by law), by direct deposit to the account we have for you on file, your earned but unpaid base
salary through the Date of Separation. In addition, we will pay to you any remaining accrued and unused PTO as of the Date of
Separation and any outstanding reasonable business expenses previously submitted but not yet reimbursed. These additional
amounts are typically paid along with your final paycheck (unless earlier payment is required by law). Your participation in any
EWC medical, dental, vision coverage will remain in effect through the last day of the month of the Date of Separation. Any other
applicable benefit plan in which you participate will effectively terminate as of the Date of Separation. You will receive COBRA
information and forms separately from our COBRA administrator.
2. Severance Payment. Consistent with the Employment Agreement, and subject to the provisions of the general
release set forth in paragraph 6 of this Agreement (the “General Release”), EWC shall continue to pay you a base salary of
$400,000 less all applicable withholdings for a twelve (12) month period after your Date of Separation. The Severance Payment
will be paid to you in equal bi-weekly installments starting on the first payroll date following the Date of Separation.
3. Equity. You were granted Class B units in EWC Ventures, LLC (“EWC Ventures”) pursuant to a Class B Unit
Agreement dated December 7, 2020 (as amended to date, the “Class B Agreement”). Prior to the consummation of the initial
public offering (“IPO”) of European Wax Center, Inc. (“EWCZ”), all of the outstanding equity interests of EWC Ventures,
including its and your Class B Units, were reclassified into common units, based on a hypothetical liquidation of EWC Ventures at
the IPO price per share (the “Reorganization”). As referenced in the Reclassification of Class B Units agreement dated effective
August 5, 2021, you received 241,841 common units, which remained subject to certain vesting time periods, conditions and other
terms. As of the Date of Separation, you have vested as to zero (0) common units pursuant to the Class
Jennifer Vanderveldt
January 17, 2021
Page 2
B Agreement, and the Company hereby agrees to accelerate the vesting of75,000 common units of EWC Ventures in
acknowledgment of your contributions to the Company. All other unvested common units of EWC Ventures granted shall be
immediately cancelled and forfeited without consideration as of the date hereof. Additionally, all other equity granted to you by
EWCZ pursuant to and under its 2021 Omnibus Incentive Plan are hereby automatically and immediately forfeited, cancelled,
terminated and have reverted to EWCZ without payment of consideration therefore, as of the date hereof.
4. 2021 Annual Bonus. You will receive the amount of any performance bonus for 2021, based on bonus
plan targets for performance in 2021, on the same date that the bonus is paid to other executive level employees.
5. Entitlement to Payment. Please understand that, but for your execution of this Agreement and provision of the
General Release below, you would not otherwise be entitled to the benefits described in Paragraphs 2, 3 and 4. Please also
understand that our request for you to execute and deliver this Agreement is consistent with our standard practices and is not
intended, and shall not be construed, as an admission that we or any other Releasee (as defined below) has violated any federal,
state or local law (statutory or decisional), ordinance or regulation, breached any contract or committed any wrongdoing
whatsoever against you or otherwise.
Without limiting the generality or force or effect of the General Release provided below, it is explicitly agreed,
understood and intended that your final base salary payment, any outstanding reimbursement of expenses, any payment of
unused PTO or vacation time, the consideration paid pursuant to this Agreement is hereby deemed to satisfy all claims for
back pay, front pay, minimum wages, overtime compensation, bonus payments, commissions, benefits or any other
compensation or wages of any kind from any EWC entity (or the value thereof) (under any applicable statute, at common
law, or otherwise). Except as described herein, by signing below, you acknowledge and affirm that you have been paid any
and all amounts owed to you by EWC or any other EWC entity including, but not limited to, any unpaid compensation or
other applicable benefits to which you may be entitled.
6. General Release. On your own behalf and on behalf of your heirs, executors, beneficiaries, creditors,
representatives, administrators, trustees, agents and any other applicable legal representative, you hereby fully and finally release,
acquit and forever discharge, to the fullest extent permitted by applicable law, EWCZ, General Atlantic Service Company, LP,
General Atlantic (EWC) Collections, LP, EWC (and, as applicable, their respective parents, subsidiaries, affiliates, predecessors,
successors and any other entity related to any of them and all of their past, present and future equity holders, directors, officers,
managers, partners, employees, creditors, representatives, administrators, insurers, agents and any other person or entity acting by,
through or for any of them – all of the foregoing, collectively, “Releasees”) from any and all claims, actions, obligations, demands,
damages, costs, expenses, compensation or other relief of any type to date, known or unknown, suspected or unsuspected, arising
out of anything to do with your employment or the end of your employment with EWC. Without limiting the generality of the
foregoing, this means you waive and give up all claims for:
• violations or alleged violations under any federal, state, or local employment law, including but not limited to the
Age Discrimination in Employment Act (ADEA), Title VII of the Civil Rights Act of 1964, Americans with
Disabilities Act, the Equal Pay Act, the Lilly Ledbetter Fair Pay Act of 2009, the Fair Labor Standards Act, the
Family and Medical Leave Act, the Employee
Jennifer Vanderveldt
January 17, 2021
Page 3
Retirement Income Security Act (ERISA), the Civil Rights Act of 1991, Section 1981 of U.S.C. Title 42, the Fair
Credit Reporting Act (FCRA), the Worker Adjustment and Retraining Notification (WARN) Act, the National
Labor Relations Act (NLRA), the Uniform Services Employment and Reemployment Rights Act, the Genetic
Information Nondiscrimination Act, the Immigration Reform and Control Act (IRCA), the Families First
Coronavirus Response Act (FFCRA), the Coronavirus Aid, Relief, and Economic Security Act (CARES) any
claims arising under the Texas Labor Code including the Texas Payday Act, the Texas Anti-Retaliation Act,
Chapter 21 of the Texas Labor Code, the Texas Whistleblower Act, and any other state or local law that may be
legally waived;
• any pay/compensation/benefits including back pay, front pay, bonuses, commissions, equity, expenses,
incentives, insurance, paid/unpaid leave/time off, profit sharing, salary, overtime or separation pay/benefits;
• compensatory/emotional/distress damages; punitive or liquidated damages, attorney fees, costs, interest or
penalties;
• any violation of express or implied employment contracts, covenants, promises or duties, intellectual property or
other proprietary rights;
• unlawful or tortious conduct such as assault or battery; background check violations; defamation; detrimental
reliance; fiduciary breach; fraud; indemnification; intentional or negligent infliction of emotional distress;
interference with contractual or other legal rights; invasion of privacy; loss of consortium; misrepresentation;
negligence (including negligent hiring, retention or supervision); personal injury; promissory estoppel; public
policy violation; retaliatory discharge; safety violations; posting or records-related violations; wrongful discharge;
or other federal, state or local statutory or common law matters;
• discrimination based on age, benefit entitlement, citizenship, color, concerted activity, disability, ethnicity,
gender, genetic information, immigration status, income source, jury duty, leave rights, military status, national
origin, parental status, protected off-duty conduct, race, religion, retaliation, sexual orientation, union activity,
veteran status, whistleblower activity (including Sarbanes-Oxley, Dodd-Frank and False Claims Act claims),
other legally protected status or activity; or any allegation that payment under this Agreement was affected by
any such discrimination; and any participation in any class, collective, or representative action against EWC or
any other Releasee.
This General Release excludes: claims arising after the Effective Date, including claims for breach of this
Agreement; any coverage or protections (including, without limitation, indemnification provisions) under our health or other
benefit plans governed by the Employee Retirement Income Security Act of 1974, as amended (with regard to vested
benefits), liability insurance policies or under the provisions of our articles of organization, limited liability company
operating agreements or comparable organizational documents or indemnification agreements for which you may be eligible
or party to (according to the terms and conditions of the applicable insurance contracts, plans, coverage documents or
indemnification agreements); and claims that cannot be waived or released by applicable law, such as for unemployment or
worker’s compensation
Jennifer Vanderveldt
January 17, 2021
Page 4
benefits Neither the General Release nor anything else in this Agreement limits your right to file a charge with any
administrative agency (such as the U.S. Equal Employment Opportunity Commission or a state fair employment practices
agency), communicate directly with or provide information to an agency, or otherwise participate in an agency proceeding;
give legislative testimony at the state legislature’s request, or testify in court pursuant to subpoena or court order; or
communicate with law enforcement or your attorney. You nonetheless give up all rights to any money or other individual
relief based on any agency or judicial decision, including class or collective action rulings.
For the purpose of implementing a full and complete release and discharge of the Releasees, you expressly
acknowledge and agree that the General Release is intended to include in its effect, without limitation, all claims which you
may have relating to any EWC and any and all Releasees entity as of the Effective Date, whether you are aware, or
reasonably should be aware, of the claims or not at the time of execution hereof, and that the General Release contemplates
the extinguishment of any and all such claims or actions. You further affirm that you have not filed nor made any claims,
charges, complaints or actions of any type, whether legal, equitable or administrative, against any Releasee, and that no other
such claims, charges, complaints or actions are currently pending that name, or are based on any claims subject to the
General Release and which involve, in any way, any Releasee. You further affirm that you have no known workplace injuries
or occupational diseases and have been provided and/or have not been denied any leave requested under the Family and
Medical Leave Act. By signing below, you further certify that no individual or entity interfered with your ability to report
within EWC possible violations of any law.
Without in any way limiting the generality of the foregoing General Release, by signing below, you covenant not to
sue or to assert, prosecute or maintain, directly or indirectly, in any form, any claim or cause of action against any Releasee
with respect to any matter, cause, omission, act or thing whatsoever; occurring in whole or in part on or at any time prior to
the Date of Separation , and which is subject to such General Release provided for in this Paragraph 6. Despite this promise
not to sue, you may file suit to enforce this Agreement or to challenge its validity under the ADEA. If you, however, sue a
Releasee in violation of this Agreement, you shall be required to pay that Releasee’s reasonable attorney fees and other
litigation costs incurred in defending against your suit. In that event and should you violate any of the other terms of this
Agreement, and without limiting our other rights and remedies in the event of such a violation, we shall be excused from any
remaining obligations that exist solely because of this Agreement, and we shall have the right to claw back all, or any portion
of the Consideration paid to you pursuant to this Agreement.
7. Confidentiality/Covenants. Please understand that we expect that you will maintain the existence of and the
terms and conditions of this Agreement in strict confidence, and therefore, you agree not to disclose its terms or any of our
discussions related to these terms to any other person or entity, except: (i) as may be required by law; and (ii) that you may disclose
the existence, terms, and conditions of this Agreement to your attorney, immediate family members, and/or accountant, and any
governmental authority with a need to know, provided that you make the person to whom disclosure is made aware of the
confidentiality provisions of this Agreement and such person agrees to keep these terms fully confidential. EWC may disclose
these terms as we may determine to be reasonably necessary for business purposes, including to any state unemployment agency.
For the avoidance of doubt, nothing in this Agreement interferes with your obligation to notify any subsequent employer of your
ongoing restrictive covenant obligations pursuant to this Agreement and the Confidentiality; Non- Interference and Proprietary
Rights Agreement that you signed during the course of your employment, a true and correct copy of which is attached hereto as
Exhibit A, (the “Confidentiality Agreement”) or your right to
Jennifer Vanderveldt
January 17, 2021
Page 5
disclose applicable terms of this Agreement to any state unemployment agency. However, you understand that any Releasee
entity may respond adequately and truthfully to inquiries from any governmental agency.
In addition, all confidential or proprietary type information that you may have received or otherwise had access to
regarding EWC and its respective businesses (you acknowledge that as between you and EWC, all of which is owned by
EWC) will continue to be treated by you in full confidence pursuant to the Confidentiality Agreement. You further
acknowledge and agree that the covenants set forth in the Confidentiality Agreement will remain ongoing per the terms
therein except for those covenants that are changed by this Agreement and as set forth herein, and your signature on this
Agreement re-affirms your obligation to comply with the unchanged covenants and affirms your obligation to comply with
the changed covenants, including the covenants of non-solicitation (as qualified below), non-interference, and non-
disparagement. EWC agrees to qualify the covenants of non-solicitation as set forth in the Confidentiality Agreement as
follows: (i) as the covenant relates to any person or entity that is not an employee of any EWC entity (e.g., franchisees,
vendors, suppliers, investors, financial resources and contractors), your covenant with respect to soliciting for employment or
interfering with the business relationship with EWC shall be limited to those third parties with whom you had contact in
connection with your employment; and (ii) the covenant restricting solicitations for employment is not intended to interfere
with untargeted general or public solicitations. These changes/qualifications and your affirmation and re-affirmation of
covenants result in additional consideration for entering into this Agreement, and accordingly, your failure to comply with
each of those covenants and qualified covenants will constitute a material breach of this Agreement.
Without limiting the foregoing, you will immediately return to us, or at our request, destroy and certify such
destruction (with respect to information) (i) all copies and manifestations of EWC information that you possess and/or to
which you have access, including any passwords or log-in information to any EWC network, (ii) all documents, other
materials and equipment provided by any EWC entity to you in connection with your employment, such as access cards,
identification cards, employer credit cards, computers, laptops, laptop chargers, cell/smart phones, manuals, removable
information storage devices and other EWC devices, hardware and technology in your possession and (iii) any other
documents and materials that you have prepared in connection with your employment that you possess and/or to which you
have access.
For the avoidance of doubt, you are currently bound by non-competition restrictive covenants that could limit your
ability to work with or for a European Wax Center franchisee or area representative. In addition, as you are aware, our
corporate employment policies provide that we generally do not award franchises to current or former associates, or their
family members. However, notwithstanding the foregoing, we will consider any requests from you in good faith to join our
franchise network as an owner, employee, consultant or otherwise, in each case taking into account the facts and
circumstances of the request.
8. Indemnification. As a former officer of EWC, you will remain entitled to all indemnification rights and
benefits provided from time to time to other and former officers of EWC. As of the date of this Agreement, EWC has no intention
to eliminate or reduce any indemnification rights and benefits currently provided to any former officers of EWC.
9. Non-Disparagement. The Parties agree that they will not at any time make, publish or communicate to any
person or entity or in any public forum any defamatory or disparaging remarks, comments
Jennifer Vanderveldt
January 17, 2021
Page 6
or statements concerning the other, and in the case or EWC, its businesses, or any of its employees, managers, officers, agents,
contractors, representatives and existing and prospective and former guests, customers, franchisees, area representatives, vendors,
suppliers, distributors, investors, licensees, regional developers, financial resources or any other associated third party with EWC,
or their respective businesses. The previous sentence does not, in any way, restrict or impede either of the Parties from exercising
protected rights to the extent that such rights cannot be waived by agreement, or from complying with any applicable law or
regulation or a valid order of a court of competent jurisdiction or an authorized government agency, provided that such compliance
does not exceed that required by the law, regulation or order. The Parties agree to provide written notice of any such order to the
other, an in the case of EWC to an authorized officer of EWC.
10. Effective Date; Conditions Precedent. This Agreement and the General Release will become effective on the
eighth (8th) day following the delivery of a copy of the fully signed Agreement to us (the “Effective Date”). You may at any time
prior to the Effective Date revoke your release of your ADEA claims in this Agreement by giving notice in writing of such
revocation as set forth in this Agreement.
11. Miscellaneous. Without limiting our rights to disclose the terms of this Agreement, this Agreement may be used
as evidence only in a subsequent proceeding in which any of the parties allege a breach of this Agreement. All releases,
representations, warranties, covenants and other agreements contained herein will survive the execution and shall continue in full
force and effect, even after the full and final payment of the consideration provided pursuant to this Agreement. Except to the
extent a prohibition is not permitted by applicable law, you may not assign your rights, or any consideration provided to you under
this Agreement or otherwise and/or delegate your duties or obligations, unless otherwise explicitly permitted by written agreement,
and any purported and unpermitted assignment and/or delegation shall be void and without effect. Subject in all respects to the
foregoing sentence, the provisions of this Agreement shall be binding upon and inure to the benefit of you and us, and your and our
respective heirs, executors, beneficiaries, creditors, administrators, trustees, representatives, agents, successors and assigns. Any
waiver of a breach of this Agreement shall not operate as a waiver of any other breach. This Agreement shall be construed and
governed under the laws of the State of Texas and venue shall be in Collin County, Texas. If any litigation is initiated in
connection with this Agreement, the prevailing party shall be entitled to any award of reasonable attorneys’ fees and costs. In no
event shall the terms of this Agreement be construed against us on the basis that we, or our counsel, drafted this Agreement. This
Agreement and incorporated portions of employment documents referenced in this Agreement represent the entire agreement
between you and us with respect to the subject matter of this Agreement, and supersedes all other writings, negotiations,
understandings and representations (if any) made by and between you and EWC and/or Releasees. The provisions of this
Agreement may not be amended, supplemented, waived or changed orally, but only by a writing signed by both you and us. This
Agreement may be executed in one or more counterparts, each of which shall be deemed an original, but all of which taken
together shall constitute one and the same instrument. Confirmation of execution by electronic transmission of a facsimile or .pdf
signature page shall be binding on the parties to this Agreement.
12. Validity of Agreement. If any provision of this Agreement is or becomes illegal, invalid or unenforceable
in any respect under the law of any applicable jurisdiction, neither the legality, validity or enforceability of the remaining
provisions of this Agreement nor the legality, validity or enforceability of such provision under the law of any other
jurisdiction will in any way be affected or impaired thereby. If any provision of this Agreement may be construed in two or
more ways, one of which would render the provision invalid or otherwise voidable or unenforceable and another of which
would render the provision valid and enforceable, such provision will have the meaning which renders it valid and
enforceable.
Jennifer Vanderveldt
January 17, 2021
Page 7
Upon any finding by a court of competent jurisdiction that the General Release or covenants provided for by this
Agreement are illegal, void or unenforceable, you agree to execute a release, waiver and/or covenant of comparable scope
that is legal and enforceable.
13. ADEA Waiver and Advice of Counsel. You hereby acknowledge that you knowingly and voluntarily enter
into this Agreement with the purpose of waiving and releasing any claims you may have under the Age Discrimination in
Employment Act of 1967 (“ADEA”), and as such, you acknowledge and agree that:
• THIS AGREEMENT IS WRITTEN IN A MANNER WHICH YOU FULLY UNDERSTAND;
• YOU HAVE BEEN ADVISED IN WRITING TO CONSULT WITH AN ATTORNEY BEFORE SIGNING
THIS AGREEMENT, AND IN FACT, HAVE HAD AN OPPORTUNITY TO DO SO;
• YOU SPECIFICALLY WAIVE ANY RIGHTS OR CLAIMS ARISING UNDER THE ADEA, AND THIS
AGREEMENT DOES NOT WAIVE RIGHTS OR CLAIMS UNDER THE ADEA THAT MAY ARISE AFTER
THE DATE THIS AGREEMENT IS EXECUTED;
• THE RIGHTS AND CLAIMS WAIVED IN THIS AGREEMENT ARE IN EXCHANGE FOR
CONSIDERATION OVER AND ABOVE ANYTHING OF VALUE TO WHICH YOU ARE ALREADY
ENTITLED;
• YOU HAVE BEEN AFFORDED THE OPPORTUNITY TO CONSIDER THE TERMS OF THIS
AGREEMENT FOR TWENTY-ONE (21) CALENDAR DAYS PRIOR TO ITS EXECUTION OR HAVE
OTHERWISE WAIVED SUCH 21-CALENDAR DAY PERIOD. YOU AGREE THAT ANY
MODIFICATIONS, MATERIAL OR OTHERWISE, MADE TO THIS AGREEMENT DO NOT RESTART OR
AFFECT IN ANY MANNER THE ORIGINAL TWENTY-ONE (21) CALENDAR DAY CONSIDERATION
PERIOD. TO THE EXTENT THAT YOU HAVE ELECTED TO ENTER INTO THIS AGREEMENT PRIOR
TO THE END OF THE CONSIDERATION PERIOD, YOU HAVE DONE SO VOLUNTARILY, AND HAVE
KNOWINGLY WAIVED THE REMAINDER OF SUCH TWENTY-ONE (21) CALENDAR DAY
CONSIDERATION PERIOD;
• YOU HAVE A PERIOD OF SEVEN CALENDAR (7) DAYS WITHIN WHICH YOU CAN REVOKE THIS
AGREEMENT AS IT RELATES TO ANY RIGHTS OR CLAIMS UNDER THE ADEA; and
• IF YOU ELECT TO REVOKE YOUR WAIVER OF ANY RIGHTS OR CLAIMS UNDER THE ADEA,
REVOCATION SHALL BE IN WRITING AND TIMELY DELIVERED TO EWC CORPORATE, BY EMAIL
[REMAINDER OF PAGE INTENTIONALLY LEFT BLANK]
Jennifer Vanderveldt
January 17, 2021
Page 8
Please confirm that this Agreement accurately sets forth our agreement by signing in the space provided below and
returning a copy of it to Aura De Biase via e-mail at [email protected]. If this Agreement is not fully executed and
so returned on or before February 7, 2022, this Agreement and the promises contained herein will automatically be
deemed null and void ab initio.
By signing below, you acknowledge that the consideration contemplated by this Agreement is sufficient for each of
the covenants, releases and agreements set forth herein.
EWC Ventures, LLC
By: /s/ GAVIN O’CONNOR
GAVIN O’CONNOR, CHIEF LEGAL OFFICER CHIEF
HUMAN RELATIONS OFFICER AND CORPORATE
SECRETARY
AGREED AND ACCEPTED:
I ACKNOWLEDGE THAT I HAVE READ THIS AGREEMENT IN ITS ENTIRETY, INCLUDING THE GENERAL
RELEASE SET FORTH IN PARAGRAPH 6; THAT I FULLY UNDERSTAND ALL OF ITS TERMS AND THEIR
SIGNIFICANCE; THAT I HAVE SIGNED IT VOLUNTARILY AND OF MY OWN FREE WILL; AND THAT I INTEND
TO ABIDE BY ITS PROVISIONS WITHOUT EXCEPTION.
I FURTHER ACKNOWLEDGE THAT NEITHER EWC NOR ANY REPRESENTATIVE OF ANY EWC ENTITY HAS
MADE ANY REPRESENTATION OR PROMISE TO ME OTHER THAN AS SET FORTH HEREIN.
/s/ JENNIFER VANDERVELDT
Jennifer Vanderveldt DATE: January 17, 2022
Jennifer Vanderveldt
January 17, 2021
Page 9
EXHIBIT A
CONFIDENTIALITY; NON‐INTERFERENCE AND
PROPRIETARY RIGHTS AGREEMENT
I, , enter into this Confidentiality, Non‐Interference and Proprietary Rights Agreement (this “Agreement”) with EWC Corporate,
LLC, a Florida limited liability company (“EWC”), on behalf of itself and its affiliated entities (collectively referred to as the
“EWC Group”, with EWC and the EWC Group being collectively referred to in this Agreement, as applicable, as “European Wax
Center”), effective as of the date I began/begin working with European Wax Center. My consideration for entering into this
Agreement is my employment or continued employment with European Wax Center, and the compensation that I receive during my
employment with European Wax Center, which I acknowledge to be good and valuable consideration for my obligations pursuant to
this Agreement.
1. Confidential Information.
A. I expressly acknowledge that the performance of my responsibilities may necessitate, and European Wax
Center may provide, access to or the disclosure of Confidential Information (as hereinafter defined) to me and that my
responsibilities shall include the development of goodwill of European Wax Center through my contacts with European Wax
Center guests, franchisees, area representatives, vendors, suppliers, lenders and other third party relationships.
B. I further acknowledge that European Wax Center has trade, business and financial secrets and other
confidential and proprietary information (collectively, the “Confidential Information”) that are special and unique assets of
European Wax Center, created and/or obtained by European Wax Center at time and/or expense, from which European Wax
Center may or does derive independent economic value from the Confidential Information not being generally known to third
parties. I understand and acknowledge that this Confidential Information and European Wax Center’s ability to preserve it for
the exclusive knowledge and use of European Wax Center is of great competitive importance and competitive value to European
Wax Center, and that improper use of disclosure of the Confidential Information by me will cause irreparable harm to European
Wax Center, for which remedies at law will not be adequate. As defined herein, the term Confidential Information includes, but
is not limited to, information whether made available to me in writing, electronically or orally and whether or not identified as
confidential, Results (as defined below), internal communications, marketing data, agreements, business plans and strategies,
new product or service offerings, product and service information, marketing information, marketing methods, unpublished
financial information, pricing information and techniques, pending mergers and acquisition transactions, expansion plans,
customer and supplier lists, customer and supplier information, strategies, methods, procedures, processes, contract terms,
contract negotiations, compensation information, structures and plans, formulas, technology, documents, reports, analyses, data,
studies, samples, copyright, trademark and patent applications, projections, software, trade secrets, know‐how, and observations,
and other disclosures pertaining to, based on, or containing, directly or indirectly, in whole or in part, any other Confidential
Information, but shall not include (i) information that is in the public domain, other than as a result of my
Jennifer Vanderveldt
January 17, 2021
Page 10
improper disclosure, or (ii) information that I can show by competent proof was generally known by me prior to any
engagement or relationship with European Wax Center and without any duty of confidentiality to European Wax Center,
including, without limitation, the trade knowledge, skill and expertise I have developed as a result of my prior experience.
C. I agree that at all times during my employment with European Wax Center, and at all times following the
termination of such employment, for any reason, I will maintain all Confidential Information in strict confidence
and will only disclose such Confidential Information during my employment to European Wax Center employees and other persons
or entities to whom I reasonably believe that such disclosure of the Confidential Information is necessary and in the best interest of
European Wax Center, and then only to the extent that such European Wax Center employees and other persons authorized by
European Wax Center have a need to know such Confidential Information; provided, however, that I understand that I may disclose
the Confidential Information under certain limited circumstances as follows: (i) as may be required by law or court process;
provided, that I provide European Wax Center reasonable prior notice to allow European Wax Center sufficient time to obtain a
protective order to prevent disclosure of the Confidential Information, or take other appropriate action; (ii) in confidence to a
federal, state, or local government official, either directly or indirectly, or to my legal counsel solely for the limited purpose of
reporting or investigating a suspected violation of law by European Wax Center; (iii) in confidence as part of a complaint or other
legal document filed in a lawsuit or other proceeding; provided, that such filing is made under protective seal; and (iv) if I file a
lawsuit for retaliation by European Wax Center for reporting a suspected violation of law, I may disclose, in confidence, relevant
trade secret information to my legal counsel representing me in such lawsuit, and use such trade secret information in the court
proceedings; provided, that (x) I either directly or through my legal counsel, file any document containing any such trade secret
under protective seal; and (y) I do not disclose the trade secret information, except pursuant to court order or with European Wax
Center’s prior written consent, which such consent may be withheld in European Wax Center’s sole discretion. I understand that
this Agreement does not, in any way, restrict or impede me from exercising protected rights to the extent such rights cannot be
waived by this Agreement. I also understand that European Wax Center reserves the right to pursue all remedies available under
federal, state, or local law for any disclosure of Confidential Information (including trade secret information) by me which does not
comply with this Section 1(C).
D. I agree to take all steps reasonably necessary and/or requested by European Wax Center to ensure that the
Confidential Information is kept confidential. I will comply with all applicable published and communicated policies,
procedures and practices that European Wax Center has established and may establish from time to time with regard to the
Confidential Information. In addition, I will not, directly or indirectly (i) access, use, copy, reproduce, reverse engineer or permit
access, use, reproduction or reverse engineering of any part of the Confidential Information except as necessary within the
authorized scope of my employment with European Wax Center, (ii) remove and/or permit removal from European Wax Center
premises, any Confidential Information, except as necessary within the authorized scope of my employment with European Wax
Center or (iii) divulge, disclose, distribute or communicate to any person or organization
Jennifer Vanderveldt
January 17, 2021
Page 11
outside of European Wax Center any of the Confidential Information without the prior written consent of European Wax Center
(except as may otherwise be permitted pursuant to this Agreement), and then such disclosure will be made only within the limits
and to the extent of such consent.
E. I acknowledge and agree that the Confidential Information, and all copies and manifestations of the
Confidential Information, are, and shall remain at all times, the exclusive property of European Wax Center. I further agree not
to use any Confidential Information for the benefit of any person or entity other than European Wax Center.
F. I will, immediately upon European Wax Center’s request, and immediately upon termination of my
employment with European Wax Center, for any reason or for no reason (and regardless of who is the terminating party and
without the need for any such request), return to European Wax Center: (i) all copies and manifestations of Confidential
Information that I may have or have access to; (ii) all documents, other materials and equipment provided by European Wax
Center or otherwise obtained by me during and in connection with my employment with European Wax Center; and (iii) all
documents and materials that I have prepared during my employment with European Wax Center.
G. I have not and will not, at any time, improperly use or disclose any proprietary information or trade secrets of
any former or current employer or other person or entity with which I have any agreement or duty to keep in confidence
information acquired by me, if any. I will not bring onto any European Wax Center premises any unpublished document or
proprietary information belonging to such employer, person or entity unless consented to in writing by European Wax Center
and such employer, person or entity.
2.Surrender of Materials Upon Termination. Upon any termination of my employment, regardless of the reason and who is
the terminating party, in addition to my obligations pursuant to Section 1(F) above, I will promptly (and in any event within ten
(10) days) return to European Wax Center: (A) any other properties of European Wax Center which are in my possession,
custody or control, including any applicable documents, other materials and equipment provided by European Wax Center, such
as access cards, identification cards, employer credit cards, computers, cell/smart phones, manuals and removable information
storage devices; and (B) all documents and materials that I have prepared in connection with my duties. Without limiting the
foregoing, I further agree, to the extent I possess any files, data, or information relating in any way to European Wax Center on
any non‐European Wax Center entity devices, networks, personal computers, storage locations or media in my possession,
custody or control that are not being returned to European Wax Center, I will delete or destroy those files, data, or information
(and will retain no copies in any form).
3. Work Product.
A. I acknowledge and agree that all work product of any nature whatsoever, that is created, prepared, produced,
authored, edited, amended, conceived or reduced to practice by me individually or jointly with others during the period of my
employment with European Wax Center and made within the scope of my employment (regardless of when or where prepared or
whose equipment or other resources are used in preparing the same), including, without limitation, all data, information,
analyses, materials,

Jennifer Vanderveldt
January 17, 2021
Page 12
documentation, reports, inventions, improvements, modifications or works of authorship, generated, created, conceived, derived
or resulting from the performance of my duties and any works in progress, and all printed, physical and electronic copies, all
improvements, rights and claims related to the foregoing, and other tangible embodiments thereof, whether or not now or
hereafter known, existing, contemplated, recognized or developed (collectively, “Results”), as well as any and all rights in and to
copyrights, trade secrets, trademarks (and related goodwill), mask works, patents and other intellectual property rights therein
arising in any jurisdiction throughout the world and all related rights of priority under international conventions with respect
thereto, including all pending and future applications and registrations therefor, and continuations, divisions, continuations‐in‐
part, reissues, extensions and renewals thereof (collectively, “Intellectual Property Rights”), shall be, to the extent permitted by
law and as applicable, deemed “works for hire” or “works made for hire,” within the meaning of the United States Copyright
Act of 1976, for the benefit of European Wax Center. European Wax Center shall be deemed the sole owner throughout the
universe of any and all such Results and all Intellectual Property Rights related thereto, with the right to use the same in
perpetuity in any manner European Wax Center, in its sole and absolute discretion, determines, without any further payment or
compensation to me whatsoever.
B. If, for any reason, any such Results shall not be legally deemed “works for hire” or “works made for hire,”
and/or there are any rights which do not accrue to European Wax Center pursuant to this Section 3, then I hereby irrevocably
assign to European Wax Center any and all of my right, title and interest in such Results and the Intellectual Property Rights
therein, and European Wax Center shall have the right to use the same in perpetuity throughout the universe in any manner it
determines, in its sole and absolute discretion, without any further payment or compensation to me whatsoever. To the extent I
have any rights in the Results or any other Intellectual Property Rights that cannot be assigned in the manner described above, I
hereby unconditionally and irrevocably waive the enforcement of such rights. The rights provided in this Section 3 are in
addition to, and shall not be deemed
to limit, restrict, or constitute any waiver by European Wax Center of, any rights of ownership to which European Wax Center may be
entitled by operation of law.
C. I will, from time to time, as may be requested by European Wax Center, do any and all things which European
Wax Center may deem useful, necessary or desirable to establish or document European Wax Center’s exclusive ownership of
any and all rights in any Results and/or the Intellectual Property Rights therein. I hereby grant European Wax Center power of
attorney to do all such things on my behalf and in my name and to do all other lawfully permitted acts to establish or document
European Wax Center's exclusive ownership of any and all rights in any Results and Intellectual Property Rights therein, to the
fullest extent permitted by law, if I do not promptly cooperate with European Wax Center's request (without limiting the rights
European Wax Center may have in such circumstances by operation of law). This power of attorney is coupled with an interest
and shall not be affected by my subsequent incapacity.
D. I have listed in Exhibit A attached hereto a complete list of all inventions that I have, alone or jointly with
others, conceived, developed, and reduced to practice prior to the commencement of my employment with European Wax
Center, that I consider to be my property or the property of third parties
Jennifer Vanderveldt
January 17, 2021
Page 13
that I wish to have excluded from the scope of this Agreement. Other than those items identified on Exhibit A, I represent,
warrant and covenant that there are no original works of authorship, developments, concepts, improvements, designs,
discoveries, ideas, trademarks, service marks, or trade secrets, or inventions which were made or acquired by me prior to my
employment by European Wax Center, which are owned in whole or in part by me, which relate to the European Wax Center’s
business or proposed business, and which are not assigned to European Wax Center under this Agreement.
E. To the extent any copyrights are assigned under this Agreement, I irrevocably waive, to the extent permitted
by applicable law, any and all claims that I may now or hereafter have in any jurisdiction to all rights of paternity, integrity,
disclosure and withdrawal and any other rights that may be known as “moral rights” with respect to all Results and all
Intellectual Property Rights therein.
F. I understand that this Agreement does not, and shall not be construed to, grant me any license or right of any
nature with respect to any Results or Intellectual Property Rights therein or any Confidential Information, materials, software or
other tools made available to me by European Wax Center.
G. I hereby consent to any and all uses and displays by European Wax Center and its agents, contractors and other
authorized representatives to my name, voice, likeness, image, appearance and biographical information in, on or in connection
with any pictures, photographs, audio and video recordings, digital images, websites, social media pages, television programs
and advertising, other advertising, sales and marketing brochures, books, magazines, other publications, CDs, DVDs, tapes and
all other printed and electronic forms and media throughout the world, at any time during or after the period of my employment
by European Wax Center, for all legitimate business purposes, as determined in European Wax Center’s sole reasonable
discretion (“Permitted Uses”). I hereby forever release European Wax Center and their respective directors, officers, managers,
employees, contractors, representatives and agents from any and all claims, actions, damages, losses, costs, expenses and
liability of any kind, arising under any legal or equitable theory whatsoever at any time during or after the period of my
employment by European Wax Center, in connection with any Permitted Use.
4.Non‐Disparagement. I agree and covenant that I will not at any time make, publish or communicate to any person or entity or
in any public forum any defamatory or disparaging remarks, comments or statements concerning European Wax Center or its
businesses, or any of its employees, managers, officers, agents, contractors, representatives and existing and prospective and
former guests, customers, franchisees, area representatives, vendors, suppliers, distributors, investors, licensees, regional
developers, financial resources or any other associated
third party with European Wax Center, or their respective businesses. The previous sentence does not, in any way, restrict or impede
me from exercising protected rights to the extent that such rights cannot be waived by agreement or from complying with any
applicable law or regulation or a valid order of a court of competent jurisdiction or an authorized government agency, provided that
such compliance does not exceed that required by the law, regulation or order. I shall promptly provide written notice of any such
order to an authorized officer of European Wax Center.
5. Non‐Solicitation; Non‐Interference.
Jennifer Vanderveldt
January 17, 2021
Page 14
A. The term of “Non‐Solicitation” (herein so referred) shall be for a term beginning effective on the
commencement of my employment and continuing until the 12‐month anniversary of the termination of my employment.
B. During the term of Non‐Solicitation, I will not, on my own behalf or on behalf of any other person, encourage,
induce or attempt to induce, any individual that is an employee of European Wax Center or any franchisee, area representative,
vendor, supplier, distributor, investor, licensee, regional developer, financial resource or any other associated third party with
whom I may have had contact in connection with my employment, to leave his or her employment with European Wax Center or
any such other third party, and I will not otherwise (and will cause my family members not to) directly or indirectly hire or
attempt to hire, or contact or solicit with respect to hiring any such employee.
C. During the term of Non‐Solicitation, I will not (and will cause my family members not to) directly or
indirectly, solicit or attempt to solicit any person who is or has been a guest, customer, franchisee, area representative, vendor,
supplier, distributor, investor, licensee, regional developer, financial resource, agent, contractor or any other associated third
party with whom I may have had contact in connection with my employment to alter, limit or cease such person’s business
relationship with European Wax Center.
D. During the term of Non‐Solicitation, I will not in any adverse way interfere in any way with any business
relationship of European Wax Center or its businesses.
E. Should I violate any of the terms of this Section, I understand that the obligation at issue will run from the first
date on which I cease to be in violation of such obligation.
F. I agree to notify any subsequent employer of the restrictive covenants section contained in this Agreement. In
addition, I authorize European Wax Center to provide a copy of the restrictive covenants section of this Agreement to third
parties, including but not limited to, my subsequent, anticipated or possible future employer(s).
6.Independent Covenants. I acknowledge and agree that each of the restrictive covenants contained in this Agreement is
independent of any other provision of this Agreement. The existence of any claim or cause of action that I may have against
European Wax Center will not constitute a defense to the enforcement of any restrictive covenant contained in this Agreement.
7.No Other Conflicting Obligations. I hereby represent, warrant and covenant to European Wax Center that I am not bound,
nor will I become bound, by any contract, agreement, covenant or other obligation that may or does prevent me in any manner
from performing pursuant to this Agreement.
8.At‐Will Employment. I acknowledge that this Agreement does not give me any rights to employment or engagement by
European Wax Center and, unless otherwise provided in another writing, executed by an officer of European Wax Center and
me, my employment at European Wax Center shall be at‐will by both
Jennifer Vanderveldt
January 17, 2021
Page 15
European Wax
Center and me. This means that, unless otherwise provided in another writing, executed by an officer of European Wax Center and
me, I am free to resign at any time, for any or no reason, and, similarly, European Wax Center is free to terminate my employment
at any time, for any or no reason, with or without notice. My employment will continue in effect, however, until terminated in
writing by either me or European Wax Center.
9.Enforcement Costs and Fees. If any legal proceedings are brought for the enforcement of this Agreement, in addition to any
other relief to which the successful or prevailing party may be entitled, the successful or prevailing party will be entitled to
recover attorneys’ fees, investigative fees, administrative fees billed by such party’s attorneys, court costs and all expenses,
including, without limitation, all fees, taxes, costs and expenses incident to arbitration, appellate, and post‐judgment
proceedings, incurred by the successful or prevailing party in that action or proceeding, whether or not taxable as costs. Solely
for purposes of determining whether I or European Wax Center will be responsible for paying such amounts, I agree that
European Wax Center shall be deemed the prevailing party in any suit, action or legal proceeding in which European Wax
Center proves by a preponderance of evidence that I have either: (A) violated, breached, or threatened to breach this Agreement;
and/or (B) retained any of the property which I am required by this Agreement to return to European Wax Center.
10. Certain Legal Effects of this Agreement.
A. I acknowledge and agree that my agreement to the restrictions set forth in this Agreement are a material
inducement to European Wax Center’s offer of employment to me; is in consideration for European Wax Center’s agreement
hereunder to provide Confidential Information to me; and is in consideration for the compensation and other benefits payable
hereunder to me. I acknowledge that this Agreement is intended to protect European Wax Center’s trade secrets and other
Confidential Information, and that the enforcement of this Agreement by European Wax Center is necessary to ensure the
preservation, protection and continuity of the business, customers and other third party relationships, Confidential Information,
and goodwill of European Wax Center. Due to the proprietary nature of European Wax Center’s business, I acknowledge and
agree that the length and scope of the terms and geographical restrictions contained in this Agreement are fair and reasonable
and not the result of overreaching, duress or coercion of any kind. I further acknowledge and agree that my full, uninhibited and
faithful observance of this Agreement will not cause me any undue hardship, financial or otherwise, and that enforcement of this
Agreement will not impair my ability to obtain employment commensurate with my abilities and on terms fully acceptable to
me, or to otherwise obtain income required for the comfortable support of me and my family, and the satisfaction of the needs of
my creditors.
B. If any provision of this Agreement is contrary to, prohibited by, or deemed invalid under, any applicable law,
rule or regulation, such provision shall be inapplicable and deemed omitted to the extent so contrary, prohibited or invalid, but
the remainder of this Agreement will not be so invalidated, and will be given full force and effect so far as possible.
Furthermore, if any provision of this Agreement may be construed to have more than one meaning, and one meaning would
make the provision invalid or otherwise voidable or unenforceable, while another meaning would make the provision valid and
enforceable, the
Jennifer Vanderveldt
January 17, 2021
Page 16
provision will have the meaning which makes it valid and enforceable.
C. I acknowledge that money damages would be both incalculable and an insufficient remedy for a breach of the
restrictive covenants set forth herein by me and that any such breach could cause European Wax Center irreparable harm.
Accordingly, European Wax Center, in addition to any other remedies it may have, at law or in equity, shall be entitled, without
the requirement of posting of bond or other security, to seek equitable relief, including injunctive relief and specific
performance, in connection with a breach of any of the restrictive covenants contained in this Agreement by me. If, in any legal
proceedings, a court shall refuse to enforce the covenants, then the duration and scope of such unenforceable covenants shall be
deemed to be reduced to the greatest duration and scope which would be enforceable by such court.
11. Miscellaneous.
A. The provisions of this Agreement may not be amended, supplemented, waived or changed orally, but only by a
writing signed by both an authorized representative of EWC Corporate, LLC and me, and making specific reference to this
Agreement.
B. European Wax Center may assign its rights and/or obligations pursuant to this Agreement without my prior
written consent. I understand that I may not assign or delegate my rights and/or obligations under this Agreement.
C. This Agreement will be governed by, and construed and enforced in accordance with, the laws of the State of
Florida without regard for the principles of conflicts of law. I irrevocably and unconditionally (i) agree that any suit, action or
legal proceeding arising out of or relating to this Agreement shall exclusively be brought in the courts of record of the State of
Florida in Broward County (or such alternate jurisdiction where European Wax Center’s principal business offices are then
located), or the court of the United States, Southern District of Florida (or such alternate federal court in the jurisdiction where
European Wax Center’s principal business offices are then located), (ii) consent to the jurisdiction of each such court in any such
suit, action or proceeding, (iii) waive any objection which I may have to the laying of venue of any such suit, action or
proceeding in any of such courts, and
(iv) agree that service of any court paper may be effected on any party in any manner as may be provided under applicable laws or
court rules in said state.
D. The headings contained in this Agreement are for convenience only. The headings are not considered a part of
this Agreement and will not limit or affect in any way the meaning or interpretation of this Agreement.
E. All covenants, agreements, representations and warranties made in this Agreement or otherwise made by me
or European Wax Center in writing pursuant to this Agreement shall survive the execution and delivery of this Agreement and
the termination of my employment with European Wax Center, for any reason or for no reason (and regardless of who is the
terminating party).
F. If European Wax Center ever fails to require, or delays requiring, my performance of any provision of this
Agreement, even if known, such failure or delay will not affect European Wax Center’s right to require performance of that
provision, or to exercise any of its rights, powers or remedies pursuant to
Jennifer Vanderveldt
January 17, 2021
Page 17
this Agreement. Any waiver by European Wax Center of any breach of any provision of this Agreement shall not be construed
as a waiver of any continuing or succeeding breach of such provision, a waiver of the provision itself, or a waiver of any right,
power or remedy under this Agreement.
G. Each remedy provided to either European Wax Center or me pursuant to this Agreement is intended not to be
exclusive of any other remedy available to European Wax Center or me pursuant to this Agreement and shall be in addition to
every other remedy available to European Wax Center or me. No single or partial exercise by either European Wax Center or me
of any right, power or remedy provided pursuant to this Agreement shall disallow or preclude any additional exercise of such
right, power or remedy by such party.
H. This Agreement shall not be construed more strongly against European Wax Center despite European Wax
Center’s responsibility for its preparation.
I. Any notices, requests for consent or other communications to be given to European Wax Center shall be
directed to European Wax Center, Attn: Legal Department, The Village At Gulfstream Park, 600 Silks Run, Suite 2270,
Hallandale Beach, FL 33009, E‐Mail: legal@waxcenter.com.
J. This Agreement represents the entire understanding and agreement between European Wax Center and me
with respect to its subject matter and supersedes all other negotiations, understandings and representations
(if any) made by and between European Wax Center and me regarding the same. Confirmation of execution by electronic
transmission of a facsimile or .pdf signature page shall be binding on the parties to this Agreement.
BY SIGNING BELOW, I ACKNOWLEDGE THAT I HAVE BEEN ADVISED TO CONSULT WITH AN ATTORNEY BEFORE
SIGNING THIS AGREEMENT; AND THAT I HAVE BEEN AFFORDED THE OPPORTUNITY TO CONSIDER THE TERMS
OF THIS AGREEMENT FOR A REASONABLE TIME PRIOR TO MY EXECUTION. I FURTHER ACKNOWLEDGE THAT I
HAVE READ THIS AGREEMENT IN ITS ENTIRETY; THAT I FULLY UNDERSTAND ALL OF ITS TERMS AND THEIR
SIGNIFICANCE; THAT I HAVE SIGNED IT VOLUNTARILY AND OF MY OWN FREE WILL; AND THAT I AGREE TO,
AND INTEND TO ABIDE BY, ITS PROVISIONS WITHOUT EXCEPTION.
Signature
Printed Name
Date
Accepted by EWC Corporate, LLC:
By:
Print Name:

Jennifer Vanderveldt
January 17, 2021
Page 18
Title:
EXHIBIT 23.1
CONSENT OF INDEPENDENT REGISTERED PUBLIC ACCOUNTING FIRM
We consent to the incorporation by reference in Registration Statement No.333-258475 on Form S-8 of our report dated March 15, 2022, relating to the
consolidated financial statements of European Wax Center, Inc. and subsidiaries appearing in this Annual Report on Form 10-K for the year ended
December 25, 2021.
/s/ DELOITTE & TOUCHE LLP
Dallas, TX
March 15, 2022
Exhibit 31.1
CERTIFICATION OF CHIEF EXECUTIVE OFFICER PURSUANT TO
RULES 13a-14(a) AND 15d-14(a) UNDER THE SECURITIES EXCHANGE ACT OF 1934,
AS ADOPTED PURSUANT TO SECTION 302 OF THE SARBANES-OXLEY ACT OF 2002
I, David P. Berg, certify that:
(1) I have reviewed this Annual Report on Form 10-K of European Wax Center, Inc.;
(2) Based on my knowledge, this report does not contain any untrue statement of a material fact or omit to state a material fact necessary to make the
statements made, in light of the circumstances under which such statements were made, not misleading with respect to the period covered by this
report;
(3) Based on my knowledge, the financial statements, and other financial information included in this report, fairly present in all material respects the
financial condition, results of operations and cash flows of the registrant as of, and for, the periods presented in this report;
(4) The registrant's other certifying officer(s) and I are responsible for establishing and maintaining disclosure controls and procedures (as defined in
Exchange Act Rules 13a-15(e) and 15d-15(e)) and internal control over financial reporting (as defined in Exchange Act Rules 13a-15(f) and 15d-
15(f)) for the registrant and have:
(a) Designed such disclosure controls and procedures, or caused such disclosure controls and procedures to be designed under our supervision, to
ensure that material information relating to the registrant, including its consolidated subsidiaries, is made known to us by others within those
entities, particularly during the period in which this report is being prepared;
(b) Designed such internal control over financial reporting, or caused such internal control over financial reporting to be designed under our
supervision, to provide reasonable assurance regarding the reliability of financial reporting and the preparation of financial statements for
external purposes in accordance with generally accepted accounting principles;
(c) Evaluated the effectiveness of the registrant's disclosure controls and procedures and presented in this report our conclusions about the
effectiveness of the disclosure controls and procedures, as of the end of the period covered by this report based on such evaluation; and
(d) Disclosed in this report any change in the registrant's internal control over financial reporting that occurred during the registrant's most recent
fiscal quarter (the registrant's fourth fiscal quarter in the case of an annual report) that has materially affected, or is reasonably likely to
materially affect, the registrant's internal control over financial reporting; and
(5) The registrant's other certifying officer(s) and I have disclosed, based on our most recent evaluation of internal control over financial reporting, to
the registrant's auditors and the audit committee of the registrant's board of directors (or persons performing the equivalent functions):
(a) All significant deficiencies and material weaknesses in the design or operation of internal control over financial reporting which are
reasonably likely to adversely affect the registrant's ability to record, process, summarize and report financial information; and
(b) Any fraud, whether or not material, that involves management or other employees who have a significant role in the registrant's internal
control over financial reporting.
Date: March 15, 2022 By: /s/ DAVID P. BERG
David P. Berg
Chief Executive Officer
Exhibit 31.2
CERTIFICATION OF CHIEF FINANCIAL OFFICER PURSUANT TO
RULES 13a-14(a) AND 15d-14(a) UNDER THE SECURITIES EXCHANGE ACT OF 1934,
AS ADOPTED PURSUANT TO SECTION 302 OF THE SARBANES-OXLEY ACT OF 2002
I, David L. Willis, certify that:
(1) I have reviewed this Annual Report on Form 10-K of European Wax Center, Inc.;
(2) Based on my knowledge, this report does not contain any untrue statement of a material fact or omit to state a material fact necessary to make the
statements made, in light of the circumstances under which such statements were made, not misleading with respect to the period covered by this
report;
(3) Based on my knowledge, the financial statements, and other financial information included in this report, fairly present in all material respects the
financial condition, results of operations and cash flows of the registrant as of, and for, the periods presented in this report;
(4) The registrant's other certifying officer(s) and I are responsible for establishing and maintaining disclosure controls and procedures (as defined in
Exchange Act Rules 13a-15(e) and 15d-15(e)) and internal control over financial reporting (as defined in Exchange Act Rules 13a-15(f) and 15d-
15(f)) for the registrant and have:
(a) Designed such disclosure controls and procedures, or caused such disclosure controls and procedures to be designed under our supervision, to
ensure that material information relating to the registrant, including its consolidated subsidiaries, is made known to us by others within those
entities, particularly during the period in which this report is being prepared;
(b) Designed such internal control over financial reporting, or caused such internal control over financial reporting to be designed under our
supervision, to provide reasonable assurance regarding the reliability of financial reporting and the preparation of financial statements for
external purposes in accordance with generally accepted accounting principles;
(c) Evaluated the effectiveness of the registrant's disclosure controls and procedures and presented in this report our conclusions about the
effectiveness of the disclosure controls and procedures, as of the end of the period covered by this report based on such evaluation; and
(d) Disclosed in this report any change in the registrant's internal control over financial reporting that occurred during the registrant's most recent
fiscal quarter (the registrant's fourth fiscal quarter in the case of an annual report) that has materially affected, or is reasonably likely to
materially affect, the registrant's internal control over financial reporting; and
(5) The registrant's other certifying officer(s) and I have disclosed, based on our most recent evaluation of internal control over financial reporting, to
the registrant's auditors and the audit committee of the registrant's board of directors (or persons performing the equivalent functions):
(a) All significant deficiencies and material weaknesses in the design or operation of internal control over financial reporting which are
reasonably likely to adversely affect the registrant's ability to record, process, summarize and report financial information; and
(b) Any fraud, whether or not material, that involves management or other employees who have a significant role in the registrant's internal
control over financial reporting.
Date: March 15, 2022 By: /s/ DAVID L. WILLIS
David L. Willis
Chief Financial Officer
Exhibit 32.1
CERTIFICATION OF CHIEF EXECUTIVE OFFICER PURSUANT TO
18 U.S.C. SECTION 1350, AS ADOPTED PURSUANT TO
SECTION 906 OF THE SARBANES-OXLEY ACT OF 2002
In connection with the Annual Report of European Wax Center, Inc. (the “Company”) on Form 10-K for the period ending December 25, 2021 as
filed with the Securities and Exchange Commission on the date hereof (the “Report”), I, David P. Berg, as Chief Executive Officer of the Company, certify,
pursuant to 18 U.S.C. § 1350, as adopted pursuant to § 906 of the Sarbanes-Oxley Act of 2002, that:
(1) The Report fully complies with the requirements of section 13(a) or 15(d) of the Securities Exchange Act of 1934; and
(2) The information contained in the Report fairly presents, in all material respects, the financial condition and result of operations of the
Company.
Date: March 15, 2022 By: /s/ DAVID P. BERG
David P. Berg
Chief Executive Officer
Exhibit 32.2
CERTIFICATION OF CHIEF FINANCIAL OFFICER PURSUANT TO
18 U.S.C. SECTION 1350, AS ADOPTED PURSUANT TO
SECTION 906 OF THE SARBANES-OXLEY ACT OF 2002
In connection with the Annual Report of European Wax Center, Inc. (the “Company”) on Form 10-K for the period ending December 25, 2021 as
filed with the Securities and Exchange Commission on the date hereof (the “Report”), I, David L. Willis as Chief Financial Officer of the Company, certify,
pursuant to 18 U.S.C. § 1350, as adopted pursuant to § 906 of the Sarbanes-Oxley Act of 2002, that:
(1) The Report fully complies with the requirements of section 13(a) or 15(d) of the Securities Exchange Act of 1934; and
(2) The information contained in the Report fairly presents, in all material respects, the financial condition and result of operations of the
Company.
Date: March 15, 2022 By: /s/ DAVID L. WILLIS
David L. Willis
Chief Financial Officer

